Draft Minimum Requirements for FTA Digital Television Receivers
... good quality video and sound for the viewer and to ensure the lowest possible cost for the free-to-air receiver decoder. The Ghana DTT receiver standard is specified to include both the DVB-T/MPEG-2 and DVB-T2/MPEG-4M4 Levels to ensure backward compatibility with existing SDTV transmissions from Sky ...
... good quality video and sound for the viewer and to ensure the lowest possible cost for the free-to-air receiver decoder. The Ghana DTT receiver standard is specified to include both the DVB-T/MPEG-2 and DVB-T2/MPEG-4M4 Levels to ensure backward compatibility with existing SDTV transmissions from Sky ...
BASrouters — BACnet Routing Examples
... This application is a variant of Application #8 except that the PC is located remotely but attached to the Internet as is the IP router. Both the PC and the WAN-side of the IP Router have public IP addresses (1.2.3.4 and 2.3.4.5 for example). On the LAN-side of the IP Router is the building’s automa ...
... This application is a variant of Application #8 except that the PC is located remotely but attached to the Internet as is the IP router. Both the PC and the WAN-side of the IP Router have public IP addresses (1.2.3.4 and 2.3.4.5 for example). On the LAN-side of the IP Router is the building’s automa ...
The TELNET Protocol
... – The client takes input, translates into NVT sends it to the server, which translates to the representation that the computer uses. – Special Telnet commands are interspersed with the data to perform the functions needed to for the operation of the protocol Netprog: ...
... – The client takes input, translates into NVT sends it to the server, which translates to the representation that the computer uses. – Special Telnet commands are interspersed with the data to perform the functions needed to for the operation of the protocol Netprog: ...
Lec9-telnet
... – The client takes input, translates into NVT sends it to the server, which translates to the representation that the computer uses. – Special Telnet commands are interspersed with the data to perform the functions needed for the operation of the protocol Netprog: ...
... – The client takes input, translates into NVT sends it to the server, which translates to the representation that the computer uses. – Special Telnet commands are interspersed with the data to perform the functions needed for the operation of the protocol Netprog: ...
Access Control Lists Lecture 1
... Distribution of routing updates can be controlled Security can be added at the network boundary Specific types of traffic can be permitted or blocked An administrator controls what areas a client can access Screen certain hosts to either allow or deny access to part of a network ...
... Distribution of routing updates can be controlled Security can be added at the network boundary Specific types of traffic can be permitted or blocked An administrator controls what areas a client can access Screen certain hosts to either allow or deny access to part of a network ...
... As can be seen from Figure 4, the TS data packet is of a fixed length, the IP data packet is of a variable length. If the IP data packet can be encapsulated in TS packets of an integer number, the maximum encapsulation efficiency can be achieved. If the IP packet length increases 1B, a new TS packe ...
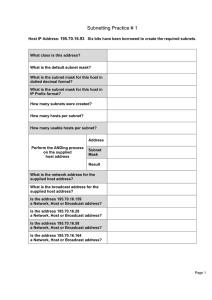
Subnetting Practice # 1
... Subnetting Practice # 12 You are the network administrator for Mangiare Food Supplies in Rome and are required to subnet the network according to the diagram. You have decided to use the network 172.31.0.0. It is the corporate policy that the IP address assigned to a default gateway is always the l ...
... Subnetting Practice # 12 You are the network administrator for Mangiare Food Supplies in Rome and are required to subnet the network according to the diagram. You have decided to use the network 172.31.0.0. It is the corporate policy that the IP address assigned to a default gateway is always the l ...
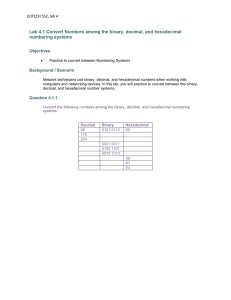
EDTECH 552, lab 4 Lab 4.1 Convert Numbers among the binary
... first 64 bits, or first four hextets, and the host portion, which is identified by the last 64 bits, or last four hextets. Remember that each number, or character, in an IPv6 address is written in hexadecimal, which is equivalent to four bits. The following is a typical global unicast address: The n ...
