Slide 20 - Ursinus College Student, Faculty and Staff Web Pages
... should not change. This preserves the identity of the real-world object being represented. Copyright © 2007 Ramez Elmasri and Shamkant B. Navathe ...
... should not change. This preserves the identity of the real-world object being represented. Copyright © 2007 Ramez Elmasri and Shamkant B. Navathe ...
1 Syntax errors Logic errors Three Example Exceptions
... public void udder() { System.out.println( ”udder: before exception" ); throw( new ArithmeticException() ); System.out.println( ”udder: after exception" ); ...
... public void udder() { System.out.println( ”udder: before exception" ); throw( new ArithmeticException() ); System.out.println( ”udder: after exception" ); ...
“while” loop
... Repetition - Cont. • The number of repetitions is controlled by changing the limit value for the loop counter - “i” in the example on the previous slide. • That example had i increasing by one each time. The loop counter was being incremented by one. • It could have been incremented by some other v ...
... Repetition - Cont. • The number of repetitions is controlled by changing the limit value for the loop counter - “i” in the example on the previous slide. • That example had i increasing by one each time. The loop counter was being incremented by one. • It could have been incremented by some other v ...
exceptions
... public void udder() { System.out.println( ”udder: before exception" ); throw( new ArithmeticException() ); System.out.println( ”udder: after exception" ); ...
... public void udder() { System.out.println( ”udder: before exception" ); throw( new ArithmeticException() ); System.out.println( ”udder: after exception" ); ...
Recursion
... • The recursion here says that the sum of the squares of the integers in the range m:n can be obtained by adding the sum of the squares of the left half range, m:middle, to the sum of the squares of the right half range, middle+1:n. • We stop when we reach the base case that occurs when the range co ...
... • The recursion here says that the sum of the squares of the integers in the range m:n can be obtained by adding the sum of the squares of the left half range, m:middle, to the sum of the squares of the right half range, middle+1:n. • We stop when we reach the base case that occurs when the range co ...
Chapter 13 Exception Handling
... is caught in a catch clause, the other statements in try block are skipped, the catch clause is executed, and the finally clause is executed. * If the catch clause does not rethrow an exception, the next statement is executed. * If it does, the exception is passed to the caller of the method. If one ...
... is caught in a catch clause, the other statements in try block are skipped, the catch clause is executed, and the finally clause is executed. * If the catch clause does not rethrow an exception, the next statement is executed. * If it does, the exception is passed to the caller of the method. If one ...
exceptions
... public void udder() { System.out.println( ”udder: before exception" ); throw( new ArithmeticException() ); System.out.println( ”udder: after exception" ); ...
... public void udder() { System.out.println( ”udder: before exception" ); throw( new ArithmeticException() ); System.out.println( ”udder: after exception" ); ...
PolyP | a polytypic programming language extension
... in the near future. In the future PolyP will be able to handle mutual recursive datatypes with an arbitrary number of type arguments and in which function spaces may occur. ...
... in the near future. In the future PolyP will be able to handle mutual recursive datatypes with an arbitrary number of type arguments and in which function spaces may occur. ...
Arrays - CIS @ Temple University
... Summary • Entire array can be passed as parameter to a method • Method return value can be an array • Partially filled array usually stores values in initial segment, use an int to track how many are used • Privacy leak caused by returning array corresponding to private instance variable JAVA: An I ...
... Summary • Entire array can be passed as parameter to a method • Method return value can be an array • Partially filled array usually stores values in initial segment, use an int to track how many are used • Privacy leak caused by returning array corresponding to private instance variable JAVA: An I ...
users.ju.edu
... allowing others to copy from an exam, students substituting for one another in exams, submission of another person’s work for evaluation, preparing work for another person’s submission, unauthorized collaboration on an assignment, submission of the same or substantially similar work for two courses ...
... allowing others to copy from an exam, students substituting for one another in exams, submission of another person’s work for evaluation, preparing work for another person’s submission, unauthorized collaboration on an assignment, submission of the same or substantially similar work for two courses ...
ppt
... Stack is generic to allow any type of value to be stored
Stack wordStack = new Stack();
Stack numStack = new Stack();
...
... Stack
Data layout transformation exploiting memory-level
... allowing usages relying on the default layout such as addressing logically adjacent elements through hard-coded pointer arithmetic. Therefore, programmers opting to use automatic transformations on arrays must be subject to more stringent interfaces that insulate the source code from changes in the ...
... allowing usages relying on the default layout such as addressing logically adjacent elements through hard-coded pointer arithmetic. Therefore, programmers opting to use automatic transformations on arrays must be subject to more stringent interfaces that insulate the source code from changes in the ...
Introduction to Software Engineering
... since the container effectively plays this role. When the applet is displayed its paint method will be called – a default one inherited from the JApplet class will be used if the class has no such method. The paint method takes an argument of type Graphics – we can apply methods to this argument to ...
... since the container effectively plays this role. When the applet is displayed its paint method will be called – a default one inherited from the JApplet class will be used if the class has no such method. The paint method takes an argument of type Graphics – we can apply methods to this argument to ...
