A Description Logic with Transitive and Inverse Roles and Role
... Like ALCHR+ , ALCHI R+ and ALCHFI R+ also allow for the internalisation of general concept inclusion axioms using a universal role: a transitive role that subsumes all other roles in the terminology [17]. This technique allows subsumption and satisfiability with respect to (possibly cyclic) general ...
... Like ALCHR+ , ALCHI R+ and ALCHFI R+ also allow for the internalisation of general concept inclusion axioms using a universal role: a transitive role that subsumes all other roles in the terminology [17]. This technique allows subsumption and satisfiability with respect to (possibly cyclic) general ...
Comparative Study of C5.0 and CART
... our dataset is still a complex question to answer. In case of excluding them, CART’s tree model has a less predictive power than C5.0’s. But in case of including them into our dataset, which of the handling missing data methods we should use. In this paper, I have introduced you the two methods: sur ...
... our dataset is still a complex question to answer. In case of excluding them, CART’s tree model has a less predictive power than C5.0’s. But in case of including them into our dataset, which of the handling missing data methods we should use. In this paper, I have introduced you the two methods: sur ...
pdf file
... Two problems occurring often in such classification tasks in real-world domains are underspecification and overspecification. Underspecification occurs when the observations are sufficient to exclude some of the values of attributes, but insufficient to determine unique values for each of the attrib ...
... Two problems occurring often in such classification tasks in real-world domains are underspecification and overspecification. Underspecification occurs when the observations are sufficient to exclude some of the values of attributes, but insufficient to determine unique values for each of the attrib ...
Lecture Notes in Computer Science
... Fig. 1 illustrates what we are trying to accomplish; it depicts the distances of 13 examples, 5 of which belong to a class that is identified by a square and 8 belong to a different class that is identified by a circle. When using the initial distance function dinit we cannot observe too much cluste ...
... Fig. 1 illustrates what we are trying to accomplish; it depicts the distances of 13 examples, 5 of which belong to a class that is identified by a square and 8 belong to a different class that is identified by a circle. When using the initial distance function dinit we cannot observe too much cluste ...
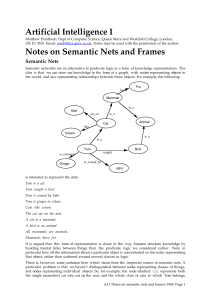
Artificial Intelligence I Notes on Semantic Nets and Frames
... The fact that various natural languages make this case distinction can be used to support using it in artificial knowledge representation. The “case for case” is associated with the linguist Charles Fillmore whose work has been influential among AI workers in knowledge representation. The idea is th ...
... The fact that various natural languages make this case distinction can be used to support using it in artificial knowledge representation. The “case for case” is associated with the linguist Charles Fillmore whose work has been influential among AI workers in knowledge representation. The idea is th ...
Sample pages 2 PDF
... In section 2.2 we developed a method to produce complete sublattices of a given complete lattice. If R C A x B is a relation between two sets A and B and if (p, L) is the Galois connection induced by R, then the fixed points of the closure operators p~ and ~p form two complete lattices which are dua ...
... In section 2.2 we developed a method to produce complete sublattices of a given complete lattice. If R C A x B is a relation between two sets A and B and if (p, L) is the Galois connection induced by R, then the fixed points of the closure operators p~ and ~p form two complete lattices which are dua ...
Creativity, Cognitive Mechanisms, and Logic
... the input spaces (cf. Figure 4). One of the famous blending examples is Goguen’s H OUSE B OAT and B OAT H OUSE blends, which result, among others, from blending the two input spaces representing the words H OUSE and B OAT (cf. [9]). Only few accounts have been proposed formalizing CB or its principl ...
... the input spaces (cf. Figure 4). One of the famous blending examples is Goguen’s H OUSE B OAT and B OAT H OUSE blends, which result, among others, from blending the two input spaces representing the words H OUSE and B OAT (cf. [9]). Only few accounts have been proposed formalizing CB or its principl ...
INTRODUCTION - Department of Computer Science
... patterns and characteristics in the problem domain. To remain on the competitive edge, there is now an increasing demand for techniques to extract these hidden patterns from large databases. Utilization of such knowledge can substantially increase the revenue of a company, and can save money. The ex ...
... patterns and characteristics in the problem domain. To remain on the competitive edge, there is now an increasing demand for techniques to extract these hidden patterns from large databases. Utilization of such knowledge can substantially increase the revenue of a company, and can save money. The ex ...
