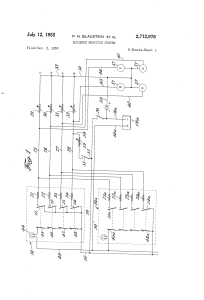
Audience reaction system
... like or interest and disinterest, or any other reactions iiow through the circuit thus closed will depend upon to the different incidents in or portions of the perform ance. These indications from a number of the viewing î’î the number of switch box resistances which are thrown in parallel. ln this ...
... like or interest and disinterest, or any other reactions iiow through the circuit thus closed will depend upon to the different incidents in or portions of the perform ance. These indications from a number of the viewing î’î the number of switch box resistances which are thrown in parallel. ln this ...
Enterprise Ethernet Switch/Routers using PowerPC
... The goals of VLANs are to control broadcasts, which can increase available network bandwidth, and to group the nodes into groups that make logical sense. For example, people who are in the same department, have the same jobs, or share common resources (servers, printers, and so on). Layer 3 switchin ...
... The goals of VLANs are to control broadcasts, which can increase available network bandwidth, and to group the nodes into groups that make logical sense. For example, people who are in the same department, have the same jobs, or share common resources (servers, printers, and so on). Layer 3 switchin ...
William Stallings Data and Computer Communications
... the previous three stage switch compared to the crossbar matrix? How many calls can simultaneously be supported in each? ...
... the previous three stage switch compared to the crossbar matrix? How many calls can simultaneously be supported in each? ...
Switches part 1 File
... • Stores the first 64 bytes of the frame before forwarding. • The first 64 bytes of the frame is where most network errors and collisions occur. • Checks for a collision before forwarding the frame. • Some switches are configured to use cut-through on each port until a user defined error threshold i ...
... • Stores the first 64 bytes of the frame before forwarding. • The first 64 bytes of the frame is where most network errors and collisions occur. • Checks for a collision before forwarding the frame. • Some switches are configured to use cut-through on each port until a user defined error threshold i ...
Chapter 1
... • Stores the first 64 bytes of the frame before forwarding. • The first 64 bytes of the frame is where most network errors and collisions occur. • Checks for a collision before forwarding the frame. • Some switches are configured to use cut-through on each port until a user defined error threshold i ...
... • Stores the first 64 bytes of the frame before forwarding. • The first 64 bytes of the frame is where most network errors and collisions occur. • Checks for a collision before forwarding the frame. • Some switches are configured to use cut-through on each port until a user defined error threshold i ...
Expl_Sw_chapter_02_Switches_Part_I
... • Stores the first 64 bytes of the frame before forwarding. • The first 64 bytes of the frame is where most network errors and collisions occur. • Checks for a collision before forwarding the frame. • Some switches are configured to use cut-through on each port until a user defined error threshold i ...
... • Stores the first 64 bytes of the frame before forwarding. • The first 64 bytes of the frame is where most network errors and collisions occur. • Checks for a collision before forwarding the frame. • Some switches are configured to use cut-through on each port until a user defined error threshold i ...
Ethernet Data Link Layer Standards
... 5-6. Add to your design in the previous question. Add another client next to the first client. Both connect to the same switch. This second client will also communicate with the server and will also need 800 Mbps in transmission speed. Again, your design will specify the locations of switches and th ...
... 5-6. Add to your design in the previous question. Add another client next to the first client. Both connect to the same switch. This second client will also communicate with the server and will also need 800 Mbps in transmission speed. Again, your design will specify the locations of switches and th ...
iPMCC - The Economic Times
... we are no longer dependable on the health of one switch. In the improbable case of a switch failure communications with the different nodes will follow the alternative path through the second switch. Tests show a typical recovery time of 500 ms. When carrying out a great number of tests, the worst c ...
... we are no longer dependable on the health of one switch. In the improbable case of a switch failure communications with the different nodes will follow the alternative path through the second switch. Tests show a typical recovery time of 500 ms. When carrying out a great number of tests, the worst c ...
