Chapter 4: Lazy Classification using P
... whether a particular split should be done at all. In our algorithm, significance is calculated on different data than information gain to get a statistically sound estimate. The training set is split into two parts, with two-thirds of the data being used to determine information gain and one-third t ...
... whether a particular split should be done at all. In our algorithm, significance is calculated on different data than information gain to get a statistically sound estimate. The training set is split into two parts, with two-thirds of the data being used to determine information gain and one-third t ...
Big Data Analysis and Its Applications for Knowledge
... Modern data-mining applications, often tool to extend human knowledge. called “big-data” analysis, require us to manage 2. Challenges to the analysis of massive data A number of challenges exist in both data immense amounts of data quickly. In many of these applications, the data is extremely regula ...
... Modern data-mining applications, often tool to extend human knowledge. called “big-data” analysis, require us to manage 2. Challenges to the analysis of massive data A number of challenges exist in both data immense amounts of data quickly. In many of these applications, the data is extremely regula ...
From Cognitive Science to Data Mining: The first intelligence amplifier
... miner works, not in the realm of bits, bytes and algorithms, but in the domain of enquiry. The data mining process enables the data miner to see things which would not be visible unaided. We know that perception is an active, knowledgebased process. The data miner sees things in the business domain ...
... miner works, not in the realm of bits, bytes and algorithms, but in the domain of enquiry. The data mining process enables the data miner to see things which would not be visible unaided. We know that perception is an active, knowledgebased process. The data miner sees things in the business domain ...
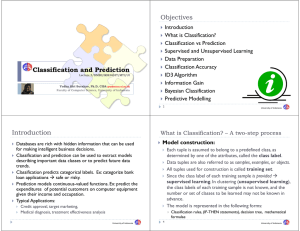
Classification and Prediction
... Accuracy rate is the percentage of test set samples that are correctly classified by the model. Test set is independent of training set otherwise over-fitting (it may have incorporated some particular anomalies of the training data that are not present in the overall sample population) will occur. ...
... Accuracy rate is the percentage of test set samples that are correctly classified by the model. Test set is independent of training set otherwise over-fitting (it may have incorporated some particular anomalies of the training data that are not present in the overall sample population) will occur. ...
Challenges Of Big Data In Scientific Discovery Outline
... – Monte Carol simulations – Understanding polls – Focus on probabilities ...
... – Monte Carol simulations – Understanding polls – Focus on probabilities ...
Application of Machine learning Algorithms in Crime Classification
... especially activities by the terrorists and Mafia activities and insurgent have attained significant level that need to be undertook with better proficient expertise and efficiency which requires co-ordination among different agencies in sharing criminal intelligence6. For this purpose, an Organized ...
... especially activities by the terrorists and Mafia activities and insurgent have attained significant level that need to be undertook with better proficient expertise and efficiency which requires co-ordination among different agencies in sharing criminal intelligence6. For this purpose, an Organized ...
Syllabus ECOM 6349 Selected Topics in Artificial Intelligence
... Graph Based Clustering Algorithms, Grid Based Clustering Algorithms, Density Based Clustering Algorithms, Model Based Clustering Algorithms, Evaluation of Clustering Algorithms. ...
... Graph Based Clustering Algorithms, Grid Based Clustering Algorithms, Density Based Clustering Algorithms, Model Based Clustering Algorithms, Evaluation of Clustering Algorithms. ...
Data Warehouses and Data Mining
... – Support is the percentage of times such a sequence occurs in the set of transactions – Confidence is the probability that when {S1} occurs, {S2} will occur on a subsequent transaction - can calculate from observed data ...
... – Support is the percentage of times such a sequence occurs in the set of transactions – Confidence is the probability that when {S1} occurs, {S2} will occur on a subsequent transaction - can calculate from observed data ...
