Cisco Product Quick Reference Guide
... Designed for our Cisco field and partners, this guide will help you determine which Cisco product, service, or solution is right for your customer. It is also ideal for end users, networking professionals, Cisco Networking Academy members, and those studying for Cisco certification needing a broad, ...
... Designed for our Cisco field and partners, this guide will help you determine which Cisco product, service, or solution is right for your customer. It is also ideal for end users, networking professionals, Cisco Networking Academy members, and those studying for Cisco certification needing a broad, ...
PDF - Complete Book (2.87 MB)
... Internet Generation, Enterprise/Solver, EtherChannel, EtherSwitch, Fast Step, GigaStack, Internet Quotient, IOS, IP/TV, iQ Expertise, LightStream, MGX, MICA, the Networkers logo, Network Registrar, Packet, PIX, Post-Routing, Pre-Routing, RateMUX, Registrar, SlideCast, StrataView Plus, Stratm, Switch ...
... Internet Generation, Enterprise/Solver, EtherChannel, EtherSwitch, Fast Step, GigaStack, Internet Quotient, IOS, IP/TV, iQ Expertise, LightStream, MGX, MICA, the Networkers logo, Network Registrar, Packet, PIX, Post-Routing, Pre-Routing, RateMUX, Registrar, SlideCast, StrataView Plus, Stratm, Switch ...
motorola solutions wing 5.4.1 cli reference guide
... program delivered hereunder (licensed program). Except as noted below, such license may not be assigned, sublicensed, or otherwise transferred by the user without prior written consent of Motorola Solutions. No right to copy a licensed program in whole or in part is granted, except as permitted unde ...
... program delivered hereunder (licensed program). Except as noted below, such license may not be assigned, sublicensed, or otherwise transferred by the user without prior written consent of Motorola Solutions. No right to copy a licensed program in whole or in part is granted, except as permitted unde ...
SSG5 and SSG20 Secure Services Gateways
... is delivered by proven unified threat management (UTM) security features that are backed by best-in-class partners. To address internal security requirements and facilitate regulatory compliance, the SSG5 and SSG20 both support an advanced set of network protection features such as security zones, v ...
... is delivered by proven unified threat management (UTM) security features that are backed by best-in-class partners. To address internal security requirements and facilitate regulatory compliance, the SSG5 and SSG20 both support an advanced set of network protection features such as security zones, v ...
N450 WiFi Cable Modem Router N450/CG2000Dv2 User Manual
... Note: The contact information listed might change. You can also find the contact number in your monthly Internet service billing statement. 2. When asked, provide the modem router’s serial number and MAC address located on the product label on the modem router. For more information, see Label on pag ...
... Note: The contact information listed might change. You can also find the contact number in your monthly Internet service billing statement. 2. When asked, provide the modem router’s serial number and MAC address located on the product label on the modem router. For more information, see Label on pag ...
PDF - Complete Book (2.43 MB)
... The following information is for FCC compliance of Class A devices: This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference when the ...
... The following information is for FCC compliance of Class A devices: This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference when the ...
wireless-mod8-Security
... Open Authentication is the default setting. Shared Key Authentication—Allows your client adapter to communicate only with access points that have the same WEP key. This option is available only if Use Static WEP Keys is selected. In shared key authentication, the access point sends a known unencrypt ...
... Open Authentication is the default setting. Shared Key Authentication—Allows your client adapter to communicate only with access points that have the same WEP key. This option is available only if Use Static WEP Keys is selected. In shared key authentication, the access point sends a known unencrypt ...
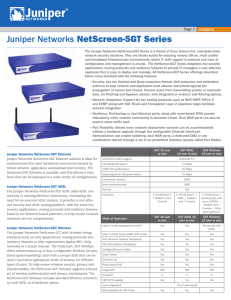
Juniper Networks NetScreen-5GT Series Datasheet
... applications, routing protocols and resiliency features to provide IT managers a cost effective appliance that is easy to deploy and manage. All NetScreen-5GT Series offerings described below come standard with the following features: • Security: Use the Stateful and Deep Inspection firewall, DoS pr ...
... applications, routing protocols and resiliency features to provide IT managers a cost effective appliance that is easy to deploy and manage. All NetScreen-5GT Series offerings described below come standard with the following features: • Security: Use the Stateful and Deep Inspection firewall, DoS pr ...
User Guide Verizon FiOS®Router Model 9100EM
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to Part 15 of the Federal Communication Commission (FCC) Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipm ...
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to Part 15 of the Federal Communication Commission (FCC) Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipm ...
Seahorse XFp Analyzer User Guide
... The XFp Analyzer uses optical detection technology to measure extremely low levels of fluorescent emission from analyte sensors. Therefore, although the instrument has been designed to shield room light, excessive light (such as direct sunlight) should be avoided. ...
... The XFp Analyzer uses optical detection technology to measure extremely low levels of fluorescent emission from analyte sensors. Therefore, although the instrument has been designed to shield room light, excessive light (such as direct sunlight) should be avoided. ...
Wireless Networking Technologies
... Physical – transmission errors and interference Sridhar Iyer ...
... Physical – transmission errors and interference Sridhar Iyer ...
Cisco RV180/RV180W Administration Guide
... The Cisco RV180/RV180W incorporates a Stateful Packet Inspection (SPI)-based router with Denial of Service (DoS) prevention and a Virtual Private Network (VPN) engine for secure communication between mobile or remote workers and branch offices. The Cisco RV180/RV180W supports up to ten gateway-to-ga ...
