A Practical Approach for Microscopy Imaging Data Management (MIDM) in Neuroscience
... repository for simple text -based retrieval, but also provides image content retrieval. Although content-based image retrieval has been widely researched to retrieve desired images on the basis of features (such as color, texture, shape) that can be automatically extracted from the images themselves ...
... repository for simple text -based retrieval, but also provides image content retrieval. Although content-based image retrieval has been widely researched to retrieve desired images on the basis of features (such as color, texture, shape) that can be automatically extracted from the images themselves ...
Database Application Development
... Locking cursors Looping through dataset while creating other cursors ...
... Locking cursors Looping through dataset while creating other cursors ...
BASE: An Acid Alternative - ACM Queue
... operation is considered idempotent if it can be applied one time or multiple times with the same result. Idempotent operations are useful in that they permit partial failures, as applying them repeatedly does not change the final state of the system. The selected example is problematic when looking ...
... operation is considered idempotent if it can be applied one time or multiple times with the same result. Idempotent operations are useful in that they permit partial failures, as applying them repeatedly does not change the final state of the system. The selected example is problematic when looking ...
ANU Metadata Stores
... Insert rows into the location table of the harvest database. This should include the system, the url of the OAI provider, the metadata prefix, how frequently the data should be harvested (in milliseconds) and an original harvest date to calculate when to next harvest the data It will harvest the nex ...
... Insert rows into the location table of the harvest database. This should include the system, the url of the OAI provider, the metadata prefix, how frequently the data should be harvested (in milliseconds) and an original harvest date to calculate when to next harvest the data It will harvest the nex ...
Access Tutorial 1: Introduction to Microsoft Access
... Most professional Access developers do not put their tables in the same database file as their queries, forms, reports, and so on. The reason for this is simple: keep the application’s data and interface separate. Access allows you to use the “linked table” feature to link two database files: one co ...
... Most professional Access developers do not put their tables in the same database file as their queries, forms, reports, and so on. The reason for this is simple: keep the application’s data and interface separate. Access allows you to use the “linked table” feature to link two database files: one co ...
Monitoring Database Objects
... transactions hide updates from other clients until they are committed ...
... transactions hide updates from other clients until they are committed ...
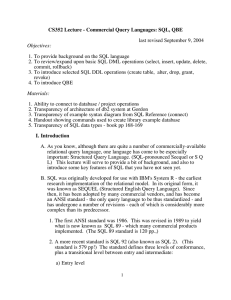
CS352 Lecture - Commercial Query Languages: SQL, QBE last
... processed at run time (This is called dynamic SQL). 3. By using JDBC - which resembles dynamic SQL, in that a Java program constructs SQL queries or updates as character strings, and then passes them off to the database to be processed) (It’s actually slightly different in terms of the way it is imp ...
... processed at run time (This is called dynamic SQL). 3. By using JDBC - which resembles dynamic SQL, in that a Java program constructs SQL queries or updates as character strings, and then passes them off to the database to be processed) (It’s actually slightly different in terms of the way it is imp ...
REVISING JOE`S DATABASE
... Throughout our efforts in developing Joes’s Fruit Stand database, we have had much emphasis on table relationships. As you remember, Joe had developed a database using just a single table. In this table he tried to do everything and soon ran into problems. You have divided this table, first into two ...
... Throughout our efforts in developing Joes’s Fruit Stand database, we have had much emphasis on table relationships. As you remember, Joe had developed a database using just a single table. In this table he tried to do everything and soon ran into problems. You have divided this table, first into two ...
Generating XML from Relational Tables using ORACLE
... function that produces a forest of XML elements from a collection of XML elements. XMLConcat() Function: It concatenates all the arguments passed in to create a XML fragment. ...
... function that produces a forest of XML elements from a collection of XML elements. XMLConcat() Function: It concatenates all the arguments passed in to create a XML fragment. ...
HP TRIM Sql Server – Setup and Maintenance
... storage means this never happens. RAID and SAN mean that most of the time everything supporting the database goes on the SAN or disk array. There will be times when this cannot happen so you need to know, given a set of disks which files can reside where. Firstly, to reduce contention, all data file ...
... storage means this never happens. RAID and SAN mean that most of the time everything supporting the database goes on the SAN or disk array. There will be times when this cannot happen so you need to know, given a set of disks which files can reside where. Firstly, to reduce contention, all data file ...
JDBC Checker: A Static Analysis Tool for SQL/JDBC Applications
... servlet web service constructs SQL query strings and dispatches them over a JDBC connector to an SQL-compliant database. The servlet programmer enjoys static checking via Java’s strong type system. However, the Java type system does little to check for possible errors in the dynamically generated SQ ...
... servlet web service constructs SQL query strings and dispatches them over a JDBC connector to an SQL-compliant database. The servlet programmer enjoys static checking via Java’s strong type system. However, the Java type system does little to check for possible errors in the dynamically generated SQ ...
P*TIME
... volume minimization. Even for the same logging granularity, differential logging stores the XOR difference between “before” and “after” images and thus reduces the log volume by almost half compared with the conventional “before/after image” logging such as ARIES [15] [16]. Compared with the block-l ...
