(3) Greatest common divisor
... The gcd is an associative function: gcd(a, gcd(b, c)) = gcd(gcd(a, b), c). The gcd of three numbers can be computed as gcd(a, b, c) = gcd(gcd(a, b), c), or in some different way by applying commutativity and associativity. This can be extended to any number of numbers. gcd(a, b) is closely related t ...
... The gcd is an associative function: gcd(a, gcd(b, c)) = gcd(gcd(a, b), c). The gcd of three numbers can be computed as gcd(a, b, c) = gcd(gcd(a, b), c), or in some different way by applying commutativity and associativity. This can be extended to any number of numbers. gcd(a, b) is closely related t ...
26 Optimal Bounds for Johnson-Lindenstrauss
... is a remarkable result because the target dimension is independent of n. Because the transform is linear, it also preserves the pairwise distances of the vectors in this set, which is what is needed for most applications. The projection matrix is itself produced by a random process that is oblivious ...
... is a remarkable result because the target dimension is independent of n. Because the transform is linear, it also preserves the pairwise distances of the vectors in this set, which is what is needed for most applications. The projection matrix is itself produced by a random process that is oblivious ...
Short signatures from the Weil pairing
... The second row shows that we can get a signature of length 154 bits with security comparable to 320-bit DSA or 320-bit ECDSA. The best known algorithm to forge a 154-bit signature requires one to solve a CDH problem in a finite field of size 923 bits or on an elliptic curve group of size 151 bits. I ...
... The second row shows that we can get a signature of length 154 bits with security comparable to 320-bit DSA or 320-bit ECDSA. The best known algorithm to forge a 154-bit signature requires one to solve a CDH problem in a finite field of size 923 bits or on an elliptic curve group of size 151 bits. I ...
Neighborly Polytopes and Sparse Solution of Underdetermined
... In this corollary, P is the convex hull of a random set of points together with their antipodes. The points are uniformly-distributed on the sphere. This is a natural model of ‘uniform random centrosymmetric polytope’ in dimension d with 2n vertices. From that perspective, Corollary 1.2 shows that ‘ ...
... In this corollary, P is the convex hull of a random set of points together with their antipodes. The points are uniformly-distributed on the sphere. This is a natural model of ‘uniform random centrosymmetric polytope’ in dimension d with 2n vertices. From that perspective, Corollary 1.2 shows that ‘ ...
COMPUTING THE SMITH FORMS OF INTEGER MATRICES AND
... has been steadily improved in the past four decades. A group of algorithms for computing the Smith forms is available now. The best asymptotic algorithm may not always yield the best practical run time. In spite of their different asymptotic complexities, different algorithms are favorable to differ ...
... has been steadily improved in the past four decades. A group of algorithms for computing the Smith forms is available now. The best asymptotic algorithm may not always yield the best practical run time. In spite of their different asymptotic complexities, different algorithms are favorable to differ ...
PseudoCode - WordPress.com
... – Read in a number and check if it’s a prime number. – What’s a prime number? – A number that’s only divisible by itself and 1, e.g. 7. – Or to put it another way, every number other than itself and 1 gives a remainder, e.g. For 7, if 6, 5, 4, 3, and 2 give a remainder then 7 is prime. – So all we n ...
... – Read in a number and check if it’s a prime number. – What’s a prime number? – A number that’s only divisible by itself and 1, e.g. 7. – Or to put it another way, every number other than itself and 1 gives a remainder, e.g. For 7, if 6, 5, 4, 3, and 2 give a remainder then 7 is prime. – So all we n ...
INF120Lec08_Methods2
... Liang, Introduction to Java Programming, Ninth Edition, (c) 2013 Pearson Education, Inc. All rights reserved. ...
... Liang, Introduction to Java Programming, Ninth Edition, (c) 2013 Pearson Education, Inc. All rights reserved. ...
Public-key encryption
... class NP: – problems solvable with an algorithm that is non-deterministic and run in p-time on a non-deterministic machine – problems in NP have no known deterministic p-time algorithms • asymptotic worst case complexity of the most efficient algorithms known is often an exponential function of th ...
... class NP: – problems solvable with an algorithm that is non-deterministic and run in p-time on a non-deterministic machine – problems in NP have no known deterministic p-time algorithms • asymptotic worst case complexity of the most efficient algorithms known is often an exponential function of th ...
