Top-Down Network Design
... Keith Nabozny is a technology consultant with HP, an adjunct professor at Macomb Community College, and a graduate of Oakland University in Rochester, Michigan. He has three Cisco professional certifications and is a Certified Information Systems Security Professional (CISSP). Keith has supported la ...
... Keith Nabozny is a technology consultant with HP, an adjunct professor at Macomb Community College, and a graduate of Oakland University in Rochester, Michigan. He has three Cisco professional certifications and is a Certified Information Systems Security Professional (CISSP). Keith has supported la ...
Core of the network
... – Problems can not be solved by covering them – Unreliable information led to broken trust amongst users. The naked truth is always better than the best dressed lie ...
... – Problems can not be solved by covering them – Unreliable information led to broken trust amongst users. The naked truth is always better than the best dressed lie ...
project report
... The growth of the Internet has been a phenomenon, which has been receiving a lot of analysis and discussion these past few years. Few who have been working with it from it's inception as ARPANET predicted this expansion, especially as the concept of a packet switched network was created by the milit ...
... The growth of the Internet has been a phenomenon, which has been receiving a lot of analysis and discussion these past few years. Few who have been working with it from it's inception as ARPANET predicted this expansion, especially as the concept of a packet switched network was created by the milit ...
Cisco WRVS4400N Wireless-N Gigabit Security Router
... dynamic IP address has expired, the DHCP server will assign it a new dynamic IP address. Most ISPs use dynamic IP addresses for their customers. By default, the Router’s Internet Connection Type is Obtain an IP automatically (DHCP). For DSL users, many ISPs may require you to log on with a user name ...
... dynamic IP address has expired, the DHCP server will assign it a new dynamic IP address. Most ISPs use dynamic IP addresses for their customers. By default, the Router’s Internet Connection Type is Obtain an IP automatically (DHCP). For DSL users, many ISPs may require you to log on with a user name ...
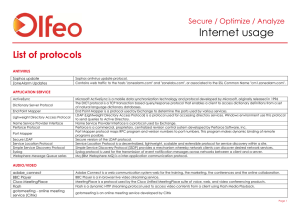
Internet usage
... The FTP protocol is used for reliable data transfer between a client and a server. This protocol is used to transport data in data connection of FTP communication. Secure version of the FTP protocol. GMAIL Drive is a Shell Namespace Extension that creates a virtual file system around your Google Mai ...
... The FTP protocol is used for reliable data transfer between a client and a server. This protocol is used to transport data in data connection of FTP communication. Secure version of the FTP protocol. GMAIL Drive is a Shell Namespace Extension that creates a virtual file system around your Google Mai ...
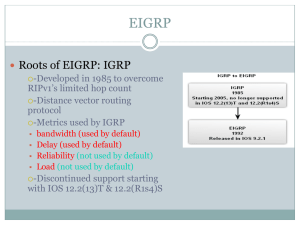
EIGRP
... maintains a list of backup routes it has already determined to be loop-free. If the primary route in the routing table fails, the best backup route is immediately added to the routing table. ...
... maintains a list of backup routes it has already determined to be loop-free. If the primary route in the routing table fails, the best backup route is immediately added to the routing table. ...
Cisco ONS 15305 Multiservice Provisioning Platform for SDH Access Networks
... Internet access – for transport over an STM-1, STM-4, or STM-16 SDH uplink to the central office. The Cisco ONS 15305 can also be deployed as a central office aggregator; consolidating STM-1 access links from Cisco ONS 15310E MA Multiservice Provisioning Platforms or other Cisco ONS 15305 CPE, as we ...
... Internet access – for transport over an STM-1, STM-4, or STM-16 SDH uplink to the central office. The Cisco ONS 15305 can also be deployed as a central office aggregator; consolidating STM-1 access links from Cisco ONS 15310E MA Multiservice Provisioning Platforms or other Cisco ONS 15305 CPE, as we ...
