Forensics Book 2: Investigating Hard Disk and File and Operating
... “respawn” for the current run level Starts those processes ...
... “respawn” for the current run level Starts those processes ...
Figure 11.01 - 醫學資訊系 鄭仁亮教授
... Simple record structure Lines Fixed length Variable length ...
... Simple record structure Lines Fixed length Variable length ...
Lecture 8: Operating Systems Structures
... » Everyone in group must have logged into their cs162-xx accounts once before you register the group » Make sure that you select at least 2 potential sections » Due tomorrow: Thursday 9/4 by 11:59pm ...
... » Everyone in group must have logged into their cs162-xx accounts once before you register the group » Make sure that you select at least 2 potential sections » Due tomorrow: Thursday 9/4 by 11:59pm ...
Virtualization: Architectural Considerations And Other
... function of product maturity. VMware has customer references that attest to the maturity of VMware based solutions. • This paper examines these issues—architecture, solution support and enterprise readiness—in greater detail. Comparisons focus primarily on XenSource. Microsoft has not released thei ...
... function of product maturity. VMware has customer references that attest to the maturity of VMware based solutions. • This paper examines these issues—architecture, solution support and enterprise readiness—in greater detail. Comparisons focus primarily on XenSource. Microsoft has not released thei ...
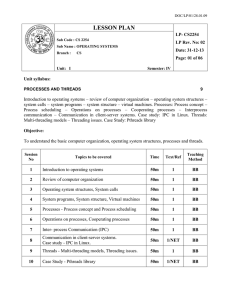
CS2254 os
... system calls – system programs – system structure – virtual machines. Processes: Process concept – Process scheduling – Operations on processes – Cooperating processes – Interprocess communication – Communication in client-server systems. Case study: IPC in Linux. Threads: Multi-threading models – T ...
... system calls – system programs – system structure – virtual machines. Processes: Process concept – Process scheduling – Operations on processes – Cooperating processes – Interprocess communication – Communication in client-server systems. Case study: IPC in Linux. Threads: Multi-threading models – T ...
Towards a Flexible, Lightweight Virtualization Alternative,
... domain should be able to achieve binary compatibility with existing applications. With that constraint as a given, we set the following subgoals. First, the abstraction level should be high enough to bridge the semantic gap. In particular, the new abstractions should allow for lightweight domains, m ...
... domain should be able to achieve binary compatibility with existing applications. With that constraint as a given, we set the following subgoals. First, the abstraction level should be high enough to bridge the semantic gap. In particular, the new abstractions should allow for lightweight domains, m ...
Intro to Linux Slides - Raspberry PI Summer Camp at IPFW
... Helsinki , Torvalds became curious about operating systems and frustrated by the licensing of MINIX, which limited it to educational use only. He began to work on his own operating system which eventually became the Linux kernel. ...
... Helsinki , Torvalds became curious about operating systems and frustrated by the licensing of MINIX, which limited it to educational use only. He began to work on his own operating system which eventually became the Linux kernel. ...
Processes - UniMAP Portal
... a set of processors simultaneously execute different instruction sequences on different data sets ...
... a set of processors simultaneously execute different instruction sequences on different data sets ...
slides
... A Note on Linux Threads Linux refers to threads and processes as tasks Thread creation is done through clone() system call clone() can be parameterized to allow a range of resource sharing ...
... A Note on Linux Threads Linux refers to threads and processes as tasks Thread creation is done through clone() system call clone() can be parameterized to allow a range of resource sharing ...
PPT
... Load Sharing One of the most commonly used schemes in current multiprocessors, despite the potential disadvantages • Load is distributed evenly across the processors ...
... Load Sharing One of the most commonly used schemes in current multiprocessors, despite the potential disadvantages • Load is distributed evenly across the processors ...
Operating System Kernels - Freie Universität Berlin
... process there is a struct called proc, which has all relevant pieces of information like the PID PPID, the priority of the process and the state of the process. There are five different stats: SIDL,SRUN,SSLEEP,SSTOP and SZOMB. The function fork() creates a copy of the actual task that PID and PPID ( ...
... process there is a struct called proc, which has all relevant pieces of information like the PID PPID, the priority of the process and the state of the process. There are five different stats: SIDL,SRUN,SSLEEP,SSTOP and SZOMB. The function fork() creates a copy of the actual task that PID and PPID ( ...
Operating System Fundamentals
... family (such as Windows 98, XP and Vista). Other examples are Unix and Linux, Mac OS X, and specialized operating systems for handheld devices like mobile phones. An operating system is the software that controls (or operates) all of the parts of your computer. It manages all of your resources, and ...
... family (such as Windows 98, XP and Vista). Other examples are Unix and Linux, Mac OS X, and specialized operating systems for handheld devices like mobile phones. An operating system is the software that controls (or operates) all of the parts of your computer. It manages all of your resources, and ...
Isolating Operating System Components with Intel SGX
... the operating system as one compromised operating system component can easily compromise other components of the kernel without the need for further vulnerabilities. To enforce isolation of operating system components even in the event of a partially compromised kernel, trust needs to be rooted, for ...
... the operating system as one compromised operating system component can easily compromise other components of the kernel without the need for further vulnerabilities. To enforce isolation of operating system components even in the event of a partially compromised kernel, trust needs to be rooted, for ...
Process
... Disadvantage: Creating a user thread requires creating the corresponding kernel thread. There is an overhead related with creating kernel thread which can be burden on theDistributed performance. Univ. of Tehran ...
... Disadvantage: Creating a user thread requires creating the corresponding kernel thread. There is an overhead related with creating kernel thread which can be burden on theDistributed performance. Univ. of Tehran ...
Module 7: Process Synchronization
... waiting to acquire a resource held by another process in the set. Example System has 2 tape drives. P1 and P2 each hold one tape drive and each needs another ...
... waiting to acquire a resource held by another process in the set. Example System has 2 tape drives. P1 and P2 each hold one tape drive and each needs another ...
A Case for High Performance Computing with Virtual
... industry and research communities. A VM environment provides virtualized hardware interfaces to VMs through a Virtual Machine Monitor (VMM) (also called hypervisor). VM technologies allow running different guest VMs in a physical box, with each guest VM possibly running a different guest operating s ...
... industry and research communities. A VM environment provides virtualized hardware interfaces to VMs through a Virtual Machine Monitor (VMM) (also called hypervisor). VM technologies allow running different guest VMs in a physical box, with each guest VM possibly running a different guest operating s ...
CS311 - NUS School of Computing
... application program is running.” “The OS may be split into a kernel which is always present and various system programs which use facilities provided by the kernel to perform higher-level housekeeping tasks, often acting as servers in a client-server relationship.” “Some would include a graphical us ...
... application program is running.” “The OS may be split into a kernel which is always present and various system programs which use facilities provided by the kernel to perform higher-level housekeeping tasks, often acting as servers in a client-server relationship.” “Some would include a graphical us ...
PPT
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space ...
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space ...
Lecture 04 Operating System
... Can a multithreaded solution using user-level threads achieve better performance on a multiprocessor system than on a single processor system? Explain? ...
... Can a multithreaded solution using user-level threads achieve better performance on a multiprocessor system than on a single processor system? Explain? ...