... first 64 bits, or first four hextets, and the host portion, which is identified by the last 64 bits, or last four hextets. Remember that each number, or character, in an IPv6 address is written in hexadecimal, which is equivalent to four bits. The following is a typical global unicast address: The n ...
Chapter 1: A First Look at Windows 2000 Professional
... protocols used with the internet to exchange messages, you should understand the fundamentals of the Internet to realize how email works. - You can send and receive e-mail via the Internet and local area network. Client computers access e-mail servers to receive messages. - Investigating crimes or p ...
... protocols used with the internet to exchange messages, you should understand the fundamentals of the Internet to realize how email works. - You can send and receive e-mail via the Internet and local area network. Client computers access e-mail servers to receive messages. - Investigating crimes or p ...
Trunks Avery ID Label
... E911 Notice for Comcast Business Trunks FCC rules require that IP-based phone service providers remind you about these important 911 facts: Comcast needs a correct service address to deliver your proper location information to a 911 operator. If you move Comcast provided equipment to a different add ...
... E911 Notice for Comcast Business Trunks FCC rules require that IP-based phone service providers remind you about these important 911 facts: Comcast needs a correct service address to deliver your proper location information to a 911 operator. If you move Comcast provided equipment to a different add ...
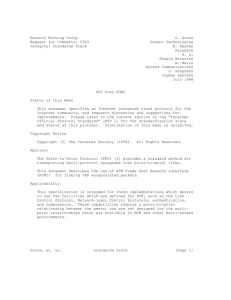
Network Working Group G. Gross Request for
... PAP/CHAP authentication protocols that are already widely in use for Internet dial up access are leveraged. As a consequence, PPP over FUNI security is at parity with those practices already established by the existing Internet infrastructure. Those applications that require stronger security are en ...
... PAP/CHAP authentication protocols that are already widely in use for Internet dial up access are leveraged. As a consequence, PPP over FUNI security is at parity with those practices already established by the existing Internet infrastructure. Those applications that require stronger security are en ...
Network Reference Model for cdma2000 Spread Spectrum
... choose any physical implementation of network entities, either individually or in combination, as long as the implementation meets the functional requirements. Sometimes, for practical reasons, the functional network entity is a physical device. The Mobile Station (MS) is an excellent example. • A r ...
... choose any physical implementation of network entities, either individually or in combination, as long as the implementation meets the functional requirements. Sometimes, for practical reasons, the functional network entity is a physical device. The Mobile Station (MS) is an excellent example. • A r ...
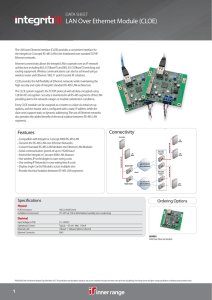
LAN Over Ethernet Module (CLOE)
... architecture including 802.3i (10baseT) and 802.3U (100baseT) switching and routing equipment. Wireless communications can also be achieved using a wireless router and Ethernet / 802.11 point to point RF solutions. CLOE provides the full flexibility of Ethernet networks while maintaining the high se ...
... architecture including 802.3i (10baseT) and 802.3U (100baseT) switching and routing equipment. Wireless communications can also be achieved using a wireless router and Ethernet / 802.11 point to point RF solutions. CLOE provides the full flexibility of Ethernet networks while maintaining the high se ...
Introduction - School of Engineering
... What are the uncompressed bit rates for the following multimedia sources : a) Telephone voice signal with a bandwidth between 200 and 3400 Hz, sampled with 8000 samples/s and 12 bit/sample. b) Wideband speech signal with a bandwidth between 50 and 7000 Hz, sampled with 16000 samples/s and 14 bit/sam ...
