slides
... Nor shall the LMS brag thou wandrest in pure maths’ shade, when international reviews state that the importance of computational mathematics grow’st. So long as men can breathe, or jobs on amazon EC2 run, So long lives this, and this gives life to thee. Steven Galbraith ...
... Nor shall the LMS brag thou wandrest in pure maths’ shade, when international reviews state that the importance of computational mathematics grow’st. So long as men can breathe, or jobs on amazon EC2 run, So long lives this, and this gives life to thee. Steven Galbraith ...
DCLG (11) 75 Presentation, HM Treasury
... date and robust membership data are available. Calculations will have an effective date of 1 April 2015. • Methodology: Projected Unit Method (PUM). Standard actuarial methodology with one year control period. PUM measures the cost of accrual and avoids emphasis on any one category of membership. It ...
... date and robust membership data are available. Calculations will have an effective date of 1 April 2015. • Methodology: Projected Unit Method (PUM). Standard actuarial methodology with one year control period. PUM measures the cost of accrual and avoids emphasis on any one category of membership. It ...
Teaching Cryptologic Mathematics
... standard computational complexity classes may be introduced. As a side excursion, it is possible to explain digital signatures based on RSA cipher. Digital signatures also allow the introduction of a specific kind of one-way function called hash. A hash function is a map h from a long input x to a m ...
... standard computational complexity classes may be introduced. As a side excursion, it is possible to explain digital signatures based on RSA cipher. Digital signatures also allow the introduction of a specific kind of one-way function called hash. A hash function is a map h from a long input x to a m ...
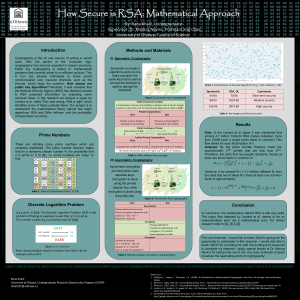
Genigraphics Research Poster Template 44x44
... unknown flaws. In this research we analyze a paper by Lenstra et al. called "Ron was wrong, Whit is right" which identifies some of these potential flaws. Our project is to understand the mathematical theory behind two major algorithms: RSA and Diffie Hellman, with the probability of these flaws occ ...
... unknown flaws. In this research we analyze a paper by Lenstra et al. called "Ron was wrong, Whit is right" which identifies some of these potential flaws. Our project is to understand the mathematical theory behind two major algorithms: RSA and Diffie Hellman, with the probability of these flaws occ ...
CMSD Aspiring Principal Program
... We are preparing leaders for anticipated principal openings in 2016 The summer intensive and residency year are pass/fail Participants must attend the entire 5 week summer program CMSD is developing an APP contract and MOU that will address specifics such as seniority and right to return should a pa ...
... We are preparing leaders for anticipated principal openings in 2016 The summer intensive and residency year are pass/fail Participants must attend the entire 5 week summer program CMSD is developing an APP contract and MOU that will address specifics such as seniority and right to return should a pa ...
Foundations of Cryptography Lecture 2
... • Show a one-way function f such that given y=f(x) each input bit of x can be guessed with probability at least 3/4 ...
... • Show a one-way function f such that given y=f(x) each input bit of x can be guessed with probability at least 3/4 ...
pdf
... master secret key is d such that ed = 1 mod ϕ(N ). A user with identity ID is given secret key SKID = H(ID)d mod N (where H is modeled as a random oracle); this user can now sign messages with respect to his identity by using the Guillou-Quisquater (GQ) signature scheme (this was the scheme from Hom ...
... master secret key is d such that ed = 1 mod ϕ(N ). A user with identity ID is given secret key SKID = H(ID)d mod N (where H is modeled as a random oracle); this user can now sign messages with respect to his identity by using the Guillou-Quisquater (GQ) signature scheme (this was the scheme from Hom ...
2002
... of accuracy, and establish consistency of the scheme. (b) By inspection, determine the spatial and temporal order of accuracy of scheme I (you do not need to derive the modified equation). (c) Perform von Neumann stability analyses for schemes I and II, and derive the amplification factors. (d) Expe ...
... of accuracy, and establish consistency of the scheme. (b) By inspection, determine the spatial and temporal order of accuracy of scheme I (you do not need to derive the modified equation). (c) Perform von Neumann stability analyses for schemes I and II, and derive the amplification factors. (d) Expe ...
Problem: Alice and Bob play the following number game. Alice
... integers a1 , a2 , ..., an and asks Alice to tell him the value of x1 a1 + x2 a+, ... + xn an . Then Bob chooses another list of positive integers b1 , b2 , ..., bn and asks Alice for x1 b1 + x2 b2 +, ... + xn bn . Play continues until Bob is able to determine Alice’s numbers. How many rounds will B ...
... integers a1 , a2 , ..., an and asks Alice to tell him the value of x1 a1 + x2 a+, ... + xn an . Then Bob chooses another list of positive integers b1 , b2 , ..., bn and asks Alice for x1 b1 + x2 b2 +, ... + xn bn . Play continues until Bob is able to determine Alice’s numbers. How many rounds will B ...