Viruses - University of Windsor
... from a Unix system. Several Linux viruses have been discovered. The Staog virus first appeared in 1996 and was written in assembly language by the VLAD virus writing group, the same group responsible for creating the first Windows 95 virus called Boza. Like the Boza virus, the Staog virus is a proof ...
... from a Unix system. Several Linux viruses have been discovered. The Staog virus first appeared in 1996 and was written in assembly language by the VLAD virus writing group, the same group responsible for creating the first Windows 95 virus called Boza. Like the Boza virus, the Staog virus is a proof ...
Chapter 11
... – Similar approach developed by the NSA – Modes of protection • People • Technology • Operations Guide to Computer Forensics and Investigations ...
... – Similar approach developed by the NSA – Modes of protection • People • Technology • Operations Guide to Computer Forensics and Investigations ...
11 Secure electronic communication
... Backup procedure tested by performing a restoration of data Backup procedure included in a documented business continuity and disaster ...
... Backup procedure tested by performing a restoration of data Backup procedure included in a documented business continuity and disaster ...
SECURITY METRICS FOR ENTERPRISE INFORMATION SYSTEMS Interdisciplinarity – New Approaches and Perspectives
... vulnerabilities in a consistent fashion while at the same time allowing for personalization within each user environment. As CVSS matures, these metrics may expand or adjust making it even more accurate, flexible and representative of modern vulnerabilities and their risks. ...
... vulnerabilities in a consistent fashion while at the same time allowing for personalization within each user environment. As CVSS matures, these metrics may expand or adjust making it even more accurate, flexible and representative of modern vulnerabilities and their risks. ...
Types of Attacks - Digital Locker and Personal Web Space
... Communication request sent to target system. Target responds to faked IP address. Target waits for non-existent system response. Request eventually times out. If the attacks outpace the requests timing-out, then systems resources will be exhausted. ...
... Communication request sent to target system. Target responds to faked IP address. Target waits for non-existent system response. Request eventually times out. If the attacks outpace the requests timing-out, then systems resources will be exhausted. ...
Federal Systems Level Guidance for Securing
... As most of us know, routers are the traffic cops of computer networks. Routers direct and control data flowing across networks and the Internet. Network administrators and security officers work in conjunction to secure network perimeters. They use routers to control network access, ward-off attacks ...
... As most of us know, routers are the traffic cops of computer networks. Routers direct and control data flowing across networks and the Internet. Network administrators and security officers work in conjunction to secure network perimeters. They use routers to control network access, ward-off attacks ...
Information Security Attack Tree Modeling for Enhancing Student Learning
... [G1, G21, G31, G41, G51], [G1, G21, G32, G41, G51], [G1, G21, G31, G42, G51], [G1, G21, G32, G42, G51], [G1, G22, G31, G41, G51], [G1, G22, G32, G41, G51], [G1, G22, G31, G42, G51], [G1, G22, G32, G42, G51], [G1, G23, G31, G41, G51], [G1, G23, G32, G41, G51], [G1, G23, G31, G42, G51], [G1, G23, G32, ...
... [G1, G21, G31, G41, G51], [G1, G21, G32, G41, G51], [G1, G21, G31, G42, G51], [G1, G21, G32, G42, G51], [G1, G22, G31, G41, G51], [G1, G22, G32, G41, G51], [G1, G22, G31, G42, G51], [G1, G22, G32, G42, G51], [G1, G23, G31, G41, G51], [G1, G23, G32, G41, G51], [G1, G23, G31, G42, G51], [G1, G23, G32, ...
COMPUTER CRIME Computer crime
... possible, hard disk is removed without turning computer on Special forensics computer is used to ensure that nothing is written to drive Forensic image copy – an exact copy or snapshot of all stored information ...
... possible, hard disk is removed without turning computer on Special forensics computer is used to ensure that nothing is written to drive Forensic image copy – an exact copy or snapshot of all stored information ...
