PPT - CSE Home
... • shell: An interactive program that uses user input to manage the execution of other programs. A command processor, typically runs in a text window. User types commands, the shell runs the commands Several different shell programs exist: • bash : the default shell program on most Linux/Unix s ...
... • shell: An interactive program that uses user input to manage the execution of other programs. A command processor, typically runs in a text window. User types commands, the shell runs the commands Several different shell programs exist: • bash : the default shell program on most Linux/Unix s ...
Page table
... bytes as it is in some operating systems (e.g., Unix) Rather, files are structured objects comprised of typed attributes Some types of attributes ◦ Conventional data of a file ◦ Standard attributes: name, creation time, security descriptor ...
... bytes as it is in some operating systems (e.g., Unix) Rather, files are structured objects comprised of typed attributes Some types of attributes ◦ Conventional data of a file ◦ Standard attributes: name, creation time, security descriptor ...
Lecture 22 File-System Interface
... collection of similar records treated as a single entity have unique file names may restrict access ...
... collection of similar records treated as a single entity have unique file names may restrict access ...
Linux - the most important … Linux: SHELL ~$ command –options
... history – list sheel command history, to select from the list type (!number) whereis, whatis, locate, which, type – Locate / display a command info sort - Sorts standard input then outputs the sorted result on standard output. uniq - Given a sorted stream of data from standard input, it removes dupl ...
... history – list sheel command history, to select from the list type (!number) whereis, whatis, locate, which, type – Locate / display a command info sort - Sorts standard input then outputs the sorted result on standard output. uniq - Given a sorted stream of data from standard input, it removes dupl ...
Part IV: Longer Answer: Use your knowledge of operating systems to
... 5. _______________ is a situation where one or more processes is waiting for an event that will never occur and can only be caused by another of the waiting processes. 6. _______________ is a situation where only one process may access a resource at a time. 7. _______________ is a UNIX system call t ...
... 5. _______________ is a situation where one or more processes is waiting for an event that will never occur and can only be caused by another of the waiting processes. 6. _______________ is a situation where only one process may access a resource at a time. 7. _______________ is a UNIX system call t ...
continued…
... When OS loads from hard drive, BIOS first executes the MBR, which executes OS boot record, which, for Windows 9x, attempts to find Io.sys on hard drive Io.sys, which uses Msdos.sys, and Command.com, form the core of real-mode Windows 9x • All three are necessary to boot to a command prompt Autoexec. ...
... When OS loads from hard drive, BIOS first executes the MBR, which executes OS boot record, which, for Windows 9x, attempts to find Io.sys on hard drive Io.sys, which uses Msdos.sys, and Command.com, form the core of real-mode Windows 9x • All three are necessary to boot to a command prompt Autoexec. ...
5-1 note
... different times to avoid crashing. • Scheduled processing tasks include – software updates – virus scanning – backup of data to other locations ...
... different times to avoid crashing. • Scheduled processing tasks include – software updates – virus scanning – backup of data to other locations ...
Functions of the operating systems
... 1. allows the user to organize their data on secondary storage into files & folders 2. also manages the use of main memory by splitting main memory into two parts (user area, system area). 3. Time sharing: operating system can allow more than one user to work on the same computer, and run more than ...
... 1. allows the user to organize their data on secondary storage into files & folders 2. also manages the use of main memory by splitting main memory into two parts (user area, system area). 3. Time sharing: operating system can allow more than one user to work on the same computer, and run more than ...
Operating System - Linux - Home Pages of People@DU
... system starts and runs till the session gets terminated Different from BIOS which is hardware dependent. Kernel is software dependent ...
... system starts and runs till the session gets terminated Different from BIOS which is hardware dependent. Kernel is software dependent ...
Formatting and Partitioning Hard Drives, and DOS
... Manufacturers now handle virtually all lowlevel formatting of hard disks End users should rarely ever perform low-level formatting of an IDE or ATA hard drive. ...
... Manufacturers now handle virtually all lowlevel formatting of hard disks End users should rarely ever perform low-level formatting of an IDE or ATA hard drive. ...
Memory Management
... Disks (secondary storage) provide longterm storage, but are awkward to use directly ...
... Disks (secondary storage) provide longterm storage, but are awkward to use directly ...
OPERATING SYSTEM FUNCTIONS
... • get/set time or date • get/set system data • get/set process, file, or device attributes Communication. • create, delete communication connection • send, receive messages • transfer status information • attach or detach remote devices ...
... • get/set time or date • get/set system data • get/set process, file, or device attributes Communication. • create, delete communication connection • send, receive messages • transfer status information • attach or detach remote devices ...
