Arrays
... themselves, such as type and length (Java), or may consist only of their components (C, C++) – I will use the terms reflective and non-reflective, respectively, to refer to these two types of arrays – This is not standard terminology, but it is consistent with other uses of the terms ...
... themselves, such as type and length (Java), or may consist only of their components (C, C++) – I will use the terms reflective and non-reflective, respectively, to refer to these two types of arrays – This is not standard terminology, but it is consistent with other uses of the terms ...
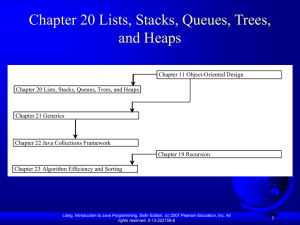
Chapter 19 Java Data Structures
... Stacks and Queues A stack can be viewed as a special type of list, where the elements are accessed, inserted, and deleted only from the end, called the top, of the stack. A queue represents a waiting list. A queue can be viewed as a special type of list, where the elements are inserted into the end ...
... Stacks and Queues A stack can be viewed as a special type of list, where the elements are accessed, inserted, and deleted only from the end, called the top, of the stack. A queue represents a waiting list. A queue can be viewed as a special type of list, where the elements are inserted into the end ...
Lock-Free Red-Black Trees Using CAS
... The negative side-effects of using lock-based synchronization mechanisms are well known and include unexpected scheduling anomalies such as priority inversion and convoying as well as unnecessary synchronization overhead and the potential for deadlock. Despite these drawbacks, the use of lock-free t ...
... The negative side-effects of using lock-based synchronization mechanisms are well known and include unexpected scheduling anomalies such as priority inversion and convoying as well as unnecessary synchronization overhead and the potential for deadlock. Despite these drawbacks, the use of lock-free t ...
Elementary Data Structures and Hash Tables
... Complexity All direct-address table operations are O(1)! So why isn’t every set implemented with a direct-address table? The space complexity is Θ(`U`) ...
... Complexity All direct-address table operations are O(1)! So why isn’t every set implemented with a direct-address table? The space complexity is Θ(`U`) ...
Lecture 28 Non-blocking Algorithms
... Non-Blocking Data Structures • Non-blocking operations so far have focused on Atomic single-value data structures – AtomicInteger – AtomicReference
– Etc.
...
... Non-Blocking Data Structures • Non-blocking operations so far have focused on Atomic single-value data structures – AtomicInteger – AtomicReference
CS 130 A: Data Structures and Algorithms
... If key present, always find it But may say Yes when in fact key is not present ...
... If key present, always find it But may say Yes when in fact key is not present ...
Data Structures for NLP
... Value* entry=hash_table[code]; while (entry && entry->v->key!=key) entry=entry->next; if (!entry) make_new_entry(key); return entry; ...
... Value* entry=hash_table[code]; while (entry && entry->v->key!=key) entry=entry->next; if (!entry) make_new_entry(key); return entry; ...
Text Processing in Linux A Tutorial for CSE 562/662 (NLP)
... Value* entry=hash_table[code]; while (entry && entry->v->key!=key) entry=entry->next; if (!entry) make_new_entry(key); return entry; ...
... Value* entry=hash_table[code]; while (entry && entry->v->key!=key) entry=entry->next; if (!entry) make_new_entry(key); return entry; ...
“while” loop
... Repetition - Cont. • The number of repetitions is controlled by changing the limit value for the loop counter - “i” in the example on the previous slide. • That example had i increasing by one each time. The loop counter was being incremented by one. • It could have been incremented by some other v ...
... Repetition - Cont. • The number of repetitions is controlled by changing the limit value for the loop counter - “i” in the example on the previous slide. • That example had i increasing by one each time. The loop counter was being incremented by one. • It could have been incremented by some other v ...
Lease/Release: Architectural Support for Scaling Contended Data
... protocols, allowing a core to lease memory, at the granularity of cache lines, by delaying incoming coherence requests for a short, bounded period of time. Our analysis shows that Lease/Release can significantly reduce the overheads of contention for both non-blocking (lock-free) and lock-based data ...
... protocols, allowing a core to lease memory, at the granularity of cache lines, by delaying incoming coherence requests for a short, bounded period of time. Our analysis shows that Lease/Release can significantly reduce the overheads of contention for both non-blocking (lock-free) and lock-based data ...
Think Data Structures
... more than 1000. By focusing on the topics I think are most useful for software engineers, I kept this book under 200 pages. Too “bottom up” Many data structures books focus on how data structures work (the implementations), with less about how to use them (the interfaces). In this book, I go “top do ...
... more than 1000. By focusing on the topics I think are most useful for software engineers, I kept this book under 200 pages. Too “bottom up” Many data structures books focus on how data structures work (the implementations), with less about how to use them (the interfaces). In this book, I go “top do ...
No Slide Title
... this.model = new DefaultBoundedRangeModel(value, 0, min, max); this.model.addChangeListener(changeListener); updateUI(); ...
... this.model = new DefaultBoundedRangeModel(value, 0, min, max); this.model.addChangeListener(changeListener); updateUI(); ...
Object-Oriented Programming versus Functional Programming
... Object-oriented programming doesn’t so much dispute this view of the world as restructure it at a higher level. It groups operations and data into modular units called objects and lets you combine objects into structured networks to form a complete program. In an object-oriented programming language ...
