COSC A365 Chapter 2
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
ch2
... operating system kernel as though they were all hardware A virtual machine provides an ...
... operating system kernel as though they were all hardware A virtual machine provides an ...
ppt
... secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: Free space management Storage allocation ...
... secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: Free space management Storage allocation ...
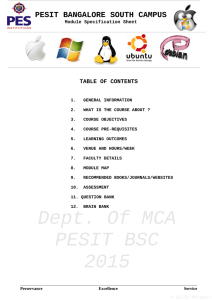
OPERATINGSYSTEMS 2015
... computer system. Without an operating system, a user cannot run an application program on their computer. Operating systems are found on almost any device that contains a computer – from cellular phones and video game consoles to supercomputers and web servers. The course covers the following essent ...
... computer system. Without an operating system, a user cannot run an application program on their computer. Operating systems are found on almost any device that contains a computer – from cellular phones and video game consoles to supercomputers and web servers. The course covers the following essent ...
2. OS Structures - FSU Computer Science
... If a system is to be protected and secure, precautions must be instituted throughout it (a chain is only as strong as its weakest link) ...
... If a system is to be protected and secure, precautions must be instituted throughout it (a chain is only as strong as its weakest link) ...
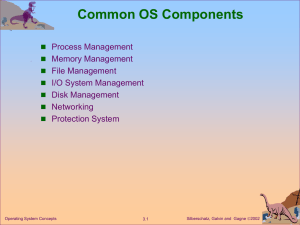
Abstract View of System Components
... memory, files, and I/O devices, to accomplish its task. The operating system is responsible for the following activities in connection with process management. Process creation and deletion. eg allocate memory, find binary, load, OS table, queue, .. process suspension and resumption. Provi ...
... memory, files, and I/O devices, to accomplish its task. The operating system is responsible for the following activities in connection with process management. Process creation and deletion. eg allocate memory, find binary, load, OS table, queue, .. process suspension and resumption. Provi ...
View
... secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: Free space management Storage allocation ...
... secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: Free space management Storage allocation ...
Module 3: Operating
... secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: Free space management Storage allocation ...
... secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: Free space management Storage allocation ...
Chapter 3: Operating-System Structures Common System
... secondary storage to back up main memory. ■ Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. ■ The operating system is responsible for the following activities in connection with disk management: ✦ Free space management ✦ Storage allocation ...
... secondary storage to back up main memory. ■ Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. ■ The operating system is responsible for the following activities in connection with disk management: ✦ Free space management ✦ Storage allocation ...
A Pattern Language for Secure Operating System Architectures
... We are building an OS for a range of applications with different reliability and security requirements and a variety of plug-ins. We would like to provide OS versions with different types of modules, some more secure, some less so. • Context – Operating systems are large systems that require decompo ...
... We are building an OS for a range of applications with different reliability and security requirements and a variety of plug-ins. We would like to provide OS versions with different types of modules, some more secure, some less so. • Context – Operating systems are large systems that require decompo ...
Chapter 3
... secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: Free space management Storage allocation ...
... secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following activities in connection with disk management: Free space management Storage allocation ...
ch3
... permanently, the computer system must provide secondary storage to back up main memory Most modern computer systems use disks as the principle on-line storage medium, for both programs and data OS responsibilities: Free space management Storage allocation Disk scheduling ...
... permanently, the computer system must provide secondary storage to back up main memory Most modern computer systems use disks as the principle on-line storage medium, for both programs and data OS responsibilities: Free space management Storage allocation Disk scheduling ...
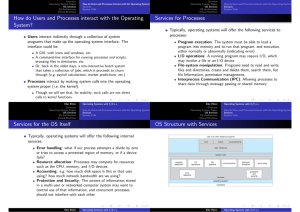
How do Users and Processes interact with the Operating System
... Traditional UNIX UNIX - one big kernel Consists of everything below the system-call interface and above the physical hardware Provides the file system, CPU scheduling, memory management, and other operating-system functions; a large number of functions for one level Limited to hardware support compi ...