... volume minimization. Even for the same logging granularity, differential logging stores the XOR difference between “before” and “after” images and thus reduces the log volume by almost half compared with the conventional “before/after image” logging such as ARIES [15] [16]. Compared with the block-l ...
Chapter 7 Managing Data Resources
... Database Technology, Management, and Users Change isn't just something you experience by chance; in all likelihood, it will be required throughout the corporate structure. You need to get the nontechies talking and working with the techies, preferably together in a group that is responsible for data ...
... Database Technology, Management, and Users Change isn't just something you experience by chance; in all likelihood, it will be required throughout the corporate structure. You need to get the nontechies talking and working with the techies, preferably together in a group that is responsible for data ...
SampleExam14(Ch37-38..
... SQL Language Structure Integrity 5 What information may be obtained from a ResultSetMetaData object? A. number of columns in the result set B. number of rows in the result set C. database URL and product name D. JDBC driver name and version 6 Which of the following statements are true? A. You may lo ...
... SQL Language Structure Integrity 5 What information may be obtained from a ResultSetMetaData object? A. number of columns in the result set B. number of rows in the result set C. database URL and product name D. JDBC driver name and version 6 Which of the following statements are true? A. You may lo ...
Introduction to Database Systems
... get the components of that tuple by applying certain methods to the ResultSet. • Method getX (i ), where X is some type, and i is the component number, returns the value of that ...
... get the components of that tuple by applying certain methods to the ResultSet. • Method getX (i ), where X is some type, and i is the component number, returns the value of that ...
Data Modeling - Temple Fox MIS
... • Out of necessity, rather than preference • Data is unstructured, must be parsed ...
... • Out of necessity, rather than preference • Data is unstructured, must be parsed ...
Kroenke-DBP-e10-PPT-Chapter11
... • Both data and log files are created by SQL Server • SQL Server provides a wizard for setting up database maintenance plan, e.g., scheduling database and log backups • To recover a database with SQL Server: – The database is restored from a prior database backup – Log after images are applied to th ...
... • Both data and log files are created by SQL Server • SQL Server provides a wizard for setting up database maintenance plan, e.g., scheduling database and log backups • To recover a database with SQL Server: – The database is restored from a prior database backup – Log after images are applied to th ...
data model
... Self-describing nature of a database system A DBMS catalog stores the description of the database. The description is called meta-data. This allows the DBMS software to work with different databases A traditional file processing can work with only one specific database. The description of the da ...
... Self-describing nature of a database system A DBMS catalog stores the description of the database. The description is called meta-data. This allows the DBMS software to work with different databases A traditional file processing can work with only one specific database. The description of the da ...
CENG 352 Database Management Systems
... Users can specify some simple integrity constraints on the data, and the DBMS will enforce these constraints. Beyond this, the DBMS does not really understand the semantics of the data. (e.g., it does not understand how the interest on a bank account is computed). Thus, ensuring that a transaction ( ...
... Users can specify some simple integrity constraints on the data, and the DBMS will enforce these constraints. Beyond this, the DBMS does not really understand the semantics of the data. (e.g., it does not understand how the interest on a bank account is computed). Thus, ensuring that a transaction ( ...
Lecture 1 : Introduction to DBMS
... Users can specify some simple integrity constraints on the data, and the DBMS will enforce these constraints. Beyond this, the DBMS does not really understand the semantics of the data. (e.g., it does not understand how the interest on a bank account is computed). Thus, ensuring that a transaction ( ...
... Users can specify some simple integrity constraints on the data, and the DBMS will enforce these constraints. Beyond this, the DBMS does not really understand the semantics of the data. (e.g., it does not understand how the interest on a bank account is computed). Thus, ensuring that a transaction ( ...
PPT File
... Describing the database system software environment Learning about classification of the types of DBMS packages Modern DBMS packages are modular in design with a client-server system architecture. In such architectures, the functionality is distributed between client module (application programs and ...
... Describing the database system software environment Learning about classification of the types of DBMS packages Modern DBMS packages are modular in design with a client-server system architecture. In such architectures, the functionality is distributed between client module (application programs and ...
Databases
... Find all male users between 20 and 50 years old who live in the state of Illinois whose license plate number begins with ‘TMX’ Find all products that have sold less than 1000 items. Remove those items from the catalog. Remove those items from the ‘Orders’ table. ...
... Find all male users between 20 and 50 years old who live in the state of Illinois whose license plate number begins with ‘TMX’ Find all products that have sold less than 1000 items. Remove those items from the catalog. Remove those items from the ‘Orders’ table. ...
Versant Object Database

Versant Object Database (VOD) is an object database software product developed by Versant Corporation.The Versant Object Database enables developers using object oriented languages to transactionally store their information by allowing the respective language to act as the Data Definition Language (DDL) for the database. In other words, the memory model is the database schema model.In general, persistence in VOD in implemented by declaring a list of classes, then providing a transaction demarcation application programming interface to use cases. Respective language integrations adhere to the constructs of that language, including syntactic and directive sugars.Additional APIs exist, beyond simple transaction demarcation, providing for the more advanced capabilities necessary to address practical issues found when dealing with performance optimization and scalability for systems with large amounts of data, many concurrent users, network latency, disk bottlenecks, etc.