Toward Conversational Human
... fact, most information can be extracted by simple patterns designed for the specific domain. For example, given the utterance “When does the Niagara Bullet leave Rochester?” patternmatching techniques could identify values for the following parameters: the train (answer: The Niagara Bullet), the eve ...
... fact, most information can be extracted by simple patterns designed for the specific domain. For example, given the utterance “When does the Niagara Bullet leave Rochester?” patternmatching techniques could identify values for the following parameters: the train (answer: The Niagara Bullet), the eve ...
Adding Local Exploration to Greedy Best-First Search in
... GBFS-LS and GBFS-LRW with hFF for first reaching a given hmin in 2004-notankage #21. in search time, with the largest (763 seconds) for the step from hmin = 2 to hmin = 1, correspond to times when the search is stalled in multiple UHRs. Since the large majority of overall search time is used to inef ...
... GBFS-LS and GBFS-LRW with hFF for first reaching a given hmin in 2004-notankage #21. in search time, with the largest (763 seconds) for the step from hmin = 2 to hmin = 1, correspond to times when the search is stalled in multiple UHRs. Since the large majority of overall search time is used to inef ...
Managing the Digital Firm - Department of Computer Engineering
... In forward chaining, the system begins with known facts about the problem and goes through the rules in the knowledge base trying to assert new facts. Rules whose left-hand side (IF part or premise) is known to be true are fired, meaning their right-hand side (THEN part, or conclusion) is declared t ...
... In forward chaining, the system begins with known facts about the problem and goes through the rules in the knowledge base trying to assert new facts. Rules whose left-hand side (IF part or premise) is known to be true are fired, meaning their right-hand side (THEN part, or conclusion) is declared t ...
Managing the Digital Firm
... In forward chaining, the system begins with known facts about the problem and goes through the rules in the knowledge base trying to assert new facts. Rules whose left-hand side (IF part or premise) is known to be true are fired, meaning their right-hand side (THEN part, or conclusion) is declared t ...
... In forward chaining, the system begins with known facts about the problem and goes through the rules in the knowledge base trying to assert new facts. Rules whose left-hand side (IF part or premise) is known to be true are fired, meaning their right-hand side (THEN part, or conclusion) is declared t ...
Chapter 12 - Missouri State University
... behaviors in large data sets, using techniques such as neural networks and data mining Artificial Intelligence (AI) technology: • Computer-based systems based on human behavior, with the ability to learn languages, accomplish physical tasks, use a perceptual apparatus, and emulate human expertise an ...
... behaviors in large data sets, using techniques such as neural networks and data mining Artificial Intelligence (AI) technology: • Computer-based systems based on human behavior, with the ability to learn languages, accomplish physical tasks, use a perceptual apparatus, and emulate human expertise an ...
Policy Communication for Coordination with Unknown Teammates
... Across many communicative multiagent frameworks, such as the COM-MTDP model (Pynadath and Tambe 2002) and STEAM (Tambe 1997), communicative actions are often limited to sharing observations or direct state information (Roth, Simmons, and Veloso 2007). As agents in such systems have complete informat ...
... Across many communicative multiagent frameworks, such as the COM-MTDP model (Pynadath and Tambe 2002) and STEAM (Tambe 1997), communicative actions are often limited to sharing observations or direct state information (Roth, Simmons, and Veloso 2007). As agents in such systems have complete informat ...
OpenProblems-2011-01-25
... (..) Obtained results facilitate building a common framework for information and computation. Now category theory is also used as unifying framework for physics, biology, topology, and logic, as well as for the whole mathematics. This provides a base for analyzing physical and information systems an ...
... (..) Obtained results facilitate building a common framework for information and computation. Now category theory is also used as unifying framework for physics, biology, topology, and logic, as well as for the whole mathematics. This provides a base for analyzing physical and information systems an ...
A Design of Criminal Investigation Expert System Based on CILS
... criminal investigation expert systems (CIESs) have been made an important point. However, conventional environment of information conduction is “man around computer”, which is difficult to deal with the information featured by procedures of brain thinking. Because of the almighty ability of computer ...
