SAP Replication Server 15.7.1 SP200 ®
... No part of this publication may be reproduced or transmitted in any form or for any purpose without the express permission of SAP AG. The information contained herein may be changed without prior notice. Some software products marketed by SAP AG and its distributors contain proprietary software comp ...
... No part of this publication may be reproduced or transmitted in any form or for any purpose without the express permission of SAP AG. The information contained herein may be changed without prior notice. Some software products marketed by SAP AG and its distributors contain proprietary software comp ...
API Guide - Embarcadero
... Embarcadero Technologies, Inc. is a leading provider of award-winning tools for application developers and database professionals so they can design systems right, build them faster and run them better, regardless of their platform or programming language. Ninety of the Fortune 100 and an active com ...
... Embarcadero Technologies, Inc. is a leading provider of award-winning tools for application developers and database professionals so they can design systems right, build them faster and run them better, regardless of their platform or programming language. Ninety of the Fortune 100 and an active com ...
Oracle Database - Oracle Help Center
... license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by la ...
... license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by la ...
Oracle Rdb™ SQL Reference Manual Volume 3
... A cache for a given sequence is populated at the first request for a number from that sequence, and whenever a value is requested when the cache is empty. If a system failure occurs, or when the cache is released any unfetched values will be discarded. The maximum number of lost values is equal to t ...
... A cache for a given sequence is populated at the first request for a number from that sequence, and whenever a value is requested when the cache is empty. If a system failure occurs, or when the cache is released any unfetched values will be discarded. The maximum number of lost values is equal to t ...
Database Administration Concepts and Configuration Reference
... This document contains proprietary information of IBM. It is provided under a license agreement and is protected by copyright law. The information contained in this publication does not include any product warranties, and any statements provided in this manual should not be interpreted as such. You ...
... This document contains proprietary information of IBM. It is provided under a license agreement and is protected by copyright law. The information contained in this publication does not include any product warranties, and any statements provided in this manual should not be interpreted as such. You ...
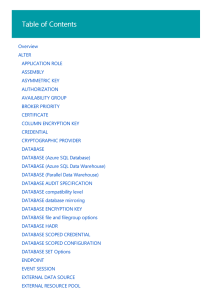
ALTER DATABASE
... triggers, user-defined types, and user-defined aggregate functions against it. If set to OFF, the assembly is intended to be called only by other assemblies. If there are existing CLR database objects already created against the assembly, the visibility of the assembly cannot be changed. Any assembl ...
... triggers, user-defined types, and user-defined aggregate functions against it. If set to OFF, the assembly is intended to be called only by other assemblies. If there are existing CLR database objects already created against the assembly, the visibility of the assembly cannot be changed. Any assembl ...
Acct 316 Acct 316 Acct 316 Acct 316 Acct 316 Acct 316 Acct 316
... is initially stored in a large nonnormalized table. This table is then decomposed using a set of normalization rules to create a set of tables in the Third Normal Form. ...
... is initially stored in a large nonnormalized table. This table is then decomposed using a set of normalization rules to create a set of tables in the Third Normal Form. ...
SQLite Tutorial
... All the content and graphics published in this e-book are the property of Tutorials Point (I) Pvt. Ltd. The user of this e-book is prohibited to reuse, retain, copy, distribute or republish any contents or a part of contents of this e-book in any manner without written consent of the publisher. We s ...
... All the content and graphics published in this e-book are the property of Tutorials Point (I) Pvt. Ltd. The user of this e-book is prohibited to reuse, retain, copy, distribute or republish any contents or a part of contents of this e-book in any manner without written consent of the publisher. We s ...
Symantec NetBackup⢠for Sybase Administrator`s Guide: for UNIX
... Using NetBackup for Sybase ............................................ 55 About using NetBackup for Sybase .................................................. About Sybase database backups ..................................................... Sybase backup strategy .................................. ...
... Using NetBackup for Sybase ............................................ 55 About using NetBackup for Sybase .................................................. About Sybase database backups ..................................................... Sybase backup strategy .................................. ...