Attribute Selection in Software Engineering Datasets for Detecting
... than a user-specified threshold value, or we can simply select the first k features from the ranked list. This approach is efficient for high-dimensional data due to its linear time complexity in terms of dimensionality. Some existing evaluation measures that have been shown effective in removing bo ...
... than a user-specified threshold value, or we can simply select the first k features from the ranked list. This approach is efficient for high-dimensional data due to its linear time complexity in terms of dimensionality. Some existing evaluation measures that have been shown effective in removing bo ...
Data Mining and Decision Support
... eld of medical decision making.3 The gure indicates that current DSS need to deal also with large volumes of data, as well as data gathering and analysis via the Internet and intranet. The main source of knowledge for DM is data from which knowledge is extracted. On the other hand, in DS the main ...
... eld of medical decision making.3 The gure indicates that current DSS need to deal also with large volumes of data, as well as data gathering and analysis via the Internet and intranet. The main source of knowledge for DM is data from which knowledge is extracted. On the other hand, in DS the main ...
Data Transformation and Reduction
... ◦ Best step-wise feature selection: ◦ The best single-attribute is picked first ◦ Then next best attribute condition to the first, ... ...
... ◦ Best step-wise feature selection: ◦ The best single-attribute is picked first ◦ Then next best attribute condition to the first, ... ...
Databases Illuminated
... – Support is the percentage of times such a sequence occurs in the set of transactions – Confidence is the probability that when {S1} occurs, {S2} will occur on a subsequent transaction - can calculate from observed data ...
... – Support is the percentage of times such a sequence occurs in the set of transactions – Confidence is the probability that when {S1} occurs, {S2} will occur on a subsequent transaction - can calculate from observed data ...
database
... Database Models: What are the different types of database models? How do they differ? (pg 416-424) Data Mining: What is data mining? Why is it important? What are the steps involved in the data-mining process? Give examples of data mining applications. (pg 424-427) E-Business & E-Commerce: What are ...
... Database Models: What are the different types of database models? How do they differ? (pg 416-424) Data Mining: What is data mining? Why is it important? What are the steps involved in the data-mining process? Give examples of data mining applications. (pg 424-427) E-Business & E-Commerce: What are ...
Ch07_final
... Involves strategies and processes of identifying, creating, capturing, organizing, transferring, and leveraging knowledge to help compete ...
... Involves strategies and processes of identifying, creating, capturing, organizing, transferring, and leveraging knowledge to help compete ...
advances in knowledge discovery in databases
... prediction. This is similar with what people do: just from seeing a few examples people can learn to interpolate between the examples given in order to generalize to new problems or cases that were not encountered. In fact the ability of generalize is one of the strongest points in using the neural ...
... prediction. This is similar with what people do: just from seeing a few examples people can learn to interpolate between the examples given in order to generalize to new problems or cases that were not encountered. In fact the ability of generalize is one of the strongest points in using the neural ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... Oracle Data mining Module(ODM) to identify the main attacks occurring on a particular protocol. Interesting patterns suggesting the vulnerability of the TCP/IP protocol towards attacks emerged in their study. Detection of anomalies and outliers in data is another interesting study. However there are ...
... Oracle Data mining Module(ODM) to identify the main attacks occurring on a particular protocol. Interesting patterns suggesting the vulnerability of the TCP/IP protocol towards attacks emerged in their study. Detection of anomalies and outliers in data is another interesting study. However there are ...
Integrating Artificial Intelligence into Data Warehousing and Data
... economists - which depends on the application of information technologies. Integrating data and extracting knowledge from the market environment is always complex; in fact, this requires sufficient modeling techniques. [5, p. 5] maintain that the world “is data rich and information poor”, due to the ...
... economists - which depends on the application of information technologies. Integrating data and extracting knowledge from the market environment is always complex; in fact, this requires sufficient modeling techniques. [5, p. 5] maintain that the world “is data rich and information poor”, due to the ...
