The State of SAT - Cornell Computer Science
... showed how to determine if there existed a renaming (permutation) ψ of the variables in a formula that resulted in the same set of clauses, which justified a new rule of inference: from any clause (a∨b∨...), infer (ψ(a) ∨ψ(b) ∨...). [58] introduced a different way of using symmetries, by strengtheni ...
... showed how to determine if there existed a renaming (permutation) ψ of the variables in a formula that resulted in the same set of clauses, which justified a new rule of inference: from any clause (a∨b∨...), infer (ψ(a) ∨ψ(b) ∨...). [58] introduced a different way of using symmetries, by strengtheni ...
Arbitrary Announcements in Propositional Belief Revision
... Public announcements cause each agent in a group to modify their beliefs to incorporate some new piece of information, while simultaneously being aware that all other agents are doing the same. Given some fixed goal formula, it is natural to ask if there exists an announcement that will make the for ...
... Public announcements cause each agent in a group to modify their beliefs to incorporate some new piece of information, while simultaneously being aware that all other agents are doing the same. Given some fixed goal formula, it is natural to ask if there exists an announcement that will make the for ...
On the connections between backdoors, restarts, and heavy
... Let aS : S ⊆ V → {T rue, F alse} be a partial truth assignment. We use F [a S ] to denote the simplified SAT instance obtained from the formula F by setting the variables defined in a S , i.e., by fixing the truth values of the variables in a S . A set of backdoor variables is defined with respect t ...
... Let aS : S ⊆ V → {T rue, F alse} be a partial truth assignment. We use F [a S ] to denote the simplified SAT instance obtained from the formula F by setting the variables defined in a S , i.e., by fixing the truth values of the variables in a S . A set of backdoor variables is defined with respect t ...
pdf
... random variables MD and L. This equation says, among other things, that if MD = 0 and L = 1, then FF = 1. Alternatively, if we want to model the fact that a fire requires both a lightning strike and a dropped match (perhaps the wood is so wet that it needs two sources of fire to get going), then the ...
... random variables MD and L. This equation says, among other things, that if MD = 0 and L = 1, then FF = 1. Alternatively, if we want to model the fact that a fire requires both a lightning strike and a dropped match (perhaps the wood is so wet that it needs two sources of fire to get going), then the ...
Ten Challenges Redux: Recent Progress in Propositional
... All nodes on the reason side that have at least one edge going to the conflict side form a cause of the conflict. The negations of the corresponding literals forms the conflict clause associated with this cut: that is, a clause that is implied by the original formula. Figure 1 illustrates different ...
... All nodes on the reason side that have at least one edge going to the conflict side form a cause of the conflict. The negations of the corresponding literals forms the conflict clause associated with this cut: that is, a clause that is implied by the original formula. Figure 1 illustrates different ...
ind and dep variables plus hypothesis
... Independent & dependent variables Observations & Inferences Qualitative & quantitative data ...
... Independent & dependent variables Observations & Inferences Qualitative & quantitative data ...
draft pdf
... the framework borrowed from SampleCount with the use of biased random coins during randomized value selection for variables. The model count can, in fact, also be estimated directly from just one fixed point run of the BP equations, by computing the value of so-called partition function [32]. In par ...
... the framework borrowed from SampleCount with the use of biased random coins during randomized value selection for variables. The model count can, in fact, also be estimated directly from just one fixed point run of the BP equations, by computing the value of so-called partition function [32]. In par ...
Lean Theorem Proving: Maximal Efficiency from Minimal - IT-SEC
... We will briefly describe the tableau-based theorem prover leanTAP listed at the beginning and explain its behavior. We assume familiarity with free-variable tableaux (e.g. [3]) and the basics of programming in Prolog. For the sake of simplicity, we restrict our considerations to first-order formulæ ...
... We will briefly describe the tableau-based theorem prover leanTAP listed at the beginning and explain its behavior. We assume familiarity with free-variable tableaux (e.g. [3]) and the basics of programming in Prolog. For the sake of simplicity, we restrict our considerations to first-order formulæ ...
Lean Theorem Proving: Maximal Efficiency from Minimal Means
... We will briefly describe the tableau-based theorem prover leanTAP listed at the beginning and explain its behavior. We assume familiarity with free-variable tableaux (e.g. [3]) and the basics of programming in Prolog. For the sake of simplicity, we restrict our considerations to first-order formulæ ...