Definitive Guide to SQLite
... Where to Get SQLite ......................................................................................................... 17 SQLite on Windows .......................................................................................................... 18 Getting the Command-Line Program .......... ...
... Where to Get SQLite ......................................................................................................... 17 SQLite on Windows .......................................................................................................... 18 Getting the Command-Line Program .......... ...
IBM Informix Administrator`s Guide
... What's new in administration for Informix, Version 12.10 . . . . . . . . . . . . . . . . . . . xviii ...
... What's new in administration for Informix, Version 12.10 . . . . . . . . . . . . . . . . . . . xviii ...
Microsoft SQL Server DBA Survival Guide -
... components. Additionally, the idea of paying thousands of dollars to rent software that runs on the mainframe is almost inconceivable for PC users who have never used mainframe technology. Rather than using common components, mainframes typically use hardware and software proprietary to the mainfram ...
... components. Additionally, the idea of paying thousands of dollars to rent software that runs on the mainframe is almost inconceivable for PC users who have never used mainframe technology. Rather than using common components, mainframes typically use hardware and software proprietary to the mainfram ...
for IBM z/OS (OS/390)
... The Programs are not intended for use in any nuclear, aviation, mass transit, medical, or other inherently dangerous applications. It shall be the licensee's responsibility to take all appropriate fail-safe, backup, redundancy and other measures to ensure the safe use of such applications if the Pro ...
... The Programs are not intended for use in any nuclear, aviation, mass transit, medical, or other inherently dangerous applications. It shall be the licensee's responsibility to take all appropriate fail-safe, backup, redundancy and other measures to ensure the safe use of such applications if the Pro ...
Teradata Archive/Recovery Utility Reference
... Corporation will be free to use any ideas, concepts, know-how, or techniques contained in such Feedback for any purpose whatsoever, including developing, manufacturing, or marketing products or services incorporating Feedback. Copyright © 1997-2016 by Teradata. All Rights Reserved. ...
... Corporation will be free to use any ideas, concepts, know-how, or techniques contained in such Feedback for any purpose whatsoever, including developing, manufacturing, or marketing products or services incorporating Feedback. Copyright © 1997-2016 by Teradata. All Rights Reserved. ...
OReilly.Enterprise.JavaBeans.3.0.5th.Edition.May.2006 [EJB 3.0]
... The purpose of the EJB 3.0 release was to refocus EJB on simplifying the developer's tasksand to fix all of these problems, and more. One of the first steps in this process was evaluating the sources of complexity in the earlier EJB releases. This involved examining criticisms of EJB; understanding ...
... The purpose of the EJB 3.0 release was to refocus EJB on simplifying the developer's tasksand to fix all of these problems, and more. One of the first steps in this process was evaluating the sources of complexity in the earlier EJB releases. This involved examining criticisms of EJB; understanding ...
Mastering EJB 2nd Edition
... Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 750-4744. Requests to the Publisher for permission should be addressed to the Permissions Department, John Wiley & Sons, Inc., 605 Third Avenue, New York, NY 10158-0012, (212) 850-6011, fax (212) 8506008, E-Mail: [email protected]. This pu ...
... Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 750-4744. Requests to the Publisher for permission should be addressed to the Permissions Department, John Wiley & Sons, Inc., 605 Third Avenue, New York, NY 10158-0012, (212) 850-6011, fax (212) 8506008, E-Mail: [email protected]. This pu ...
InnoDB 1.1 for MySQL 5.5 User`s Guide
... responsible to take all appropriate fail-safe, backup, redundancy, and other measures to ensure the safe use of this software. Oracle Corporation and its affiliates disclaim any liability for any damages caused by use of this software in dangerous applications. Oracle is a registered trademark of Or ...
... responsible to take all appropriate fail-safe, backup, redundancy, and other measures to ensure the safe use of this software. Oracle Corporation and its affiliates disclaim any liability for any damages caused by use of this software in dangerous applications. Oracle is a registered trademark of Or ...
