(Simple) Preprocessor for Adding Multi
... assignment to v is captured by the binary predicate val . Thus passing the logic program in (1) to an ASP system yields three answer sets, given by {val (v, 1)}, {val (v, 2)}, and {val (v, 3)}, each representing a valid assignment to variable v. The declaration #variables also allows for more fine-g ...
... assignment to v is captured by the binary predicate val . Thus passing the logic program in (1) to an ASP system yields three answer sets, given by {val (v, 1)}, {val (v, 2)}, and {val (v, 3)}, each representing a valid assignment to variable v. The declaration #variables also allows for more fine-g ...
Nicola Muscettola, Ioannis Tsamardinos, Luke Hunsberger
... A set of time-points that are pairwise rigidly connected form a rigid component. tj ...
... A set of time-points that are pairwise rigidly connected form a rigid component. tj ...
Breaking Symmetry with Different Orderings
... in M 0 . Hence, a row from the third set that embeds a row from B has to be the third row in M 0 . We do not specify which row it is at this point. The fourth row has to be again a row from the second set as any of remaining rows from the second set has z + 1 zeros in the last z + 1 columns in M 0 w ...
... in M 0 . Hence, a row from the third set that embeds a row from B has to be the third row in M 0 . We do not specify which row it is at this point. The fourth row has to be again a row from the second set as any of remaining rows from the second set has z + 1 zeros in the last z + 1 columns in M 0 w ...
Algorithms for Maximum Satisfiability
... software package management [Argelich, Berre, Lynce, Marques-Silva, and Rapicault, 2010] [Ignatiev, Janota, and Marques-Silva, 2014] ...
... software package management [Argelich, Berre, Lynce, Marques-Silva, and Rapicault, 2010] [Ignatiev, Janota, and Marques-Silva, 2014] ...
Executing clinical guidelines: temporal issues
... the temporal constraints given on their classes. This also means that the (implicit) temporal constraints conveyed by the part-of relations between actions in the guideline must be respected, as well as those involved by periodicity and repetitions. In a broad sense, periodic events are special kind ...
... the temporal constraints given on their classes. This also means that the (implicit) temporal constraints conveyed by the part-of relations between actions in the guideline must be respected, as well as those involved by periodicity and repetitions. In a broad sense, periodic events are special kind ...
Survey of Applications Integrating Constraint Satisfaction and Case
... also help a reasoner focus its reasoning on important parts of a problem by pointing out what features of a problem are the important ones. User acceptance is another often difficult problem for knowledge-based systems. Users can be reluctant to trust the results from an automated computer system. ...
... also help a reasoner focus its reasoning on important parts of a problem by pointing out what features of a problem are the important ones. User acceptance is another often difficult problem for knowledge-based systems. Users can be reluctant to trust the results from an automated computer system. ...
Document
... constraints examples of elements of GCL X/Age(Monika) is R/young (annotated element) (X isp R) and (X,Y) is S) (X isr R) is unlikely) and (X iss S) is likely If X is A then Y is B the language of fuzzy if-then rules is a sublanguage of GCL deduction= generalized constraint propagation and ...
... constraints examples of elements of GCL X/Age(Monika) is R/young (annotated element) (X isp R) and (X,Y) is S) (X isr R) is unlikely) and (X iss S) is likely If X is A then Y is B the language of fuzzy if-then rules is a sublanguage of GCL deduction= generalized constraint propagation and ...
PDF
... ∀jk (¬x1jk ∧ ¬x2jk )(¬x1jk ∧ ¬x3jk ) . . . (¬x1jk ∧ ¬xnjk ). Constraint (1) becomes a clause of length n for each cell, and (2) and (3) become sets of negative binary clauses. The total number of clauses is O(n4 ). The binary representation of a Latin square can be viewed as a cube, where the dimens ...
... ∀jk (¬x1jk ∧ ¬x2jk )(¬x1jk ∧ ¬x3jk ) . . . (¬x1jk ∧ ¬xnjk ). Constraint (1) becomes a clause of length n for each cell, and (2) and (3) become sets of negative binary clauses. The total number of clauses is O(n4 ). The binary representation of a Latin square can be viewed as a cube, where the dimens ...
Reasoning about Time
... Constraint-based approaches mainly focus on the definition of a representation formalism and of reasoning techniques to deal specifically with temporal constraints between temporal entities (time points or intervals), independently of the events and states associated with them. For instance, given t ...