Communications Server for z/OS V1R2 TCP/IP
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. © Copyright International Business Machines Corporation 2002. All rights reserved. Note to U.S Government Users - Doc ...
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. © Copyright International Business Machines Corporation 2002. All rights reserved. Note to U.S Government Users - Doc ...
D1.1: Functional Architecture Definition and Top Level
... blocks, enabling him to implement relative packet differentiation. However, it is not clear yet how “real” customer services, such as interactive multimedia including voice over IP, can be build on top of this. The DiffServ architecture has some shortcomings at this time. Deploying QoS sensitive cus ...
... blocks, enabling him to implement relative packet differentiation. However, it is not clear yet how “real” customer services, such as interactive multimedia including voice over IP, can be build on top of this. The DiffServ architecture has some shortcomings at this time. Deploying QoS sensitive cus ...
On Networks N300 WiFi Router(N300R) User Manual
... Brand and product names are trademarks or registered trademarks of their respective holders. Information is subject to change without notice. In the interest of improving internal design, operational function, and/or reliability, On Networks reserves the right to make changes to the products describ ...
... Brand and product names are trademarks or registered trademarks of their respective holders. Information is subject to change without notice. In the interest of improving internal design, operational function, and/or reliability, On Networks reserves the right to make changes to the products describ ...
Computer Networking : Principles, Protocols and Practice
... A drawback of bus-based networks is that if the bus is physically cut, then the network is split into two isolated networks. For this reason, bus-based networks are sometimes considered to be difficult to operate and maintain, especially when the cable is long and there are many places where it can ...
... A drawback of bus-based networks is that if the bus is physically cut, then the network is split into two isolated networks. For this reason, bus-based networks are sometimes considered to be difficult to operate and maintain, especially when the cable is long and there are many places where it can ...
OSPF
... - Cisco menghitung Cost dgn rumus = 108 / bandwidth interface. - Nilai cost dapat dimanipulasi dalam range 1 s/d 65.535, perintahnya: ip ospf cost ...
... - Cisco menghitung Cost dgn rumus = 108 / bandwidth interface. - Nilai cost dapat dimanipulasi dalam range 1 s/d 65.535, perintahnya: ip ospf cost ...
PAN‐OS Web Interface Reference Guide
... Enter the tag number (0‐4094) or range of tag numbers (tag1‐tag2) for the traffic allowed on the virtual wire. A tag value of zero indicates untagged traffic (the default). Multiple tags or ranges must be separated by commas. Traffic that has an excluded tag value is dropped. Tag values are not ...
... Enter the tag number (0‐4094) or range of tag numbers (tag1‐tag2) for the traffic allowed on the virtual wire. A tag value of zero indicates untagged traffic (the default). Multiple tags or ranges must be separated by commas. Traffic that has an excluded tag value is dropped. Tag values are not ...
INR11%20-%20OSPF
... Routers will only accept routing information from other routers that have been configured with the same password or authentication information ...
... Routers will only accept routing information from other routers that have been configured with the same password or authentication information ...
Powerpoint Slides - Suraj @ LUMS
... Examples of constraints: Do not use links left with less than 7Mb/s bandwidth Do not use blue-colored links for this request Use a path with delay less than 130ms ...
... Examples of constraints: Do not use links left with less than 7Mb/s bandwidth Do not use blue-colored links for this request Use a path with delay less than 130ms ...
PDF - Complete Book (2.38 MB)
... You can use the ip default-gateway global configuration command to define a default gateway when IP routing is disabled on a device. For instance, if a device is a host, you can use this command to define a default gateway for the device. You can also use this command to transfer a Cisco software im ...
... You can use the ip default-gateway global configuration command to define a default gateway when IP routing is disabled on a device. For instance, if a device is a host, you can use this command to define a default gateway for the device. You can also use this command to transfer a Cisco software im ...
TRANSITION FROM IPv4 TO IPv6 LAHTI UNIVERSITY OF APPLIED
... network administrators, board of directors, information executives, or students and network researchers who have an interest in the network communication and would like to join the community of IPv6. Therefore, with the topic “Transition from IPv4 to IPv6: The best method for large enterprise networ ...