... criminal investigation expert systems (CIESs) have been made an important point. However, conventional environment of information conduction is “man around computer”, which is difficult to deal with the information featured by procedures of brain thinking. Because of the almighty ability of computer ...
Probabilistic Approaches in Search AAAI Press
... refusal to any publication (including electronic distribution) arising from this AAAI event. Please do not make any inquiries or arrangements for hardcopy or electronic publication of all or part of the papers contained in these working notes without first exploring the options available through AAA ...
... refusal to any publication (including electronic distribution) arising from this AAAI event. Please do not make any inquiries or arrangements for hardcopy or electronic publication of all or part of the papers contained in these working notes without first exploring the options available through AAA ...
OpenProblems-2011-02
... informal aspect be integrated when postulating an underlying common nature parts of which are formalizable while other parts are not (similar to Ludwig von Bertalanffy’s idea concerning the use of mathematical tools in his General System Theory [see Hofkirchner and Schafranek 2011])? Can the syntact ...
... informal aspect be integrated when postulating an underlying common nature parts of which are formalizable while other parts are not (similar to Ludwig von Bertalanffy’s idea concerning the use of mathematical tools in his General System Theory [see Hofkirchner and Schafranek 2011])? Can the syntact ...
OpenProblems-2011-01-28
... communication is an interaction between a system and its environment. Burgin [2005] puts it in the following way: “It is necessary to remark that there is an ongoing synthesis of computation and communication into a unified process of information processing. Practical and theoretical advances are ai ...
... communication is an interaction between a system and its environment. Burgin [2005] puts it in the following way: “It is necessary to remark that there is an ongoing synthesis of computation and communication into a unified process of information processing. Practical and theoretical advances are ai ...
Management Information Systems Chapter 12
... behaviors in large data sets, using techniques such as neural networks and data mining Artificial Intelligence (AI) technology: • Computer-based systems based on human behavior, with the ability to learn languages, accomplish physical tasks, use a perceptual apparatus, and emulate human expertise an ...
... behaviors in large data sets, using techniques such as neural networks and data mining Artificial Intelligence (AI) technology: • Computer-based systems based on human behavior, with the ability to learn languages, accomplish physical tasks, use a perceptual apparatus, and emulate human expertise an ...
Design of Collaborative Information Agents
... designed system actually will show the required behaviour. In verification formalised behavioural requirements and a formalised conceptual design play a main role. Also for verification proofs reusable patterns can be specified. The methodological approach discussed in this paper assumes two specifi ...
... designed system actually will show the required behaviour. In verification formalised behavioural requirements and a formalised conceptual design play a main role. Also for verification proofs reusable patterns can be specified. The methodological approach discussed in this paper assumes two specifi ...
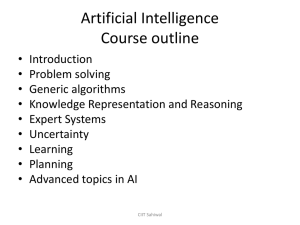
Artificial Intelligence
... each assignment, including the contribution of each member. All submitted assignments will have to be accompanied by a short documentation as well. There can be at most 3 members in a group. ...
... each assignment, including the contribution of each member. All submitted assignments will have to be accompanied by a short documentation as well. There can be at most 3 members in a group. ...
Answering Subcognitive Turing Test Questions: A
... from its ability to exploit a huge collection of text. In the following examples, I used the AltaVista® search engine, which indexes about 350 million Web pages in English.1 PMI-IR was designed to recognize synonyms. The task of synonym recognition is, given a problem word and a set of alternative w ...
... from its ability to exploit a huge collection of text. In the following examples, I used the AltaVista® search engine, which indexes about 350 million Web pages in English.1 PMI-IR was designed to recognize synonyms. The task of synonym recognition is, given a problem word and a set of alternative w ...
