we know all the incoming query templates beforehand
... In this poster, we describe our architecture that utilizes these data placement techniques for determining an optimum layout of data. Our solution is general, and other data placement techniques can be integrated within our system. Once the data is laid out on the different database servers, our eff ...
... In this poster, we describe our architecture that utilizes these data placement techniques for determining an optimum layout of data. Our solution is general, and other data placement techniques can be integrated within our system. Once the data is laid out on the different database servers, our eff ...
Object-Relational Mapping with Hibernate and JPA
... O/R Mapping Annotations Describe how Java classes are mapped to relational tables ...
... O/R Mapping Annotations Describe how Java classes are mapped to relational tables ...
finalExamReview2
... SELECT UWStudent.Name, UWStudent.StudentID, Fit100Student.Exam1Grade FROM (UWStudent INNER JOIN Fit100Students ON UWStudent.StudentID = Fit100Student.StudentID) ...
... SELECT UWStudent.Name, UWStudent.StudentID, Fit100Student.Exam1Grade FROM (UWStudent INNER JOIN Fit100Students ON UWStudent.StudentID = Fit100Student.StudentID) ...
to view the file
... for Billions of Gizmos on the Move – What’s in it for the Database Folks Ralf Hartmut Güting Fernuniversität Hagen, Germany ...
... for Billions of Gizmos on the Move – What’s in it for the Database Folks Ralf Hartmut Güting Fernuniversität Hagen, Germany ...
Andmebaaside tarkvara
... smaller company than its chief rival, Oracle, Informix has been able to make large market-share gains recently due to its innovative technology. ...
... smaller company than its chief rival, Oracle, Informix has been able to make large market-share gains recently due to its innovative technology. ...
CSS 5xx: Advanced Database Management
... This class explores methods and techniques to achieve the availability needs and also focuses on how to protect the database against disasters by maintaining multiple copies of the databases in separate locations, synchronized in real-time. Students learn to design and manage key business resumption ...
... This class explores methods and techniques to achieve the availability needs and also focuses on how to protect the database against disasters by maintaining multiple copies of the databases in separate locations, synchronized in real-time. Students learn to design and manage key business resumption ...
Features of ORM
... scoped to a transaction. The entire transaction can either be committed or rolled back. Multiple transactions can be active in memory in the same time, and each transactions changes are isolated form on another. ...
... scoped to a transaction. The entire transaction can either be committed or rolled back. Multiple transactions can be active in memory in the same time, and each transactions changes are isolated form on another. ...
DBCache: Database Caching For Web Application Servers*
... Many e-Business applications today are being developed and deployed on multi-tier environments involving browser-based clients, web application servers and backend databases. The dynamic nature of these applications necessitates generating web pages on-demand, making middle-tier database caching an ...
... Many e-Business applications today are being developed and deployed on multi-tier environments involving browser-based clients, web application servers and backend databases. The dynamic nature of these applications necessitates generating web pages on-demand, making middle-tier database caching an ...
Connecting to a Database
... can use cookies, the Session object and text files. All these methods have their drawbacks. Databases are specifically designed to store massive amounts of information efficiently. Many commercial databases are available, including Access, MS SQLServer, Oracle and Informix etc. It is possible to rea ...
... can use cookies, the Session object and text files. All these methods have their drawbacks. Databases are specifically designed to store massive amounts of information efficiently. Many commercial databases are available, including Access, MS SQLServer, Oracle and Informix etc. It is possible to rea ...
DATABASE PROGRAMS
... Oracle Databases help customers lower IT costs and deliver a higher quality of service by enabling consolidation onto database clouds and engineered systems like Oracle Exadata and Oracle Database Appliance. ...
... Oracle Databases help customers lower IT costs and deliver a higher quality of service by enabling consolidation onto database clouds and engineered systems like Oracle Exadata and Oracle Database Appliance. ...
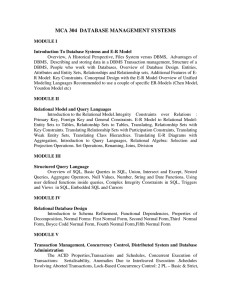
MCA 304 DATABASE MANAGEMENT SYSTEMS
... Introduction To Database Systems and E-R Model Overview, A Historical Perspective, Files System versus DBMS, Advantages of DBMS, Describing and storing data in a DBMS Transaction management, Structure of a DBMS, People who work with Databases, Overview of Database Design. Entities, Attributes and En ...
... Introduction To Database Systems and E-R Model Overview, A Historical Perspective, Files System versus DBMS, Advantages of DBMS, Describing and storing data in a DBMS Transaction management, Structure of a DBMS, People who work with Databases, Overview of Database Design. Entities, Attributes and En ...
Access lesson 1 Database Basics
... SHORT TEXT • Data type used to store up to 255 characters of data in a field and is a good data type for a field that stores small amounts of text like names, cities and ...
... SHORT TEXT • Data type used to store up to 255 characters of data in a field and is a good data type for a field that stores small amounts of text like names, cities and ...
Document
... The row-level lock is much less restrictive than the locks we have just discussed. Row-level locks permit the DBMS to allow concurrent transactions to access different rows of the same table, even if these rows are located on the same page. Although the row-level locking approach improves the avai ...
