SCTP - UMBC
... – UDP • No Reliability • Absence of congestion control • Absence of flow control Nimish Vartak ...
... – UDP • No Reliability • Absence of congestion control • Absence of flow control Nimish Vartak ...
ECE 260B - CSE241A VLSI Digital Circuits
... When measured in terms of number of inputs, there are functions whose size is exponential in sum of products representation, but polynomial in factored form. ...
... When measured in terms of number of inputs, there are functions whose size is exponential in sum of products representation, but polynomial in factored form. ...
IPv6 Lab
... Simply restart the dovecot demon and test your IPv6 IMAP or POP3 server by using and IPv6 compliant MUA. There are still few IPv6 enabled SMTP, POP3 and IMAP clients. Sylpheed is a client with a graphical interface under Unix & windows that supports all these features since release 0.4.4. More inf ...
... Simply restart the dovecot demon and test your IPv6 IMAP or POP3 server by using and IPv6 compliant MUA. There are still few IPv6 enabled SMTP, POP3 and IMAP clients. Sylpheed is a client with a graphical interface under Unix & windows that supports all these features since release 0.4.4. More inf ...
Multi-Threaded Programming in Java
... IT managers can sign servlets for use in their organization ISPs can allow users to run servlets ...
... IT managers can sign servlets for use in their organization ISPs can allow users to run servlets ...
Mobile Communications
... low power for battery use no special permissions or licenses needed to use the LAN robust transmission technology simplified spontaneous cooperation at meetings easy to use for everyone, simple management protection of investment in wired networks security (no one should be able to read my data), pr ...
... low power for battery use no special permissions or licenses needed to use the LAN robust transmission technology simplified spontaneous cooperation at meetings easy to use for everyone, simple management protection of investment in wired networks security (no one should be able to read my data), pr ...
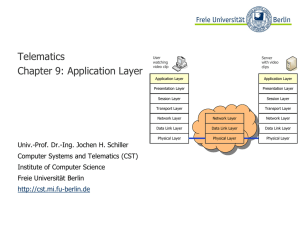
Application Layer - Freie Universität Berlin
... ● The reverse tree represents the Domain Name Space ● The depth of the tree is limited to 127 levels ● Each label can have up to 63 characters ● The whole domain name can have up to 255 characters ● A label of the length 0 is reserved for the root node (“”) ● The Fully Qualified Domain Name (FQDN) i ...
... ● The reverse tree represents the Domain Name Space ● The depth of the tree is limited to 127 levels ● Each label can have up to 63 characters ● The whole domain name can have up to 255 characters ● A label of the length 0 is reserved for the root node (“”) ● The Fully Qualified Domain Name (FQDN) i ...
슬라이드 제목 없음
... In Slide 47 we want to send data from a node with network address A and physical address 10, located on one LAN, to a node with a network address P and physical address 95, located on another LAN. Because the two devices are located on different networks, we cannot use link addresses only; the link ...
... In Slide 47 we want to send data from a node with network address A and physical address 10, located on one LAN, to a node with a network address P and physical address 95, located on another LAN. Because the two devices are located on different networks, we cannot use link addresses only; the link ...
D11 - State of Interoperability
... The application of standards in these tools is quite rare. Many tools rely on proprietary command line interfaces or GUIs for control and also produce proprietary data output in human readable ASCII format. A lot of tools also lack the ability for remote control and data export. Thus interoperation ...
... The application of standards in these tools is quite rare. Many tools rely on proprietary command line interfaces or GUIs for control and also produce proprietary data output in human readable ASCII format. A lot of tools also lack the ability for remote control and data export. Thus interoperation ...
PPT - Mining of Massive Datasets
... Note to other teachers and users of these slides: We would be delighted if you found this our material useful in giving your own lectures. Feel free to use these slides verbatim, or to modify them to fit your own needs. If you make use of a significant portion of these slides in your own lecture, pl ...
... Note to other teachers and users of these slides: We would be delighted if you found this our material useful in giving your own lectures. Feel free to use these slides verbatim, or to modify them to fit your own needs. If you make use of a significant portion of these slides in your own lecture, pl ...
SharePoint 2010: Medium Farm - Performance Study __ Final
... SharePoint deployment. Some of these services, or sets of services, comprise predefined roles and must be configured within the solution. Other services and components are optional, but they provide additional features and functionality that are often desirable. These optional components may include ...
... SharePoint deployment. Some of these services, or sets of services, comprise predefined roles and must be configured within the solution. Other services and components are optional, but they provide additional features and functionality that are often desirable. These optional components may include ...
TR-M2M-0009v0.7.0 oneM2M Protocol Analysis
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
Protocol Analysis
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
Slide 1
... • The IP SLA UDP jitter operation was primarily designed to diagnose network suitability for real-time traffic applications such as voice over IP (VoIP), video over IP, or real-time conferencing. • Jitter means inter-packet delay variance. When multiple packets are sent consecutively from source to ...
