COS 318: Operating Systems Overview Kai Li and Andy Bavier
... Examples that are not provided at user level System calls: file open, close, read and write l Control the CPU so that users won’t get stuck by running l ...
... Examples that are not provided at user level System calls: file open, close, read and write l Control the CPU so that users won’t get stuck by running l ...
OS Components and Structure
... directly for long-term storage. The file system provides logical objects and logical operations on those objects. A file is the basic long-term storage entity: a file is a named collection of persistent information that can be read or written. The file system supports directories -- special files th ...
... directly for long-term storage. The file system provides logical objects and logical operations on those objects. A file is the basic long-term storage entity: a file is a named collection of persistent information that can be read or written. The file system supports directories -- special files th ...
Chapter - 5th Semester Notes
... – Keep track of and record which users use how much and what kinds of computer resources for account billing or for accumulating usage ...
... – Keep track of and record which users use how much and what kinds of computer resources for account billing or for accumulating usage ...
I. Course code and Title OPERATING SYSTEM CONCEPTS II
... Management Hardware, Memory Management Techniques, Working Sets and Thrashing, Caching; Security and Protection: Overview of System Security, Policy/Mechanism Separation, Security Methods and Devices Protection, Access Control and Authentication, Backups, File Systems; I/O Management; Disk Manageme ...
... Management Hardware, Memory Management Techniques, Working Sets and Thrashing, Caching; Security and Protection: Overview of System Security, Policy/Mechanism Separation, Security Methods and Devices Protection, Access Control and Authentication, Backups, File Systems; I/O Management; Disk Manageme ...
Sec (3.2)
... the illusion of additional memory space by rotating programs and data backs and forth between main memory and mass storage (a technique called paging) Virtual memory: the large memory space created by the paging ...
... the illusion of additional memory space by rotating programs and data backs and forth between main memory and mass storage (a technique called paging) Virtual memory: the large memory space created by the paging ...
Operating System Overview
... • Using multiprogramming to handle multiple interactive jobs • Processor’s time is shared among multiple users • Multiple users simultaneously access the system through terminals ...
... • Using multiprogramming to handle multiple interactive jobs • Processor’s time is shared among multiple users • Multiple users simultaneously access the system through terminals ...
Operating Systems
... It provides security by supporting access control and ownership privileges, meaning you can set permission for groups or individual users to access certain files. NTFS supports compression of individual files and folders which can be read and written to while they are ...
... It provides security by supporting access control and ownership privileges, meaning you can set permission for groups or individual users to access certain files. NTFS supports compression of individual files and folders which can be read and written to while they are ...
2. OS Components
... Protection & Security refer to a mechanism for controlling access by programs, processes, or users to both system and user resources The protection mechanism: When several separate processes execute concurrently, it should not be ...
... Protection & Security refer to a mechanism for controlling access by programs, processes, or users to both system and user resources The protection mechanism: When several separate processes execute concurrently, it should not be ...
dasan.sejong.ac.kr
... user no longer has direct access to processor job is submitted to computer operator who batches them together and places them on an input device program branches back to the monitor when finished ...
... user no longer has direct access to processor job is submitted to computer operator who batches them together and places them on an input device program branches back to the monitor when finished ...
Structure of Operating Systems
... • In the idle loop: – OS executes an infinite loop (UNIX) – OS performs some system management & profiling – OS halts the processor and enter in low-power mode (notebooks) – OS computes some function (DEC’s VMS on VAX computed Pi) • OS wakes up on: – interrupts from hardware devices – traps from use ...
... • In the idle loop: – OS executes an infinite loop (UNIX) – OS performs some system management & profiling – OS halts the processor and enter in low-power mode (notebooks) – OS computes some function (DEC’s VMS on VAX computed Pi) • OS wakes up on: – interrupts from hardware devices – traps from use ...
Lecture 1: Operating System Services What is an Operating System?
... and the O.S. takes control of the computer system again, avoiding thus, that none program monopolizes the CPU. ...
... and the O.S. takes control of the computer system again, avoiding thus, that none program monopolizes the CPU. ...
Cindy - Anatomy of a Window
... Basic units of file management are files and folders or directories Memory management deals with temporary storage or use of applications and data The OS controls where applications and data are stored in memory ...
... Basic units of file management are files and folders or directories Memory management deals with temporary storage or use of applications and data The OS controls where applications and data are stored in memory ...
Operating Systems - Home - KSU Faculty Member websites
... • Systems generally first distinguish among users, to determine who can do what – User identities (user IDs, security IDs) include name and associated number, one per user – User ID then associated with all files, processes of that user to determine access control – Group identifier (group ID) allow ...