... The Cisco RV180/RV180W incorporates a Stateful Packet Inspection (SPI)-based router with Denial of Service (DoS) prevention and a Virtual Private Network (VPN) engine for secure communication between mobile or remote workers and branch offices. The Cisco RV180/RV180W supports up to ten gateway-to-ga ...
ZigBee: Home Wireless Control Made Simple
... Freescale Semiconductor Confidential and Proprietary Information. Freescale™ and the Freescale logo are trademarks of Freescale Semiconductor, Inc. All other product or service names are the property of their respective owners. © Freescale Semiconductor, Inc. 2005. ...
... Freescale Semiconductor Confidential and Proprietary Information. Freescale™ and the Freescale logo are trademarks of Freescale Semiconductor, Inc. All other product or service names are the property of their respective owners. © Freescale Semiconductor, Inc. 2005. ...
Wireless Design - Kenneth M. Chipps Ph.D. Home Page
... • The way to start any network design is to apply a top down approach that relates the business needs of the organization to the technical implementation of the network • Based on this systematic design approach a physical network is laid out on paper • The discussion here is the changes to this net ...
... • The way to start any network design is to apply a top down approach that relates the business needs of the organization to the technical implementation of the network • Based on this systematic design approach a physical network is laid out on paper • The discussion here is the changes to this net ...
Cisco WRVS4400N Wireless-N Gigabit Security Router
... your network into multiple IP subnets to increase the intranet throughput and reduce the size of the IP broadcast domain and its interference. In this case, you need one WRVS4400Nv2 for each subnetwork and you can connect all the WAN ports to a second level Router or switch to the Internet. Note tha ...
... your network into multiple IP subnets to increase the intranet throughput and reduce the size of the IP broadcast domain and its interference. In this case, you need one WRVS4400Nv2 for each subnetwork and you can connect all the WAN ports to a second level Router or switch to the Internet. Note tha ...
Fit AP networking
... The AP5030DN provides 802.11n/ac wireless access networks for places with simple building structure, small size, dense users, and high capacity demands, such as small and medium enterprises and branches.The AP5030DN can be flexibly deployed and works in both Fit AP and bridge mode. ...
... The AP5030DN provides 802.11n/ac wireless access networks for places with simple building structure, small size, dense users, and high capacity demands, such as small and medium enterprises and branches.The AP5030DN can be flexibly deployed and works in both Fit AP and bridge mode. ...
IPv6 Deployment Status in KT/Korea
... • Premium network separate from Kornet – IPv6 over MPLS at PE of Premium network first and then full IPv6 functions enabled over the premium network – Part of access network/Kornet is not ready yet for IPv6 and will take some time to be ready for IPv6 ...
... • Premium network separate from Kornet – IPv6 over MPLS at PE of Premium network first and then full IPv6 functions enabled over the premium network – Part of access network/Kornet is not ready yet for IPv6 and will take some time to be ready for IPv6 ...
6LoWPAN: The Wireless Embedded Internet
... Wiley also publishes its books in a variety of electronic formats. Some content that appears in print may not be available in electronic books. Designations used by companies to distinguish their products are often claimed as trademarks. All brand names and product names used in this book are trade ...
... Wiley also publishes its books in a variety of electronic formats. Some content that appears in print may not be available in electronic books. Designations used by companies to distinguish their products are often claimed as trademarks. All brand names and product names used in this book are trade ...
PDF
... Setup wizards: Cisco Configuration Assistant includes an easy-to-use telephony setup wizard that allows users to configure IP addressing functions such as the WAN IP address and the voice and data VLAN IP address. The wizard also adds configuration options for automated attendant, business schedules ...
... Setup wizards: Cisco Configuration Assistant includes an easy-to-use telephony setup wizard that allows users to configure IP addressing functions such as the WAN IP address and the voice and data VLAN IP address. The wizard also adds configuration options for automated attendant, business schedules ...
AltitudeTM 35x0 Access Point Product Reference Guide, Software
... This guide provides configuration and setup information for the Extreme Networks® Altitude™ 3510 Access Point and Altitude 3550 Access Point. For the purposes of this guide, the devices will be called the generic term “access point” when identical configuration activities are applied to both models. ...
... This guide provides configuration and setup information for the Extreme Networks® Altitude™ 3510 Access Point and Altitude 3550 Access Point. For the purposes of this guide, the devices will be called the generic term “access point” when identical configuration activities are applied to both models. ...
0110/0111/0115 Access Point
... want these JANUS devices to communicate to a host using standard VT, ANSI, 3270, or 5250 terminal emulation or screen mapping. The access point routes packets from the terminal to the Model 200 Controller, which routes the packets on to the host. TRAKKER Antares UDP Plus terminals These terminals ca ...
... want these JANUS devices to communicate to a host using standard VT, ANSI, 3270, or 5250 terminal emulation or screen mapping. The access point routes packets from the terminal to the Model 200 Controller, which routes the packets on to the host. TRAKKER Antares UDP Plus terminals These terminals ca ...
PDF - Complete Book (2.17 MB)
... The following information is for FCC compliance of Class A devices: This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference when the ...
... The following information is for FCC compliance of Class A devices: This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference when the ...
Sonicwall - Shalimar Infonet
... dynamically update each of these services as new updates become available. All-in-One, Network Security Solutions All-in-one security solutions are available from SonicWALL which are based upon deep packet inspection firewall and IPSec VPN technologies with integrated gateway anti-virus, anti-spywar ...
... dynamically update each of these services as new updates become available. All-in-One, Network Security Solutions All-in-one security solutions are available from SonicWALL which are based upon deep packet inspection firewall and IPSec VPN technologies with integrated gateway anti-virus, anti-spywar ...