Client-Side Web Programming (Part 1) Robert M. Dondero, Ph.D.
... Applet tag commands browser to load specified Applet class and create Applet object ...
... Applet tag commands browser to load specified Applet class and create Applet object ...
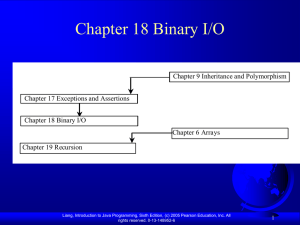
Chapter 18 Binary I/O
... ASCII and Unicode efficiently. Most operating systems use ASCII. Java uses Unicode. The ASCII character set is a subset of the Unicode character set. Since most applications need only the ASCII character set, it is a waste to represent an 8-bit ASCII character as a 16-bit Unicode character. The UTF- ...
... ASCII and Unicode efficiently. Most operating systems use ASCII. Java uses Unicode. The ASCII character set is a subset of the Unicode character set. Since most applications need only the ASCII character set, it is a waste to represent an 8-bit ASCII character as a 16-bit Unicode character. The UTF- ...
Programming with Coq
... The type of functions The value add3 is not a natural number Check add3. add3 : nat -> nat The value add3 is a function I ...
... The type of functions The value add3 is not a natural number Check add3. add3 : nat -> nat The value add3 is a function I ...
Introduction to telecommunication network software design
... • For example: .NET, JM framework, API and others. • .NET framework is a basic programming tool for programmers to design and develop software in OSes like Windows, Linux, Android, iOS, MAC. • In developing software for different platforms we use different IDEs. ...
... • For example: .NET, JM framework, API and others. • .NET framework is a basic programming tool for programmers to design and develop software in OSes like Windows, Linux, Android, iOS, MAC. • In developing software for different platforms we use different IDEs. ...
The scope of local v..
... Variables with same name in nested scopes (cont.) • The first definition of the variable r takes places inside the outer scope • The second definition of the variable with the same name r takes places inside the inner scope • From what we have learned above, the first variable r is also accessible ...
... Variables with same name in nested scopes (cont.) • The first definition of the variable r takes places inside the outer scope • The second definition of the variable with the same name r takes places inside the inner scope • From what we have learned above, the first variable r is also accessible ...
Text files
... » so is any file created with a "text editor" Binary files: the bits represent other types of encoded information, such as executable instructions or numeric data » these files are easily read by the computer but not humans » they are not "printable" files – actually, you can print them, but they wi ...
... » so is any file created with a "text editor" Binary files: the bits represent other types of encoded information, such as executable instructions or numeric data » these files are easily read by the computer but not humans » they are not "printable" files – actually, you can print them, but they wi ...
Chapter 4 Methods - I.T. at The University of Toledo
... To develop reusable code that is modular, easy-to-read, easy-todebug, and easy-to-maintain. (§5.6). To use method overloading and understand ambiguous overloading (§5.7). To design and implement overloaded methods (§5.8). To determine the scope of variables (§5.9). To know how to use the methods in ...
... To develop reusable code that is modular, easy-to-read, easy-todebug, and easy-to-maintain. (§5.6). To use method overloading and understand ambiguous overloading (§5.7). To design and implement overloaded methods (§5.8). To determine the scope of variables (§5.9). To know how to use the methods in ...
05slide
... To develop reusable code that is modular, easy-to-read, easy-todebug, and easy-to-maintain. (§5.6). To use method overloading and understand ambiguous overloading (§5.7). To design and implement overloaded methods (§5.8). To determine the scope of variables (§5.9). To know how to use the methods in ...
... To develop reusable code that is modular, easy-to-read, easy-todebug, and easy-to-maintain. (§5.6). To use method overloading and understand ambiguous overloading (§5.7). To design and implement overloaded methods (§5.8). To determine the scope of variables (§5.9). To know how to use the methods in ...
RSTL Manual Rev H - TDK
... under control. Each power supply is unique and the RSTL must be calibrated for each supply. Section 3.2 has all the calibration details, but this should be performed after you are familiar with the basic operation of the RSTL. Each command sent to the RSTL must be followed by a CR LF (ASCII 13 and 1 ...
... under control. Each power supply is unique and the RSTL must be calibrated for each supply. Section 3.2 has all the calibration details, but this should be performed after you are familiar with the basic operation of the RSTL. Each command sent to the RSTL must be followed by a CR LF (ASCII 13 and 1 ...
Chapter 9
... Stream: an object that either delivers data to its destination (screen, file, etc.) or that takes data from a source (keyboard, file, etc.) » it acts as a buffer between the data source and destination Input stream: a stream that provides input to a program Output stream: a stream that accepts outpu ...
... Stream: an object that either delivers data to its destination (screen, file, etc.) or that takes data from a source (keyboard, file, etc.) » it acts as a buffer between the data source and destination Input stream: a stream that provides input to a program Output stream: a stream that accepts outpu ...
Chapter 4 Methods
... To define methods with formal parameters (§6.2). To invoke methods with actual parameters (i.e., arguments) (§6.2). To define methods with a return value (§6.3). To define methods without a return value (§6.4). To pass arguments by value (§6.5). To develop reusable code that is modular, easy to read ...
... To define methods with formal parameters (§6.2). To invoke methods with actual parameters (i.e., arguments) (§6.2). To define methods with a return value (§6.3). To define methods without a return value (§6.4). To pass arguments by value (§6.5). To develop reusable code that is modular, easy to read ...