Oracle Rdb™ SQL Reference Manual Volume 2
... The Programs (which include both the software and documentation) contain proprietary information of Oracle Corporation; they are provided under a license agreement containing restrictions on use and disclosure and are also protected by copyright, patent, and other intellectual and industrial propert ...
... The Programs (which include both the software and documentation) contain proprietary information of Oracle Corporation; they are provided under a license agreement containing restrictions on use and disclosure and are also protected by copyright, patent, and other intellectual and industrial propert ...
Oracle Essentials Fifth Edition
... syntax. There simply isn’t room for myriad syntax diagrams and examples in this book. Uniqueness We’ve tried to make this an ideal first Oracle book for a wide spectrum of Oracle users—but not the last! You will very likely have to refer to Oracle documentation or other, more specific books for more ...
... syntax. There simply isn’t room for myriad syntax diagrams and examples in this book. Uniqueness We’ve tried to make this an ideal first Oracle book for a wide spectrum of Oracle users—but not the last! You will very likely have to refer to Oracle documentation or other, more specific books for more ...
1.2 Oracle Database High Availability Best Practices
... transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice an ...
... transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice an ...
Command Reference
... Provides information on how to use SQL statements from the command line. Appendix A Explains the conventions used in syntax diagrams. Appendix B Explains the conventions used to name objects such as databases and tables. ...
... Provides information on how to use SQL statements from the command line. Appendix A Explains the conventions used in syntax diagrams. Appendix B Explains the conventions used to name objects such as databases and tables. ...
SESAM/SQL-Server V8.0 BS2000/OSD Core Manual
... according to DIN EN ISO 9001:2008 To ensure a consistently high quality standard and user-friendliness, this documentation was created to meet the regulations of a quality management system which complies with the requirements of the standard DIN EN ISO 9001:2008. cognitas. Gesellschaft für Technik- ...
... according to DIN EN ISO 9001:2008 To ensure a consistently high quality standard and user-friendliness, this documentation was created to meet the regulations of a quality management system which complies with the requirements of the standard DIN EN ISO 9001:2008. cognitas. Gesellschaft für Technik- ...
Oracle Essentials: Oracle Database 11g
... audiences include DBAs who spend most of their workday managing Oracle, application developers who build their systems on the data available in an Oracle database, and system administrators who are concerned with how Oracle will affect their computing environments. Of course, IT managers and busines ...
... audiences include DBAs who spend most of their workday managing Oracle, application developers who build their systems on the data available in an Oracle database, and system administrators who are concerned with how Oracle will affect their computing environments. Of course, IT managers and busines ...
Teradata Archive/Recovery Utility Reference
... Corporation will be free to use any ideas, concepts, know-how, or techniques contained in such Feedback for any purpose whatsoever, including developing, manufacturing, or marketing products or services incorporating Feedback. Copyright © 1997-2008 by Teradata Corporation. All Rights Reserved. ...
... Corporation will be free to use any ideas, concepts, know-how, or techniques contained in such Feedback for any purpose whatsoever, including developing, manufacturing, or marketing products or services incorporating Feedback. Copyright © 1997-2008 by Teradata Corporation. All Rights Reserved. ...
SQL Server Backup and Restore
... Server 6.5 instance, on Windows NT, and it hosted every database for every client that the company serviced. There was no dedicated administration team; just a few developers and the owner. One day, I was watching and learning from a fellow developer while he made code changes to one of our backend ...
... Server 6.5 instance, on Windows NT, and it hosted every database for every client that the company serviced. There was no dedicated administration team; just a few developers and the owner. One day, I was watching and learning from a fellow developer while he made code changes to one of our backend ...






![OReilly.Enterprise.JavaBeans.3.0.5th.Edition.May.2006 [EJB 3.0]](http://s1.studyres.com/store/data/002282153_1-6366a42d074c8a52020a645f2635ed64-300x300.png)