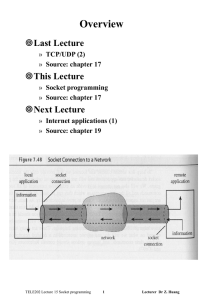
System Calls for Elementary TCP Sockets
... *servaddr: a pointer to a socket address structure addrlen: the size of the socket address structure The socket address structure must contain the IP address and the port number for the connection wanted. In TCP connect initiates a three-way handshake. connect returns when the connection is establis ...
... *servaddr: a pointer to a socket address structure addrlen: the size of the socket address structure The socket address structure must contain the IP address and the port number for the connection wanted. In TCP connect initiates a three-way handshake. connect returns when the connection is establis ...
Slides
... How to perform an IO action • Some thing of type: IO Int is a potential action which will return an Int, if it is ever performed. • In order for the action to occur, it must be performed. • Any thing with type : IO a typed at top level will be performed. • This is the only way that an action can be ...
... How to perform an IO action • Some thing of type: IO Int is a potential action which will return an Int, if it is ever performed. • In order for the action to occur, it must be performed. • Any thing with type : IO a typed at top level will be performed. • This is the only way that an action can be ...
Document
... variable-sized : e.g., alloca() call in C allocates variable-sized array on the stack -not a problem in Iota where arrays heapallocated CS 412/413 Introduction to Compilers and Translators -- Spring ...
... variable-sized : e.g., alloca() call in C allocates variable-sized array on the stack -not a problem in Iota where arrays heapallocated CS 412/413 Introduction to Compilers and Translators -- Spring ...
Document
... – SOCK_RAW, a raw type that allows privileged programs to access low-level protocols or network interfaces » protocol is used to select a specific protocol in the protocol family if there are multiple protocols to support the same service type ...
... – SOCK_RAW, a raw type that allows privileged programs to access low-level protocols or network interfaces » protocol is used to select a specific protocol in the protocol family if there are multiple protocols to support the same service type ...
View
... Class definitions can appear anywhere in a program, but they are usually near the beginning (after the import statements). The syntax rules for a class definition are the same as for other compound statements (see Section 4.4). This definition creates a new class called Point. The pass statement has ...
... Class definitions can appear anywhere in a program, but they are usually near the beginning (after the import statements). The syntax rules for a class definition are the same as for other compound statements (see Section 4.4). This definition creates a new class called Point. The pass statement has ...
Compilation I: Java Byte Code
... thus instead of iload we find aload and similar instructions. If we do not mark the method same() below as being static then it is a non-static (or virtual) method which can refer to the object with which it is associated using this. Method int same(java.lang.Object) 0 aload 0 1 aload 1 2 invokevirt ...
... thus instead of iload we find aload and similar instructions. If we do not mark the method same() below as being static then it is a non-static (or virtual) method which can refer to the object with which it is associated using this. Method int same(java.lang.Object) 0 aload 0 1 aload 1 2 invokevirt ...
Table of contents
... In computer programming, operator overloading (less commonly known as ad-hoc polymorphism) is a specific case of polymorphism in which some or all of operators like +, = or == are treated as polymorphic functions and as such have different behaviours depending on the types of its arguments. Operator ...
... In computer programming, operator overloading (less commonly known as ad-hoc polymorphism) is a specific case of polymorphism in which some or all of operators like +, = or == are treated as polymorphic functions and as such have different behaviours depending on the types of its arguments. Operator ...
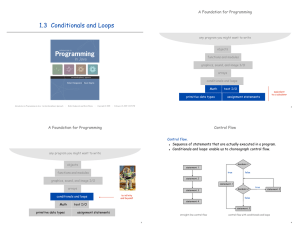
1.3 Conditionals and Loops A Foundation for Programming
... Fact. [see ORF 309] Probability of winning = stake ÷ goal. Fact. [see ORF 309] Expected number of bets = stake # desired gain. Ex. 20% chance of turning $500 into $2500, ...
... Fact. [see ORF 309] Probability of winning = stake ÷ goal. Fact. [see ORF 309] Expected number of bets = stake # desired gain. Ex. 20% chance of turning $500 into $2500, ...
Chapter 1 and 2
... • Cannot include special characters such as !, %, ], or $ • Cannot include an empty space • Cannot be any of the reserved words • Should not be longer than 32 characters (although allowed) ...
... • Cannot include special characters such as !, %, ], or $ • Cannot include an empty space • Cannot be any of the reserved words • Should not be longer than 32 characters (although allowed) ...
Slides
... use type annotations. Type-checking of rank 2 polymorphism is decidable What kind of annotations must we give? ...
... use type annotations. Type-checking of rank 2 polymorphism is decidable What kind of annotations must we give? ...
ch02-IntroductionToProgramming
... All the lines in the block must be indented, and indented the same amount. Variables in the command area don’t exist in your functions, and variables in your functions don’t exist in the command area. The computer can’t read your mind. It will only do exactly what you tell it to do. ...
... All the lines in the block must be indented, and indented the same amount. Variables in the command area don’t exist in your functions, and variables in your functions don’t exist in the command area. The computer can’t read your mind. It will only do exactly what you tell it to do. ...