Slides
... Let inv be 0 <= i <= length && result = sum(array[j] for all j in 0..i-1); 1. inv is true right before the loop starts, i.e., length >= 0 && array.length = length && i = 0 && result = 0.0 ...
... Let inv be 0 <= i <= length && result = sum(array[j] for all j in 0..i-1); 1. inv is true right before the loop starts, i.e., length >= 0 && array.length = length && i = 0 && result = 0.0 ...
LEC01 - aiub study guide
... Initialization: it is true prior to the first iteration. Maintenance: if it is true before an iteration, then it is true after the iteration. Termination: when a loop terminates the invariant gives a useful property to show the correctness of the algorithm ...
... Initialization: it is true prior to the first iteration. Maintenance: if it is true before an iteration, then it is true after the iteration. Termination: when a loop terminates the invariant gives a useful property to show the correctness of the algorithm ...
Solution
... In the following, use either a direct proof (by giving values for c and n0 in the definition of big-Oh notation) or cite one of the rules given in the book or in the lecture slides. (a) Show that if f(n) is O(g(n)) and d(n) is O(h(n)), then f(n)+d(n) is O(g(n)+ h(n)). Solution Recall the de_nition o ...
... In the following, use either a direct proof (by giving values for c and n0 in the definition of big-Oh notation) or cite one of the rules given in the book or in the lecture slides. (a) Show that if f(n) is O(g(n)) and d(n) is O(h(n)), then f(n)+d(n) is O(g(n)+ h(n)). Solution Recall the de_nition o ...
Wavelength management in WDM rings to maximize the
... set of size k may force at most k compatible sets of an optimal k-set packing to be excluded from the solution, this algorithm has approximation ratio k for solving the k-set packing problem. Using different methods for computing k-set packings, we obtain different algorithms. When the maximum compa ...
... set of size k may force at most k compatible sets of an optimal k-set packing to be excluded from the solution, this algorithm has approximation ratio k for solving the k-set packing problem. Using different methods for computing k-set packings, we obtain different algorithms. When the maximum compa ...
Karp Algorithm
... capable of the exact solution of ;-city traveling-salesman problems, where / is specified by the user of the algorithm. We show that the execution time of Algorithm 1 is Oin log n) plus the time for (« - l)/it - 1) calls on TOUR, and that \Wj\-\ T* ), where \W^\ is the length of the spanning walk ff ...
... capable of the exact solution of ;-city traveling-salesman problems, where / is specified by the user of the algorithm. We show that the execution time of Algorithm 1 is Oin log n) plus the time for (« - l)/it - 1) calls on TOUR, and that \Wj\-\ T* ), where \W^\ is the length of the spanning walk ff ...
Linear Systems
... Since the application of a Gauss transformation to a matrix involves an outer product, we can regard LU factorization as a sequence of outer product updates Since zeros have already been introduced in columns 1 through k -1, the Gauss transformation update need only be applied to columns k throu ...
... Since the application of a Gauss transformation to a matrix involves an outer product, we can regard LU factorization as a sequence of outer product updates Since zeros have already been introduced in columns 1 through k -1, the Gauss transformation update need only be applied to columns k throu ...
Chapter 10
... 4. If the item is found, then report “success” and the location where the item was found. 5. If the item is not found, then report “failure.” The following value-returning method will satisfy requirements (4) and (5): If the search item is found in the list, the method returns the location in the li ...
... 4. If the item is found, then report “success” and the location where the item was found. 5. If the item is not found, then report “failure.” The following value-returning method will satisfy requirements (4) and (5): If the search item is found in the list, the method returns the location in the li ...
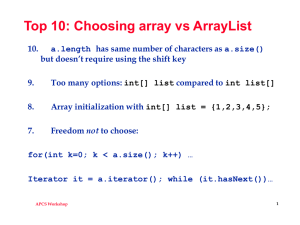
apworkshoparrays
... You can add a String to an ArrayList, but you can’t get a String out of an ArrayList (well, ok, you can with a cast). ...