... The row-level lock is much less restrictive than the locks we have just discussed. Row-level locks permit the DBMS to allow concurrent transactions to access different rows of the same table, even if these rows are located on the same page. Although the row-level locking approach improves the avai ...
Effective Keyword-Based Selection of Relational Databases
... in a relational database at each distance construct the Wd matrices – the frequencies of keyword pairs at distance d; Example: Figure 3 ...
... in a relational database at each distance construct the Wd matrices – the frequencies of keyword pairs at distance d; Example: Figure 3 ...
OODB - Personal.psu.edu
... and their behavior (methods) Better interaction with object-oriented languages such as Java and C++ Definition of complex and user-defined types Encapsulation of operations and user-defined methods ...
... and their behavior (methods) Better interaction with object-oriented languages such as Java and C++ Definition of complex and user-defined types Encapsulation of operations and user-defined methods ...
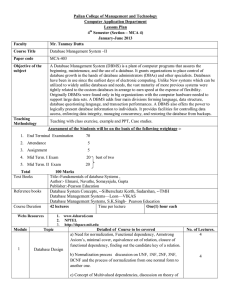
Database System Concepts, --Silberschatz Korth, Sudarshan, -
... database growth in the hands of database administrators (DBAs) and other specialists. Databases have been in use since the earliest days of electronic computing. Unlike New systems which can be utilized to widely unlike databases and needs, the vast maturity of more previous systems were tightly rel ...
... database growth in the hands of database administrators (DBAs) and other specialists. Databases have been in use since the earliest days of electronic computing. Unlike New systems which can be utilized to widely unlike databases and needs, the vast maturity of more previous systems were tightly rel ...
Database Management issues from Hoffer - Moodle
... The process of managing simultaneous operations against a database so that data integrity is maintained and the operations do not interfere with each other in a multi-user environment ...
... The process of managing simultaneous operations against a database so that data integrity is maintained and the operations do not interfere with each other in a multi-user environment ...
Data Modeling Case Study
... He makes an appointment with his family doctor who confirm his diagnosis. The doctor prescribes an antibiotic and nasal decongestant tablets. Jack leaves the doctor's office and drives to his local drug store. The pharmacist packages the medication and types the labels for pill bottles. The label in ...
... He makes an appointment with his family doctor who confirm his diagnosis. The doctor prescribes an antibiotic and nasal decongestant tablets. Jack leaves the doctor's office and drives to his local drug store. The pharmacist packages the medication and types the labels for pill bottles. The label in ...
Database Systems Syllabus - Lehman College
... Lecture Schedule: Mondays and Wednesdays: 7:50 PM - 9:30 PM (GI 333) Office Hours: Mondays and Wednesdays: 3:00 - 5:30 PM; and other time by appointment Course Objectives: Understand fundamental concepts of modern database systems. Topics include: database systems concepts and architecture, data mod ...
... Lecture Schedule: Mondays and Wednesdays: 7:50 PM - 9:30 PM (GI 333) Office Hours: Mondays and Wednesdays: 3:00 - 5:30 PM; and other time by appointment Course Objectives: Understand fundamental concepts of modern database systems. Topics include: database systems concepts and architecture, data mod ...
An introduction to SQL
... • SELECT – Read only query to examine data from the database. May be used in conjunction with update statements. • UPDATE – Update existing data • INSERT – Insert new rows • DELETE – Delete existing rows ...
... • SELECT – Read only query to examine data from the database. May be used in conjunction with update statements. • UPDATE – Update existing data • INSERT – Insert new rows • DELETE – Delete existing rows ...
Database Management System(DBMS)
... Many of the parts are duplicated so data is less likely to be lost It appears to the user to be a single system Duplication enables faster processing It is an old technology that is still widely used ...
... Many of the parts are duplicated so data is less likely to be lost It appears to the user to be a single system Duplication enables faster processing It is an old technology that is still widely used ...
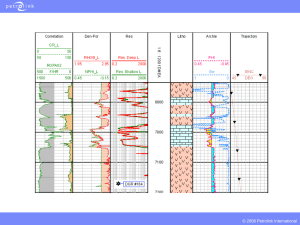
PPT - Energistics
... PowerStore is the Petrolink WITSML store, which supports the full specifications of WITSML Version 1.2 and Version 1.3.1. It strictly follows the WITSML specification, including the publish/subscribe method dropped by other contractors, special handling, and full support for all objects. ...
... PowerStore is the Petrolink WITSML store, which supports the full specifications of WITSML Version 1.2 and Version 1.3.1. It strictly follows the WITSML specification, including the publish/subscribe method dropped by other contractors, special handling, and full support for all objects. ...
Versant Object Database

Versant Object Database (VOD) is an object database software product developed by Versant Corporation.The Versant Object Database enables developers using object oriented languages to transactionally store their information by allowing the respective language to act as the Data Definition Language (DDL) for the database. In other words, the memory model is the database schema model.In general, persistence in VOD in implemented by declaring a list of classes, then providing a transaction demarcation application programming interface to use cases. Respective language integrations adhere to the constructs of that language, including syntactic and directive sugars.Additional APIs exist, beyond simple transaction demarcation, providing for the more advanced capabilities necessary to address practical issues found when dealing with performance optimization and scalability for systems with large amounts of data, many concurrent users, network latency, disk bottlenecks, etc.