... What are the uncompressed bit rates for the following multimedia sources : a) Telephone voice signal with a bandwidth between 200 and 3400 Hz, sampled with 8000 samples/s and 12 bit/sample. b) Wideband speech signal with a bandwidth between 50 and 7000 Hz, sampled with 16000 samples/s and 14 bit/sam ...
《Electromagnetic Field and Microwave Technology》 Course syllabus
... One, the nature of the course, the purpose and the task High frequency electronic circuits is a professional basic courses of Communication Engineering Specialty .Through the studying of this course, make students familiar with the course described in various parts of the composition, characteristic ...
... One, the nature of the course, the purpose and the task High frequency electronic circuits is a professional basic courses of Communication Engineering Specialty .Through the studying of this course, make students familiar with the course described in various parts of the composition, characteristic ...
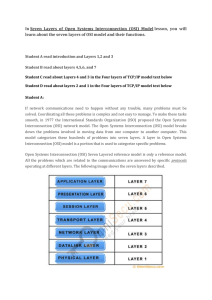
(Seven Layers of Open Systems Interconnection (OSI
... The fourth layer is the Transport layer. The Transport layer handles transport functions such as reliable or unreliable delivery of the data to the destination. On the sending computer, the transport layer is responsible for breaking the data into smaller packets, so that if any packet is lost durin ...
... The fourth layer is the Transport layer. The Transport layer handles transport functions such as reliable or unreliable delivery of the data to the destination. On the sending computer, the transport layer is responsible for breaking the data into smaller packets, so that if any packet is lost durin ...
True-False Questions
... two data communications on the same fiber-optic cable. two computers of different architecture talking to each other. interference with the signals on twisted wire media during high-speed transmission. set up by protocols. changing an analog signal to a digital one. ...
... two data communications on the same fiber-optic cable. two computers of different architecture talking to each other. interference with the signals on twisted wire media during high-speed transmission. set up by protocols. changing an analog signal to a digital one. ...
SOONERCARE INDEPENDENT LABORATORY PROVIDER
... The parties to this Agreement acknowledge and expect that over the term of this Agreement laws may change. Specifically, the parties acknowledge and expect (i) federal Medicaid statutes and regulations, (ii) state Medicaid statutes and rules, (iii) state statutes and rules governing practice of heal ...
... The parties to this Agreement acknowledge and expect that over the term of this Agreement laws may change. Specifically, the parties acknowledge and expect (i) federal Medicaid statutes and regulations, (ii) state Medicaid statutes and rules, (iii) state statutes and rules governing practice of heal ...
Foundation Fieldbus
... The VCR is like the speed dial feature on your memory telephone. There are many digits to dial for an international call—an international access code, country code, city code, exchange code, and the specific telephone number. This information only needs to be entered once and then a “speed dial numb ...
... The VCR is like the speed dial feature on your memory telephone. There are many digits to dial for an international call—an international access code, country code, city code, exchange code, and the specific telephone number. This information only needs to be entered once and then a “speed dial numb ...
CORD Fabric, Overlay Virtualization, and Service Composition
... Finally, SR is sourcerouting, where we can change the path traffic takes through the network, by simply changing the label assignment at the source (leaf) switch there is only one switch to ‘touch’ instead of the entire ‘path’ of switches. This is how we have performed elephantflow trafficen ...
... Finally, SR is sourcerouting, where we can change the path traffic takes through the network, by simply changing the label assignment at the source (leaf) switch there is only one switch to ‘touch’ instead of the entire ‘path’ of switches. This is how we have performed elephantflow trafficen ...
Chapter 1 Lecture Presentation
... TCP provides connection-oriented reliable byte transfer service UDP provides best-effort datagram service ...
... TCP provides connection-oriented reliable byte transfer service UDP provides best-effort datagram service ...
Slide 1
... Network devices can function as clients or as servers – Application server – File server – Print server Networks that include one or more servers can operate in client/server mode ...
... Network devices can function as clients or as servers – Application server – File server – Print server Networks that include one or more servers can operate in client/server mode ...