... You can add a String to an ArrayList, but you can’t get a String out of an ArrayList (well, ok, you can with a cast). ...
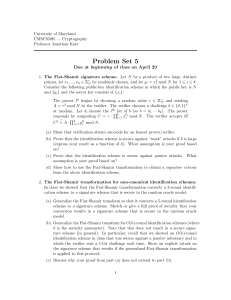
pdf
... signature scheme: the master public key is a modulus N and an exponent e; the master secret key is d such that ed = 1 mod ϕ(N ). A user with identity ID is given secret key SKID = H(ID)d mod N (where H is modeled as a random oracle); this user can now sign messages with respect to his identity by us ...
... signature scheme: the master public key is a modulus N and an exponent e; the master secret key is d such that ed = 1 mod ϕ(N ). A user with identity ID is given secret key SKID = H(ID)d mod N (where H is modeled as a random oracle); this user can now sign messages with respect to his identity by us ...
Python XML Element Trees
... (head recursion); and line 20 does it to leaf nodes (recursion end). So all subelements get the the same text and tail indention. Unfortunately, this applies the wrong value to the last sub-element’s tail field (!); but a correction is performed at line 18 when the indent function returns to its cal ...
... (head recursion); and line 20 does it to leaf nodes (recursion end). So all subelements get the the same text and tail indention. Unfortunately, this applies the wrong value to the last sub-element’s tail field (!); but a correction is performed at line 18 when the indent function returns to its cal ...
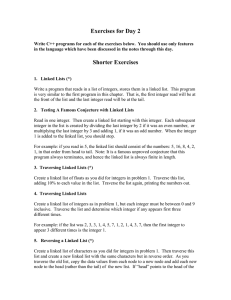
Day_2_prob
... head of the new list are: p -> next = head; head = p; Note: Any linked list can be constructed from scratch using this simple method rather than the slightly more complicated method of this chapter. The downside is that the first value read ends up at the tail of the list and the last value read end ...
... head of the new list are: p -> next = head; head = p; Note: Any linked list can be constructed from scratch using this simple method rather than the slightly more complicated method of this chapter. The downside is that the first value read ends up at the tail of the list and the last value read end ...
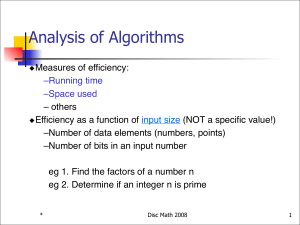
Analysis of Algorithms
... These are bounds on running time, not for the problem! The thumbrules for getting the running time are! 1. Throw away all terms other than the most significant one -- Calculus may be needed ! e.g.: which is greater: n log n or n1.001 ?! 2. Throw away the constant factor.! 3. The expression is Θ() of ...
... These are bounds on running time, not for the problem! The thumbrules for getting the running time are! 1. Throw away all terms other than the most significant one -- Calculus may be needed ! e.g.: which is greater: n log n or n1.001 ?! 2. Throw away the constant factor.! 3. The expression is Θ() of ...
and two-dimensional arrays
... data items that all have the same data type and are accessed by the same name • The individual elements that make up the array are accessed by the use of an index or subscript beside the name of the array – for example, scores (3) Simple Program Design, Fourth Edition Chapter 7 ...
... data items that all have the same data type and are accessed by the same name • The individual elements that make up the array are accessed by the use of an index or subscript beside the name of the array – for example, scores (3) Simple Program Design, Fourth Edition Chapter 7 ...
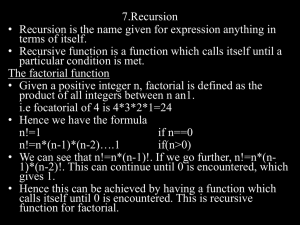
Recursion Review - Department of Computer Science
... To obtain the answer to a large problem, the large problem is often reduced to one or more problems of a similar nature but a smaller size Subproblems are further divided until the size of the subproblems is reduced to some smallest, base case, where the solution is given directly without further re ...
