Data Mining Methods for Detection of New Malicious Executables
... To compare the data mining methods with a traditional signature-based method, we designed an automatic signature generator. Since the virus scanner that we used to label the data set had signatures for every malicious example in our data set, it was necessary to implement a similar signature-based m ...
... To compare the data mining methods with a traditional signature-based method, we designed an automatic signature generator. Since the virus scanner that we used to label the data set had signatures for every malicious example in our data set, it was necessary to implement a similar signature-based m ...
A Novel Classification Approach for C2C E
... In fraud detection research, there are several widely used classification algorithms which are naïve Byes, C4.5 decision tree, AdaBoost and so on[7-9]. 1) Naive Bayes Naive Bayes is a simple probabilistic classifier based on applying Bayes theorem with naïve independence assumptions. It assumes that ...
... In fraud detection research, there are several widely used classification algorithms which are naïve Byes, C4.5 decision tree, AdaBoost and so on[7-9]. 1) Naive Bayes Naive Bayes is a simple probabilistic classifier based on applying Bayes theorem with naïve independence assumptions. It assumes that ...
Sentiment Analysis on Twitter with Stock Price and Significant
... Networks on Twitter and DJIA feeds. In their research, they created a custom questionnaire with words to analyze tweets for their sentiment. Their work is similar to [4], with a few minor modifications. On a side note, [12] discusses some common problems involved in many of the techniques presented ...
... Networks on Twitter and DJIA feeds. In their research, they created a custom questionnaire with words to analyze tweets for their sentiment. Their work is similar to [4], with a few minor modifications. On a side note, [12] discusses some common problems involved in many of the techniques presented ...
Data Mining Lab Manual
... Note: this example is extremely small. In practical applications, a rule needs a support of several hundred transactions before it can be considered statistically significant, and datasets often contain thousands or millions of transactions. To select interesting rules from the set of all possible r ...
... Note: this example is extremely small. In practical applications, a rule needs a support of several hundred transactions before it can be considered statistically significant, and datasets often contain thousands or millions of transactions. To select interesting rules from the set of all possible r ...
Bayesian learning
... between proteins for gene SVS1. The width of edges corresponds to the conditional probability. ...
... between proteins for gene SVS1. The width of edges corresponds to the conditional probability. ...
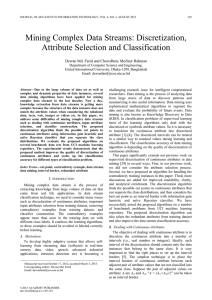
A Clustering based Discretization for Supervised Learning
... instance space. Global methods [6], on the other hand, use the entire instance space and forms a mesh over the entire n-dimensional continuous instance space, where each feature is partitioned into regions independent of other attributes. • Static discretization methods require some parameter, k, in ...
... instance space. Global methods [6], on the other hand, use the entire instance space and forms a mesh over the entire n-dimensional continuous instance space, where each feature is partitioned into regions independent of other attributes. • Static discretization methods require some parameter, k, in ...
Classification: basic concepts
... Let X be a data sample (“evidence”): class label is unknown Let H be a hypothesis that X belongs to class C Classification is to determine P(H|X), (i.e., posteriori probability): the probability that the hypothesis holds given the observed data sample X P(H) (prior probability): the initial probabil ...
... Let X be a data sample (“evidence”): class label is unknown Let H be a hypothesis that X belongs to class C Classification is to determine P(H|X), (i.e., posteriori probability): the probability that the hypothesis holds given the observed data sample X P(H) (prior probability): the initial probabil ...
pdf preprint - UWO Computer Science
... distributions of data are highly imbalanced. Again, without loss of generality, we assume that the minority or rare class is the positive class, and the majority class is the negative class. Often the minority class is very small, such as 1% of the dataset. If we apply most traditional (costinsensit ...
... distributions of data are highly imbalanced. Again, without loss of generality, we assume that the minority or rare class is the positive class, and the majority class is the negative class. Often the minority class is very small, such as 1% of the dataset. If we apply most traditional (costinsensit ...
toward optimal feature selection using ranking methods and
... It is possible to derive a general architecture from most of the feature selection algorithms. It consists of four basic steps (refer to Figure 1): subset generation, subset evaluation, stopping criterion, and result validation [7]. The feature selection algorithms create a subset, evaluate it, and ...
... It is possible to derive a general architecture from most of the feature selection algorithms. It consists of four basic steps (refer to Figure 1): subset generation, subset evaluation, stopping criterion, and result validation [7]. The feature selection algorithms create a subset, evaluate it, and ...
Machine learning: a review of classification and combining techniques
... outcome and uses the other features as predictors. • Hot deck inputting: The most similar case to the case with a missing value is identified, and then a similar case’s Y value for the missing case’s Y value is substituted. • Method of treating missing feature values as special values: “Unknown” its ...
... outcome and uses the other features as predictors. • Hot deck inputting: The most similar case to the case with a missing value is identified, and then a similar case’s Y value for the missing case’s Y value is substituted. • Method of treating missing feature values as special values: “Unknown” its ...
A Comparative Performance Analysis of Classification
... classification. Classification is classified into different models, these are followed:Types of classification models:o Classification by decision tree induction o Bayesian Classification o Neural Networks o Support Vector Machines (SVM) o Classification Based on Associations 3. WEKA TOOL Weka is a ...
... classification. Classification is classified into different models, these are followed:Types of classification models:o Classification by decision tree induction o Bayesian Classification o Neural Networks o Support Vector Machines (SVM) o Classification Based on Associations 3. WEKA TOOL Weka is a ...
Decision Tree and Naïve Bayes Algorithm
... the limited resource problems and designing a greedy heuristic algorithm to solve it efficiently. There is a comparison of the performance of the exhaustive search algorithm with a greedy heuristic algorithm, and the authors show that the greedy algorithm is efficient. The paper integrates between d ...
... the limited resource problems and designing a greedy heuristic algorithm to solve it efficiently. There is a comparison of the performance of the exhaustive search algorithm with a greedy heuristic algorithm, and the authors show that the greedy algorithm is efficient. The paper integrates between d ...
CANCER MICROARRAY DATA FEATURE SELECTION USING
... Cancer investigations in microarray data play a major role in cancer analysis and the treatment. Cancer microarray data consists of complex gene expressed patterns of cancer. In this article, a Multi-Objective Binary Particle Swarm Optimization (MOBPSO) algorithm is proposed for analyzing cancer gen ...
... Cancer investigations in microarray data play a major role in cancer analysis and the treatment. Cancer microarray data consists of complex gene expressed patterns of cancer. In this article, a Multi-Objective Binary Particle Swarm Optimization (MOBPSO) algorithm is proposed for analyzing cancer gen ...