BLIND QUANTUM COMPUTATION 1. Introduction and Background
... Unfortunately, in general, the commutation relations between arbitrary U and random Pauli matrix is not easy to calculate. The blind algorithm is described in general having Alice retrieve the encrypted data, decrypt it, run the computation herself, re-encrypt the data, and return it to Bob. Effecti ...
... Unfortunately, in general, the commutation relations between arbitrary U and random Pauli matrix is not easy to calculate. The blind algorithm is described in general having Alice retrieve the encrypted data, decrypt it, run the computation herself, re-encrypt the data, and return it to Bob. Effecti ...
Quantum Programming Languages: Survey and Bibliography
... Firstly, it overlooks the dramatic progress that has been made in the practical implementation of quantum cryptographic systems. Components for these systems are now commercially available, and it seems very likely that quantum cryptography will be an important technology long before quantum compute ...
... Firstly, it overlooks the dramatic progress that has been made in the practical implementation of quantum cryptographic systems. Components for these systems are now commercially available, and it seems very likely that quantum cryptography will be an important technology long before quantum compute ...
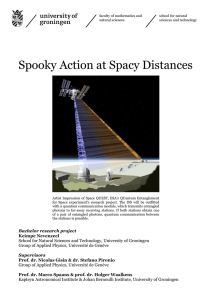
Spooky Action at Spacy Distances
... to establish such a network. ESA’s program, the Space-QUEST program, currently brings the first experimental hardware up to TRL3, launch of this hardware is envisioned for 2015. The fundamental property of quantum mechanics that allows quantum communication is non-locality. Non-local quantum states ...
... to establish such a network. ESA’s program, the Space-QUEST program, currently brings the first experimental hardware up to TRL3, launch of this hardware is envisioned for 2015. The fundamental property of quantum mechanics that allows quantum communication is non-locality. Non-local quantum states ...
950 - IACR
... (modeled as a functionality) such that the owner of the card can sign messages, everyone can access the public key, and no-one (not even the owner) can get the secret key.4 Their protocol is, however, only known to be secure in the classical setting. In fact, when we try to prove the protocol secure ...
... (modeled as a functionality) such that the owner of the card can sign messages, everyone can access the public key, and no-one (not even the owner) can get the secret key.4 Their protocol is, however, only known to be secure in the classical setting. In fact, when we try to prove the protocol secure ...
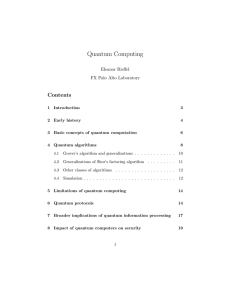
Quantum Computing
... Deutsch developed a notion of a quantum mechanical Turing machine. Bernstein, Vazirani, and Yao showed that quantum computers can do anything a classical computer can do with at most a small (logarithmic) slow down. The early 1990s saw the first truly quantum algorithms, algorithms with no classica ...
... Deutsch developed a notion of a quantum mechanical Turing machine. Bernstein, Vazirani, and Yao showed that quantum computers can do anything a classical computer can do with at most a small (logarithmic) slow down. The early 1990s saw the first truly quantum algorithms, algorithms with no classica ...
Introduction to Quantum Computing (2010) (e-book)
... considering that the simulation is approximate, given any accuracy, a braid can be found, and it will simulate the computation to that accuracy. In the experimental point of view, there are already many approaches of realizing a quantum computer. The optical approach in trapping of ions, the use of ...
... considering that the simulation is approximate, given any accuracy, a braid can be found, and it will simulate the computation to that accuracy. In the experimental point of view, there are already many approaches of realizing a quantum computer. The optical approach in trapping of ions, the use of ...
Investigating incompatibility: How to reconcile complementarity with EPR C
... The traditional picture drawn about the Bohr-EPR debate is that of utter contrast, to which Bohr’s own reply to EPR constitutes no exception. Bohr’s reply to EPR is incompatible with EPR. This is exactly what it was intended to be right from the start and it would not be a reply in his mind if it we ...
... The traditional picture drawn about the Bohr-EPR debate is that of utter contrast, to which Bohr’s own reply to EPR constitutes no exception. Bohr’s reply to EPR is incompatible with EPR. This is exactly what it was intended to be right from the start and it would not be a reply in his mind if it we ...
pdf
... relevant to the work described here. In particular, one key constraint in quantum computation is the no cloning theorem [33], which states that a superposition state cannot be perfectly copied from one qubit to another qubit, without destroying the first one. Thus, in order to use the state of a qub ...
... relevant to the work described here. In particular, one key constraint in quantum computation is the no cloning theorem [33], which states that a superposition state cannot be perfectly copied from one qubit to another qubit, without destroying the first one. Thus, in order to use the state of a qub ...
Tree Search and Quantum Computation
... search through the state space systematically checks if the current state is a goal state. If a nongoal state is discovered then the current state is expanded by applying a successor function, generating a new set of states. The choice of which state to expand is determined by a search strategy. In ...
... search through the state space systematically checks if the current state is a goal state. If a nongoal state is discovered then the current state is expanded by applying a successor function, generating a new set of states. The choice of which state to expand is determined by a search strategy. In ...
Quantum Physics and the Holy Grail BRIAN JOHN PICCOLO
... Quantum Physics & The Holy Grail - 8 consciousness.5 This means that at every one of the four stages of human consciousness, they are fully self aware and functioning. They do not dream, or sleep, nor are they ever unconscious. They are consciously one with their Higher Self. They have transformed ...
... Quantum Physics & The Holy Grail - 8 consciousness.5 This means that at every one of the four stages of human consciousness, they are fully self aware and functioning. They do not dream, or sleep, nor are they ever unconscious. They are consciously one with their Higher Self. They have transformed ...
Exciton Fine-Structure Splitting in Self- Assembled Lateral InAs/GaAs Quantum-Dot Molecular Structures
... QMSs, no correlation can be found between the aspect ratio and the FSS. Furthermore, the DQD1 sample with the smaller sizes and the larger lateral shape anisotropy of individual QDs than those in the DQD-2 sample should exhibit larger FSS15 if only the shape anisotropy is considered. This is inconsi ...
... QMSs, no correlation can be found between the aspect ratio and the FSS. Furthermore, the DQD1 sample with the smaller sizes and the larger lateral shape anisotropy of individual QDs than those in the DQD-2 sample should exhibit larger FSS15 if only the shape anisotropy is considered. This is inconsi ...
From Quantum Gates to Quantum Learning
... • A quantum (combinational) circuit is a sequence of quantum gates, linked by “wires” • The circuit has fixed “width” corresponding to the number of qubits being processed • Logic design (classical and quantum) attempts to find circuit structures for needed operations that are ...
... • A quantum (combinational) circuit is a sequence of quantum gates, linked by “wires” • The circuit has fixed “width” corresponding to the number of qubits being processed • Logic design (classical and quantum) attempts to find circuit structures for needed operations that are ...