Answering Subcognitive Turing Test Questions: A Reply
... from its ability to exploit a huge collection of text. In the following examples, I used the AltaVista® search engine, which indexes about 350 million Web pages in English.1 PMI-IR was designed to recognize synonyms. The task of synonym recognition is, given a problem word and a set of alternative w ...
... from its ability to exploit a huge collection of text. In the following examples, I used the AltaVista® search engine, which indexes about 350 million Web pages in English.1 PMI-IR was designed to recognize synonyms. The task of synonym recognition is, given a problem word and a set of alternative w ...
Week10-BUAD283-Chp04
... emphasizes sharing and flow of information A type of decision support system that facilitates the formulation of and solution to problems by a team A GDSS helps a team to generate ideas, identify strengths and weaknesses, choose an alternative, and reach a consensus ...
... emphasizes sharing and flow of information A type of decision support system that facilitates the formulation of and solution to problems by a team A GDSS helps a team to generate ideas, identify strengths and weaknesses, choose an alternative, and reach a consensus ...
Automatic Extraction of Efficient Axiom Sets from Large Knowledge
... We assume that the set of LearnablePredicates can be constructed by examining the structure of the system that is producing facts. We include all predicates produced by learning systems in LearnablePredicates because estimates of the distribution of statements produced may not be known in advance. W ...
... We assume that the set of LearnablePredicates can be constructed by examining the structure of the system that is producing facts. We include all predicates produced by learning systems in LearnablePredicates because estimates of the distribution of statements produced may not be known in advance. W ...
Facilitating Information Sharing Across the International Space
... independent ability to launch unmanned orbital missions. Many more have also built what are known as hosted payloads for launch via partnerships with other countries. Hosted payloads use excess capacity on spacecraft or rockets that are already scheduled for launch. In addition, private companies, s ...
... independent ability to launch unmanned orbital missions. Many more have also built what are known as hosted payloads for launch via partnerships with other countries. Hosted payloads use excess capacity on spacecraft or rockets that are already scheduled for launch. In addition, private companies, s ...
Searching Social Networks
... Finding relevant information is a longstanding problem in computing. Conventional approaches such as databases, information retrieval systems, and Web search engines partially address this problem. Often, however, the most valuable information is not widely available and may not even be indexed or c ...
... Finding relevant information is a longstanding problem in computing. Conventional approaches such as databases, information retrieval systems, and Web search engines partially address this problem. Often, however, the most valuable information is not widely available and may not even be indexed or c ...
Collaborative Practice
... practice thus both optimises and improves professional actions. There are thus two interlinked dimensions to professional work. Over the last 20 years, the reflective practitioner concept has been extended, embellished and critiqued (see for example Killion and Todnem (1991), Van Manen (1991), Moon ...
... practice thus both optimises and improves professional actions. There are thus two interlinked dimensions to professional work. Over the last 20 years, the reflective practitioner concept has been extended, embellished and critiqued (see for example Killion and Todnem (1991), Van Manen (1991), Moon ...
Lecture II -- Problem Solving and Search
... Time complexity: number of nodes generated/expanded Space complexity: number of nodes holds in memory Optimality: does it always find a least-cost solution? ...
... Time complexity: number of nodes generated/expanded Space complexity: number of nodes holds in memory Optimality: does it always find a least-cost solution? ...
Lecture II -- Problem Solving and Search
... Time complexity: number of nodes generated/expanded Space complexity: number of nodes holds in memory Optimality: does it always find a least-cost solution? ...
... Time complexity: number of nodes generated/expanded Space complexity: number of nodes holds in memory Optimality: does it always find a least-cost solution? ...
Artificial Intelligence Problem Solving and Search
... • Operator: description of an action • State space: all states reachable from the initial state by any sequence action • Path: sequence of actions leading from one state to another • Goal test: which the agent can apply to a single state description to determine if it is a goal state • Path cost fun ...
... • Operator: description of an action • State space: all states reachable from the initial state by any sequence action • Path: sequence of actions leading from one state to another • Goal test: which the agent can apply to a single state description to determine if it is a goal state • Path cost fun ...