Rio3224-D/Rio1608-D Owner`s Manual
... expressly approved by Yamaha may void your authority, granted by the FCC, to use the product. 2. IMPORTANT: When connecting this product to accessories and/ or another product use only high quality shielded cables. Cable/s supplied with this product MUST be used. Follow all installation instructions ...
... expressly approved by Yamaha may void your authority, granted by the FCC, to use the product. 2. IMPORTANT: When connecting this product to accessories and/ or another product use only high quality shielded cables. Cable/s supplied with this product MUST be used. Follow all installation instructions ...
Ethernet for Industrial Automation
... Ethernet has been used in automation applications for more than 15 years. It is the oldest LAN technology on the factory floor. Most PLCs have Ethernet option now. Ethernet that transmits programs, diagnostics, operator data is in widespread use. ...
... Ethernet has been used in automation applications for more than 15 years. It is the oldest LAN technology on the factory floor. Most PLCs have Ethernet option now. Ethernet that transmits programs, diagnostics, operator data is in widespread use. ...
Ethernet for Industrial Automation
... Ethernet has been used in automation applications for more than 15 years. It is the oldest LAN technology on the factory floor. Most PLCs have Ethernet option now. Ethernet that transmits programs, diagnostics, operator data is in widespread use. ...
... Ethernet has been used in automation applications for more than 15 years. It is the oldest LAN technology on the factory floor. Most PLCs have Ethernet option now. Ethernet that transmits programs, diagnostics, operator data is in widespread use. ...
TC-20020308-035_GSC7_EWG_TIA_update
... • A Committee volunteer is the list administrator with help of TIA staff • Initial reflector list is established by TIA staff ...
... • A Committee volunteer is the list administrator with help of TIA staff • Initial reflector list is established by TIA staff ...
ruggedcom rx1500/1501
... interior gateway protocol (IGP), which is designed to work within an autonomous system. It is also a link state protocol, meaning that the best route is determined by the type and speed of the inter-router links, not by how many router hops they are away from each other (as in Distance-Vector routin ...
... interior gateway protocol (IGP), which is designed to work within an autonomous system. It is also a link state protocol, meaning that the best route is determined by the type and speed of the inter-router links, not by how many router hops they are away from each other (as in Distance-Vector routin ...
Physical plane for Intelligent Network Capability Set 2
... CS-2 is identified, and functional interfaces suitable for standardization are highlighted. The PEs described in this subclause are for illustrative purposes only, and do not imply the only possible mapping of functionality for CS-2. This subclause describes a flexible physical architecture made up ...
... CS-2 is identified, and functional interfaces suitable for standardization are highlighted. The PEs described in this subclause are for illustrative purposes only, and do not imply the only possible mapping of functionality for CS-2. This subclause describes a flexible physical architecture made up ...
Text String Activation
... For single Message Center connection use RS232 wiring method. For multiple Message Center operation use RS485 wiring method. A PLC can be used to send a complete message to one or more Message Centers. Or the PLC can activate a previously loaded message in one or more Message Centers. A PLC can be u ...
... For single Message Center connection use RS232 wiring method. For multiple Message Center operation use RS485 wiring method. A PLC can be used to send a complete message to one or more Message Centers. Or the PLC can activate a previously loaded message in one or more Message Centers. A PLC can be u ...
EPL-Router sorgt für Transparenz und Durchgängigkeit
... The Ethernet Powerlink-Router is equipped with two Ethernet-ports and connects two networks on IP-level. For this purpose it requires two IEEE802.3-compliant network accesses. The real-time port is connected with an Ethernet-Powerlink-segment. The second port is the interface to an IPnetwork, the so ...
... The Ethernet Powerlink-Router is equipped with two Ethernet-ports and connects two networks on IP-level. For this purpose it requires two IEEE802.3-compliant network accesses. The real-time port is connected with an Ethernet-Powerlink-segment. The second port is the interface to an IPnetwork, the so ...
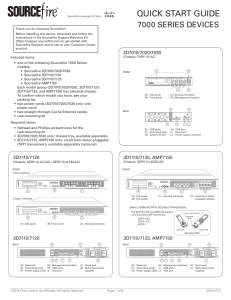
http://www.cisco.com/c/dam/en/us/td/docs/security/sourcefire/3d-system/53/quick-start-guides/QSG-3D7xxx-v53-3-20140311.pdf
... is connected to your trusted management network and the various network segments you want to monitor. In a simple deployment scenario, you connect the management interface on your device to your trusted management network using an Ethernet cable, then connect the sensing interfaces to the network se ...