... Object-oriented programming doesn’t so much dispute this view of the world as restructure it at a higher level. It groups operations and data into modular units called objects and lets you combine objects into structured networks to form a complete program. In an object-oriented programming language ...
Stacks and Queues
... AP AB Subset Requirements: Although there is no standard Java Interface we need to be able to work with the AP interfaces for Stacks and Queues (handouts) Students are also responsible for understanding that these ADT’s can be implemented as an array or a linked list, although you will NOT be te ...
... AP AB Subset Requirements: Although there is no standard Java Interface we need to be able to work with the AP interfaces for Stacks and Queues (handouts) Students are also responsible for understanding that these ADT’s can be implemented as an array or a linked list, although you will NOT be te ...
Chapter 12: Dictionary (Hash Tables)
... Indexing into a hash table is extremely fast, even faster than searching a skip list or an AVL tree. There are many different ways to exploit this speed. A cache is a data structure that uses two levels of storage. One level is simply an ordinary collection class, such as a bag dictionary. The secon ...
... Indexing into a hash table is extremely fast, even faster than searching a skip list or an AVL tree. There are many different ways to exploit this speed. A cache is a data structure that uses two levels of storage. One level is simply an ordinary collection class, such as a bag dictionary. The secon ...
Chapter26
... the methods get(int index) and set(int index, Object o) for accessing and modifying an element through an index and the add(Object o) for adding an element at the end of the list are efficient. However, the methods add(int index, Object o) and remove(int index) are inefficient because it requires sh ...
... the methods get(int index) and set(int index, Object o) for accessing and modifying an element through an index and the add(Object o) for adding an element at the end of the list are efficient. However, the methods add(int index, Object o) and remove(int index) are inefficient because it requires sh ...
Powerpoint - MHS Comp Sci
... boolean isEmpty(); // precondition: queue is [e1, e2, ..., en] with n >= 0 // postcondition: queue is [e1, e2, ..., en, x] void enqueue(Object x); // precondition: queue is [e1, e2, ..., en] with n >= 1 // postcondition: queue is [e2, ..., en]; returns e1 ...
... boolean isEmpty(); // precondition: queue is [e1, e2, ..., en] with n >= 0 // postcondition: queue is [e1, e2, ..., en, x] void enqueue(Object x); // precondition: queue is [e1, e2, ..., en] with n >= 1 // postcondition: queue is [e2, ..., en]; returns e1 ...
Section 5 slides - Emory Math/CS Department
... method shown below in (a) is logically correct, but it has a compilation error because the Java compiler thinks it possible that this method does not return any value. public static int sign(int n) { if (n > 0) return 1; else if (n == 0) return 0; else if (n < 0) return –1; ...
... method shown below in (a) is logically correct, but it has a compilation error because the Java compiler thinks it possible that this method does not return any value. public static int sign(int n) { if (n > 0) return 1; else if (n == 0) return 0; else if (n < 0) return –1; ...
Lecture 3
... User of data structure should not need to know details of its implementation Creator of data structure should be able to change implementation without affecting applications that use it Therefore implementation information should be hidden ...
... User of data structure should not need to know details of its implementation Creator of data structure should be able to change implementation without affecting applications that use it Therefore implementation information should be hidden ...
Corporate Profile 2014
... •The ...To... annotations define a single/multiple-valued association to another entity that has ...-to-... multiplicity. It is not normally necessary to specify the associated target entity explicitly since it can usually be inferred from the type of the object being referenced. •If the relationshi ...
... •The ...To... annotations define a single/multiple-valued association to another entity that has ...-to-... multiplicity. It is not normally necessary to specify the associated target entity explicitly since it can usually be inferred from the type of the object being referenced. •If the relationshi ...
lec4
... Algorithms and Data Structures* • Objective: To review the fundamental algorithms and data structures that are commonly used in programs. To see how to use and implement these algorithms and data structures in different languages and to see what language and library support exists for them. ...
... Algorithms and Data Structures* • Objective: To review the fundamental algorithms and data structures that are commonly used in programs. To see how to use and implement these algorithms and data structures in different languages and to see what language and library support exists for them. ...
Chapter5. Linear Lists
... An abstract class can define nonconstant data members and nonabstract methods If only constants and abstract methods are needed interface will do A class can implement many interfaces but can extend at most one class Only single inheritance among classes Multiple inheritance is simulated using ...
... An abstract class can define nonconstant data members and nonabstract methods If only constants and abstract methods are needed interface will do A class can implement many interfaces but can extend at most one class Only single inheritance among classes Multiple inheritance is simulated using ...
Lecture 3 Data Structures (DAT037)
... • For using as a queue, provides add = addFirst, remove = removeLast • For using as a stack, provides push = addFirst, pop = removeFirst • Note: Java also provides a Stack class, but this ...
... • For using as a queue, provides add = addFirst, remove = removeLast • For using as a stack, provides push = addFirst, pop = removeFirst • Note: Java also provides a Stack class, but this ...
Chapter 1
... • Portable means that a program may be written on one type of computer and then run on a wide variety of computers, with little or no modification. • Java byte code runs on the JVM and not on any particular CPU; therefore, compiled Java programs are highly portable. • JVMs exist on many platforms: • ...
... • Portable means that a program may be written on one type of computer and then run on a wide variety of computers, with little or no modification. • Java byte code runs on the JVM and not on any particular CPU; therefore, compiled Java programs are highly portable. • JVMs exist on many platforms: • ...