무선 메쉬 네트워크 (Wireless Mesh Network)
... Loss rate of broadcast probe packets is not the same as loss rate of data packets Under-estimates data loss ratios, over-estimates ACK loss ratios ...
... Loss rate of broadcast probe packets is not the same as loss rate of data packets Under-estimates data loss ratios, over-estimates ACK loss ratios ...
Introduction - Tsinghua Future Internet communication Lab
... library of m files. Requests can be served by the cellular base station, and/or by D2D links. Realistic assumptions on the channel models are made for the cellular links and the D2D links, assuming that the former uses a 4th generation cellular standard (2.1 GHz) and the latter use either microwav ...
... library of m files. Requests can be served by the cellular base station, and/or by D2D links. Realistic assumptions on the channel models are made for the cellular links and the D2D links, assuming that the former uses a 4th generation cellular standard (2.1 GHz) and the latter use either microwav ...
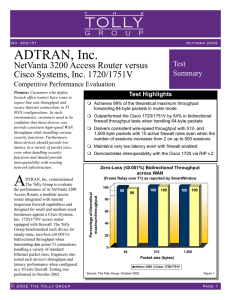
NetVanta 3200 Tolly Group Report
... using the SmartBits SmartWindow and the latency test defined in the RFC 2544 test suite. Traffic was generated at 10% of T1 line rate with 2 sessions running for baseline latency tests. For firewall latency tests, traffic was generated at 10%, 13% and 39% of the T1 line rate, while using 64-, 512- a ...
... using the SmartBits SmartWindow and the latency test defined in the RFC 2544 test suite. Traffic was generated at 10% of T1 line rate with 2 sessions running for baseline latency tests. For firewall latency tests, traffic was generated at 10%, 13% and 39% of the T1 line rate, while using 64-, 512- a ...
Neutron hybrid mode
... • Overlays provide connectivity between VMs and Network Devices using tunnels • The physical core network does not need to be re-provisioned constantly ...
... • Overlays provide connectivity between VMs and Network Devices using tunnels • The physical core network does not need to be re-provisioned constantly ...
TCP in Wireless Networks
... losses) by appropriately throttling the senders’ transmission rates. Network congestion is deemed to be the underlying reason for packet losses. Consequently, TCP performance is often unsatisfactory when used in wireless networks and requires various improvement techniques [2]. A key factor causing ...
... losses) by appropriately throttling the senders’ transmission rates. Network congestion is deemed to be the underlying reason for packet losses. Consequently, TCP performance is often unsatisfactory when used in wireless networks and requires various improvement techniques [2]. A key factor causing ...
IEEE Vehicular Technology Conference (VTC)
... interference and congestion that reduces the achievable throughput. A variety of mechanisms including RTS/CTS and exponential back-off are intended to limit the damage of congestion and interference. On the other hand, unlike cellular networks, mesh networks such as these can exhibit cooperative gai ...
... interference and congestion that reduces the achievable throughput. A variety of mechanisms including RTS/CTS and exponential back-off are intended to limit the damage of congestion and interference. On the other hand, unlike cellular networks, mesh networks such as these can exhibit cooperative gai ...
Presentation
... When the wireless medium is congested and the traffic consists of many random UDP flows, COPE increases the throughput 3-4x. In the absence of congestion controlled traffic (UDP), COPE’s throughput improvement may substantially exceed the expected theoretical coding gain. (Coding + MAC gain) For a ...
... When the wireless medium is congested and the traffic consists of many random UDP flows, COPE increases the throughput 3-4x. In the absence of congestion controlled traffic (UDP), COPE’s throughput improvement may substantially exceed the expected theoretical coding gain. (Coding + MAC gain) For a ...
Communication Performance over a Gigabit Ethernet Network.
... • The host systems must support RFC1323 ”Large Windows” extensions to TCP. This RFC defines a set of TCP extensions to improve performance over large bandwidth × delay paths and to provide reliable operation over high-speed paths. • The host system must support large enough socket buffers for readin ...
... • The host systems must support RFC1323 ”Large Windows” extensions to TCP. This RFC defines a set of TCP extensions to improve performance over large bandwidth × delay paths and to provide reliable operation over high-speed paths. • The host system must support large enough socket buffers for readin ...
pptx - CSE Labs User Home Pages
... Design Goal 2 says to send all your traffic on the least congested path, in this case 3G. But this has high RTT, hence it will give low throughput. Goal 3a. A Multipath TCP user should get at least as much throughput as a single-path TCP would on the best of the available paths. Goal 3b. A Multipath ...
... Design Goal 2 says to send all your traffic on the least congested path, in this case 3G. But this has high RTT, hence it will give low throughput. Goal 3a. A Multipath TCP user should get at least as much throughput as a single-path TCP would on the best of the available paths. Goal 3b. A Multipath ...
Understanding Carrier Ethernet Throughput
... Committed Burst Size (CBS) will provide a poor user experience, with dropped traffic, retransmissions, and net throughputs which are much lower than expected. Other key application issues include optimally setting Transport Control Protocol (TCP) window size on applications which require higher spee ...
... Committed Burst Size (CBS) will provide a poor user experience, with dropped traffic, retransmissions, and net throughputs which are much lower than expected. Other key application issues include optimally setting Transport Control Protocol (TCP) window size on applications which require higher spee ...
CN Lab Manual For IS Dept.
... applications over TCP and UDP agents changing the parameter and determine the number of packets by TCP/UDP. 3. Simulate the different types of Internet traffic such as FTP a TELNET over a network and analyze the throughput. 4. Simulate the transmission of ping messaged over a network topology consis ...
... applications over TCP and UDP agents changing the parameter and determine the number of packets by TCP/UDP. 3. Simulate the different types of Internet traffic such as FTP a TELNET over a network and analyze the throughput. 4. Simulate the transmission of ping messaged over a network topology consis ...
