Information Assurance Presentation
... motherboard. A driver has been introduced to support the embedding of security measures in hardware, including TPM devices from National Semiconductor and Atmel. Also, enhancements have been made to IPv6, SELinux, the Software Suspend feature, and the device mapper; upgrades have been made to driver ...
... motherboard. A driver has been introduced to support the embedding of security measures in hardware, including TPM devices from National Semiconductor and Atmel. Also, enhancements have been made to IPv6, SELinux, the Software Suspend feature, and the device mapper; upgrades have been made to driver ...
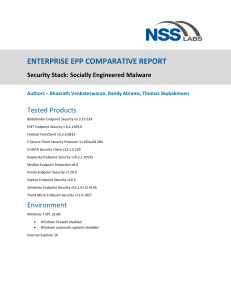
NSS Labs 2015 Enterprise Endpoint Testing
... The endpoint user creates a broad attack surface that is difficult to defend. Socially engineered malware (SEM) and the exploitation of software vulnerabilities are among the most common and effective cyberattacks that enterprises face today. Endpoint protection (EPP) products must provide robust de ...
... The endpoint user creates a broad attack surface that is difficult to defend. Socially engineered malware (SEM) and the exploitation of software vulnerabilities are among the most common and effective cyberattacks that enterprises face today. Endpoint protection (EPP) products must provide robust de ...
HUNTING-AS-A-SERVICE By Accenture, Powered by Endgame
... of money into infrastructure security technology and resources, organizations have fallen far short of gaining control over cyber threats. Today, most security monitoring approaches are alert-driven and reactive. Operators wait for evidence of a breach before security analysts take action. This appr ...
... of money into infrastructure security technology and resources, organizations have fallen far short of gaining control over cyber threats. Today, most security monitoring approaches are alert-driven and reactive. Operators wait for evidence of a breach before security analysts take action. This appr ...
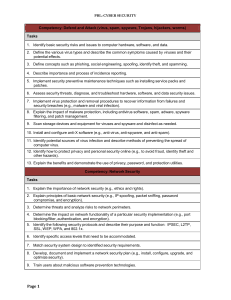
Competency: Defend and Attack (virus, spam, spyware - FBLA-PBL
... Computer Network Software Operations, Computer Applications, Information Technology Fundamentals, and Computer Information Systems Competency-Based Tasks/Competency Lists. 2009-2010. Virginia Department of Education. Richmond, VA. Computer Business Applications and Network Administration. 2001. Care ...
... Computer Network Software Operations, Computer Applications, Information Technology Fundamentals, and Computer Information Systems Competency-Based Tasks/Competency Lists. 2009-2010. Virginia Department of Education. Richmond, VA. Computer Business Applications and Network Administration. 2001. Care ...
View the graphic
... You face unprecedented challenges to protect your midsize business from cybersecurity threats. New trends such as mobility and cloud are changing how you need to secure devices, data and your network. To deal with these challenges, you need a smart, scalable threat-centric security model. This model ...
... You face unprecedented challenges to protect your midsize business from cybersecurity threats. New trends such as mobility and cloud are changing how you need to secure devices, data and your network. To deal with these challenges, you need a smart, scalable threat-centric security model. This model ...
Green-Aware Security
... overhead within the computing infrastructure; Optimal and non-overlapping security solutions sufficient for countering network and application security issues is required but not sufficient in the near future; Energy-consumption perspective must be taken also into account. ...
... overhead within the computing infrastructure; Optimal and non-overlapping security solutions sufficient for countering network and application security issues is required but not sufficient in the near future; Energy-consumption perspective must be taken also into account. ...
Essentials of Security
... Strive for systems that are secure by design Apply the principle of least privilege Learn from experience ...
... Strive for systems that are secure by design Apply the principle of least privilege Learn from experience ...
Enhanced Security Models for Operating Systems: A Cryptographic
... Only the system kernel is able to directly access GPRIV. Global public vaults(GPUV): GPUV is opposite to GPRIV in that it holds values that must be accessible by all users on the system as required. ...
... Only the system kernel is able to directly access GPRIV. Global public vaults(GPUV): GPUV is opposite to GPRIV in that it holds values that must be accessible by all users on the system as required. ...
information Security Blueprint
... The Information Security Blueprint • Basis for design, selection, and implementation of all security policies, education and training programs, and technological controls • More detailed version of security framework (outline of overall information security strategy for organization) • Should speci ...
... The Information Security Blueprint • Basis for design, selection, and implementation of all security policies, education and training programs, and technological controls • More detailed version of security framework (outline of overall information security strategy for organization) • Should speci ...
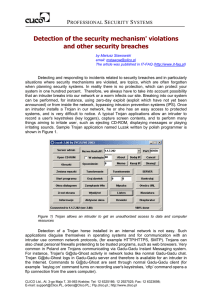
Detection of the security mechanism` violations and other
... detection break-ins (i.e. attacks resulting in unauthorized control over the system) and explaining security breaches. The analysis of events logged by IDP/IDS systems is difficult because Internet worms generate many attacks and therefore well-thought-of intruders' attacks can go unspotted. The ana ...
... detection break-ins (i.e. attacks resulting in unauthorized control over the system) and explaining security breaches. The analysis of events logged by IDP/IDS systems is difficult because Internet worms generate many attacks and therefore well-thought-of intruders' attacks can go unspotted. The ana ...
