* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download PALMS-CI A Policy-driven Cyberinfrastructure 2010
Survey
Document related concepts
Transcript
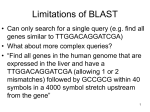
PALMS-CI: A Policy-driven Cyberinfrastructure For the Exposure Biology Community Barry Demchak ([email protected]), Jacqueline Kerr, Gregory Norman, Ernesto Ramirez, Fred Raab, Dane Lotspeich, Ingolf Krüger, and Kevin Patrick California Institute for Telecommunications and Information Technology, San Diego Division This material is based upon work supported by the National Institutes of Health under Grant No 1U01CA130771-01and the National Science Foundation under Grant No CCF-0702791 The Problem The Solution † (CI) Sensor Data Stakeholder Policies Build Cyberinfrastructures to serve stakeholder communities Model-based Policy Elicitation • Support research workflows • Workflows are templates to be customized by stakeholders • Traditional development cycles are long & mis-target stakeholder concerns • Healthy CIs solve all requirements simultaneously & continuously • Stakeholders specify policies directly1,2 on workflow models (UML Activity Diagrams4) using visual 5 Domain Specific Language (DSL ) • Policies specify alternate workflows & data flow transformations • Cross-pollination of other requirement domains PALMS Cyberinfrastructure Service Oriented Architecture logical/deployment models Solve Stakeholder Concerns • • • • • • • • Leverage standard patterns3: strategy, messaging, routing, & composite pattern (i.e., systems-ofsystems) • Leverage role-based interaction, choreography, & interceptor techniques Support emerging workflows Multifactor access control Confidentiality & privacy (HIPAA/IRB) High availability & reliability Scalability (bandwidth/storage/users) Auditability Provenance & curation Challenges PALMS Browser Shared Data Requirement elicitation Policy Concerns • Functional & quality requirements • Crosscutting concerns • Precise & accurate formulation • • • • • Enactment • • • • Low latency to implementation Faithful to original requirement Conflict & error detection Scalable to large data flows • Leverage relationships with other visual notations (e.g., Business Process Modeling Notation) • Alignment with additional policy patterns & domains References Physical Activity Location Measurement System to understand where activity-related energy expenditure occurs in humans as a function of time and space. Harvests data fromf wearable devices on small and large scales, provides framework for research and analysis, and has ultimate goal of discovering methods for engineering better health. †Cyberinfrastructures Expand repertoire of policy patterns Define policy composition rules Code generation and deployment Conflict/completeness checking Scalable and distributed execution Domain Specific Language End-to-end Traceability PALMS Future Work (CI) An Internet-based research computing environment that supports data acquisition, data storage, data management, data integration, data mining, data visualization, and other computing and information processing services. Different f stakeholders produce, consume, manage, and govern a CI, and their requirements must be simultaneously met or else the integrity of the CI degrades. 1. J. Juerjens. Security Systems Development with UML. Springer-Verlag Berlin Heidelberg, 2003. 2. T. Lodderstedt, D. Basin, and J. Doser. SecureUML: A UML-Based Modeling Language for Model-Driven Security. Proceedings of the 5th International Conference on The Unified Modeling Language. pp426-441. Springer Verlag, 2002. 3. M. Arrott, B. Demchak, V. Ermagan, C. Farcas, E. Farcas, I. H. Krüger, and M. Menarini. Rich Services: The Integration Piece of the SOA Puzzle. In Proceedings of the IEEE International Conference on Web Services (ICWS), Salt Lake City, Utah, USA. IEEE, Jul. f 2007, pp. 176-183. 4. A. Bhattacharjee and R. Shyamasundar. Activity Diagrams: A Formal Framework to Model Business Processes and Code Generation. Journal of Object Technology. Vol 8, No 1, Jan 2009. 5. J. Viega. Building security requirements with CLASP. Proceedings of the 2005 Workshop on Software Engineering for Secure Systems – Building Trustworthy Applications. St Louis, MO, 2005.