... We will briefly describe the tableau-based theorem prover leanTAP listed at the beginning and explain its behavior. We assume familiarity with free-variable tableaux (e.g. [3]) and the basics of programming in Prolog. For the sake of simplicity, we restrict our considerations to first-order formulæ ...
1 HYBRID EXPERT SYSTEM OF ROUGH SET AND NEURAL
... this paper a new method for pre-processing data for neural network based on rough set has been developed and merged with neural expert system. The process consists of acquisition of data, formalization of decision tables, reduction of attributes, and binarization of input data [7, 15]. First decisio ...
... this paper a new method for pre-processing data for neural network based on rough set has been developed and merged with neural expert system. The process consists of acquisition of data, formalization of decision tables, reduction of attributes, and binarization of input data [7, 15]. First decisio ...
Lecture 15 - Wiki Index
... computing as human-centric intelligent systems. Human-centered information processing was initiated with the introduction of fuzzy sets. Such insights have led to the development of the granular computing paradigm. From machine-centered to human-centered approaches is considered one of the trends in ...
... computing as human-centric intelligent systems. Human-centered information processing was initiated with the introduction of fuzzy sets. Such insights have led to the development of the granular computing paradigm. From machine-centered to human-centered approaches is considered one of the trends in ...
A Closest Fit Approach to Missing Attribute Values in Preterm Birth
... imperfection is inconsistency—the data set may contain conflicting cases (examples), having the same values of all attributes yet belonging to different concepts (classes). Knowledge considered in this paper is expressed in the form of rules, also called production rules. Rules are induced from give ...
... imperfection is inconsistency—the data set may contain conflicting cases (examples), having the same values of all attributes yet belonging to different concepts (classes). Knowledge considered in this paper is expressed in the form of rules, also called production rules. Rules are induced from give ...
View Sample PDF
... A partitioning method creates an initial set of k partitions, where the parameter k is the number of partitions to be constructed. Then it uses an iterative relocation technique that attempts to improve the partitioning by moving objects from one group to another. Typical partitioning methods includ ...
... A partitioning method creates an initial set of k partitions, where the parameter k is the number of partitions to be constructed. Then it uses an iterative relocation technique that attempts to improve the partitioning by moving objects from one group to another. Typical partitioning methods includ ...
Fixed-Point Logics and Computation
... Includes definitions of syntax and semantics of most languages, of data structures (trees, lists, etc.), of arithmetic functions. ...
... Includes definitions of syntax and semantics of most languages, of data structures (trees, lists, etc.), of arithmetic functions. ...
degrees radians 36 radians radians radians π ⋅ = 180° π ° ⋅ = 180
... the terminal side of this angle lies in quadrant I. B. Incorrect! Use the fact that both coordinates of the point on the terminal side are positive to find that the quadrant the terminal side lies in. C. Incorrect! Use the fact that both coordinates of the point on the terminal side are positive to ...
... the terminal side of this angle lies in quadrant I. B. Incorrect! Use the fact that both coordinates of the point on the terminal side are positive to find that the quadrant the terminal side lies in. C. Incorrect! Use the fact that both coordinates of the point on the terminal side are positive to ...
Chapter 7
... • In order to indicate the general distribution of electrons among the bonded atoms in a molecular compound or a polyatomic ion, oxidation numbers are assigned to the atoms composing the compound or ion. • Unlike ionic charges, oxidation numbers do not have an exact physical meaning: rather, they se ...
... • In order to indicate the general distribution of electrons among the bonded atoms in a molecular compound or a polyatomic ion, oxidation numbers are assigned to the atoms composing the compound or ion. • Unlike ionic charges, oxidation numbers do not have an exact physical meaning: rather, they se ...
Independence in Relational Languages with Finite Domains
... 2. Probabilistic Logic and PPL Networks The combination of logic and probabilities has been extensively studied in the last decades. This promising mixture has old roots and has been rediscovered a few times. Nilsson’s probabilistic logic [Nilsson 1986] has been a significant influence, as well as ...
... 2. Probabilistic Logic and PPL Networks The combination of logic and probabilities has been extensively studied in the last decades. This promising mixture has old roots and has been rediscovered a few times. Nilsson’s probabilistic logic [Nilsson 1986] has been a significant influence, as well as ...
On Correctness of Mathematical Texts from a Logical and Practical
... presented below, share a lot of similar traits owed to the common striving for a natural-like formal mathematical language. Finally, there are systems that do not use user-given proofs and rely instead on proof generation methods: planning, rewriting, or inference search facilities to deduce each cl ...