Decision Support System for Heart Disease Prediction using Data
... characterized gatherings, sacking calculation and help vector machine demonstrating diverse levels of correctness’s on numerous databases of patients from around the globe[7]. One of the bases on which the papers differ are the determination of parameters on which the methods have been used. Various ...
... characterized gatherings, sacking calculation and help vector machine demonstrating diverse levels of correctness’s on numerous databases of patients from around the globe[7]. One of the bases on which the papers differ are the determination of parameters on which the methods have been used. Various ...
(IT) has also generated a ... world is drowning in a ...
... development of novel data mining (DM) or knowledge discovery in databases (KDD) and data understanding (DU) technologies, hyperdimensional visialization, etc. The use of AI/machine-assisted discovery may become a standard scientific practice. This is where the qualitative differences in the way scie ...
... development of novel data mining (DM) or knowledge discovery in databases (KDD) and data understanding (DU) technologies, hyperdimensional visialization, etc. The use of AI/machine-assisted discovery may become a standard scientific practice. This is where the qualitative differences in the way scie ...
Slide - Purdue University
... • A data warehouse may store terabytes of data – Complex data analysis/mining may take a very long time to run on the complete data set ...
... • A data warehouse may store terabytes of data – Complex data analysis/mining may take a very long time to run on the complete data set ...
Learning Models of Plant Behavior for Anomaly Detection and
... and analysis techniques in a flexible, extensible way. Agents have previously been used for power engineering applications such as feeder automation [1], substation automation [2], and microgrid control [3]. Previous work resulted in the COndition Monitoring MultiAgent System (COMMAS) [4], a system ...
... and analysis techniques in a flexible, extensible way. Agents have previously been used for power engineering applications such as feeder automation [1], substation automation [2], and microgrid control [3]. Previous work resulted in the COndition Monitoring MultiAgent System (COMMAS) [4], a system ...
Interactive Linguistics and Distributed Grammar
... regression etc.) 2. Structure of the Model adapted to data (it determines the limits of what will be compared or revealed) 3. Evaluation function (adequacy / correspondence and generalization problems) 4. Search or Optimalization Methods (heart of data exploration algorithms) 5. Data Management Tech ...
... regression etc.) 2. Structure of the Model adapted to data (it determines the limits of what will be compared or revealed) 3. Evaluation function (adequacy / correspondence and generalization problems) 4. Search or Optimalization Methods (heart of data exploration algorithms) 5. Data Management Tech ...
ADVANCES IN KNOWLEDGE DISCOVERY IN
... distributed systems is still opened. • The continuous improvement of additional steps from the KDD process. A very important matter here is that in the real world analysed data is not pre-processed. Most of the time it is incomplete or incorrect. So the data ...
... distributed systems is still opened. • The continuous improvement of additional steps from the KDD process. A very important matter here is that in the real world analysed data is not pre-processed. Most of the time it is incomplete or incorrect. So the data ...
The AI Revolution in Insurance
... with the perfection of machine intelligence. We are being replaced, resistance is futile, and insurance is next! Just look at the writing on the wall. “Your next insurance agent will be a robot,” confidently reports c/ net.1 “How Artificial Intelligence Will Eliminate the Need for the Vast Majority ...
... with the perfection of machine intelligence. We are being replaced, resistance is futile, and insurance is next! Just look at the writing on the wall. “Your next insurance agent will be a robot,” confidently reports c/ net.1 “How Artificial Intelligence Will Eliminate the Need for the Vast Majority ...
Business Intelligence and Decision Support Systems
... Simulation generally refers to a technique for conducting experiments (such as "what-if") with a computer on a model of a management system. Because DSS deals with semi structured or unstructured situations, it involves complex reality, which may not be easily represented by optimization or other st ...
... Simulation generally refers to a technique for conducting experiments (such as "what-if") with a computer on a model of a management system. Because DSS deals with semi structured or unstructured situations, it involves complex reality, which may not be easily represented by optimization or other st ...