Migrating from Microsoft SQL Server to IBM Informix
... 3.3 Migrating . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53 3.3.1 Migrating and designing the database . . . . . . . . . . . . . . . . . . . . . . . 53 3.3.2 Calibrating the planned strategy . . . . . . . . . . . . . . . . . . . . . . . . . . ...
... 3.3 Migrating . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53 3.3.1 Migrating and designing the database . . . . . . . . . . . . . . . . . . . . . . . 53 3.3.2 Calibrating the planned strategy . . . . . . . . . . . . . . . . . . . . . . . . . . ...
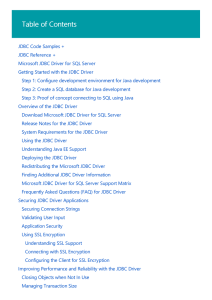
Microsoft JDBC Driver for SQL Server | Microsoft Docs
... encrypting the data in the application, so that SQL Server will only handle the encrypted data and not plaintext values. Even if the SQL instance or the host machine is compromised, all an attacker can get is ciphertext of sensitive data. For details see Using Always Encrypted with the JDBC Driver. ...
... encrypting the data in the application, so that SQL Server will only handle the encrypted data and not plaintext values. Even if the SQL instance or the host machine is compromised, all an attacker can get is ciphertext of sensitive data. For details see Using Always Encrypted with the JDBC Driver. ...
... transmit, distribute, disseminate, sell, publish or sublicense the work or any part of it without McGraw-Hill’s prior consent. You may use the work for your own noncommercial and personal use; any other use of the work is strictly prohibited. Your right to use the work may be terminated if you fail ...
The Underground PHP and Oracle Manual
... The Programs are not intended for use in any nuclear, aviation, mass transit, medical, or other inherently dangerous applications. It shall be the licensee's responsibility to take all appropriate fail-safe, backup, redundancy and other measures to ensure the safe use of such applications if the Pro ...
... The Programs are not intended for use in any nuclear, aviation, mass transit, medical, or other inherently dangerous applications. It shall be the licensee's responsibility to take all appropriate fail-safe, backup, redundancy and other measures to ensure the safe use of such applications if the Pro ...
Optimization of LMS for Improving User Response Time
... Moodle community has grown extensively, and both developers and users have actively participated in the discussion forums, by sharing their ideas, tips, resources, and also helping new users. Some of the reasons for using Moodle are listed below[10] 1. Moodle is an Open Source software. This means, ...
... Moodle community has grown extensively, and both developers and users have actively participated in the discussion forums, by sharing their ideas, tips, resources, and also helping new users. Some of the reasons for using Moodle are listed below[10] 1. Moodle is an Open Source software. This means, ...
Oracle® Thesaurus Management System
... documentation includes features that make information available to users of assistive technology. This documentation is available in HTML format, and contains markup to facilitate access by the disabled community. Accessibility standards will continue to evolve over time, and Oracle is actively enga ...
... documentation includes features that make information available to users of assistive technology. This documentation is available in HTML format, and contains markup to facilitate access by the disabled community. Accessibility standards will continue to evolve over time, and Oracle is actively enga ...
DBI_Talk5_2001 - CPAN
... – even from power failures and system crashes! – Incomplete transactions are automatically rolled-back by the database ...
... – even from power failures and system crashes! – Incomplete transactions are automatically rolled-back by the database ...
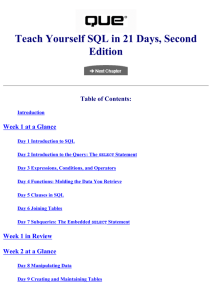
Teach Yourself SQL in 21 Days, Second Edition
... 12. Nonsubversion--It must not be possible to bypass the integrity rules defined through the database language by using lower-level languages. Most databases have had a "parent/child" relationship; that is, a parent node would contain file pointers to its children. (See Figure 1.1.) Figure 1.1. Codd ...
