YABLO WITHOUT GODEL
... In the present paper we do not advocate a particular analysis of circularity or selfreference. We only would like to explain in which sense Yablo’s and Visser’s paradox in our setting are not circular or self-referential. First, the paradox doesn’t involve any term that denotes a formula in which th ...
... In the present paper we do not advocate a particular analysis of circularity or selfreference. We only would like to explain in which sense Yablo’s and Visser’s paradox in our setting are not circular or self-referential. First, the paradox doesn’t involve any term that denotes a formula in which th ...
A Survey on Small Fragments of First-Order Logic over Finite
... basic transformations between finite automata and rational expressions. However, very often the connection to logic and algebra is completely ignored although highlights in formal language theory can be found here. The connection between automata and logic goes back to Büchi. He used monadic second ...
... basic transformations between finite automata and rational expressions. However, very often the connection to logic and algebra is completely ignored although highlights in formal language theory can be found here. The connection between automata and logic goes back to Büchi. He used monadic second ...
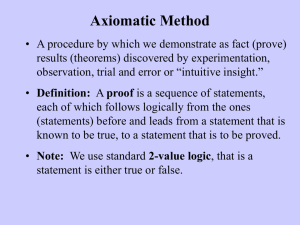
ppt - UBC Computer Science
... Proof by intimidation Proof by lack of space (Fermat's favorite!) Proof by authority Proof by never-ending revision For the full list, see: ...
... Proof by intimidation Proof by lack of space (Fermat's favorite!) Proof by authority Proof by never-ending revision For the full list, see: ...
fp_in_scheme
... • We’ll look at how the variable environments work to support this in the next topic, closures • But first, let’s see how to define a general version of compose taking any number of args ...
... • We’ll look at how the variable environments work to support this in the next topic, closures • But first, let’s see how to define a general version of compose taking any number of args ...
The greatest common divisor: a case study for program extraction
... Recall that, using the abbreviations above, u denotes the assumption u: ∀~k(µ(~k)|a1 → µ(~k)|a2 → N (~k)). The derivations below are given in a natural deduction calculus and are written as typed λ–terms according to the well–known Curry–Howard correspondence. By e we will denote (different) subderi ...
... Recall that, using the abbreviations above, u denotes the assumption u: ∀~k(µ(~k)|a1 → µ(~k)|a2 → N (~k)). The derivations below are given in a natural deduction calculus and are written as typed λ–terms according to the well–known Curry–Howard correspondence. By e we will denote (different) subderi ...
Functional Programming
... function. Relate to mathematical notation f(x) = x2 – (( x . x2 )2): apply the function to a value, similar to f(x) = x2 for x = 2 ...
... function. Relate to mathematical notation f(x) = x2 – (( x . x2 )2): apply the function to a value, similar to f(x) = x2 for x = 2 ...
First-Order Loop Formulas for Normal Logic Programs
... variables, we can hopefully avoid this problem of having to compute similar loops and loop formulas every time a program is grounded on a domain. Thus extending loop formulas in logic programming to first-order case is not only theoretically interesting, but may also be of practical relevance. Speci ...
... variables, we can hopefully avoid this problem of having to compute similar loops and loop formulas every time a program is grounded on a domain. Thus extending loop formulas in logic programming to first-order case is not only theoretically interesting, but may also be of practical relevance. Speci ...
Logic and Discrete Mathematics for Computer Scientists
... Discrete mathematics is a required course in the undergraduate Computer Science curriculum. In a perhaps unsympathetic view, the standard presentations (and there are many )the material in the course is treated as a discrete collection of so many techniques that the students must master for further ...
... Discrete mathematics is a required course in the undergraduate Computer Science curriculum. In a perhaps unsympathetic view, the standard presentations (and there are many )the material in the course is treated as a discrete collection of so many techniques that the students must master for further ...
Microelectronic Circuit Design
... • Voltage levels of the output of one gate should be compatible with the input levels of a proceeding gate • The gate should have sufficient fan-out and fan-in capabilities • The gate should consume minimal power (and area for ICs) and still operate under the design specifications ...
... • Voltage levels of the output of one gate should be compatible with the input levels of a proceeding gate • The gate should have sufficient fan-out and fan-in capabilities • The gate should consume minimal power (and area for ICs) and still operate under the design specifications ...
Argument construction and reinstatement in logics for
... among conflicting arguments is particularly important for the application of techniques from artificial intelligence to fields in which adversarial reasoning figures prominently, such as negotiation or, of course, the law. I focus in this paper on two recent argument systems, both of which are heavi ...
... among conflicting arguments is particularly important for the application of techniques from artificial intelligence to fields in which adversarial reasoning figures prominently, such as negotiation or, of course, the law. I focus in this paper on two recent argument systems, both of which are heavi ...
pdf
... modeled is that in all the states an agent considers possible at a state s, fewer concepts may be defined than are defined at state s. Because a proposition p may be undefined at a given state s, the underlying logic in HMS is best viewed as a 3-valued logic: a proposition p may be true, false, or ...
... modeled is that in all the states an agent considers possible at a state s, fewer concepts may be defined than are defined at state s. Because a proposition p may be undefined at a given state s, the underlying logic in HMS is best viewed as a 3-valued logic: a proposition p may be true, false, or ...
Expressing C++ Template Metaprograms as Lambda expressions
... Recursive template metafunctions can be defined as well because a class is in scope in it’s definition. Recursion can be stopped by pattern matching. Here is an ...
... Recursive template metafunctions can be defined as well because a class is in scope in it’s definition. Recursion can be stopped by pattern matching. Here is an ...
Curry–Howard correspondence

In programming language theory and proof theory, the Curry–Howard correspondence (also known as the Curry–Howard isomorphism or equivalence, or the proofs-as-programs and propositions- or formulae-as-types interpretation) is the direct relationship between computer programs and mathematical proofs. It is a generalization of a syntactic analogy between systems of formal logic and computational calculi that was first discovered by the American mathematician Haskell Curry and logician William Alvin Howard. It is the link between logic and computation that is usually attributed to Curry and Howard, although the idea is related to the operational interpretation of intuitionistic logic given in various formulations by L. E. J. Brouwer, Arend Heyting and Andrey Kolmogorov (see Brouwer–Heyting–Kolmogorov interpretation) and Stephen Kleene (see Realizability). The relationship has been extended to include category theory as the three-way Curry–Howard–Lambek correspondence.