... Constraint-based approaches mainly focus on the definition of a representation formalism and of reasoning techniques to deal specifically with temporal constraints between temporal entities (time points or intervals), independently of the events and states associated with them. For instance, given t ...
X is A - Wiki Index
... constraints examples of elements of GCL X/Age(Monika) is R/young (annotated element) (X isp R) and (X,Y) is S) (X isr R) is unlikely) and (X iss S) is likely If X is A then Y is B the language of fuzzy if-then rules is a sublanguage of GCL deduction= generalized constraint propagation and ...
... constraints examples of elements of GCL X/Age(Monika) is R/young (annotated element) (X isp R) and (X,Y) is S) (X isr R) is unlikely) and (X iss S) is likely If X is A then Y is B the language of fuzzy if-then rules is a sublanguage of GCL deduction= generalized constraint propagation and ...
Reasoning about Topological and Positional Information in Dynamic Settings
... Qualitative reasoning problems are usually cast as constraint satisfaction problems (CSP), i. e., as the problem to determine whether a given finite set of constraints (a constraint network) is satisfiable or entailed by another constraint network. Here we focus on binary constraint satisfaction pro ...
... Qualitative reasoning problems are usually cast as constraint satisfaction problems (CSP), i. e., as the problem to determine whether a given finite set of constraints (a constraint network) is satisfiable or entailed by another constraint network. Here we focus on binary constraint satisfaction pro ...
A case-based expert system for scheduling problems
... system approach cannot be applied. In scheduling problems, theoretical knowledge and some heuristics exists. Unfortunately, practical knowledge and experience may be of limited value. A number of review papers have been published in this area (Steffen [13], Kusiak and Chen [14], Charalambous and Hin ...
... system approach cannot be applied. In scheduling problems, theoretical knowledge and some heuristics exists. Unfortunately, practical knowledge and experience may be of limited value. A number of review papers have been published in this area (Steffen [13], Kusiak and Chen [14], Charalambous and Hin ...
Paper - FB3
... Description Logics (DLs) are an important family of logic-based knowledge representation formalisms [4]. In DL, one of the main research goals is to provide a toolbox of logics such that, for a given application, one can select a DL with adequate expressivity. Here, adequate means that, on the one h ...
... Description Logics (DLs) are an important family of logic-based knowledge representation formalisms [4]. In DL, one of the main research goals is to provide a toolbox of logics such that, for a given application, one can select a DL with adequate expressivity. Here, adequate means that, on the one h ...
Incremental temporal reasoning in job shop scheduling repair Please share
... specifically gathering massive observable data in real time. In addition, tools such as reactive monitoring systems will manipulate these data and estimate the current status of the job shop, so as to support reactive schedule repairing. The predictive schedules are usually based on optimization obj ...
... specifically gathering massive observable data in real time. In addition, tools such as reactive monitoring systems will manipulate these data and estimate the current status of the job shop, so as to support reactive schedule repairing. The predictive schedules are usually based on optimization obj ...
PDF
... A label corresponds to a snapshot of variable assignments at a particular point in the search. The current assignments of these variables may or may not correspond to the assignments specified in the label. Definition 3. A label, λ, is valid iff every variable assignment hx = ai ∈ λ is the current ...
... A label corresponds to a snapshot of variable assignments at a particular point in the search. The current assignments of these variables may or may not correspond to the assignments specified in the label. Definition 3. A label, λ, is valid iff every variable assignment hx = ai ∈ λ is the current ...
Distributed Constraint Satisfaction Algorithm for Complex Local
... For example, if agent k has two local variables xi ; xj , we assume that there exist two virtual agents, each of which corresponds to either xi or xj . Then, agent k simulates the concurrent activities of these two virtual agents. In this case, each agent does not have to predetermine all the local ...
... For example, if agent k has two local variables xi ; xj , we assume that there exist two virtual agents, each of which corresponds to either xi or xj . Then, agent k simulates the concurrent activities of these two virtual agents. In this case, each agent does not have to predetermine all the local ...
Linear-Time Filtering Algorithms for the Disjunctive Constraint
... Abstract We present three new filtering algorithms for the D ISJUNCTIVE constraint that all have a linear running time complexity in the number of tasks. The first algorithm filters the tasks according to the rules of the time tabling. The second algorithm performs an overload check that could also ...
... Abstract We present three new filtering algorithms for the D ISJUNCTIVE constraint that all have a linear running time complexity in the number of tasks. The first algorithm filters the tasks according to the rules of the time tabling. The second algorithm performs an overload check that could also ...
