Document
... • Writing to and reading from the memory takes no time and can be shared • We can use as many processors as we wish (for different instances of the same problem different number of processors can be used), but this number is polynomial in the size of the input - from the point of view of complexity ...
... • Writing to and reading from the memory takes no time and can be shared • We can use as many processors as we wish (for different instances of the same problem different number of processors can be used), but this number is polynomial in the size of the input - from the point of view of complexity ...
A Quick Overview of Computational Complexity
... •MST •Shortest path O(N log N ) •Search for similar case O(N ) (assuming constant similarity) O(log N) •Binary search ordered array • all the other sorts: O(1) •Simple instruction ...
... •MST •Shortest path O(N log N ) •Search for similar case O(N ) (assuming constant similarity) O(log N) •Binary search ordered array • all the other sorts: O(1) •Simple instruction ...
Document
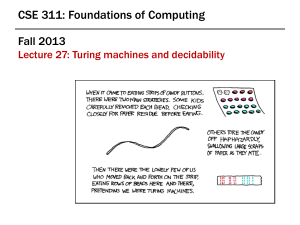
... would actually want to compute? – The argument does not even give any example of something that can’t be done, it just says that such an example exists ...
... would actually want to compute? – The argument does not even give any example of something that can’t be done, it just says that such an example exists ...
Mathematical Research and Modeling for the Army
... Key application areas are computational fluid dynamics for ballistics and rotorcraft, combustion, detonation, mechanics of penetration, material behavior, computational chemistry, simulation of large mechanical systems, vulnerability analysis, logistics, and resource management. The areas of invest ...
... Key application areas are computational fluid dynamics for ballistics and rotorcraft, combustion, detonation, mechanics of penetration, material behavior, computational chemistry, simulation of large mechanical systems, vulnerability analysis, logistics, and resource management. The areas of invest ...
Humans, Computer, and Computational Complexity
... notion. The technical details are difficult however the key ideas within the proof demonstrate the power of paradox in showing the limits of formal mathematics. The key example to consider is the statement: “This statement is unprovable”. Within a formal mathematical system, a statement can only hav ...
... notion. The technical details are difficult however the key ideas within the proof demonstrate the power of paradox in showing the limits of formal mathematics. The key example to consider is the statement: “This statement is unprovable”. Within a formal mathematical system, a statement can only hav ...
Department of Applied Mathematics and Physics Engineering
... various things, from mobile vehicles such as automobiles and aircraft to production systems for the steel production process. For example, preventing vibration on robot manipulators is also a control task. We need to extract characteristics that are important to control from a control object that di ...
... various things, from mobile vehicles such as automobiles and aircraft to production systems for the steel production process. For example, preventing vibration on robot manipulators is also a control task. We need to extract characteristics that are important to control from a control object that di ...
Introduction. - philosophica
... Aristotle tried to reduce the complexity by looking for building blocks, essential principles or universal causes. With the development of the experimental method in the seventeenth century, along with the use of mathematics, the understanding of complexity by studying it in its more simple componen ...
... Aristotle tried to reduce the complexity by looking for building blocks, essential principles or universal causes. With the development of the experimental method in the seventeenth century, along with the use of mathematics, the understanding of complexity by studying it in its more simple componen ...
Theoretical Foundation for Jung`s "Mandala Symbolism" Based on
... Breaking results, related to the living systems dynamics, have been obtained in chaos theory, when it became clear that chaotic regimes and "chaotic systems" have not only the same right to exist in nature as the systems with regular deterministic behavior, but in fact extremely sensitive to the inf ...
... Breaking results, related to the living systems dynamics, have been obtained in chaos theory, when it became clear that chaotic regimes and "chaotic systems" have not only the same right to exist in nature as the systems with regular deterministic behavior, but in fact extremely sensitive to the inf ...
PDF
... number because it is the sum of 1 and 47, and no other pair. 49 is not an Ulam number because it is the sum of 1 and 48, and of 2 and 47. Stanislaw Ulam first studied this sequences in the 1960s “in a peculiar attempt to get a 1D analog of a 2D cellular automaton” (Wolfram, 2002). In 2001 Jud McCran ...
... number because it is the sum of 1 and 47, and no other pair. 49 is not an Ulam number because it is the sum of 1 and 48, and of 2 and 47. Stanislaw Ulam first studied this sequences in the 1960s “in a peculiar attempt to get a 1D analog of a 2D cellular automaton” (Wolfram, 2002). In 2001 Jud McCran ...
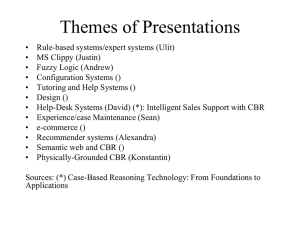
Slides.
... on instances. Quite likely infeasible to get a match with “real-world” problem distribution. Computational tasks are studied as if they were a formal mathematical object. ...
... on instances. Quite likely infeasible to get a match with “real-world” problem distribution. Computational tasks are studied as if they were a formal mathematical object. ...
Slides - Department of Computer Science
... on instances. Quite likely infeasible to get a match with “real-world” problem distribution. Computational tasks are studied as if they were a formal mathematical object. ...
... on instances. Quite likely infeasible to get a match with “real-world” problem distribution. Computational tasks are studied as if they were a formal mathematical object. ...
Parallel Computation
... • Writing to and reading from the memory takes no time and can be shared • We can use as many processors as we wish (for different instances of the same problem different number of processors can be used), but this number is polynomial in the size of the input - from the point of view of complexity ...