Firewall Evolution
... packets in a flow based on source and destination IP addresses, source and destination ports, and the protocol used. If a packet matched this information bi-directionally, then it belonged to the flow. As use of the Internet expanded and businesses became highly networked, they could selectively pro ...
... packets in a flow based on source and destination IP addresses, source and destination ports, and the protocol used. If a packet matched this information bi-directionally, then it belonged to the flow. As use of the Internet expanded and businesses became highly networked, they could selectively pro ...
Chapter 1
... technology becomes outdated, there is a risk of loss of data integrity to threats and attacks Ideally, proper planning by management should prevent risks from technology obsolesce, but when obsolescence is identified, management must take action ...
... technology becomes outdated, there is a risk of loss of data integrity to threats and attacks Ideally, proper planning by management should prevent risks from technology obsolesce, but when obsolescence is identified, management must take action ...
Estimating Impact and Frequency of Risks to
... Our work is mainly related to controlling security risks and in particular quantifying security risks; that is, quantitative risk analysis. The current strategies for controlling security risks are: (i) penetration and patch, (ii) standards, (iii) risk management/assessment and (iv) “wait and see” a ...
... Our work is mainly related to controlling security risks and in particular quantifying security risks; that is, quantitative risk analysis. The current strategies for controlling security risks are: (i) penetration and patch, (ii) standards, (iii) risk management/assessment and (iv) “wait and see” a ...
Real-Time Georgia…….
... European Internet Business Group (EIBG) – Established and led Digital Equipment Corporation’s European Internet Group for 5 years, from 1994 to 1999. Projects included support for the national Internet infrastructure for countries across EMEA as well as major enterprise, government & educational Int ...
... European Internet Business Group (EIBG) – Established and led Digital Equipment Corporation’s European Internet Group for 5 years, from 1994 to 1999. Projects included support for the national Internet infrastructure for countries across EMEA as well as major enterprise, government & educational Int ...
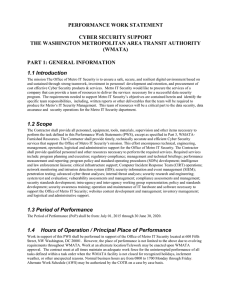
SOW
... methods of notification will be provided by WMATA. No price adjustments will be made for any delays resulting from an installation closing. When area radio stations, TV stations or WMATA’s website report that a facility has "delayed reporting" until a particular time, the Contractor's personnel have ...
... methods of notification will be provided by WMATA. No price adjustments will be made for any delays resulting from an installation closing. When area radio stations, TV stations or WMATA’s website report that a facility has "delayed reporting" until a particular time, the Contractor's personnel have ...
AISE PoIS4E_PP_ch02_57
... • Enforcement of copyright law has been attempted with a number of technical security mechanisms, including digital watermarks, embedded codes. ...
... • Enforcement of copyright law has been attempted with a number of technical security mechanisms, including digital watermarks, embedded codes. ...
updated system threat and requirements analysis for high assurance
... a protection layer is the High Assurance Wireless Computing System (HAWCS™) for consumer/commercial wireless. To protect a wireless system which employs “soft” consumer operating systems and applications and guarantee secure eCommerce, the defensive layers must span a portion of the wireless device ...
... a protection layer is the High Assurance Wireless Computing System (HAWCS™) for consumer/commercial wireless. To protect a wireless system which employs “soft” consumer operating systems and applications and guarantee secure eCommerce, the defensive layers must span a portion of the wireless device ...
Top Five DNS Security Attack Risks and How to Avoid Them
... Many administrators don’t take the simple precaution of configuring their forwarders to process recursive queries only from internal IP addresses. This may be because they don’t know how or because they don’t understand the implications of leaving an external name server “open” to recursive queries. ...
... Many administrators don’t take the simple precaution of configuring their forwarders to process recursive queries only from internal IP addresses. This may be because they don’t know how or because they don’t understand the implications of leaving an external name server “open” to recursive queries. ...