Implementation of Log Based File Systems on Open Source
... large-scale Cray supercomputers to the booming market of Palm Pilots, each type of computer has its own set of advantages and disadvantages. Likewise, computing components, both physical components and software components, have similar sets of advantages and disadvantages One area of research is the ...
... large-scale Cray supercomputers to the booming market of Palm Pilots, each type of computer has its own set of advantages and disadvantages. Likewise, computing components, both physical components and software components, have similar sets of advantages and disadvantages One area of research is the ...
PDF
... – File and device I/O are as similar as possible – File and device names have the same syntax and meaning, can pass as arguments to programs – Same protection mechanism as regular files ...
... – File and device I/O are as similar as possible – File and device names have the same syntax and meaning, can pass as arguments to programs – Same protection mechanism as regular files ...
PPTX
... rooted tree current working directory back link to parent multiple links to ordinary files ...
... rooted tree current working directory back link to parent multiple links to ordinary files ...
PPTX
... rooted tree current working directory back link to parent multiple links to ordinary files ...
... rooted tree current working directory back link to parent multiple links to ordinary files ...
Traditional UNIX kernels
... • man provides online documentation on nearly every standard command and configuration file. • Optional Syntax: man -k keyword • man man for more details ...
... • man provides online documentation on nearly every standard command and configuration file. • Optional Syntax: man -k keyword • man man for more details ...
DOS (“Disk Operating System”)
... print lines matching a pattern kills a running program creates a link between two files; try ln –s list contents of directory; try ls –lisa show library calls made WWW/News/Mail browser shows current processes set/get the value of shell variables transfer files securely to/from a remote machine exec ...
... print lines matching a pattern kills a running program creates a link between two files; try ln –s list contents of directory; try ls –lisa show library calls made WWW/News/Mail browser shows current processes set/get the value of shell variables transfer files securely to/from a remote machine exec ...
Operating Systems (OS)
... e.g. a batch job, the shell of a login session, a program run The execution of processes is controlled by the kernel and is interlaced – this part of the kernel is known as the despatcher or low-level scheduler when a process ends, or uses up its scheduled time, or cannot be continued because an int ...
... e.g. a batch job, the shell of a login session, a program run The execution of processes is controlled by the kernel and is interlaced – this part of the kernel is known as the despatcher or low-level scheduler when a process ends, or uses up its scheduled time, or cannot be continued because an int ...
Chapter 4 - Killarney Secondary School
... All files start at the root directory All other directories branch off of the root directory Must know the path to find files in DOS Paths are typed in either relatively or absolute ...
... All files start at the root directory All other directories branch off of the root directory Must know the path to find files in DOS Paths are typed in either relatively or absolute ...
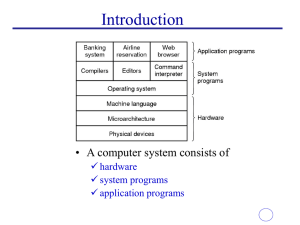
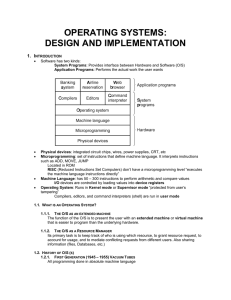
OPERATING SYSTEMS:
... ADDRESS SPACE: memory locations from 0 – maximum, which the process can read and write. It contains: the executable program, the program’s data, and its stack Set of registers, including the program counter, stack pointer, and H/W registers Process Table: An array of structures, one for each current ...
... ADDRESS SPACE: memory locations from 0 – maximum, which the process can read and write. It contains: the executable program, the program’s data, and its stack Set of registers, including the program counter, stack pointer, and H/W registers Process Table: An array of structures, one for each current ...
Operating System - GCG-42
... Concept of Path: Every file can be specified by enumerating all of the directories between the root and it, separated by the backslash '\' character, and appending the file name to the end. ...
... Concept of Path: Every file can be specified by enumerating all of the directories between the root and it, separated by the backslash '\' character, and appending the file name to the end. ...
DOS - InfoShare.tk
... The DOS kernel initializes its tables and sets up various work areas. It sets up the interrupt vector table. It then loads and executes the device drivers. These driver function determine device status, perform necessary hardware initialization and set up vectors for any external hardware interrupts ...
... The DOS kernel initializes its tables and sets up various work areas. It sets up the interrupt vector table. It then loads and executes the device drivers. These driver function determine device status, perform necessary hardware initialization and set up vectors for any external hardware interrupts ...