Performance Analysis of a Heterogeneous Traffic Scheduler
... problem, we use the large deviation theory. According to the property of large deviation, we reformulate the quality-of-service (QoS) constraint of delay-sensitive and guaranteed-throughput traffic in terms of the asymptotic decay rate of the queue-overflow probability as B approaches infinity. Part ...
... problem, we use the large deviation theory. According to the property of large deviation, we reformulate the quality-of-service (QoS) constraint of delay-sensitive and guaranteed-throughput traffic in terms of the asymptotic decay rate of the queue-overflow probability as B approaches infinity. Part ...
Solving Problems with Magma
... solved using the Magma language and intrinsics. It is hoped that by studying these examples, especially those in your specialty, you will gain a practical understanding of how to express mathematical problems in Magma terms. Most of the examples have arisen from genuine research questions, some of w ...
... solved using the Magma language and intrinsics. It is hoped that by studying these examples, especially those in your specialty, you will gain a practical understanding of how to express mathematical problems in Magma terms. Most of the examples have arisen from genuine research questions, some of w ...
An Efficient Scheme for Proving a Shuffle
... g̃j Aji mod p i = 1, . . . , n g̃ 0 = g̃ α g0 = gα m0 = y α ...
... g̃j Aji mod p i = 1, . . . , n g̃ 0 = g̃ α g0 = gα m0 = y α ...
Matched Field Processing Based on Least Squares with a Small
... the right singular vectors, and they all have specific physical meanings in our problem: the former M singular vectors correspond to the M modes of acoustic fields, and the last one is least square solution, usually it is called total least square solution [15–18] ...
... the right singular vectors, and they all have specific physical meanings in our problem: the former M singular vectors correspond to the M modes of acoustic fields, and the last one is least square solution, usually it is called total least square solution [15–18] ...
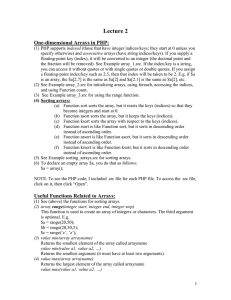
PHP
... (1) PHP supports indexed (those that have integer indices/keys; they start at 0 unless you specify otherwise) and associative arrays (have string indices/keys). If you supply a floating-point key (index), it will be converted to an integer (the decimal point and the fraction will be removed). See Ex ...
... (1) PHP supports indexed (those that have integer indices/keys; they start at 0 unless you specify otherwise) and associative arrays (have string indices/keys). If you supply a floating-point key (index), it will be converted to an integer (the decimal point and the fraction will be removed). See Ex ...
pptx
... 1. Generate random population of chromosomes 2. Until the end condition is met, create a new population by repeating following steps 1. Evaluate the fitness of each chromosome 2. Select two parent chromosomes from a population, weighed by their fitness 3. With probability pc cross over the parents t ...
... 1. Generate random population of chromosomes 2. Until the end condition is met, create a new population by repeating following steps 1. Evaluate the fitness of each chromosome 2. Select two parent chromosomes from a population, weighed by their fitness 3. With probability pc cross over the parents t ...
Basic Algorithmic Number Theory
... is that an algorithm to break a cryptosystem is considered devastating even if only a relatively small proportion of ciphertexts are vulnerable to the attack. Two examples of attacks that only apply to a small proportion of ciphertexts are the attack by Boneh, Joux and Nguyen on textbook Elgamal (se ...
... is that an algorithm to break a cryptosystem is considered devastating even if only a relatively small proportion of ciphertexts are vulnerable to the attack. Two examples of attacks that only apply to a small proportion of ciphertexts are the attack by Boneh, Joux and Nguyen on textbook Elgamal (se ...
Fisher–Yates shuffle

The Fisher–Yates shuffle (named after Ronald Fisher and Frank Yates), also known as the Knuth shuffle (after Donald Knuth), is an algorithm for generating a random permutation of a finite set—in plain terms, for randomly shuffling the set. A variant of the Fisher–Yates shuffle, known as Sattolo's algorithm, may be used to generate random cyclic permutations of length n instead. The Fisher–Yates shuffle is unbiased, so that every permutation is equally likely. The modern version of the algorithm is also rather efficient, requiring only time proportional to the number of items being shuffled and no additional storage space.Fisher–Yates shuffling is similar to randomly picking numbered tickets (combinatorics: distinguishable objects) out of a hat without replacement until there are none left.