... • Systems generally first distinguish among users, to determine who can do what – User identities (user IDs, security IDs) include name and associated number, one per user – User ID then associated with all files, processes of that user to determine access control – Group identifier (group ID) allow ...
General overview of the System
... • Operating system is a software that enables all the programs we use. • Examples – Windows, Linux, Unix, etc. ...
... • Operating system is a software that enables all the programs we use. • Examples – Windows, Linux, Unix, etc. ...
Traditional UNIX kernels
... • Real Time: Operating Systems for information that needs to be updated in real time • Embedded Systems: Systems that are found within another System ...
... • Real Time: Operating Systems for information that needs to be updated in real time • Embedded Systems: Systems that are found within another System ...
VMS-Spr-2001-sect-1-group
... • A register called the processor status long word (PSL) contains information about the process • information contained includes the current access mode, the current interrupt priority level (IPL), the stack alignment, and several reserved fields ...
... • A register called the processor status long word (PSL) contains information about the process • information contained includes the current access mode, the current interrupt priority level (IPL), the stack alignment, and several reserved fields ...
Slides. - Department of Computer Science and Information Systems
... 2. Processes and threads 3. Deadlock 4. Memory management 5. Input/output 6. File systems 7. Multimedia operating systems 8. Multiple processor systems 9. Security UNIX and Windows are to be used as running case studies. ...
... 2. Processes and threads 3. Deadlock 4. Memory management 5. Input/output 6. File systems 7. Multimedia operating systems 8. Multiple processor systems 9. Security UNIX and Windows are to be used as running case studies. ...
Memory Management
... Decide how much memory space to allocate each process Decide when a process should be removed from memory ...
... Decide how much memory space to allocate each process Decide when a process should be removed from memory ...
talk
... – What algorithms are typically used • We will do this through reading, lectures, and a project. • You will need to keep up with all three of these. ...
... – What algorithms are typically used • We will do this through reading, lectures, and a project. • You will need to keep up with all three of these. ...
Operating System Services
... Resource allocation - When multiple users or multiple jobs running concurrently, resources must be allocated to each of them Many types of resources - Some (such as CPU cycles, main memory, and file storage) may have special allocation code, others (such as I/O devices) may have general request ...
... Resource allocation - When multiple users or multiple jobs running concurrently, resources must be allocated to each of them Many types of resources - Some (such as CPU cycles, main memory, and file storage) may have special allocation code, others (such as I/O devices) may have general request ...
Computers
... New/Ready/Wait/etc Address of next instruction Start and end location of process in memory Register contents I/O requests and assignments ...
... New/Ready/Wait/etc Address of next instruction Start and end location of process in memory Register contents I/O requests and assignments ...
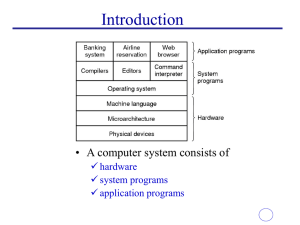
Chapter 1 - Introduction to Operating Systems
... Acts as an interface between user and system Organised set of programs Schedule tasks and it manage storage Control and manage computer resources Making computer system convenient to use in effective manner. ...
... Acts as an interface between user and system Organised set of programs Schedule tasks and it manage storage Control and manage computer resources Making computer system convenient to use in effective manner. ...
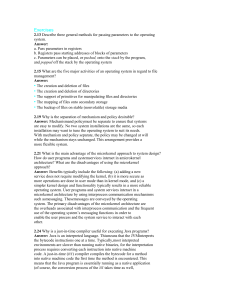
Exercises
... Answer: Mechanismand policymust be separate to ensure that systems are easy to modify. No two system installations are the same, so each installation may want to tune the operating system to suit its needs. With mechanism and policy separate, the policy may be changed at will while the mechanism sta ...
... Answer: Mechanismand policymust be separate to ensure that systems are easy to modify. No two system installations are the same, so each installation may want to tune the operating system to suit its needs. With mechanism and policy separate, the policy may be changed at will while the mechanism sta ...
OS 2200

OS 2200 is the operating system for the Unisys ClearPath Dorado family of mainframe systems. The operating system kernel of OS 2200 is a lineal descendant of Exec 8 for the UNIVAC 1108. Documentation and other information on current and past Unisys systems can be found on the Unisys public support website.See Unisys 2200 Series system architecture for a description of the machine architecture and its relationship to the OS 2200 operating system.