Basic Switch Concept
... frame is set to all ones. (MAC address is FF-FF-FFFF-FF-FF ) • When a switch receives a broadcast frame, it forwards the frame to each of its ports, except the incoming port where the switch received the ...
... frame is set to all ones. (MAC address is FF-FF-FFFF-FF-FF ) • When a switch receives a broadcast frame, it forwards the frame to each of its ports, except the incoming port where the switch received the ...
Repeaters, Switches and Routers
... extremely fast switching but often increases the number of errors, especially on a busy network Errors take a heavy toll on the network ...
... extremely fast switching but often increases the number of errors, especially on a busy network Errors take a heavy toll on the network ...
NENA NG911 arch for SDO workshop
... Recognize local (and maybe home) dialstrings as emergency calls Mark emergency calls with service URN Try to update location and LoST mapping at call time, use cached values if needed Several other SIP things to support PSAP operations on calls Support manual override of determined location, but mak ...
... Recognize local (and maybe home) dialstrings as emergency calls Mark emergency calls with service URN Try to update location and LoST mapping at call time, use cached values if needed Several other SIP things to support PSAP operations on calls Support manual override of determined location, but mak ...
Catalyst 3512 XL, 3524, and 3548 XL Stackable 10/100 and Gigabit
... Users can also implement higher levels of data security and boost LAN performance by deploying up to 250 virtual LANs ...
... Users can also implement higher levels of data security and boost LAN performance by deploying up to 250 virtual LANs ...
PDF
... Cisco Services Available with Cisco IOS Software and the IP Base image, the Cisco Catalyst Blade Switch 3120 products offer a complete set of intelligent services to deliver security, quality of service (QoS), and high availability in the server farm access environment. The IP Base feature set inclu ...
... Cisco Services Available with Cisco IOS Software and the IP Base image, the Cisco Catalyst Blade Switch 3120 products offer a complete set of intelligent services to deliver security, quality of service (QoS), and high availability in the server farm access environment. The IP Base feature set inclu ...
Document
... – individual endpoints (hosts/phones) generate small quantities of data traffic – Costs should be kept low for end users ...
... – individual endpoints (hosts/phones) generate small quantities of data traffic – Costs should be kept low for end users ...
Why Big Data Needs Big Buffer Switches
... running on server clusters with many-to-many communication patterns. The key to achieving predictable performance for these distributed applications is to provide consistent network bandwidth and latency to the various traffic flows since in most cases it is the slowest flow or query completing last ...
... running on server clusters with many-to-many communication patterns. The key to achieving predictable performance for these distributed applications is to provide consistent network bandwidth and latency to the various traffic flows since in most cases it is the slowest flow or query completing last ...
Layer-2-Network Design
... – Independent TX / RX wires for each end node – Independent device traffic in each wire – A second layer of switches can be added to build a hierarchical network that extends the same two benefits above – ALWAYS DESIGN WITH MODULARITY IN MIND ...
... – Independent TX / RX wires for each end node – Independent device traffic in each wire – A second layer of switches can be added to build a hierarchical network that extends the same two benefits above – ALWAYS DESIGN WITH MODULARITY IN MIND ...
A Scalable Fault-Tolerant Layer 2 Data Center Network Fabric
... Forwarding. There are a number of available data forwarding techniques in data center networks. The high-level dichotomy is between creating a Layer 2 network or a Layer 3 network, each with associated tradeoffs. A Layer 3 approach assigns IP addresses to hosts hierarchically based on their directly ...
... Forwarding. There are a number of available data forwarding techniques in data center networks. The high-level dichotomy is between creating a Layer 2 network or a Layer 3 network, each with associated tradeoffs. A Layer 3 approach assigns IP addresses to hosts hierarchically based on their directly ...
How LAN Switches Work
... a 10-Mbps network, then each node may only get a portion of the 10 Mbps if other nodes on the hub want to communicate as well. But with a switch, each node could possibly communicate at the full 10 Mbps. Think about our road analogy. If all of the traffic is coming to a common intersection, then eac ...
