PPT - Purdue Computer Science
... Not a Public Key Encryption system, but can allow A and B to agree on a shared secret in a public channel (with passive, i.e., eavesdropping adversaries) Setup: p prime and g generator of Zp*, p and g public. ga mod p gb mod p ...
... Not a Public Key Encryption system, but can allow A and B to agree on a shared secret in a public channel (with passive, i.e., eavesdropping adversaries) Setup: p prime and g generator of Zp*, p and g public. ga mod p gb mod p ...
Problem: Alice and Bob play the following number game. Alice
... Alice and Bob play the following number game. Alice writes down a list of positive integers x1 , x2 , ..., xn but does not reveal them to Bob, who will try to determine the numbers by asking Alice questions. Bob chooses a list of positive integers a1 , a2 , ..., an and asks Alice to tell him the val ...
... Alice and Bob play the following number game. Alice writes down a list of positive integers x1 , x2 , ..., xn but does not reveal them to Bob, who will try to determine the numbers by asking Alice questions. Bob chooses a list of positive integers a1 , a2 , ..., an and asks Alice to tell him the val ...
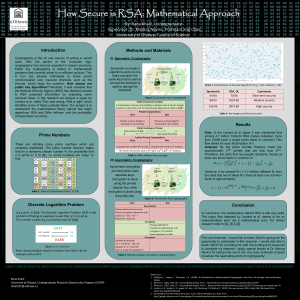
Genigraphics Research Poster Template 44x44
... Cryptography is the art and science of writing in secret code. With the advent of the Computer Age, cryptography has become essential in today's economy. Public key cryptography is based on mathematical problems that currently admit to no efficient solution. This in turn has allowed individuals to s ...
... Cryptography is the art and science of writing in secret code. With the advent of the Computer Age, cryptography has become essential in today's economy. Public key cryptography is based on mathematical problems that currently admit to no efficient solution. This in turn has allowed individuals to s ...
Diffie–Hellman key exchange
Diffie–Hellman key exchange (D–H) is a specific method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols as originally conceptualized by Ralph Merkle. D–H is one of the earliest practical examples of public key exchange implemented within the field of cryptography. The Diffie–Hellman key exchange method allows two parties that have no prior knowledge of each other to jointly establish a shared secret key over an insecure channel. This key can then be used to encrypt subsequent communications using a symmetric key cipher.The scheme was first published by Whitfield Diffie and Martin Hellman in 1976. By 1975, James H. Ellis, Clifford Cocks and Malcolm J. Williamson within GCHQ, the British signals intelligence agency, had also shown how public-key cryptography could be achieved; however, their work was kept secret until 1997.Although Diffie–Hellman key agreement itself is a non-authenticated key-agreement protocol, it provides the basis for a variety of authenticated protocols, and is used to provide perfect forward secrecy in Transport Layer Security's ephemeral modes (referred to as EDH or DHE depending on the cipher suite).The method was followed shortly afterwards by RSA, an implementation of public-key cryptography using asymmetric algorithms.U.S. Patent 4,200,770, from 1977, is now expired and describes the now public domain algorithm. It credits Hellman, Diffie, and Merkle as inventors.