Lecture 01 of IB Databases Course
... from the University of Michigan in Ann Arbor. He then joined IBM research in San Jose. ...
... from the University of Michigan in Ann Arbor. He then joined IBM research in San Jose. ...
Literacy Exam 3 review.doc
... 12. What is the difference in a device-dependent and a device-independent operating system? Are there any advantages of one over the other? 13. What is the purpose of a personal computer maintenance utility? 14. What is groupware? What features does this provide? 15. What are some advantages of a ne ...
... 12. What is the difference in a device-dependent and a device-independent operating system? Are there any advantages of one over the other? 13. What is the purpose of a personal computer maintenance utility? 14. What is groupware? What features does this provide? 15. What are some advantages of a ne ...
Mid term
... 4. What are the responsibilities of the DBA and the database designers? 5. Specify all the relationships among the records of the database shown in Figure 1.2. 6. Give some additional views that may be needed by other user groups for the database shown in Figure 1.2. 7. Identify some informal querie ...
... 4. What are the responsibilities of the DBA and the database designers? 5. Specify all the relationships among the records of the database shown in Figure 1.2. 6. Give some additional views that may be needed by other user groups for the database shown in Figure 1.2. 7. Identify some informal querie ...
CRSP SuRvivoR-biaS-fRee uS mutual fund databaSe OctOber 2012 quarterly update
... release of the CRSP Survivor-Bias-Free US Mutual Fund Database, and contain data through September 2012. File Version Specifics The database has 51,150 total funds. Of these 29,115 are active and 22,035 are delisted. The mutual fund database is available in SAS and ASCII formats and as a CRSPAccess ...
... release of the CRSP Survivor-Bias-Free US Mutual Fund Database, and contain data through September 2012. File Version Specifics The database has 51,150 total funds. Of these 29,115 are active and 22,035 are delisted. The mutual fund database is available in SAS and ASCII formats and as a CRSPAccess ...
Object Summary
... An OS is a tree comprised of tuples, with the tDS tuple as the root node and t’s neighboring typles the child nodes Based on a Data Subject Schema Graph(GDS) automatically generated for each RDS ...
... An OS is a tree comprised of tuples, with the tDS tuple as the root node and t’s neighboring typles the child nodes Based on a Data Subject Schema Graph(GDS) automatically generated for each RDS ...
File - Ghulam Hassan
... Distributed – databases that are physically distributed in whole or in part to network servers at a variety of sites example is GOOGLE there are two types of Distributed databases: • Partitioned: Separate locations store different parts of database • Replicated: Central database duplicated in entire ...
... Distributed – databases that are physically distributed in whole or in part to network servers at a variety of sites example is GOOGLE there are two types of Distributed databases: • Partitioned: Separate locations store different parts of database • Replicated: Central database duplicated in entire ...
ppt
... Database Management System What is a DBMS ? • A big C program written by someone else that allows us to manage efficiently a large database and allows it to persist over long periods of time Give examples of DBMS • DB2 (IBM), SQL Server (MS), Oracle, Sybase • MySQL, Postgres, … ...
... Database Management System What is a DBMS ? • A big C program written by someone else that allows us to manage efficiently a large database and allows it to persist over long periods of time Give examples of DBMS • DB2 (IBM), SQL Server (MS), Oracle, Sybase • MySQL, Postgres, … ...
DATABASE SECURITY
... that renders the data unreadable by any program without the decryption key. There will be degradation in performance because of the time taken to decode it. It also protects the data transmitted over communication lines. ...
... that renders the data unreadable by any program without the decryption key. There will be degradation in performance because of the time taken to decode it. It also protects the data transmitted over communication lines. ...
Slide 1
... To Connect to a relational database from within Java Application, can be done using JDBC API of Java. It mainly do the following tasks. 1. Establish a connection with a database. 2. Send SQL statements to database server. 3. Process the result obtained. ...
... To Connect to a relational database from within Java Application, can be done using JDBC API of Java. It mainly do the following tasks. 1. Establish a connection with a database. 2. Send SQL statements to database server. 3. Process the result obtained. ...
Database Concepts
... According to a Gartner study in ‘06, Microsoft SQL server had the highest annual growth of any proprietary DBMS at 28% increasing market share from 15.6% to 17.4% ...
... According to a Gartner study in ‘06, Microsoft SQL server had the highest annual growth of any proprietary DBMS at 28% increasing market share from 15.6% to 17.4% ...
Lecture 10 MS-SQL Server Basics
... “default” is first SQL server on this box If need more SQL servers (virtual hosts), use “Named Instance” ...
