Linux Clustering with with CSM and GPFS d GPFS
... International Technical Support Organization Linux Clustering with CSM and GPFS January 2004 ...
... International Technical Support Organization Linux Clustering with CSM and GPFS January 2004 ...
Linux Clustering with CSM and GPFS
... International Technical Support Organization Linux Clustering with CSM and GPFS December 2002 ...
... International Technical Support Organization Linux Clustering with CSM and GPFS December 2002 ...
Beowulf Cluster Computing with Linux (Scientific and Engineering
... Beowulf hardware, operating system software, programming approaches and libraries, and machine management software are all covered here. The book can be used as an academic textbook as well as a practical guide for designing, implementing, and operating a Beowulf for those in science and industry wh ...
... Beowulf hardware, operating system software, programming approaches and libraries, and machine management software are all covered here. The book can be used as an academic textbook as well as a practical guide for designing, implementing, and operating a Beowulf for those in science and industry wh ...
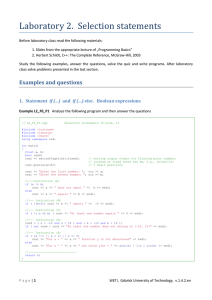
Laboratory 2. Selection statements
... lines of the instruction are skipped? Are conditional statements necessary when using some functions of cmath library? If so, then why? c) Modify conditions in instructions (A), (B) and (C) to obtain logically equivalent conditions without negation operator ( ! , not ). d) Now, modify condition in ( ...
... lines of the instruction are skipped? Are conditional statements necessary when using some functions of cmath library? If so, then why? c) Modify conditions in instructions (A), (B) and (C) to obtain logically equivalent conditions without negation operator ( ! , not ). d) Now, modify condition in ( ...
Outfitting an Inter-AS Topology to a Network of DDoS Countermeasures
... RBF. The two ASes, which are placed in the left upper side on Fig. 4, are isolated from other JP domain ASes. The isolated island problem makes it difficult to identify troubles in setting eBGP configurations and / or running an experiment. This problem occurs when an AS is connected to another AS o ...
... RBF. The two ASes, which are placed in the left upper side on Fig. 4, are isolated from other JP domain ASes. The isolated island problem makes it difficult to identify troubles in setting eBGP configurations and / or running an experiment. This problem occurs when an AS is connected to another AS o ...
Using extended feature objects for partial similarity
... therefore determine the extended feature objects which correspond to the polygon sections starting anywhere on the first edge and ending anywhere on the last edge. Since we have two continuous parameters, the extended feature objects are 2D objects in multidimensional feature space. The 2D feature o ...
... therefore determine the extended feature objects which correspond to the polygon sections starting anywhere on the first edge and ending anywhere on the last edge. Since we have two continuous parameters, the extended feature objects are 2D objects in multidimensional feature space. The 2D feature o ...
Netcool/Impact: Solutions Guide
... Installing Netcool/Impact and the DB2 database Installing the Discovery Library Toolkit. . . . Event Isolation and Correlation policies . . . Event Isolation and Correlation operator views . Configuring Event Isolation and Correlation data sources . . . . . . . . . . . . . . Configuring Event Isolat ...
... Installing Netcool/Impact and the DB2 database Installing the Discovery Library Toolkit. . . . Event Isolation and Correlation policies . . . Event Isolation and Correlation operator views . Configuring Event Isolation and Correlation data sources . . . . . . . . . . . . . . Configuring Event Isolat ...
Document
... Able to tell what an algorithm is and have some understanding why we study algorithms ...
... Able to tell what an algorithm is and have some understanding why we study algorithms ...
CROSS-LAYER MODELING AND OPTIMIZATION OF NEXT-GENERATION INTERNET NETWORKS a dissertation
... To address these issues and in an attempt to move toward next-generation network architectures, this thesis focuses on the modeling, optimization and performance analysis of a set of potential technologies to be deployed in future cross-layer network architectures. By applying a transversal design a ...
... To address these issues and in an attempt to move toward next-generation network architectures, this thesis focuses on the modeling, optimization and performance analysis of a set of potential technologies to be deployed in future cross-layer network architectures. By applying a transversal design a ...
PDF
... is not the degree spectrum of any structure, a fact established in unpublished work of Knight and others [personal communication] and by Soskov [108]. Thus it becomes interesting to ask whether certain natural upwards-closed classes of degrees can be degree spectra of structures. (For a broader surv ...
... is not the degree spectrum of any structure, a fact established in unpublished work of Knight and others [personal communication] and by Soskov [108]. Thus it becomes interesting to ask whether certain natural upwards-closed classes of degrees can be degree spectra of structures. (For a broader surv ...