... To obtain the answer to a large problem, the large problem is often reduced to one or more problems of a similar nature but a smaller size Subproblems are further divided until the size of the subproblems is reduced to some smallest, base case, where the solution is given directly without further re ...
ALGORITHMS AND FLOWCHARTS
... A flowchart consists of a sequence of instructions linked together by arrows to show the order in which the instructions must be carried out. ...
... A flowchart consists of a sequence of instructions linked together by arrows to show the order in which the instructions must be carried out. ...
Document
... Case 1: There is a majority in A. – Then it is a majority in B, by Lemma, therefore it will be found in the recursive stage of the algorithm Majority(B) (by inductive argument), and will be checked (successfully) in the last point of the algorithm Majority(A). ...
... Case 1: There is a majority in A. – Then it is a majority in B, by Lemma, therefore it will be found in the recursive stage of the algorithm Majority(B) (by inductive argument), and will be checked (successfully) in the last point of the algorithm Majority(A). ...
External Memory Value Iteration
... that the solution to the latter will be a good approximation to the input problem. There are different approaches to do this. Perhaps the most known one is to use polynomial approximations or linear combinations of basis functions to represent the value function [BKK63, TR96], or more complex appro ...
... that the solution to the latter will be a good approximation to the input problem. There are different approaches to do this. Perhaps the most known one is to use polynomial approximations or linear combinations of basis functions to represent the value function [BKK63, TR96], or more complex appro ...
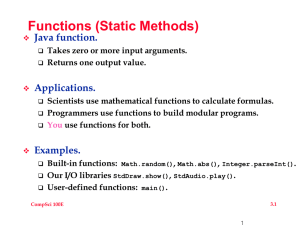
slides03
... In its own .java file, nothing wrong with that Private, used for implementation and not public behavior o Use a nested class, then decide on static or non-static o Non-static is part of an object, access inner fields ...
... In its own .java file, nothing wrong with that Private, used for implementation and not public behavior o Use a nested class, then decide on static or non-static o Non-static is part of an object, access inner fields ...
The Unbearable Lightness of Consensus
... From fail-stop to fail-silent We assume a majority of correct processes In the 1-N algorithm, the writer writes in a majority using a timestamp determined locally and the reader selects a value from a majority and then imposes this value on a majority In the N-N algorithm, the writers determi ...
... From fail-stop to fail-silent We assume a majority of correct processes In the 1-N algorithm, the writer writes in a majority using a timestamp determined locally and the reader selects a value from a majority and then imposes this value on a majority In the N-N algorithm, the writers determi ...
CMPS101: Homework #1 Solutions
... (Problem 2.2-3 on p. 29 of the text): Assume that the element being searched is in the list exactly one time and assume it is equally likely in each position ...
... (Problem 2.2-3 on p. 29 of the text): Assume that the element being searched is in the list exactly one time and assume it is equally likely in each position ...
Quicksort

Quicksort (sometimes called partition-exchange sort) is an efficient sorting algorithm, serving as a systematic method for placing the elements of an array in order. Developed by Tony Hoare in 1959, with his work published in 1961, it is still a commonly used algorithm for sorting. When implemented well, it can be about two or three times faster than its main competitors, merge sort and heapsort.Quicksort is a comparison sort, meaning that it can sort items of any type for which a ""less-than"" relation (formally, a total order) is defined. In efficient implementations it is not a stable sort, meaning that the relative order of equal sort items is not preserved. Quicksort can operate in-place on an array, requiring small additional amounts of memory to perform the sorting.Mathematical analysis of quicksort shows that, on average, the algorithm takes O(n log n) comparisons to sort n items. In the worst case, it makes O(n2) comparisons, though this behavior is rare.