... Traditional UNIX UNIX - one big kernel Consists of everything below the system-call interface and above the physical hardware Provides the file system, CPU scheduling, memory management, and other operating-system functions; a large number of functions for one level Limited to hardware support compi ...
Module 3: Operating
... protection of system resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources – shared only thru emulator. A virtual-machine system is a perfect vehicle for operating-systems research and development. System d ...
... protection of system resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources – shared only thru emulator. A virtual-machine system is a perfect vehicle for operating-systems research and development. System d ...
Integrated End-to-End Dependability in the Loris Storage Stack,
... base system), resource isolation, and the potential to checkpoint/restart and migrate environments [16]. 1) The naming layer: The Loris naming layer is part of the MEE. This has two main advantages. First, this allows a MEE (and thus its applications) to choose its own, private naming scheme. The ca ...
... base system), resource isolation, and the potential to checkpoint/restart and migrate environments [16]. 1) The naming layer: The Loris naming layer is part of the MEE. This has two main advantages. First, this allows a MEE (and thus its applications) to choose its own, private naming scheme. The ca ...
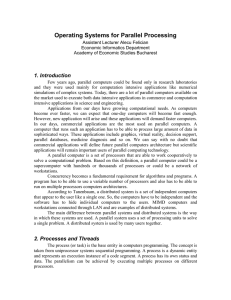
Operating Systems for Parallel Processing - Current Activities
... such distributed systems. A distributed system is managed by a distributed operating system. A distributed operating system manages the system shared resources used by multiple processes, the process scheduling activity (how processes are allocating on available processors), the communication and sy ...
... such distributed systems. A distributed system is managed by a distributed operating system. A distributed operating system manages the system shared resources used by multiple processes, the process scheduling activity (how processes are allocating on available processors), the communication and sy ...
Module 4: Processes
... Extensibility (Can easily add new functions--user processes) Flexibility (Can remove functions that are not needed) Portability (Only the small kernel has hardware specific code) Distributed System support (Message passing can generalize to network communications) Object oriented (A good d ...
... Extensibility (Can easily add new functions--user processes) Flexibility (Can remove functions that are not needed) Portability (Only the small kernel has hardware specific code) Distributed System support (Message passing can generalize to network communications) Object oriented (A good d ...
PPT
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
Module 3: Operating-System Structures
... write, create, and delete files. Communications – exchange of information between processes executing either on the same computer or on different systems tied together by a network. Error detection – ensure correct computing by detecting errors in the CPU and memory hardware, in I/O devices, or in u ...
... write, create, and delete files. Communications – exchange of information between processes executing either on the same computer or on different systems tied together by a network. Error detection – ensure correct computing by detecting errors in the CPU and memory hardware, in I/O devices, or in u ...
2.01 - Faculty of Computer Science and Information Technology
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
Micro-CernVM: Slashing the Cost of Building and
... sourced just before the root file system is switched and allows for custom actions. Special care has to be taken in the shutdown script of the operating system. Typically, the shutdown script does not expect an AUFS file system stack as root file system. Therefore, the script needs to be modified to ...
... sourced just before the root file system is switched and allows for custom actions. Special care has to be taken in the shutdown script of the operating system. Typically, the shutdown script does not expect an AUFS file system stack as root file system. Therefore, the script needs to be modified to ...
Interfacing with the Operating System
... space and actual memory locations. • We can see how this works by considering computers with a very small amount of memory – le’ts say 4096 bytes. • If the processor used 2 byte integers to hold addresses it could in principle refer to 65536 (2 ** 16) locations. • But only 4096 of these could actual ...
... space and actual memory locations. • We can see how this works by considering computers with a very small amount of memory – le’ts say 4096 bytes. • If the processor used 2 byte integers to hold addresses it could in principle refer to 65536 (2 ** 16) locations. • But only 4096 of these could actual ...