Resolve and Expand
... Expansion often needs to copy almost all clauses of the CNF. Moreover, the elimination procedures of Sec. 3 produce a lot of redundant subsumed clauses. Therefore, subsumed clauses should be removed. If a new clause is added, all old clauses are checked for being subsumed by this new clause. This ch ...
... Expansion often needs to copy almost all clauses of the CNF. Moreover, the elimination procedures of Sec. 3 produce a lot of redundant subsumed clauses. Therefore, subsumed clauses should be removed. If a new clause is added, all old clauses are checked for being subsumed by this new clause. This ch ...
LNCS 3258 - Full Dynamic Substitutability by SAT Encoding
... Full Dynamic Substitutability by SAT Encoding ...
... Full Dynamic Substitutability by SAT Encoding ...
Full Dynamic Substitutability by SAT Encoding
... space size. The most straightforward approach is to add constraints to the problem formulation, so that each equivalence class of solutions to the original problem corresponds to a single solution in the new problem [28]. Alternatively symmetries may be detected and exploited dynamically during sear ...
... space size. The most straightforward approach is to add constraints to the problem formulation, so that each equivalence class of solutions to the original problem corresponds to a single solution in the new problem [28]. Alternatively symmetries may be detected and exploited dynamically during sear ...
Constraint-Based Knowledge Representation for Individualized
... but the instructor might not be able to steer them towards a particular topic, making this type of instruction difficult to use in public schools and other instructional institutions that assume a prespecified curriculum. Also, openended instruction is not appropriate for all types of subject matter ...
... but the instructor might not be able to steer them towards a particular topic, making this type of instruction difficult to use in public schools and other instructional institutions that assume a prespecified curriculum. Also, openended instruction is not appropriate for all types of subject matter ...
A Partial Taxonomy of Substitutability and Interchangeability
... [Freuder, 1991]. At the end of the process, the leaves of the discrimination tree are annotated with the equivalence NI values for the variable. The complexity of this process is O(n2 d2 ), where n is the number of variables and d is the maximum domain size. Alternatively, one can build a refutatio ...
... [Freuder, 1991]. At the end of the process, the leaves of the discrimination tree are annotated with the equivalence NI values for the variable. The complexity of this process is O(n2 d2 ), where n is the number of variables and d is the maximum domain size. Alternatively, one can build a refutatio ...
Logic Programming for Knowledge Representation
... We note that if P is a Horn constraint program and t is a P -computation, Rt is a supported model of P . Derivable models. A set M of atoms is a derivable model of a Horn constraint program P if there exists a P -computation t such that M = Rt . If a Horn constraint program has a model, one can sho ...
... We note that if P is a Horn constraint program and t is a P -computation, Rt is a supported model of P . Derivable models. A set M of atoms is a derivable model of a Horn constraint program P if there exists a P -computation t such that M = Rt . If a Horn constraint program has a model, one can sho ...
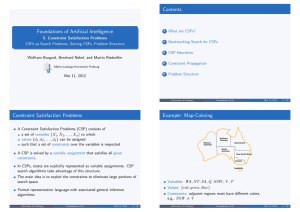
5. Constraint Satisfaction Problems CSPs as Search Problems
... function R EVISE( csp, Xi , Xj ) returns true iff we revise the domain of Xi revised ← false for each x in Di do if no value y in Dj allows (x ,y) to satisfy the constraint between Xi and Xj then delete x from Di revised ← true return revised Figure 6.3 ...
... function R EVISE( csp, Xi , Xj ) returns true iff we revise the domain of Xi revised ← false for each x in Di do if no value y in Dj allows (x ,y) to satisfy the constraint between Xi and Xj then delete x from Di revised ← true return revised Figure 6.3 ...
A Fast Arc Consistency Algorithm for n-ary Constraints Olivier Lhomme Jean-Charles R´egin
... of the values in the current domain of x6 . The next support after t which is a support for (x6 , 1) is (1, 1, 1, 1, 1, 1); the next support after t which is a support for (x6 , 2) is (2, 2, 2, 2, 2, 2); the next support after t which is a support for (x6 , 3) is (3, 3, 3, 3, 3, 3), The next support ...
... of the values in the current domain of x6 . The next support after t which is a support for (x6 , 1) is (1, 1, 1, 1, 1, 1); the next support after t which is a support for (x6 , 2) is (2, 2, 2, 2, 2, 2); the next support after t which is a support for (x6 , 3) is (3, 3, 3, 3, 3, 3), The next support ...