T R ECHNICAL ESEARCH
... satellite or via a terrestrial link. (The value of h was chosen supposing the ARQ frame has a 16-bit sequence number and a 16-bit CRC for error detection. The value of ` was chosen to maximize the throughput in a point-to-point satellite network, which is the reference network for comparison purpose ...
... satellite or via a terrestrial link. (The value of h was chosen supposing the ARQ frame has a 16-bit sequence number and a 16-bit CRC for error detection. The value of ` was chosen to maximize the throughput in a point-to-point satellite network, which is the reference network for comparison purpose ...
Model-T: Rethinking the OS for terabit speeds
... First, we replace the common model of having few coarsegrained tasks with one built from many smaller processing steps. These operations are not independent. Each operation executes a single step in the network stack, such as IP defragmentation, TCP port routing or HTTP gzip decompression. For each ...
... First, we replace the common model of having few coarsegrained tasks with one built from many smaller processing steps. These operations are not independent. Each operation executes a single step in the network stack, such as IP defragmentation, TCP port routing or HTTP gzip decompression. For each ...
What do we use it for?
... Operates in a high-performance environment L is a packet size C is the capacity Does not need cooperation of the destination ...
... Operates in a high-performance environment L is a packet size C is the capacity Does not need cooperation of the destination ...
Document
... Operates in a high-performance environment L is a packet size C is the capacity Does not need cooperation of the destination ...
... Operates in a high-performance environment L is a packet size C is the capacity Does not need cooperation of the destination ...
STDMA-based Scheduling Algorithm for Concurrent Transmissions
... (STDMA) to improve the system throughput by allowing both non-interfering and interfering links to transmit concurrently, considering the high propagation loss at mmWave band and the utilization of directional antenna. Concurrent transmission scheduling in mmWave networks is formulated as an optimiz ...
... (STDMA) to improve the system throughput by allowing both non-interfering and interfering links to transmit concurrently, considering the high propagation loss at mmWave band and the utilization of directional antenna. Concurrent transmission scheduling in mmWave networks is formulated as an optimiz ...
paper
... to the configurations summarized in Table 4. Note that a single thread (Np = 1) is implemented, and a single redundancy round (Nk = 1) of Nm packets is transmitted immediately (Tr = 0) after the block. For each PHY setting and reliability configuration, two transmission trials are conducted. First, ...
... to the configurations summarized in Table 4. Note that a single thread (Np = 1) is implemented, and a single redundancy round (Nk = 1) of Nm packets is transmitted immediately (Tr = 0) after the block. For each PHY setting and reliability configuration, two transmission trials are conducted. First, ...
Improving VPN Performance over Multiple Access Links Larry Roberts
... previous research [2], [3], [4] has shown that inverse multiplexing a single TCP connection over heterogeneous links to obtain aggregated bandwidth is difficult; one can naively attempt to combine the bandwidths of 2 different links and realize even less bandwidth than the bandwidth of the slower of ...
... previous research [2], [3], [4] has shown that inverse multiplexing a single TCP connection over heterogeneous links to obtain aggregated bandwidth is difficult; one can naively attempt to combine the bandwidths of 2 different links and realize even less bandwidth than the bandwidth of the slower of ...
A Scheme for a Guaranteed Minimum Throughput Service
... Internet traffic is currently dominated by TCP connections carrying files generated by applications such as the web, ftp, or peer-to-peer file sharing [1]. The users of these applications expect no errors in the file transfer and the best possible response time. The source breaks up the file and sen ...
... Internet traffic is currently dominated by TCP connections carrying files generated by applications such as the web, ftp, or peer-to-peer file sharing [1]. The users of these applications expect no errors in the file transfer and the best possible response time. The source breaks up the file and sen ...
Evaluating the impact of RTS-CTS in OLPC`s XOs` Mesh Networks
... Frames transmitted at lower rates have higher probability to succeed but their associated metric is higher (worse). So, if a choice exists, the protocol tends to select the higher throughput path. However, the choice for higher performance links must take the number of hops into account. In terms of ...
... Frames transmitted at lower rates have higher probability to succeed but their associated metric is higher (worse). So, if a choice exists, the protocol tends to select the higher throughput path. However, the choice for higher performance links must take the number of hops into account. In terms of ...
Sep 2008 doc: 15-08-0631-00-004e-Distitbuted
... As the system becomes busier with a larger number of competitors attempting to push the system to the limits of its throughput capacity, a new analysis of the channel access method is required This must address the assignment of the backoff variable as well as limits placed on the number of Backoffs ...
... As the system becomes busier with a larger number of competitors attempting to push the system to the limits of its throughput capacity, a new analysis of the channel access method is required This must address the assignment of the backoff variable as well as limits placed on the number of Backoffs ...
Wire-Speed Total Order
... we identified the appropriate combination of the window size and the number of aggregated ACKs to achieve maximum throughput. The specific implementation of the flow control mechanism presented in this paper allows overall performance to converge with the receiving limit of the PCI bus. B. Optimizat ...
... we identified the appropriate combination of the window size and the number of aggregated ACKs to achieve maximum throughput. The specific implementation of the flow control mechanism presented in this paper allows overall performance to converge with the receiving limit of the PCI bus. B. Optimizat ...
Vertical handover criteria and algorithm in IEEE 802.11 and 802.16
... the connection is transferred between two base stations using the same access technology: the signal strength is the common metric used to predict the connection loss and to find the best neighboring cell to associate to. The notion of vertical handover was introduced with the development of differe ...
... the connection is transferred between two base stations using the same access technology: the signal strength is the common metric used to predict the connection loss and to find the best neighboring cell to associate to. The notion of vertical handover was introduced with the development of differe ...