... 12. Nonsubversion--It must not be possible to bypass the integrity rules defined through the database language by using lower-level languages. Most databases have had a "parent/child" relationship; that is, a parent node would contain file pointers to its children. (See Figure 1.1.) Figure 1.1. Codd ...
Relational Database(RDBMS via ODBC) Interface
... Copyright: © 2006-2017 OSIsoft, LLC. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, mechanical, photocopying, recording, or otherwise, without the prior written permission of OSIsoft, LLC. OSIsoft, the OS ...
... Copyright: © 2006-2017 OSIsoft, LLC. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, mechanical, photocopying, recording, or otherwise, without the prior written permission of OSIsoft, LLC. OSIsoft, the OS ...
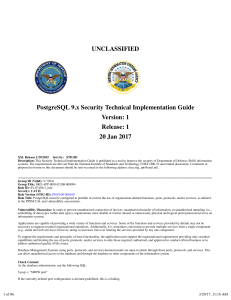
PostgreSQL 9.x Security Technical Implementation
... events, security personnel cannot make an accurate assessment as to whether an attack was successful or if changes were made to the security state of the system. Event outcomes can include indicators of event success or failure and event-specific results (e.g., the security state of the information ...
... events, security personnel cannot make an accurate assessment as to whether an attack was successful or if changes were made to the security state of the system. Event outcomes can include indicators of event success or failure and event-specific results (e.g., the security state of the information ...
Teradata Aster Big Analytics Appliance 3H
... The information contained in this document may contain references or cross-references to features, functions, products, or services that are not announced or available in your country. Such references do not imply that Teradata Corporation intends to announce such features, functions, products, or s ...
... The information contained in this document may contain references or cross-references to features, functions, products, or services that are not announced or available in your country. Such references do not imply that Teradata Corporation intends to announce such features, functions, products, or s ...
Beginning Access 2007 VBA
... What Is Access 2007 VBA? ................................................................................................................................................... 15 What’s New in Access 2007 VBA? ....................................................................................... ...
... What Is Access 2007 VBA? ................................................................................................................................................... 15 What’s New in Access 2007 VBA? ....................................................................................... ...
Ingres 2006 SQL Reference Guide
... This documentation and related computer software program (hereinafter referred to as the "Documentation") is for the end user's informational purposes only and is subject to change or withdrawal by Ingres Corporation ("Ingres") at any time. This Documentation may not be copied, transferred, reprodu ...
... This documentation and related computer software program (hereinafter referred to as the "Documentation") is for the end user's informational purposes only and is subject to change or withdrawal by Ingres Corporation ("Ingres") at any time. This Documentation may not be copied, transferred, reprodu ...
IBM Redbook: Informix Dynamic Server 11 Extending
... 8.2.2 Logical log space . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 172 8.3 Prepare the database server. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 176 8.3.1 Define ER related dbspaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
... 8.2.2 Logical log space . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 172 8.3 Prepare the database server. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 176 8.3.1 Define ER related dbspaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
EMC VSPEX FOR VIRTUALIZED MICROSOFT SQL SERVER 2012 WITH VMWARE VSPHERE
... EMC VSPEX FOR VIRTUALIZED MICROSOFT SQL SERVER 2012 WITH VMWARE VSPHERE ...
... EMC VSPEX FOR VIRTUALIZED MICROSOFT SQL SERVER 2012 WITH VMWARE VSPHERE ...
EDB Postgres Enterprise Guide
... Copyright © 2014 - 2017 EnterpriseDB Corporation. All rights reserved. ...
... Copyright © 2014 - 2017 EnterpriseDB Corporation. All rights reserved. ...
AWS Database Migration Service - User Guide
... Prerequisites When Using MongoDB as a Source for AWS Database Migration Service ................ Prerequisites When Using CDC with MongoDB as a Source for AWS Database Migration Service ... Security Requirements When Using MongoDB as a Source for AWS Database Migration Service ... Limitations When U ...
