Text12-DynamicArrays
... There are more methods in the ArrayList class. The six methods in this section are AP tested methods, because they are the most common methods and allow a wide range of data processing with a dynamic array. It may seem that the ArrayList, with all its methods and dynamic resizing, is so superior to ...
... There are more methods in the ArrayList class. The six methods in this section are AP tested methods, because they are the most common methods and allow a wide range of data processing with a dynamic array. It may seem that the ArrayList, with all its methods and dynamic resizing, is so superior to ...
h + 1
... – Too big will waste memory; too small will increase collisions and may eventually force rehashing (copying into a larger table) – Should be appropriate for the hash function used – and a prime number is best ...
... – Too big will waste memory; too small will increase collisions and may eventually force rehashing (copying into a larger table) – Should be appropriate for the hash function used – and a prime number is best ...
Text11-Arrays - Vernon Computer Science
... are practical for loop counter variables, maximum number of grades, the height of Pikes Peak and the number of medals won by the United States at the last Olympics. Programs that handle passenger airline reservations, student college transcripts, employee payroll records and hospital patient informa ...
... are practical for loop counter variables, maximum number of grades, the height of Pikes Peak and the number of medals won by the United States at the last Olympics. Programs that handle passenger airline reservations, student college transcripts, employee payroll records and hospital patient informa ...
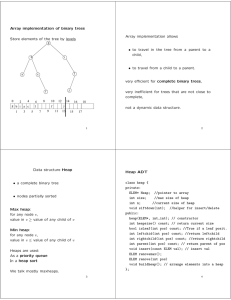
3 Representing Sequences by Arrays and Linked Lists
... of the sequence, the successor of h1 stores the second element of the sequence, and so on. The predecessor of h stores the last element of the sequence; see Fig. 3.2. The empty sequence is represented by a ring consisting only of h. Since there are no elements in that sequence, h is its own successo ...
... of the sequence, the successor of h1 stores the second element of the sequence, and so on. The predecessor of h stores the last element of the sequence; see Fig. 3.2. The empty sequence is represented by a ring consisting only of h. Since there are no elements in that sequence, h is its own successo ...
Functional Programming in JavaScript
... data; hence, the name of the original functional language, LISP (list processing), from which JavaScript is derived. JavaScript 5.1 provides native versions of these operations known as the functional array extras; but in order to create complete solutions that may involve other similar types of ope ...
... data; hence, the name of the original functional language, LISP (list processing), from which JavaScript is derived. JavaScript 5.1 provides native versions of these operations known as the functional array extras; but in order to create complete solutions that may involve other similar types of ope ...
Dictionaries and Hash Tables
... hash table take O(n) time The worst case occurs when all the keys inserted into the dictionary collide The load factor a = n/N affects the performance of a hash table Assuming that the hash values are like random numbers, it can be shown that the expected number of probes for an insertion with open ...
... hash table take O(n) time The worst case occurs when all the keys inserted into the dictionary collide The load factor a = n/N affects the performance of a hash table Assuming that the hash values are like random numbers, it can be shown that the expected number of probes for an insertion with open ...
study guide
... Initialising the elements of an array • Arrays of variable size – Some programs, the number of entries in an array can vary – In this case, a sentinel value (for example, 9999) is used to mark the last element of the array, both in the initialising file of data items and in the array itself – Inclu ...
... Initialising the elements of an array • Arrays of variable size – Some programs, the number of entries in an array can vary – In this case, a sentinel value (for example, 9999) is used to mark the last element of the array, both in the initialising file of data items and in the array itself – Inclu ...
Elementary Data Structures and Hash Tables
... All direct-address table operations are O(1)! So why isn’t every set implemented with a direct-address table? The space complexity is Θ(`U`) ...
... All direct-address table operations are O(1)! So why isn’t every set implemented with a direct-address table? The space complexity is Θ(`U`) ...