Semantic Networks: Visualizations of Knowledge
... where the target of the mapping is some formal construct that uses mathematical, or at least, abstract ideas. The formal construct is often mant to capture the nature of the real world in some way, but it is not, in fact the real world.Typically this is done for symbolic systems such as formal logic ...
... where the target of the mapping is some formal construct that uses mathematical, or at least, abstract ideas. The formal construct is often mant to capture the nature of the real world in some way, but it is not, in fact the real world.Typically this is done for symbolic systems such as formal logic ...
Improving the scalability of rule
... alternatives also exist. Some method apply various kinds of windowing techniques (Bacardit et al, 2004). That is, they use only a subset of the training examples to perform the fitness computations of the individuals. The strategy to choose the training subset, the frequency of changing them, etc. d ...
... alternatives also exist. Some method apply various kinds of windowing techniques (Bacardit et al, 2004). That is, they use only a subset of the training examples to perform the fitness computations of the individuals. The strategy to choose the training subset, the frequency of changing them, etc. d ...
Does the Human Brain Have Algorithms? (PDF Available)
... building blocks algorithms can include any combination of steps and rules including If-Then rules. A very simple building block algorithm could consist of a single If-Then rule. An example is given in the experiments of Jordan and Brannon [4] where the brains of 7 month old infants were able to carr ...
... building blocks algorithms can include any combination of steps and rules including If-Then rules. A very simple building block algorithm could consist of a single If-Then rule. An example is given in the experiments of Jordan and Brannon [4] where the brains of 7 month old infants were able to carr ...
ROUGH SETS DETERMINED BY QUASIORDERS 1. Introduction
... Later this result was improved by Comer [3] by showing that in fact RS is a double Stone lattice. Finally, in [4] Gehrke and Walker described the structure of RS precisely. They showed that RS is isomorphic to 2I ×3J , where 2 and 3 are the chains of two and three elements, I is the set of singleton ...
... Later this result was improved by Comer [3] by showing that in fact RS is a double Stone lattice. Finally, in [4] Gehrke and Walker described the structure of RS precisely. They showed that RS is isomorphic to 2I ×3J , where 2 and 3 are the chains of two and three elements, I is the set of singleton ...
A First Study of Fuzzy Cognitive Maps Learning Using Particle
... state, i.e. all output concepts are bounded within the desired regions. The objective function F suits straightforwardly the problem, however, it is non–differentiable and, thus, gradient–based methods are not applicable for its minimization. On the other hand, in the proposed approach, PSO is used ...
... state, i.e. all output concepts are bounded within the desired regions. The objective function F suits straightforwardly the problem, however, it is non–differentiable and, thus, gradient–based methods are not applicable for its minimization. On the other hand, in the proposed approach, PSO is used ...
Artificial Intelligence (AI): Trying to Get Computers to Think Like Us
... AI is a field older than most realize – the term was coined in the mid 1950s. The field is comprised of many subfields but the main focus is on building intelligent entities. In order to achieve this goal many subcomponents need to be built, including methods for assisting computers to think like hu ...
... AI is a field older than most realize – the term was coined in the mid 1950s. The field is comprised of many subfields but the main focus is on building intelligent entities. In order to achieve this goal many subcomponents need to be built, including methods for assisting computers to think like hu ...
Artificial intelligence tools for software engineering
... Transactions on Information and Communications Technologies vol 2, © 1993 WIT Press, www.witpress.com, ISSN 1743-3517 ...
... Transactions on Information and Communications Technologies vol 2, © 1993 WIT Press, www.witpress.com, ISSN 1743-3517 ...
Bootstrapping Probabilistic Models of Qualitative
... objects segmented and category labelled in 3D. In this paper we focus on searching for objects on desks, so we require this data to be observations of desktop object configurations. This data must then be labelled with QSRs to indicate which observations should contribute to which learnt relational ...
... objects segmented and category labelled in 3D. In this paper we focus on searching for objects on desks, so we require this data to be observations of desktop object configurations. This data must then be labelled with QSRs to indicate which observations should contribute to which learnt relational ...
DU35687693
... theory and statistical mathematics, [12], pattern recognition knows in the present applications of which wide stretches from anthropology research to hardware and software projection, [1]. Pattern recognition theory is defined as representing the totality of rules, principles, methods and tools for ...