... “default” is first SQL server on this box If need more SQL servers (virtual hosts), use “Named Instance” ...
Database A database is an organized collection of data. The data is
... only the DBMS and related software. Database servers are usually multiprocessor computers, with generous memory and RAID disk arrays used for stable storage. Hardware database accelerators, connected to one or more servers via a high-speed channel, are also used in large volume transaction processin ...
... only the DBMS and related software. Database servers are usually multiprocessor computers, with generous memory and RAID disk arrays used for stable storage. Hardware database accelerators, connected to one or more servers via a high-speed channel, are also used in large volume transaction processin ...
Database System Concepts, --Silberschatz Korth, Sudarshan, -
... database growth in the hands of database administrators (DBAs) and other specialists. Databases have been in use since the earliest days of electronic computing. Unlike New systems which can be utilized to widely unlike databases and needs, the vast maturity of more previous systems were tightly rel ...
... database growth in the hands of database administrators (DBAs) and other specialists. Databases have been in use since the earliest days of electronic computing. Unlike New systems which can be utilized to widely unlike databases and needs, the vast maturity of more previous systems were tightly rel ...
Data Models
... Is there a type of DBMS whose structure best mirrors that of the underlying data? ...
... Is there a type of DBMS whose structure best mirrors that of the underlying data? ...
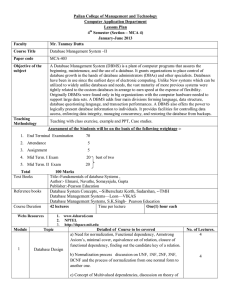
Computer Information System
... 2. Analyze results of processed data and evaluate the method used and results obtained. 3. Enable students to describe advantages and disadvantages of various types of computers, and data storage and peripheral devices. 4. Identify features of Computer Information Systems and basic concepts of compu ...
... 2. Analyze results of processed data and evaluate the method used and results obtained. 3. Enable students to describe advantages and disadvantages of various types of computers, and data storage and peripheral devices. 4. Identify features of Computer Information Systems and basic concepts of compu ...
Introduction to Data Integrity
... Concurrent user access to the same data is one of the most central and vexing issues for applications utilizing databases. Concurrency can affect two of the most important facets of any application: the underlying integrity of the data and the performance of the application system. ...
... Concurrent user access to the same data is one of the most central and vexing issues for applications utilizing databases. Concurrency can affect two of the most important facets of any application: the underlying integrity of the data and the performance of the application system. ...
Introduction to Database Systems
... What is a database ? • A collection of files storing related data Give examples of databases • Accounts database; payroll database; UW’s students database; Amazon’s products database; airline reservation database ...
... What is a database ? • A collection of files storing related data Give examples of databases • Accounts database; payroll database; UW’s students database; Amazon’s products database; airline reservation database ...
Chapter 1
... programs, rather than being stored separately and independently. No control over access and manipulation of data beyond that imposed by application programs. ...
... programs, rather than being stored separately and independently. No control over access and manipulation of data beyond that imposed by application programs. ...
DBMS, ITS FEATURES AND COMPONETNS - MUET-CRP
... systems etc., and so on. It is impossible to implement the DBMS without the hardware devices, in a network, a powerful computer with high data processing speed and a storage device with large storage capacity is required as database server. DATA: Data is the most important component of the DBMS. The ...
... systems etc., and so on. It is impossible to implement the DBMS without the hardware devices, in a network, a powerful computer with high data processing speed and a storage device with large storage capacity is required as database server. DATA: Data is the most important component of the DBMS. The ...
Document - Oman College of Management & Technology
... Each application must have duplicate programs for filehandling operations Duplicate data exists in each application’s data files Duplicate data can become inconsistent ...
... Each application must have duplicate programs for filehandling operations Duplicate data exists in each application’s data files Duplicate data can become inconsistent ...
MS-Access(Basics)
... • A primary key is a field, or a collection of fields, whose values uniquely identify each record in a table • When you include the primary key from one table as a field in a second table to form a relationship between the two tables, it is called a foreign key in the second table New Perspectives o ...
... • A primary key is a field, or a collection of fields, whose values uniquely identify each record in a table • When you include the primary key from one table as a field in a second table to form a relationship between the two tables, it is called a foreign key in the second table New Perspectives o ...
Scientific Databases - LTER Information Management
... Is there a type of DBMS whose structure best mirrors that of the underlying data? ...
... Is there a type of DBMS whose structure best mirrors that of the underlying data? ...