Normalisation
... A database must support a clearly defined language to define the database, view the definition, manipulate the data, and restrict some data values to maintain integrity. ...
... A database must support a clearly defined language to define the database, view the definition, manipulate the data, and restrict some data values to maintain integrity. ...
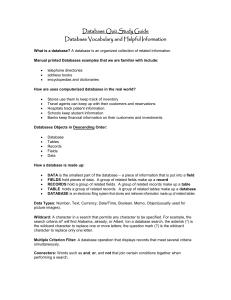
Database Quiz Study Guide
... Date and Time Field – used for storing dates and times in a specific format to allow you to do such things as age an account or time an event. Descending – sorting from largest to smallest. Example: Z – A or 9 – 0. Design View – displays the field names and what kind of values you can enter in each ...
... Date and Time Field – used for storing dates and times in a specific format to allow you to do such things as age an account or time an event. Descending – sorting from largest to smallest. Example: Z – A or 9 – 0. Design View – displays the field names and what kind of values you can enter in each ...
Level 3 Unit 20 Database software
... the software tools and functions involved will be complex and at times require new learning, which will involve having the idea that there may be a tool or function to do something (e.g. improve efficiency or create an effect), exploring technical support, self-teaching and applying; and ...
... the software tools and functions involved will be complex and at times require new learning, which will involve having the idea that there may be a tool or function to do something (e.g. improve efficiency or create an effect), exploring technical support, self-teaching and applying; and ...
Unit Descriptor - Solent Online Learning
... Teaching sessions are organised around ‘stages’ in the development of database application reflecting the main areas of study above. This ensures that the areas of study introduced in the unit are situated in a relevant context that reflects the practical application of the concepts learned. It allo ...
... Teaching sessions are organised around ‘stages’ in the development of database application reflecting the main areas of study above. This ensures that the areas of study introduced in the unit are situated in a relevant context that reflects the practical application of the concepts learned. It allo ...
Visual Database Creation with MySQL Workbench
... Relationships • 1:1 relationships. Primary key for one of the tables is included as foreign key in the other table • 1:n relationships. Primary key of the table in the ’1′ side is added as foreign key in the table in the ‘n’ side • n:m relationships. A new table ( join table) is created. The primar ...
... Relationships • 1:1 relationships. Primary key for one of the tables is included as foreign key in the other table • 1:n relationships. Primary key of the table in the ’1′ side is added as foreign key in the table in the ‘n’ side • n:m relationships. A new table ( join table) is created. The primar ...
KALEEM AHMED
... Six years as Oracle Database Administrator with three years Oracle Applications database administration (Oracle Applications R12.1.3) Ten years as Project Manager and Head of Technical Team, having in depth knowledge in Systems Analysis and Design, Development and Documentation at various levels ...
... Six years as Oracle Database Administrator with three years Oracle Applications database administration (Oracle Applications R12.1.3) Ten years as Project Manager and Head of Technical Team, having in depth knowledge in Systems Analysis and Design, Development and Documentation at various levels ...
Lab Session-II CS121 Summer
... Start with a root node (root is at the top as opposed to natural trees) One child is shown on left and the other one is shown on right The children can also have maximum two ...
... Start with a root node (root is at the top as opposed to natural trees) One child is shown on left and the other one is shown on right The children can also have maximum two ...
Databases and SQL
... a set of data elements (values) organized by records (horizontal rows) and fields (vertical columns) ...
... a set of data elements (values) organized by records (horizontal rows) and fields (vertical columns) ...
ASET - WordPress.com
... • Integrity constraints (e.g., account balance > 0) become “buried” in program code rather than being stated explicitly • Hard to add new constraints or change existing ones ...
... • Integrity constraints (e.g., account balance > 0) become “buried” in program code rather than being stated explicitly • Hard to add new constraints or change existing ones ...
Three types of information systems:
... dBase All have proprietary graphicalinterfaces, and provide programming-style queries as well. ...
... dBase All have proprietary graphicalinterfaces, and provide programming-style queries as well. ...
Chapter 1 - Department of Computer Science
... A software system that enables users to define, create, maintain, and control access to the database: • Allows the definition of the DB and its constraints (Data Definition Language); • Allows the update, deletion and retrieval of data (Data ...
... A software system that enables users to define, create, maintain, and control access to the database: • Allows the definition of the DB and its constraints (Data Definition Language); • Allows the update, deletion and retrieval of data (Data ...
Distributed Databases
... to prepare to commit transaction Ti. Ci adds the records to the log
and forces log to stable storage (a log is a file
which maintains a record of all changes to the
...
... to prepare to commit transaction Ti. Ci adds the records
Document
... The DBMS locks an entire table within a database. This lock level prevents access to any row by a transaction T2 while transaction T1 is using the table. However, two transactions can access the database as long as they access different tables. Table-level locks are only appropriate when table s ...
... The DBMS locks an entire table within a database. This lock level prevents access to any row by a transaction T2 while transaction T1 is using the table. However, two transactions can access the database as long as they access different tables. Table-level locks are only appropriate when table s ...
Study Guide for Mid
... Desirable Characteristics of a primary key (PK) - unique values, no embedded intelligence, time invariant, single attribute, ...
... Desirable Characteristics of a primary key (PK) - unique values, no embedded intelligence, time invariant, single attribute, ...
PPT
... Prepares and validates the query, reporting back success or failure. Provides access to the results collection. ...
... Prepares and validates the query, reporting back success or failure. Provides access to the results collection. ...
End Users
... Appointing Technical Staff: The trained technical persons such as database administrator and application programmers etc are required to handle the DBMS. You have to pay handsome salaries to these persons. Therefore, the system cost increases. ...
... Appointing Technical Staff: The trained technical persons such as database administrator and application programmers etc are required to handle the DBMS. You have to pay handsome salaries to these persons. Therefore, the system cost increases. ...
Thomas L. Brown ... Phone: 903.886.5403
... A course on the development of database applications with an emphasis on programming for database access. It includes data storage and manipulation, information presentation with database connectivity using such application programming interfaces as stored procedures, and embedded SQL. Topics in PHP ...
... A course on the development of database applications with an emphasis on programming for database access. It includes data storage and manipulation, information presentation with database connectivity using such application programming interfaces as stored procedures, and embedded SQL. Topics in PHP ...
MANAGING DATA RESOURCES
... – Advantages of using SQL Users do not need to learn different DDLs and DMLs. SQL can be embedded in widely used 3rd generation languages, increasing efficiency and effectiveness. Programmer not forced to rewrite statements since SQL statements are portable. ...
... – Advantages of using SQL Users do not need to learn different DDLs and DMLs. SQL can be embedded in widely used 3rd generation languages, increasing efficiency and effectiveness. Programmer not forced to rewrite statements since SQL statements are portable. ...
lecture1 - EECS Instructional Support Group Home Page
... – Google’s big step forward was to exploit some of the structure in web documents. – Still, web search places a large burden on people to do the last stage of filtering and interpretation. • Structure gives computers the ability to manipulate and maintain the data. • Traditional (relational) Databas ...
... – Google’s big step forward was to exploit some of the structure in web documents. – Still, web search places a large burden on people to do the last stage of filtering and interpretation. • Structure gives computers the ability to manipulate and maintain the data. • Traditional (relational) Databas ...