... theory and statistical mathematics, [12], pattern recognition knows in the present applications of which wide stretches from anthropology research to hardware and software projection, [1]. Pattern recognition theory is defined as representing the totality of rules, principles, methods and tools for ...
hierarchical intelligent simulation
... meaning to be specified by user-defined semantic functions that control the simulation. E.g., an unfinished design module is characterized by constraints regarding its interaction to other modules, resulting a model system, open to be interpreted, thus implemented, in different ways that derive from ...
... meaning to be specified by user-defined semantic functions that control the simulation. E.g., an unfinished design module is characterized by constraints regarding its interaction to other modules, resulting a model system, open to be interpreted, thus implemented, in different ways that derive from ...
Large-scale attribute selection using wrappers
... standard wrapper approach. [20] suggests that this holds for standard wrapper evaluation via cross-validation as well, as it asymptotically yields a constant improvement over a test set. However, performing an exhaustive search makes this algorithm intractable on most real-world data. A. Forward Se ...
... standard wrapper approach. [20] suggests that this holds for standard wrapper evaluation via cross-validation as well, as it asymptotically yields a constant improvement over a test set. However, performing an exhaustive search makes this algorithm intractable on most real-world data. A. Forward Se ...
Large-scale attribute selection using wrappers
... standard wrapper approach. [20] suggests that this holds for standard wrapper evaluation via cross-validation as well, as it asymptotically yields a constant improvement over a test set. However, performing an exhaustive search makes this algorithm intractable on most real-world data. A. Forward Se ...
... standard wrapper approach. [20] suggests that this holds for standard wrapper evaluation via cross-validation as well, as it asymptotically yields a constant improvement over a test set. However, performing an exhaustive search makes this algorithm intractable on most real-world data. A. Forward Se ...
Rough set approach to knowledge
... the core is the most important subset of attributes, for none of its elements can be removed without affecting the classification power of attributes. Complexity of computing all reducts in an information system is rather high. However, in many applications we do not need to compute all reducts, but ...
... the core is the most important subset of attributes, for none of its elements can be removed without affecting the classification power of attributes. Complexity of computing all reducts in an information system is rather high. However, in many applications we do not need to compute all reducts, but ...
Description Logics
... Race, and Dlp [67, 61, 98]) showed that tableau-based algorithms for expressive DLs lead to a good practical behavior of the system even on (some) large knowledge bases. In this phase, the relationship to modal logics [44, 104] and to decidable fragments of first-order logic was also studied in more ...
... Race, and Dlp [67, 61, 98]) showed that tableau-based algorithms for expressive DLs lead to a good practical behavior of the system even on (some) large knowledge bases. In this phase, the relationship to modal logics [44, 104] and to decidable fragments of first-order logic was also studied in more ...
1 HYBRID EXPERT SYSTEM OF ROUGH SET AND NEURAL
... this paper a new method for pre-processing data for neural network based on rough set has been developed and merged with neural expert system. The process consists of acquisition of data, formalization of decision tables, reduction of attributes, and binarization of input data [7, 15]. First decisio ...
... this paper a new method for pre-processing data for neural network based on rough set has been developed and merged with neural expert system. The process consists of acquisition of data, formalization of decision tables, reduction of attributes, and binarization of input data [7, 15]. First decisio ...
Category Theory: an abstract setting for analogy
... itself implies a use of comparison, as does ‘ratio’ and most other simple binary relations2 .) In the first of the two cases the transformations must preserve the attribute of distance between points, in the second they do not, so we get more ‘allowable transformations’ and a different geometry. The ...
... itself implies a use of comparison, as does ‘ratio’ and most other simple binary relations2 .) In the first of the two cases the transformations must preserve the attribute of distance between points, in the second they do not, so we get more ‘allowable transformations’ and a different geometry. The ...
On the Structure of Abstract Algebras
... lattice of the subalgebras of A. Expressions such as G(L(A)) and L(L(6(A))) are then self-explanatory. We shall also adopt the usual definitions J of isomorphism and homomorphism. We shall supplement these by saying that a (1, 1) correspondence between a lattice Land a lattice L is " dually jsomorph ...
... lattice of the subalgebras of A. Expressions such as G(L(A)) and L(L(6(A))) are then self-explanatory. We shall also adopt the usual definitions J of isomorphism and homomorphism. We shall supplement these by saying that a (1, 1) correspondence between a lattice Land a lattice L is " dually jsomorph ...