... • The IP SLA UDP jitter operation was primarily designed to diagnose network suitability for real-time traffic applications such as voice over IP (VoIP), video over IP, or real-time conferencing. • Jitter means inter-packet delay variance. When multiple packets are sent consecutively from source to ...
`Talk` Applications in C and Java
... done by binding it to a local network adapter. This means that a local address and port must be selected. Most servers are expected to be operating on the same address and port all of the time, in which case the socket may be bound to these and unless the binding process fails the clients will know ...
... done by binding it to a local network adapter. This means that a local address and port must be selected. Most servers are expected to be operating on the same address and port all of the time, in which case the socket may be bound to these and unless the binding process fails the clients will know ...
Oreifej-Stricklan
... criteria that include ranges of values to match or sets of values to match, cannot be expressed with a single ServiceTemplate ...
... criteria that include ranges of values to match or sets of values to match, cannot be expressed with a single ServiceTemplate ...
9.4.2 CSMA/CD – The Process
... Ethernet uses Carrier Sense Multiple Access with Collision Detection (CSMA/CD) to detect and handle collisions and manage the resumption of communications. A device can then determine when it can transmit. When a device detects that no other computer is sending a frame, or carrier signal, the de ...
... Ethernet uses Carrier Sense Multiple Access with Collision Detection (CSMA/CD) to detect and handle collisions and manage the resumption of communications. A device can then determine when it can transmit. When a device detects that no other computer is sending a frame, or carrier signal, the de ...
Resource-Freeing Attacks: Improve Your Cloud Performance (at Your Neighbor’s Expense)
... interference on a single contended resource, termed the target resource. For example, a disk-bound beneficiary may suffer from competing disk accesses from victim VMs. Conceptual framework. The beneficiary and the helper work together to change the victim’s resource consumption in a manner that free ...
... interference on a single contended resource, termed the target resource. For example, a disk-bound beneficiary may suffer from competing disk accesses from victim VMs. Conceptual framework. The beneficiary and the helper work together to change the victim’s resource consumption in a manner that free ...
Integrating Cisco Press Resources into the Academy Classroom
... • Primary duty of the transport layer (OSI Layer 4), is to take data from the application process on one computer and deliver the data to the correct application process on another computer • Both TCP and UDP identify data from upper-layer applications based on port number • UDP provides only basic ...
... • Primary duty of the transport layer (OSI Layer 4), is to take data from the application process on one computer and deliver the data to the correct application process on another computer • Both TCP and UDP identify data from upper-layer applications based on port number • UDP provides only basic ...
oneM2M-TR-0009-Protocol_Analysis-V0_4_0
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
CCNA Exploration 1 Chapter 03
... Web browsers are the client applications our computers use to connect to the World Wide Web and access resources stored on a web server. As with most server processes, the web server runs as a background service and makes different types of files available Browsers can interpret and present many ...
... Web browsers are the client applications our computers use to connect to the World Wide Web and access resources stored on a web server. As with most server processes, the web server runs as a background service and makes different types of files available Browsers can interpret and present many ...
Universal Plug and Play - Dead simple or simply
... Devices can be controlled by sending SOAP requests to the “control URL”. There is no authentication/authorization in UPnP, being on the LAN is enough to do this. No administrative privileges needed: any user can do this. ...
... Devices can be controlled by sending SOAP requests to the “control URL”. There is no authentication/authorization in UPnP, being on the LAN is enough to do this. No administrative privileges needed: any user can do this. ...
Network Node v1.1 Protocol Document
... functionalities that will not immediately be utilized but are expected to become paramount as the Exchange Network evolves during its initial implementation. For example, the documents discuss and describe UDDI and other Registries as integral parts of the Network. Their use is implicit in the Proto ...
... functionalities that will not immediately be utilized but are expected to become paramount as the Exchange Network evolves during its initial implementation. For example, the documents discuss and describe UDDI and other Registries as integral parts of the Network. Their use is implicit in the Proto ...
SEMI Object Model Extensions ()
... All object messages are sent between two nodes to execute service transactions. All service transactions are associated with “request” services and consist of a request message and a corresponding response message. Some service transactions are associated with “notify” services and consist of a sing ...
... All object messages are sent between two nodes to execute service transactions. All service transactions are associated with “request” services and consist of a request message and a corresponding response message. Some service transactions are associated with “notify” services and consist of a sing ...
Hypertext Transfer Protocol

The Hypertext Transfer Protocol (HTTP) is an application protocol for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web.Hypertext is structured text that uses logical links (hyperlinks) between nodes containing text. HTTP is the protocol to exchange or transfer hypertext.The standards development of HTTP was coordinated by the Internet Engineering Task Force (IETF) and the World Wide Web Consortium (W3C), culminating in the publication of a series of Requests for Comments (RFCs). The first definition of HTTP/1.1, the version of HTTP in common use, occurred in RFC 2068 in 1997, although this was obsoleted by RFC 2616 in 1999.