... Prerequisites When Using MongoDB as a Source for AWS Database Migration Service ................ Prerequisites When Using CDC with MongoDB as a Source for AWS Database Migration Service ... Security Requirements When Using MongoDB as a Source for AWS Database Migration Service ... Limitations When U ...
SQL Data Control Language - Information Products
... Corporation will have no obligation of any kind with respect to Feedback and will be free to use, reproduce, disclose, exhibit, display, transform, create derivative works of, and distribute the Feedback and derivative works thereof without limitation on a royalty-free basis. Further, Teradata Corpo ...
... Corporation will have no obligation of any kind with respect to Feedback and will be free to use, reproduce, disclose, exhibit, display, transform, create derivative works of, and distribute the Feedback and derivative works thereof without limitation on a royalty-free basis. Further, Teradata Corpo ...
Acronis Backup
... Third party code may be provided with the Software and/or Service. The license terms for such third-parties are detailed in the license.txt file located in the root installation directory. You can always find the latest up-to-date list of the third party code and the associated license terms used wi ...
... Third party code may be provided with the Software and/or Service. The license terms for such third-parties are detailed in the license.txt file located in the root installation directory. You can always find the latest up-to-date list of the third party code and the associated license terms used wi ...
Oracle DBA Questions Database and SQL Multiple choice questions
... Question ________means data is protected from deletion and corruption, both while it resides within database Correct Answer Data integrity Question To be able to successfully design and maintain databases we have to do following Correct Answer Identify relationship between objects , Identify worlds ...
... Question ________means data is protected from deletion and corruption, both while it resides within database Correct Answer Data integrity Question To be able to successfully design and maintain databases we have to do following Correct Answer Identify relationship between objects , Identify worlds ...
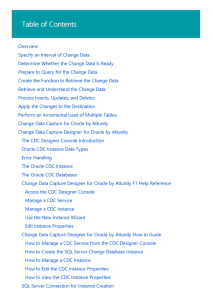
Change Data Capture (SSIS) | Microsoft Docs
... As shown in the previous diagram, creating a package that performs an incremental load of changed data involves the following steps: Step 1: Designing the Control Flow In the control flow in the package, the following tasks need to be defined: Calculate the starting and ending datetime values for t ...
... As shown in the previous diagram, creating a package that performs an incremental load of changed data involves the following steps: Step 1: Designing the Control Flow In the control flow in the package, the following tasks need to be defined: Calculate the starting and ending datetime values for t ...
Greenplum Database 4.3 Installation Guide
... You may optionally deploy a backup or mirror of the master instance. A backup master host serves as a warm standby if the primary master host becomes nonoperational. You can deploy the standby master on a designated redundant master host or on one of the segment hosts. The standby master is kept up ...
... You may optionally deploy a backup or mirror of the master instance. A backup master host serves as a warm standby if the primary master host becomes nonoperational. You can deploy the standby master on a designated redundant master host or on one of the segment hosts. The standby master is kept up ...
PI Interface for Relational Database (RDBMS via ODBC)
... Copyright: © 2006-2017 OSIsoft, LLC. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, mechanical, photocopying, recording, or otherwise, without the prior written permission of OSIsoft, LLC. OSIsoft, the OS ...
... Copyright: © 2006-2017 OSIsoft, LLC. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, mechanical, photocopying, recording, or otherwise, without the prior written permission of OSIsoft, LLC. OSIsoft, the OS ...
SQL Server to SQL Server PDW Migration Guide
... As data volumes grow and the number of users increase, we find the traditional architecture of running your data warehouse on a single SMP server insufficient to meet the business requirements. To overcome these limitations and scale and perform beyond your existing deployment, Parallel Data Warehou ...
... As data volumes grow and the number of users increase, we find the traditional architecture of running your data warehouse on a single SMP server insufficient to meet the business requirements. To overcome these limitations and scale and perform beyond your existing deployment, Parallel Data Warehou ...