... presented below, share a lot of similar traits owed to the common striving for a natural-like formal mathematical language. Finally, there are systems that do not use user-given proofs and rely instead on proof generation methods: planning, rewriting, or inference search facilities to deduce each cl ...
week 14 Datamining print PPT95
... This illustrates the approach: rather than directly relating documents and terms as in vector retrieval, there exists a middle layer into which both queries and documents map. The space of concepts can be of smaller dimension. For example, we could determine that the query t3 returns d2, d3, d4 in t ...
... This illustrates the approach: rather than directly relating documents and terms as in vector retrieval, there exists a middle layer into which both queries and documents map. The space of concepts can be of smaller dimension. For example, we could determine that the query t3 returns d2, d3, d4 in t ...
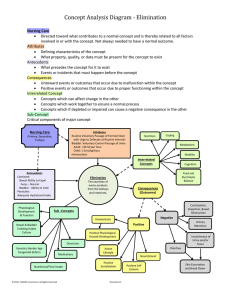
Concept Analysis Diagram
... Sub-Concepts are teaching points regarding the Concept being defined thus just a line is printed between the Concept and Sub-Concepts. The need for Nursing Care is triggered by: Compromised Antecedent(s), Decreased quality of Attribute(s), Negative Consequence(s), and/or a potentially negative impac ...
... Sub-Concepts are teaching points regarding the Concept being defined thus just a line is printed between the Concept and Sub-Concepts. The need for Nursing Care is triggered by: Compromised Antecedent(s), Decreased quality of Attribute(s), Negative Consequence(s), and/or a potentially negative impac ...
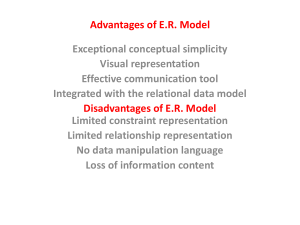
محاضرة جبر العلاقات
... • Weak entity set. The primary key of the relation consists of the union of the primary key of the strong entity set and the discriminator of the weak entity set. • Relationship set. The union of the primary keys of the related entity sets becomes a super key of the relation. – For binary many-to-on ...
... • Weak entity set. The primary key of the relation consists of the union of the primary key of the strong entity set and the discriminator of the weak entity set. • Relationship set. The union of the primary keys of the related entity sets becomes a super key of the relation. – For binary many-to-on ...
Introduction to logistic regression
... y (number of partners) = α + β1 age + β2 income + β3 gender ...
... y (number of partners) = α + β1 age + β2 income + β3 gender ...
Temporal Logic Theorem Proving and its Application to the Feature
... In the CFBL property, note the use of ∃, even though the definition of LTL so far doesn’t include quantifiers. Quantifiers can be added directly to LTL [15], but it was important for our model checking approach to leave them out. The use of ∃ here can be viewed as an abbreviation. When we are checki ...
... In the CFBL property, note the use of ∃, even though the definition of LTL so far doesn’t include quantifiers. Quantifiers can be added directly to LTL [15], but it was important for our model checking approach to leave them out. The use of ∃ here can be viewed as an abbreviation. When we are checki ...
MAI0203 Lecture 7: Inference and Predicate Calculus
... interpretation of und holds that is valid iff is ...
... interpretation of und holds that is valid iff is ...
ORDINAL REGRESSION. 1. Motivation. Many variables of interest
... dependent variable given one or more independent variables. For example we could use ordinal logistic regression to predict the belief that “people who study Statistics are weird”, this is the ordinal dependent variable measure on the 5-point Likert scale given above, based on some independent varia ...
... dependent variable given one or more independent variables. For example we could use ordinal logistic regression to predict the belief that “people who study Statistics are weird”, this is the ordinal dependent variable measure on the 5-point Likert scale given above, based on some independent varia ...
Granular computing

Granular computing (GrC) is an emerging computing paradigm of information processing. It concerns the processing of complex information entities called information granules, which arise in the process of data abstraction and derivation of knowledge from information or data. Generally speaking, information granules are collections of entities that usually originate at the numeric level and are arranged together due to their similarity, functional or physical adjacency, indistinguishability, coherency, or the like.At present, granular computing is more a theoretical perspective than a coherent set of methods or principles. As a theoretical perspective, it encourages an approach to data that recognizes and exploits the knowledge present in data at various levels of resolution or scales. In this sense, it encompasses all methods which provide flexibility and adaptability in the resolution at which knowledge or information is extracted and represented.