Computer Networks Laboratory
... takes place. The data is transmitted via this physical medium to the destination's physical layer. It is responsible for sending data and receiving data across a physical medium. This data is sent in bits, either a 0 or a 1. The data may be transmitted as electrical signals (that is, positive and ne ...
... takes place. The data is transmitted via this physical medium to the destination's physical layer. It is responsible for sending data and receiving data across a physical medium. This data is sent in bits, either a 0 or a 1. The data may be transmitted as electrical signals (that is, positive and ne ...
3GPP report skeleton
... such as DSL, Cellular networks, etc, the gateway is connected to numerous sensors using interface I1. IoT applications are connected to the sensor gateway over the core network. Since the sensors (which are IoT devices/IoT limited devices) perform multiple functions associated with different resourc ...
... such as DSL, Cellular networks, etc, the gateway is connected to numerous sensors using interface I1. IoT applications are connected to the sensor gateway over the core network. Since the sensors (which are IoT devices/IoT limited devices) perform multiple functions associated with different resourc ...
Network Training 2008-05-25
... You may have heard the term 802.3 used in conjunction with the term Ethernet. "Ethernet" originally referred to a networking implementation standardized by Digital, Intel and Xerox. (it is also known as the DIX standard). In February 1980, the Institute of Electrical and Electronics Engineers, or IE ...
... You may have heard the term 802.3 used in conjunction with the term Ethernet. "Ethernet" originally referred to a networking implementation standardized by Digital, Intel and Xerox. (it is also known as the DIX standard). In February 1980, the Institute of Electrical and Electronics Engineers, or IE ...
PPT
... Two types of “links”: point-to-point PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
... Two types of “links”: point-to-point PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
CryptoGuard VPN
... configuration information required for daily use (e.g., filter rules (security policy), connection keys, logbook definitions and so on) into the CryptoGuard VPN device. ...
... configuration information required for daily use (e.g., filter rules (security policy), connection keys, logbook definitions and so on) into the CryptoGuard VPN device. ...
Part I: Introduction - Department of Computer Science and Technology
... plane: JFK to Geneva train: Geneva to Lausanne ...
... plane: JFK to Geneva train: Geneva to Lausanne ...
Routing Protocol vs. Routed Protocol
... • Using the SPF tree, each router can independently determine the shortest path to every network. Distance vector routing protocols do not have a topological map of the network. • Routers implementing a distance vector routing protocol only have a list of networks, which includes the cost (distance) ...
... • Using the SPF tree, each router can independently determine the shortest path to every network. Distance vector routing protocols do not have a topological map of the network. • Routers implementing a distance vector routing protocol only have a list of networks, which includes the cost (distance) ...
Physical and logical topologies. LAN devices.
... Basics LAN devices The evolution of network devices The basics of data flow through LANs The building of LANs ...
... Basics LAN devices The evolution of network devices The basics of data flow through LANs The building of LANs ...
Layer 3 - Ohio Supercomputer Center
... Local Area Network Layer (Layer 3) Internet Protocol (IP) Layer 1 (Layer 2) Local Area Network (LAN) Physical Layer (Layer 1) Physical ...
... Local Area Network Layer (Layer 3) Internet Protocol (IP) Layer 1 (Layer 2) Local Area Network (LAN) Physical Layer (Layer 1) Physical ...
TR 0006 - oneM2M
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
Routing in IPv6 over Low-Power Wireless Personal Area Networks
... the IEEE 802.15.4. However, ZigBee uses the IEEE 802.15.4 standard as its communication protocol for Medium Access Control (MAC) layer and Physical (PHY) layer. IEEE 802.15.4 devices are characterized by low computational power, scarce memory capacity, lower bit rate, short range, and low cost [1]. ...
... the IEEE 802.15.4. However, ZigBee uses the IEEE 802.15.4 standard as its communication protocol for Medium Access Control (MAC) layer and Physical (PHY) layer. IEEE 802.15.4 devices are characterized by low computational power, scarce memory capacity, lower bit rate, short range, and low cost [1]. ...
Layer 3 Protocols
... device that passes data packets between networks, based on Layer 3 addresses. • A router has the ability to make intelligent decisions regarding the best path for delivery of data on the network. ...
... device that passes data packets between networks, based on Layer 3 addresses. • A router has the ability to make intelligent decisions regarding the best path for delivery of data on the network. ...
chapter5
... Two types of “links”: point-to-point PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
... Two types of “links”: point-to-point PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
ICTs: device to device communication
... some of the technologies and issues that you will be encountering later in this course. We're not going to ask you to read the entire article, but we would like you to get an idea of the article's contents, the kind of points the author is making, and the range of issues that it throws up. With this ...