... • Writing to and reading from the memory takes no time and can be shared • We can use as many processors as we wish (for different instances of the same problem different number of processors can be used), but this number is polynomial in the size of the input - from the point of view of complexity ...
some methods of the investigation of chaotic behaviour on
... the asymptotic behaviour must be contained in I. Fig.1. shows computer generated orbits for a large number of iterations for a discrete set of values of a, separated by narrow intervals.(Feigenbaum’s diagram). The orbit generated for fixed a approximates an asymptotic limit set. In the scale of Fig. ...
... the asymptotic behaviour must be contained in I. Fig.1. shows computer generated orbits for a large number of iterations for a discrete set of values of a, separated by narrow intervals.(Feigenbaum’s diagram). The orbit generated for fixed a approximates an asymptotic limit set. In the scale of Fig. ...
On three consecutive primes
... [4] Nagura, J. "On the interval containing at least one prime number." Proceedings of the Japan Academy, Series A 28 (1952), pp. 177--181. [5] Ishikawa, H. "Über die Verteilung der Primzahlen." Science Rep. Tokyo Bunrika Daigaku 2, 27-4 ...
... [4] Nagura, J. "On the interval containing at least one prime number." Proceedings of the Japan Academy, Series A 28 (1952), pp. 177--181. [5] Ishikawa, H. "Über die Verteilung der Primzahlen." Science Rep. Tokyo Bunrika Daigaku 2, 27-4 ...
Introduction to Symbolic Computation for Engineers
... Based on the book of Winkler F. Polynomial Algorithms in Computer Algebra. Springer Verlag (1996). ...
... Based on the book of Winkler F. Polynomial Algorithms in Computer Algebra. Springer Verlag (1996). ...
0,1 - Duke University
... • Simulate the effect of this transition on the coded input and the stored state (Tapes 2 and 3); • Search the list of transitions for one that applies in the new situation; • Continue until a final state is reached. (Marvin Minsky designed a UTM using only 7 states and 4 symbols in 1962. No one has ...
... • Simulate the effect of this transition on the coded input and the stored state (Tapes 2 and 3); • Search the list of transitions for one that applies in the new situation; • Continue until a final state is reached. (Marvin Minsky designed a UTM using only 7 states and 4 symbols in 1962. No one has ...
bioweek9
... Pickover, C. (1990). Computers, pattern, chaos and beauty, Alan Sutton Publishing, Stroud, UK. ISBN 0862997925 (not in UniS library) Mandlebrot, B. (1982). The Fractal Geometry of Nature (Updated and augmented). Freeman, New York. ...
... Pickover, C. (1990). Computers, pattern, chaos and beauty, Alan Sutton Publishing, Stroud, UK. ISBN 0862997925 (not in UniS library) Mandlebrot, B. (1982). The Fractal Geometry of Nature (Updated and augmented). Freeman, New York. ...
MS-Word version
... to explore further the additive theory of infinite sets of prime numbers, both with absolute results and its links with number theory via the Schinzel's hypothesis ; to code natural numbers, complex numbers, and quadratic integers by automata accepting numbers (written in non-classical systems) ; to ...
... to explore further the additive theory of infinite sets of prime numbers, both with absolute results and its links with number theory via the Schinzel's hypothesis ; to code natural numbers, complex numbers, and quadratic integers by automata accepting numbers (written in non-classical systems) ; to ...
Chapter 2: Evaluate Parallel Program
... The equation to compute the communication time ignore the fact that the source and destination may not be directly linked in a real system so that the message may pass through intermediate nodes. It is also assumed that the overhead incurred by including information other than data in the packet is ...
... The equation to compute the communication time ignore the fact that the source and destination may not be directly linked in a real system so that the message may pass through intermediate nodes. It is also assumed that the overhead incurred by including information other than data in the packet is ...
SUBS 6370: Computational Methods and Design Experiments
... verification/validation will be highlighted. This topic will conclude with a review of simulation steps needed to conduct a proper computer simulation with application to an open-ended engineering problem with optimization as a key objective. ...
... verification/validation will be highlighted. This topic will conclude with a review of simulation steps needed to conduct a proper computer simulation with application to an open-ended engineering problem with optimization as a key objective. ...
ppt
... we have enough information to find it. However, actually getting the answer from the inputs is not feasible due to the complexity of the problem. This is not like asking “will the human race exist in 5,000 years” – we do not have enough information to answer that ...
... we have enough information to find it. However, actually getting the answer from the inputs is not feasible due to the complexity of the problem. This is not like asking “will the human race exist in 5,000 years” – we do not have enough information to answer that ...
Slides for Rosen, 5th edition
... • Mathematics is much more than that: Mathematics is, most generally, the study of any and all absolutely certain truths about any and all perfectly well-defined concepts. ...
... • Mathematics is much more than that: Mathematics is, most generally, the study of any and all absolutely certain truths about any and all perfectly well-defined concepts. ...
GRAMMAR 1B MOCK EXAM A. Give the past tense and the
... the sentence is correct, write down ‘correct’. 14 points (1 for correction, 1 for correct rule) 1. In 2014, the Russians are occupying this country for twenty years. 2. When my brother and his wife arrived, the rest of us had had dinner already. 3. Please be quiet – Sally tries to write an essay. 4. ...
... the sentence is correct, write down ‘correct’. 14 points (1 for correction, 1 for correct rule) 1. In 2014, the Russians are occupying this country for twenty years. 2. When my brother and his wife arrived, the rest of us had had dinner already. 3. Please be quiet – Sally tries to write an essay. 4. ...