Chapter 6
... To define methods with formal parameters (§6.2). To invoke methods with actual parameters (i.e., arguments) (§6.2). To define methods with a return value (§6.3). To define methods without a return value (§6.4). To pass arguments by value (§6.5). To develop reusable code that is modular, easy to read ...
... To define methods with formal parameters (§6.2). To invoke methods with actual parameters (i.e., arguments) (§6.2). To define methods with a return value (§6.3). To define methods without a return value (§6.4). To pass arguments by value (§6.5). To develop reusable code that is modular, easy to read ...
Introduction to ASIC Design
... Include some (possibly all) customized logic cells Have all their mask layers customized Full-custom ASIC design makes sense only When no suitable existing libraries exist or Existing library cells are not fast enough or The available pre-designed/pre-tested cells consume too much power ...
... Include some (possibly all) customized logic cells Have all their mask layers customized Full-custom ASIC design makes sense only When no suitable existing libraries exist or Existing library cells are not fast enough or The available pre-designed/pre-tested cells consume too much power ...
Object Oriented Programming
... methodology of programming where new types of objects are defined • An object is a single software unit that combines attributes and methods • An attribute is a “characteristic” of an object; it’s a variable associated with an object (“instance variable”) • A method is a “behavior” of an object; it’ ...
... methodology of programming where new types of objects are defined • An object is a single software unit that combines attributes and methods • An attribute is a “characteristic” of an object; it’s a variable associated with an object (“instance variable”) • A method is a “behavior” of an object; it’ ...
UNIT-1
... 11. Write a program to convert the given temperature in Fahrenheit to Celsius using the following conversion formula c=(F-32)/1.8 and display the values in a tabular form. 12. What is class? How does it accomplish data hiding? 13. How do classes help us to organize our programs? 14. What is class? C ...
... 11. Write a program to convert the given temperature in Fahrenheit to Celsius using the following conversion formula c=(F-32)/1.8 and display the values in a tabular form. 12. What is class? How does it accomplish data hiding? 13. How do classes help us to organize our programs? 14. What is class? C ...
OCR Computer Science -PLC – the big one
... will be used as appropriate in the solution of the task. This does not mean that they all have to be identifiably present, but responses that use few of them are unlikely to merit the higher mark bands. This list is not intended to be exclusive. The use of further techniques such as functions might ...
... will be used as appropriate in the solution of the task. This does not mean that they all have to be identifiably present, but responses that use few of them are unlikely to merit the higher mark bands. This list is not intended to be exclusive. The use of further techniques such as functions might ...
- RehanCodes
... Encourage team members to find faults in code A fault must be considered a normal and accepted event The team as whole will develop an ethos, group identity Modules will “belong” to the team as whole A group of up to 10 egoless programmers constitutes a ...
... Encourage team members to find faults in code A fault must be considered a normal and accepted event The team as whole will develop an ethos, group identity Modules will “belong” to the team as whole A group of up to 10 egoless programmers constitutes a ...
Savitch Java Ch. 9 - University of Scranton: Computing Sciences Dept.
... UTF stands for Universal Text Format » a special version of Unicode Unicode: a text (printable) code that uses 2 bytes per character » designed to accommodate languages with a different alphabet or no alphabet (such as Chinese and Japanese) ASCII: also a text (printable) code, but it uses just 1 byt ...
... UTF stands for Universal Text Format » a special version of Unicode Unicode: a text (printable) code that uses 2 bytes per character » designed to accommodate languages with a different alphabet or no alphabet (such as Chinese and Japanese) ASCII: also a text (printable) code, but it uses just 1 byt ...
slides18-stm
... Too large: delay progress because deny other threads access to needed resources. ...
... Too large: delay progress because deny other threads access to needed resources. ...
David Walker
... - Too large: delay progress because deny other threads access to needed resources. ...
... - Too large: delay progress because deny other threads access to needed resources. ...
DR. J VS. THE BIRD: JAVA IDE`S ONE-ON-ONE
... Instructors in beginning software design courses are faced with a number of pedagogical choices when selecting topics to cover and tools to support instruction. Should knowledge of the underlying operating system and file system be required? How much knowledge of the language system will be required ...
... Instructors in beginning software design courses are faced with a number of pedagogical choices when selecting topics to cover and tools to support instruction. Should knowledge of the underlying operating system and file system be required? How much knowledge of the language system will be required ...
Writing a Compiler
... binary, and wrote out the bit string as shown above. The first and most primitive programming language translator were assemblers; these permitted the programmer to write (In assembly language): LR 3, 5 instead of the bit string shown above.(LR=00011000, 3=0011, 5=0101) A single line of assembly ...
... binary, and wrote out the bit string as shown above. The first and most primitive programming language translator were assemblers; these permitted the programmer to write (In assembly language): LR 3, 5 instead of the bit string shown above.(LR=00011000, 3=0011, 5=0101) A single line of assembly ...
ASP.NET Programming with C# and SQL Server First
... ASP.NET Programming with C# and SQL Server, First Edition ...
... ASP.NET Programming with C# and SQL Server, First Edition ...
Structured programming

Structured programming is a programming paradigm aimed at improving the clarity, quality, and development time of a computer program by making extensive use of subroutines, block structures and for and while loops—in contrast to using simple tests and jumps such as the goto statement which could lead to ""spaghetti code"" which is difficult both to follow and to maintain.It emerged in the 1960s—particularly from a famous letter, Go To Statement Considered Harmful.—and was bolstered theoretically by the structured program theorem, and practically by the emergence of languages such as ALGOL with suitably rich control structures.