... network administrators, board of directors, information executives, or students and network researchers who have an interest in the network communication and would like to join the community of IPv6. Therefore, with the topic “Transition from IPv4 to IPv6: The best method for large enterprise networ ...
Multicasting
... •Reliabiliy requires acknowledgements, since multicastr groups can have an arbitary number of members, traditional reliable protocols require the sender to handle an arbitary number of acknowledgements. This problem is refered to as the ACK Implosion, since no computer has enough processing power to ...
... •Reliabiliy requires acknowledgements, since multicastr groups can have an arbitary number of members, traditional reliable protocols require the sender to handle an arbitary number of acknowledgements. This problem is refered to as the ACK Implosion, since no computer has enough processing power to ...
PDF - Complete Book (2.34 MB)
... to identify and group Network Layer Reachability Information (NLRI) for each topology in updates for a given protocol. In OSPF, EIGRP, and IS-IS, you enter the topology ID during the first configuration of the topology command for a class-specific topology. In BGP, you configure the topology ID by e ...
... to identify and group Network Layer Reachability Information (NLRI) for each topology in updates for a given protocol. In OSPF, EIGRP, and IS-IS, you enter the topology ID during the first configuration of the topology command for a class-specific topology. In BGP, you configure the topology ID by e ...
DEPLOYMENT IPV6 OVER IPV4 NETWORK INFRASTRUCTURE Tien Dung Hoang
... or more than two smaller networks. In a big company or in ISP, each department or customer will have a private subnet to increase security and management. 2.1.2 IPv4 limitation IPv4 only supports 32 bits, so IPv4 cannot respond to address requirements on Internet nowadays. Two major issues IPv4 are ...
... or more than two smaller networks. In a big company or in ISP, each department or customer will have a private subnet to increase security and management. 2.1.2 IPv4 limitation IPv4 only supports 32 bits, so IPv4 cannot respond to address requirements on Internet nowadays. Two major issues IPv4 are ...
LABEL SPACE REDUCTION IN GMPLS AND ALL-OPTICAL LABEL SWAPPING NETWORKS
... another using a Photonic Cross-Connect (PXC), enabling the configuration of optical routes between any pair of WRSs in the network. These optical routes are named lightpaths [Dix03]. The interconnection of these optical elements can be seen in the upper part of Fig. 1. Fig. 1 also shows the forwardi ...
... another using a Photonic Cross-Connect (PXC), enabling the configuration of optical routes between any pair of WRSs in the network. These optical routes are named lightpaths [Dix03]. The interconnection of these optical elements can be seen in the upper part of Fig. 1. Fig. 1 also shows the forwardi ...
Demystifying Layer 2 and Layer 3 VPNs
... 4.3 Business Features of Layer 2 and Layer 3 Services ................................................................................................................................................................... 37 4.3.1 Multi-point Any-to-Any Connectivity ..................................... ...
... 4.3 Business Features of Layer 2 and Layer 3 Services ................................................................................................................................................................... 37 4.3.1 Multi-point Any-to-Any Connectivity ..................................... ...
Practical BGP
... The BGP Peering Process ...................................................................................................................... 20 BGP Attributes ........................................................................................................................................... ...
... The BGP Peering Process ...................................................................................................................... 20 BGP Attributes ........................................................................................................................................... ...
The History of nordunet
... project was to develop a communication protocol that would guide the transmission of data across different networks. The Transmission Control Protocol, tcp, was outlined in 1974 by darpa researchers, and in a few years, it was developed as the tcp/ip Protocol Suite. Later, tcp/ip would become the st ...
... project was to develop a communication protocol that would guide the transmission of data across different networks. The Transmission Control Protocol, tcp, was outlined in 1974 by darpa researchers, and in a few years, it was developed as the tcp/ip Protocol Suite. Later, tcp/ip would become the st ...