Isolating Operating System Components with Intel SGX
... are shielded from all other software running on the system including privileged software such as the operating system or the hypervisor. The Intel Skylake processor, released in October 2015, allows the creation and execution of SGX enclaves via its extended instruction set. Various researchers alre ...
... are shielded from all other software running on the system including privileged software such as the operating system or the hypervisor. The Intel Skylake processor, released in October 2015, allows the creation and execution of SGX enclaves via its extended instruction set. Various researchers alre ...
The Kernel Real Time Operating Systems and Middleware
... Real-Time Operating Systems • Real-Time operating system (RTOS): OS providing support to Real-Time applications • Real-Time application: the correctness depends not only on the output values, but also on the time when such values are produced • Operating System: • Set of computer programs • Interfa ...
... Real-Time Operating Systems • Real-Time operating system (RTOS): OS providing support to Real-Time applications • Real-Time application: the correctness depends not only on the output values, but also on the time when such values are produced • Operating System: • Set of computer programs • Interfa ...
... This includes long-term storage, the central processing unit (CPU), short-term memory and the input and output devices. When an application needs one of these resources, the kernel makes the resource available and completes the request. This handling of resources allows the operating systems to be b ...
Embedded Linux Design and Programming
... Kernel Modules System Call – Explicit request to the kernel made through a software interrupt. Service provided in the kernel, cross the user-space / kernel ...
... Kernel Modules System Call – Explicit request to the kernel made through a software interrupt. Service provided in the kernel, cross the user-space / kernel ...
PowerPoint Format
... – Whenever two allocated partner regions are both freed up they are combined to form a larger region. – If a small memory request cannot be satisfied by allocating an existing small free region, then a larger free region will be subdivided into two partners to satisfy the request. Memory allocations ...
... – Whenever two allocated partner regions are both freed up they are combined to form a larger region. – If a small memory request cannot be satisfied by allocating an existing small free region, then a larger free region will be subdivided into two partners to satisfy the request. Memory allocations ...
No Slide Title
... Whenever two allocated partner regions are both freed up they are combined to form a larger region. If a small memory request cannot be satisfied by allocating an existing small free region, then a larger free region will be subdivided into two partners to satisfy the request. ...
... Whenever two allocated partner regions are both freed up they are combined to form a larger region. If a small memory request cannot be satisfied by allocating an existing small free region, then a larger free region will be subdivided into two partners to satisfy the request. ...
A user-mode port of the Linux kernel
... run the host's unmodi ed user space. If processes are going to run exactly the same way in a virtual machine as in the host, then their system calls need to be intercepted and executed in the virtual kernel. This is because those processes are going to trap directly into the host kernel, rather than ...
... run the host's unmodi ed user space. If processes are going to run exactly the same way in a virtual machine as in the host, then their system calls need to be intercepted and executed in the virtual kernel. This is because those processes are going to trap directly into the host kernel, rather than ...
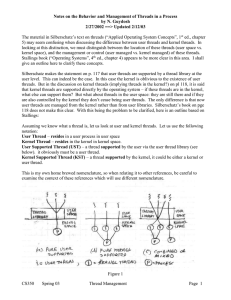
Notes by Guydosh on Thread managment
... 5) may seem confusing when discussing the difference between user threads and kernel threads. In looking at this distinction, we must distinguish between the location of these threads (user space vs. kernel space), and the management or control (user managed vs. kernel managed) of these threads. Sta ...
... 5) may seem confusing when discussing the difference between user threads and kernel threads. In looking at this distinction, we must distinguish between the location of these threads (user space vs. kernel space), and the management or control (user managed vs. kernel managed) of these threads. Sta ...
Multiuser Systems
... Each computer system includes a basic set of programs called the operating system. The most important program in the set is called the kernel. It is loaded into RAM when the system boots and contains many critical procedures that are needed for the system to operate. The other programs are less cruc ...
... Each computer system includes a basic set of programs called the operating system. The most important program in the set is called the kernel. It is loaded into RAM when the system boots and contains many critical procedures that are needed for the system to operate. The other programs are less cruc ...