... a 10-Mbps network, then each node may only get a portion of the 10 Mbps if other nodes on the hub want to communicate as well. But with a switch, each node could possibly communicate at the full 10 Mbps. Think about our road analogy. If all of the traffic is coming to a common intersection, then eac ...
[cic] [cic ends] I
... in digitised form between the customer’s premises and the nearest local switching point, rather than as an analogue signal. However, where this occurs, the underlying digital technology used remains circuit-based in order to enable telephone calls to be carried and switched over an end to end circui ...
... in digitised form between the customer’s premises and the nearest local switching point, rather than as an analogue signal. However, where this occurs, the underlying digital technology used remains circuit-based in order to enable telephone calls to be carried and switched over an end to end circui ...
ch15 AM3 File
... This is an example of the same switched LAN but divided into three VLANs. The idea of VLAN technology is to divide a LAN into logical, instead of physical, segments. Each VLAN is a work group in the organization. If a user moves from one group to another, there is no need to change the physical conf ...
... This is an example of the same switched LAN but divided into three VLANs. The idea of VLAN technology is to divide a LAN into logical, instead of physical, segments. Each VLAN is a work group in the organization. If a user moves from one group to another, there is no need to change the physical conf ...
Catalyst 6000 Family Release 5.1CSX and 5.2CSX
... port and alerts the user. A unidirectional link occurs when traffic transmitted by one device over a link is received by the neighbor, but traffic from the neighbor is not received. Unidirectional links may cause a variety of problems difficult to troubleshoot , including spanning-tree topology loop ...
... port and alerts the user. A unidirectional link occurs when traffic transmitted by one device over a link is received by the neighbor, but traffic from the neighbor is not received. Unidirectional links may cause a variety of problems difficult to troubleshoot , including spanning-tree topology loop ...
Class Power Points for Chapter #9
... • Flat network problems – A flat internetwork’s security used to be tackled by connecting hubs and switches together with routers. – So it was the router’s job to maintain security. This was pretty ineffective for several reasons. • First, anyone connecting to the physical network could access the n ...
... • Flat network problems – A flat internetwork’s security used to be tackled by connecting hubs and switches together with routers. – So it was the router’s job to maintain security. This was pretty ineffective for several reasons. • First, anyone connecting to the physical network could access the n ...
Telephone exchange

A telephone exchange is a telecommunications system used in the public switched telephone network or in large enterprises. An exchange consists of electronic components and in older systems also human operators that interconnect (switch) telephone subscriber lines or virtual circuits of digital systems to establish telephone calls between subscribers.In the public telecommunication networks a telephone exchange is located in a central office (CO), typically a building used to house the inside plant equipment of potentially several telephone exchanges, each serving a certain geographical exchange area. Central office locations are often identified in North America as wire centers, designating a facility from which a telephone obtains dial tone. For business and billing purposes, telephony carriers also define rate centers, which in larger cities may be clusters of central offices, to define specified geographical locations for determining distance measurements.In the United States and Canada, the Bell System established in the 1940s a uniform system of identifying each telephone exchange with a three-digit exchange code, or central office code, that was used as a prefix to subscriber telephone numbers. All exchanges within a larger region, typically aggregated by state, were assigned a common area code. With the development of international and transoceanic telephone trunks, especially driven by direct customer dialing, similar efforts of systematic organization of the telephone networks occurred in many countries in the mid-20th century.For corporate or enterprise use, a private telephone exchange is often referred to as a private branch exchange (PBX), when it has connections to the public switched telephone network. A PBX is installed in enterprise facilities, typically collocated with large office spaces or within an organizational campus to serve the local private telephone system and any private leased line circuits. Smaller installations might deploy a PBX or key telephone system in the office of a receptionist.




![[cic] [cic ends] I](http://s1.studyres.com/store/data/015504182_1-179e06be61d658df76dea95690048b04-300x300.png)