... some of the technologies and issues that you will be encountering later in this course. We're not going to ask you to read the entire article, but we would like you to get an idea of the article's contents, the kind of points the author is making, and the range of issues that it throws up. With this ...
3rd Edition: Chapter 4 - Web Services Overview
... Distance Vector Hierarchical routing 4.6 Routing in the ...
... Distance Vector Hierarchical routing 4.6 Routing in the ...
Motorola Outdoor System Planner
... however this guide looks at the access points from a system level where they can all interact with each other in a multiple access point infrastructure. Motorola’s MCX (MeshConnex™) feature allows access ...
... however this guide looks at the access points from a system level where they can all interact with each other in a multiple access point infrastructure. Motorola’s MCX (MeshConnex™) feature allows access ...
Emerging_Wireless_Standards2
... • These diversity gains can be attained with multiple receive antennas, multiple transmit antennas, or a combination of both. • Beamforming techniques are an alternative to directly increase the desired signal energy while suppressing, or nulling, interfering signals. • In contrast to diversity and ...
... • These diversity gains can be attained with multiple receive antennas, multiple transmit antennas, or a combination of both. • Beamforming techniques are an alternative to directly increase the desired signal energy while suppressing, or nulling, interfering signals. • In contrast to diversity and ...
Link Layer
... multiple access protocol distributed algorithm that determines how nodes share channel, i.e., determine when node can transmit communication about channel sharing must use channel itself! • no out-of-band channel for coordination ...
... multiple access protocol distributed algorithm that determines how nodes share channel, i.e., determine when node can transmit communication about channel sharing must use channel itself! • no out-of-band channel for coordination ...
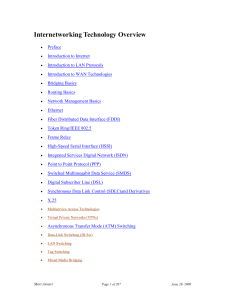
Internetworking Technology Overview
... Implementing a functional internetwork is no simple task. Many challenges must be faced, especially in the areas of connectivity, reliability, network management, and flexibility. Each area is key in establishing an efficient and effective internetwork. The challenge when connecting various systems ...
... Implementing a functional internetwork is no simple task. Many challenges must be faced, especially in the areas of connectivity, reliability, network management, and flexibility. Each area is key in establishing an efficient and effective internetwork. The challenge when connecting various systems ...
Hacking Wireless Networks
... uses the Orthogonal Frequency Division Multiplexing (OFDM) encoding class. The maximum speed supported by the 802.11a standard is 54Mbps. 802.11b: 802.11b is an amendment to the IEEE 802.11 specification that extended the throughput up to 11 Mbit/s using the same 2.4 GHz band. This specification und ...
... uses the Orthogonal Frequency Division Multiplexing (OFDM) encoding class. The maximum speed supported by the 802.11a standard is 54Mbps. 802.11b: 802.11b is an amendment to the IEEE 802.11 specification that extended the throughput up to 11 Mbit/s using the same 2.4 GHz band. This specification und ...
IEC 62591 Wireless Interface Instruction Manual Remote Automation Solutions
... The customer should note that a failure of this instrument or system, for whatever reason, may leave an operating process without protection. Depending upon the application, this could result in possible damage to property or injury to persons. It is suggested that the purchaser review the need for ...
... The customer should note that a failure of this instrument or system, for whatever reason, may leave an operating process without protection. Depending upon the application, this could result in possible damage to property or injury to persons. It is suggested that the purchaser review the need for ...
4 Kyung Hee University Line configuration (cont`d)
... peer-to-peer : the devices share the link equally(ring, mesh) primary-secondary : one device controls traffic and the others must transmit through it (star, tree) ...
... peer-to-peer : the devices share the link equally(ring, mesh) primary-secondary : one device controls traffic and the others must transmit through it (star, tree) ...
Linux+ Guide to Linux Certification
... • Several different IR WLANs have been developed during past 20 years • Infrared WLANs use part of electromagnetic spectrum just below visible light • IR shares these characteristics – Operates at high frequencies – Travels in straight lines – Does not penetrate physical objects ...
... • Several different IR WLANs have been developed during past 20 years • Infrared WLANs use part of electromagnetic spectrum just below visible light • IR shares these characteristics – Operates at high frequencies – Travels in straight lines – Does not penetrate physical objects ...
Packet Tracer Network Simulator
... Cisco Packet Tracer is a network simulator that can be used not just by students but also by instructors and network administrators. This software provides a wide range of Cisco switches and routers running on IOS 12 and IOS 15, wireless devices from Linksys, and several end devices such as PCs and ...
... Cisco Packet Tracer is a network simulator that can be used not just by students but also by instructors and network administrators. This software provides a wide range of Cisco switches and routers running on IOS 12 and IOS 15, wireless devices from Linksys, and several end devices such as PCs and ...