No Slide Title
... need_resched flag is set so that the scheduler will run once the system call has completed and control is about to be returned to user mode. 2. The second technique applies to critical sections that occur in an interrupt service routines. – By using the processor’s interrupt control hardware to disa ...
... need_resched flag is set so that the scheduler will run once the system call has completed and control is about to be returned to user mode. 2. The second technique applies to critical sections that occur in an interrupt service routines. – By using the processor’s interrupt control hardware to disa ...
Osprey: Operating System for Predictable Clouds
... that controls resource consumption by the application. We distinguish between two types of resources: preemptive and non-preemptive. Preemptive resources, such as CPU time or network interface bandwidth, can be freely given to the application and taken back by the kernel when needed. Resource contai ...
... that controls resource consumption by the application. We distinguish between two types of resources: preemptive and non-preemptive. Preemptive resources, such as CPU time or network interface bandwidth, can be freely given to the application and taken back by the kernel when needed. Resource contai ...
Project 2, Linux Kernel Hacking
... • _syscalln is “deprecated” • I.e., Linux/Unix speak for “don’t use this any more!” • It is officially on the way out (even if it still works) ...
... • _syscalln is “deprecated” • I.e., Linux/Unix speak for “don’t use this any more!” • It is officially on the way out (even if it still works) ...
Operating Systems Concepts Resource Abstraction
... • How does the hardware know where the kernel is or how to load that kernel? – Use a bootstrap program or loader – Execution starts at a predefined memory location in ROM (read-only memory) – Read a single block at a fixed location on disk and execute the code from that boot block – Easily change op ...
... • How does the hardware know where the kernel is or how to load that kernel? – Use a bootstrap program or loader – Execution starts at a predefined memory location in ROM (read-only memory) – Read a single block at a fixed location on disk and execute the code from that boot block – Easily change op ...
Lecture 15 - Department of Math and Computer Science
... Personality. Not traditionally found on UNIX systems, but under Linux each process has an associated personality identifier that can slightly modify the semantics of certain system calls z Used primaril ...
... Personality. Not traditionally found on UNIX systems, but under Linux each process has an associated personality identifier that can slightly modify the semantics of certain system calls z Used primaril ...
Project 1, Linux Kernel Hacking
... • System call numbers different for various architectures • Even for same operating system & version! • E.g., poll system call is #167 on PowerPC but #168 on Intel 386 platforms (in SUSE Linux 9.3) CS-502 Fall 2007 ...
... • System call numbers different for various architectures • Even for same operating system & version! • E.g., poll system call is #167 on PowerPC but #168 on Intel 386 platforms (in SUSE Linux 9.3) CS-502 Fall 2007 ...
Using Linux Kernel Modules For Operating Systems Class Projects
... competency with C and Unix and to establish basic concepts which would be used in later projects. Four projects involving Linux kernel modules were used. The first project is to develop a simple shell using the fork() and execv() system calls to learn about process creation. This is Lab 2.1 as desc ...
... competency with C and Unix and to establish basic concepts which would be used in later projects. Four projects involving Linux kernel modules were used. The first project is to develop a simple shell using the fork() and execv() system calls to learn about process creation. This is Lab 2.1 as desc ...
Operating System Kernels - Freie Universität Berlin
... Since the 2.6.23 kernel Linux uses a Completely Fair Scheduler (CFS) [2], [3]. On real hardware only one single task can run at once. Most fair would be running each process with 1/n of the processors physical power. So while one task runs, the other tasks that are waiting for the CPU are at a disad ...
... Since the 2.6.23 kernel Linux uses a Completely Fair Scheduler (CFS) [2], [3]. On real hardware only one single task can run at once. Most fair would be running each process with 1/n of the processors physical power. So while one task runs, the other tasks that are waiting for the CPU are at a disad ...
Construction of a Highly Dependable Operating System,
... written in these languages make heavy use of pointers, a rich source of bugs. Our approach is therefore based on the ideas of modularity and fault isolation. To keep faults from spreading we have compartmentalized the system by running all servers and drivers as isolated user-mode processes and redu ...