Slides - School of Information Sciences
... Composed of a sequence of instructions that is interpreted rather than executed directly Infected “executable” isn’t machine code Relies on something “executed” inside application data Example: Melissa virus infected Word 97/98 docs ...
... Composed of a sequence of instructions that is interpreted rather than executed directly Infected “executable” isn’t machine code Relies on something “executed” inside application data Example: Melissa virus infected Word 97/98 docs ...
Cloudinomicon - Rational Survivability
... “The high level of usage (and its somewhat clandestine nature) was illustrated at a conference earlier this year when one CIO noted that he had gone through the expense reports turned into him for reimbursement and found 50 different cloud computing accounts being used by developers in his organisat ...
... “The high level of usage (and its somewhat clandestine nature) was illustrated at a conference earlier this year when one CIO noted that he had gone through the expense reports turned into him for reimbursement and found 50 different cloud computing accounts being used by developers in his organisat ...
Proactive Compliance for Insider Threat Protection
... It is important to remember that insider threat detection and information assurance (IA) are two different missions with some overlapping areas of data and tools. An insider threat is an individual who uses his/her authorized access to wittingly or unwittingly do harm. To meet this challenge, you ne ...
... It is important to remember that insider threat detection and information assurance (IA) are two different missions with some overlapping areas of data and tools. An insider threat is an individual who uses his/her authorized access to wittingly or unwittingly do harm. To meet this challenge, you ne ...
IMPACT OF SECURITY BREACHES
... the three primary processes that a business needs to implement in order to become and stay secure. The three processes are: • Assessment – This phase involves gathering relevant information from the organization’s environment to perform a security assessment. You need to capture enough data to effec ...
... the three primary processes that a business needs to implement in order to become and stay secure. The three processes are: • Assessment – This phase involves gathering relevant information from the organization’s environment to perform a security assessment. You need to capture enough data to effec ...
Practice Questions with Solutions
... b. To prove that it is not malicious c. To prove that it can be trusted d. To prove that it was downloaded properly 61. An organization wants to prevent SQL and script injection attacks on its Internet web application. The organization should implement a/an: a. Intrusion detection system b. Firewall ...
... b. To prove that it is not malicious c. To prove that it can be trusted d. To prove that it was downloaded properly 61. An organization wants to prevent SQL and script injection attacks on its Internet web application. The organization should implement a/an: a. Intrusion detection system b. Firewall ...
Intrusion Detection System (IDS)
... The level of seriousness and sophistication of recent cyberattacks has risen dramatically over the past 10 years The availability of widespread free automated intrusion tools and exploit scripts duplicate the known methods of attack Attacks are getting more sophisticated and easy to copy Increased c ...
... The level of seriousness and sophistication of recent cyberattacks has risen dramatically over the past 10 years The availability of widespread free automated intrusion tools and exploit scripts duplicate the known methods of attack Attacks are getting more sophisticated and easy to copy Increased c ...
Document
... The level of seriousness and sophistication of recent cyberattacks has risen dramatically over the past 10 years The availability of widespread free automated intrusion tools and exploit scripts duplicate the known methods of attack Attacks are getting more sophisticated and easy to copy Increased c ...
... The level of seriousness and sophistication of recent cyberattacks has risen dramatically over the past 10 years The availability of widespread free automated intrusion tools and exploit scripts duplicate the known methods of attack Attacks are getting more sophisticated and easy to copy Increased c ...
ppt
... Should we consider 3a part of the data stream “USER root”? Or is 3b part of the data stream? “USER foot”! • If the OS makes a different decision than the monitor: Bad. • Even worse: Different OS’s have different protocol interpretations, so it’s impossible for a firewall to agree with all of them ...
... Should we consider 3a part of the data stream “USER root”? Or is 3b part of the data stream? “USER foot”! • If the OS makes a different decision than the monitor: Bad. • Even worse: Different OS’s have different protocol interpretations, so it’s impossible for a firewall to agree with all of them ...