... is connected to your trusted management network and the various network segments you want to monitor. In a simple deployment scenario, you connect the management interface on your device to your trusted management network using an Ethernet cable, then connect the sensing interfaces to the network se ...
arp
... – NIC accepts Ethernet frame addressed to it – Passes to OS via interrupt – OS determines frame type and passes for handling as IP – Checks packet is not corrupt – Checks destination IP address If local, continue processing for local delivery If not local… ...
... – NIC accepts Ethernet frame addressed to it – Passes to OS via interrupt – OS determines frame type and passes for handling as IP – Checks packet is not corrupt – Checks destination IP address If local, continue processing for local delivery If not local… ...
Unit 2 Lesson 5
... The token with its encapsulated data travels around the network from one computer to the next, where each device accepts the frame and checks the destination address. If the hardware addresses match, the device processes the data, if it does not match the data is retransmitted to the next device unt ...
... The token with its encapsulated data travels around the network from one computer to the next, where each device accepts the frame and checks the destination address. If the hardware addresses match, the device processes the data, if it does not match the data is retransmitted to the next device unt ...
Documentation
... application. Unauthorized modifications and changes to the hardware or software configuration, which go beyond the documented options, are prohibited and nullify the liability of Beckhoff Automation GmbH & Co. ...
... application. Unauthorized modifications and changes to the hardware or software configuration, which go beyond the documented options, are prohibited and nullify the liability of Beckhoff Automation GmbH & Co. ...
Voice Over IP
... Step 5 Establish a dial plan to determine how the call can be routed. Use the dial-peer voice command to define dial peers and to implement the dial plan. Step 6 Fine-tune your network to adequately support VoIP by configuring a series of protocols and features for quality of service ...
... Step 5 Establish a dial plan to determine how the call can be routed. Use the dial-peer voice command to define dial peers and to implement the dial plan. Step 6 Fine-tune your network to adequately support VoIP by configuring a series of protocols and features for quality of service ...
10/100/1000 and Gig-E Testing SmartClass™ Ethernet
... Enables a low cost single ended loopback device for latency and RFC 2544 testing across a network Filter and analyze incoming traffic to determine customer throughput and QoS Check that circuit is up and connected and physical layer is correct Professional Report Generation for validating or storing ...
... Enables a low cost single ended loopback device for latency and RFC 2544 testing across a network Filter and analyze incoming traffic to determine customer throughput and QoS Check that circuit is up and connected and physical layer is correct Professional Report Generation for validating or storing ...
Ethernet over 4 E1 / 8 E1 / 16 E1 - IP over TDM
... Supports GFP-F encapsulation complying with ITU-T G.7041 Supports port based Ethernet bandwidth limit for ingress traffic Port based Ethernet limit allows user to provide different speed for the different customers to utilize bandwidth according to their requirement Supports differential del ...
... Supports GFP-F encapsulation complying with ITU-T G.7041 Supports port based Ethernet bandwidth limit for ingress traffic Port based Ethernet limit allows user to provide different speed for the different customers to utilize bandwidth according to their requirement Supports differential del ...
CCNA Cheat Sheet Internetworking Essentials
... © Copyright 2010 Internetwork Training – Although the authors of have made every effort to ensure the information in this document is correct, the authors do not assume and hereby disclaim any liability to any party for loss or damage caused by errors, omissions or misleading information. ...
... © Copyright 2010 Internetwork Training – Although the authors of have made every effort to ensure the information in this document is correct, the authors do not assume and hereby disclaim any liability to any party for loss or damage caused by errors, omissions or misleading information. ...
Ethernet - ECE Users Pages
... multicast addresses. This makes it possible for a set of stations to be assigned to a multicast group which has been given a specific multicast address. A single packet sent to the multicast address assigned to that group will then be received by all stations in that group. • There is also the speci ...
... multicast addresses. This makes it possible for a set of stations to be assigned to a multicast group which has been given a specific multicast address. A single packet sent to the multicast address assigned to that group will then be received by all stations in that group. • There is also the speci ...
a Engineer-to-Engineer Note EE-269
... The 100Base-TX transfers data with Multilevel Threshold-3 (MLT3) mechanism at the line. Three values (+1, 0, and -.1) are possible to code from NRZI signal and vice versa. The benefit of the MLT3 method is to half the NRZI transfer frequency from 62.5 MHz to 31.25 MHz. In 100Base-TX transmission req ...