... written in these languages make heavy use of pointers, a rich source of bugs. Our approach is therefore based on the ideas of modularity and fault isolation. To keep faults from spreading we have compartmentalized the system by running all servers and drivers as isolated user-mode processes and redu ...
Kernel - Duke University
... with access to a private instance of the program’s code and data. • A thread can access any virtual memory in its process, but is contained by the “fence” of the process virtual address space. • Threads run on cores: a thread’s core executes instructions for it. • Sometimes threads idle to wait for ...
... with access to a private instance of the program’s code and data. • A thread can access any virtual memory in its process, but is contained by the “fence” of the process virtual address space. • Threads run on cores: a thread’s core executes instructions for it. • Sometimes threads idle to wait for ...
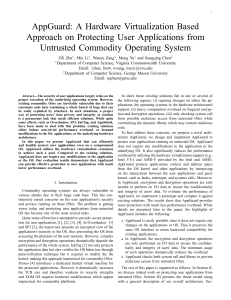
AppGuard - UTSA CS
... extensions. In addition, marshalling code at the user level in Overshadow could be exploited by the attacker. In AppGuard, all code is inside the hypervisor, which provides more strict protection. InkTag [2] verifies the OS behaviors through a new paraverification technique. It effectively secures t ...
... extensions. In addition, marshalling code at the user level in Overshadow could be exploited by the attacker. In AppGuard, all code is inside the hypervisor, which provides more strict protection. InkTag [2] verifies the OS behaviors through a new paraverification technique. It effectively secures t ...
Microkernels
... from their other processes that got pages from first. • Why is memory manager flexibility useful? – Different applications: real-time, multimedia, disk cache. ...
... from their other processes that got pages from first. • Why is memory manager flexibility useful? – Different applications: real-time, multimedia, disk cache. ...
Microkernels
... Tanenbaum, Modern Operating Systems 3 e, (c) 2008 Prentice-Hall, Inc. All rights reserved. 0-13-6006639 ...
... Tanenbaum, Modern Operating Systems 3 e, (c) 2008 Prentice-Hall, Inc. All rights reserved. 0-13-6006639 ...
Slides - Winlab
... • GPL requires back attribution and redistribution of changes • BSD is Free for All (very few clauses). • There are others:Mozilla Public license, Creative ...
... • GPL requires back attribution and redistribution of changes • BSD is Free for All (very few clauses). • There are others:Mozilla Public license, Creative ...
11. Kernel Design
... Only for very short periods of time Now mostly in legacy drivers and in the virtual file system ...
... Only for very short periods of time Now mostly in legacy drivers and in the virtual file system ...
The 27 Year Old Microkernel - foundry27
... Ex: Blocking kernel causes current thread to be blocked, another to be made RUNNING > __ker_exit implements this ...
... Ex: Blocking kernel causes current thread to be blocked, another to be made RUNNING > __ker_exit implements this ...
Kernel (operating system)
In computing, the kernel is a computer program that manages I/O requests from software, and translates them into data processing instructions for the central processing unit and other electronic components of a computer. The kernel is a fundamental part of a modern computer's operating system.The critical code of the kernel is usually loaded into a protected area of memory, which prevents it from being overwritten by other, less frequently used parts of the operating system or by applications. The kernel performs its tasks, such as executing processes and handling interrupts, in kernel space, whereas everything a user normally does, such as writing text in a text editor or running programs in a GUI (graphical user interface), is done in user space. This separation prevents user data and kernel data from interfering with each other and thereby diminishing performance or causing the system to become unstable (and possibly crashing). When a process makes requests of the kernel, the request is called a system call. Various kernel designs differ in how they manage system calls and resources. For example, a monolithic kernel executes all the operating system instructions in the same address space in order to improve the performance of the system. A microkernel runs most of the operating system's background processes in user space, to make the operating system more modular and, therefore, easier to maintain.The kernel's interface is a low-level abstraction layer.