MASTER - HubSpot
... outsourcing administration of information assets , networks, or data you must retain legal control of proprietary information and use limited “need to know” access to such assets, networks or data; and (xiii) reference the protection of Customer Information and compliance with the Security Standards ...
... outsourcing administration of information assets , networks, or data you must retain legal control of proprietary information and use limited “need to know” access to such assets, networks or data; and (xiii) reference the protection of Customer Information and compliance with the Security Standards ...
Computer and Information Security
... Availability - The more critical a component or service is, the higher the level of availability required: • High availability- authentication service ...
... Availability - The more critical a component or service is, the higher the level of availability required: • High availability- authentication service ...
security threats: a guide for small and medium
... whereby people are required to choose a unique password that others cannot guess but is still easy for them to remember. Nowadays most people have at least five other passwords to remember, and the password used for company business should not be the same one used for webmail accounts, site membersh ...
... whereby people are required to choose a unique password that others cannot guess but is still easy for them to remember. Nowadays most people have at least five other passwords to remember, and the password used for company business should not be the same one used for webmail accounts, site membersh ...
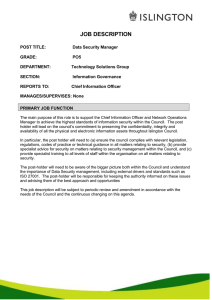
Data Security Manager
... To assist in taking timely action resulting from any risk assessment recommendations. This may involve liaison with other department such as estates or planning etc. It is essential to keep the Chief Information Officer informed if there are any issues of non-compliance. ...
... To assist in taking timely action resulting from any risk assessment recommendations. This may involve liaison with other department such as estates or planning etc. It is essential to keep the Chief Information Officer informed if there are any issues of non-compliance. ...
Chapter 1
... Hardware, Software, Storage, Data, People/User Any system is most vulnerable at its weakest point. Principle of Easiest Penetration - An intruder must be ...
... Hardware, Software, Storage, Data, People/User Any system is most vulnerable at its weakest point. Principle of Easiest Penetration - An intruder must be ...
Chapter 1
... Hardware, Software, Storage, Data, People/User Any system is most vulnerable at its weakest point. Principle of Easiest Penetration - An intruder must be ...
... Hardware, Software, Storage, Data, People/User Any system is most vulnerable at its weakest point. Principle of Easiest Penetration - An intruder must be ...
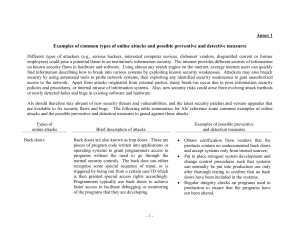
Annex 1
... employees) could pose a potential threat to an institution's information security. The internet provides different sources of information on known security flaws in hardware and software. Using almost any search engine on the internet, average internet users can quickly find information describing h ...
... employees) could pose a potential threat to an institution's information security. The internet provides different sources of information on known security flaws in hardware and software. Using almost any search engine on the internet, average internet users can quickly find information describing h ...
Threats in Unix OS
... Failure to handle exception Improper/inadequate Origin validation Input validation Boundary condition Access right validation ...
... Failure to handle exception Improper/inadequate Origin validation Input validation Boundary condition Access right validation ...
Course Schedule
... 133b F. Roosevelt & Omonoia Ave 3011, Limassol, Cyprus Tel. +357 25029300, Fax: +357 25029301 ...
... 133b F. Roosevelt & Omonoia Ave 3011, Limassol, Cyprus Tel. +357 25029300, Fax: +357 25029301 ...
Huntsman Security updates trail-blazing cyber security analytics and
... release of its enterprise-wide cyber defence technology. This update enhances the security analytic capabilities, expands the cloud integration connector and delivers increased response capabilities. “This new version builds on the existing capabilities we have in enterprise security analytics, mach ...
... release of its enterprise-wide cyber defence technology. This update enhances the security analytic capabilities, expands the cloud integration connector and delivers increased response capabilities. “This new version builds on the existing capabilities we have in enterprise security analytics, mach ...
abidah
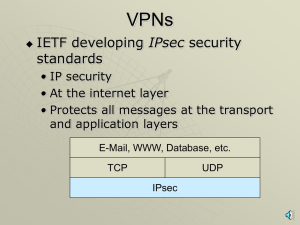
... A managed distributed host-based firewall system utilizing end-to-end IPsec can implement separate multi-level security policies with fine granularity. Using end-to-end model, it is possible to divide users and servers into various trust groups and interest communities to implement separate security ...
... A managed distributed host-based firewall system utilizing end-to-end IPsec can implement separate multi-level security policies with fine granularity. Using end-to-end model, it is possible to divide users and servers into various trust groups and interest communities to implement separate security ...
Information security in a youth organisation?
... The information security policy is one solution • to ensure security on the three criteria (CID) • that is not limited to computers • for all information and resources ...
... The information security policy is one solution • to ensure security on the three criteria (CID) • that is not limited to computers • for all information and resources ...
Voice Over IP and Security
... Use SRTP: offers encryption, authentication and periodic refreshment of session keys. Implement strict ACL at gateways. Implement NAT behind firewalls: issues with incoming call. ...
... Use SRTP: offers encryption, authentication and periodic refreshment of session keys. Implement strict ACL at gateways. Implement NAT behind firewalls: issues with incoming call. ...
Airport security
Airport security refers to the techniques and methods used in protecting passengers, staff and aircraft which use the airports from accidental/malicious harm, crime and other threats.