... The 100Base-TX transfers data with Multilevel Threshold-3 (MLT3) mechanism at the line. Three values (+1, 0, and -.1) are possible to code from NRZI signal and vice versa. The benefit of the MLT3 method is to half the NRZI transfer frequency from 62.5 MHz to 31.25 MHz. In 100Base-TX transmission req ...
1 - IC Intracom
... Example 1 The Converter allows the conversion from 10Base-T UTP to 10Base-2 Coaxial cable. In this configuration, equipment can be added to existing 10Base-T networks. Distances of up to 185 meters can be achieved. Ethernet Hub/Switch ...
... Example 1 The Converter allows the conversion from 10Base-T UTP to 10Base-2 Coaxial cable. In this configuration, equipment can be added to existing 10Base-T networks. Distances of up to 185 meters can be achieved. Ethernet Hub/Switch ...
RuggedBackbone™ RX1500/1501
... interior gateway protocol (IGP), which is designed to work within an autonomous system. It is also a link state protocol, meaning that the best route is determined by the type and speed of the inter-router links, not by how many router hops they are away from each other (as in Distance-Vector routin ...
... interior gateway protocol (IGP), which is designed to work within an autonomous system. It is also a link state protocol, meaning that the best route is determined by the type and speed of the inter-router links, not by how many router hops they are away from each other (as in Distance-Vector routin ...
A Beginner`s Guide to Ethernet 802.3 Application Note (EE-269)
... The 100Base-TX transfers data with Multilevel Threshold-3 (MLT3) mechanism at the line. Three values (+1, 0, and -.1) are possible to code from NRZI signal and vice versa. The benefit of the MLT3 method is to half the NRZI transfer frequency from 62.5 MHz to 31.25 MHz. In 100Base-TX transmission req ...
... The 100Base-TX transfers data with Multilevel Threshold-3 (MLT3) mechanism at the line. Three values (+1, 0, and -.1) are possible to code from NRZI signal and vice versa. The benefit of the MLT3 method is to half the NRZI transfer frequency from 62.5 MHz to 31.25 MHz. In 100Base-TX transmission req ...
WAVE Interface Modules
... You must retain the same link speed from one end of the connection to the other end. Inline adapter interfaces are able to autonegotiate link speeds. If you configure any of your connecting interfaces for Fast Ethernet (whether on a switch or a router), your WAVE inline adapter uses Fast Ethernet. I ...
... You must retain the same link speed from one end of the connection to the other end. Inline adapter interfaces are able to autonegotiate link speeds. If you configure any of your connecting interfaces for Fast Ethernet (whether on a switch or a router), your WAVE inline adapter uses Fast Ethernet. I ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE) ISSN: , PP: 39-43 www.iosrjournals.org
... arise because enterprises need to retain control over their own VLAN administration (such as assigning Q-tags to VLANs), and over a shared infrastructure the service provider must control this to ensure that one customer’s Q-tags do not overlap with another’s. Also, because the Q-tag consists of a 1 ...
... arise because enterprises need to retain control over their own VLAN administration (such as assigning Q-tags to VLANs), and over a shared infrastructure the service provider must control this to ensure that one customer’s Q-tags do not overlap with another’s. Also, because the Q-tag consists of a 1 ...
Registered jack

A Registered Jack (RJ) is a standardized telecommunication network interface for connecting voice and data equipment to a service provided by a local exchange carrier or long distance carrier. Registration interfaces were first defined in the Universal Service Ordering Code (USOC) system of the Bell System in the United States for complying with the registration program for customer-supplied telephone equipment mandated by the Federal Communications Commission (FCC) in the 1970s. They were subsequently codified in the Code of Federal Regulations Part 68.The specification includes physical construction, wiring, and signal semantics. Accordingly, registered jacks are primarily named by the letters RJ, followed by two digits that express the type. Additionally, letter suffixes indicate minor variations. For example, RJ11, RJ14, and RJ25 are the most commonly used interfaces for telephone connections for one-, two-, and three-line service, respectively. Although these standards are legal definitions in the United States, some interfaces are used world-wide. Specifically, for example, the IEEE 802 standards project has adopted RJ-type interfaces for ISDN (RJ48) and computer networking specifications (RJ45), such as Ethernet.The connectors used for registered jack installations are primarily the modular connector and the 50-pin miniature ribbon connector types. For example, RJ11 uses a six-position two-conductor connector (6P2C), RJ14 uses a six-position four-conductor (6P4C) modular jack, while RJ21 uses a 25-pair (50-pin) miniature ribbon connector.