Chapter 32
... • IPsec authentication is designed to make sure that an arriving datagram is identical to the one sent – But we know that the TTL and checksum fields are changed each hop – Mutable fields are those IP headers that get changed in transit • We don’t want these slight changes to cause authentication er ...
... • IPsec authentication is designed to make sure that an arriving datagram is identical to the one sent – But we know that the TTL and checksum fields are changed each hop – Mutable fields are those IP headers that get changed in transit • We don’t want these slight changes to cause authentication er ...
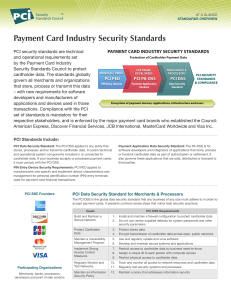
Payment Card Industry Security Standards
... © 2008 PCI Security Standards Council LLC. The intent of this document is to provide supplemental information, which does not replace or supersede PCI SSC Security Standards or their supporting documents. ...
... © 2008 PCI Security Standards Council LLC. The intent of this document is to provide supplemental information, which does not replace or supersede PCI SSC Security Standards or their supporting documents. ...
Chapter 11 Outline
... between machines. Identification, authorization, and all other standard functions are done with the standard mechanisms for the established system. D. VPNs can use many different protocols to offer a secure method of communicating between endpoints. ...
... between machines. Identification, authorization, and all other standard functions are done with the standard mechanisms for the established system. D. VPNs can use many different protocols to offer a secure method of communicating between endpoints. ...
Introduction to Biometrics
... BioAPI for Java Card • Java Card: – Java Card technology provides a secure environment for applications that run on smart cards and other devices with very limited memory and processing capabilities. – Multiple applications can be deployed on a single card, and new ones can be added to it even afte ...
... BioAPI for Java Card • Java Card: – Java Card technology provides a secure environment for applications that run on smart cards and other devices with very limited memory and processing capabilities. – Multiple applications can be deployed on a single card, and new ones can be added to it even afte ...
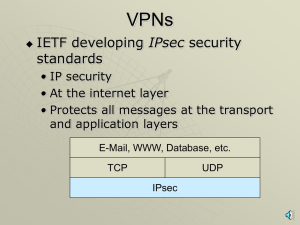
VPNs, PKIs, ISSs, SSLs with narration
... SSL ISS Process • Two sides negotiate security parameters • Webserver authenticates itself • Browser may authenticate itself but rarely does • Browser selects a symmetric session key, sends to webserver • Adds a digital signature and encrypts all messages with the symmetric key ...
... SSL ISS Process • Two sides negotiate security parameters • Webserver authenticates itself • Browser may authenticate itself but rarely does • Browser selects a symmetric session key, sends to webserver • Adds a digital signature and encrypts all messages with the symmetric key ...
Security
... captured by a third party Integrity – how to ensure the information has not been altered in transit Authentication – how to ensure the identity of the sender and receiver Authorization – how to ensure a user has the authority to access / update information Non-repudiation – how do you legally prove ...
... captured by a third party Integrity – how to ensure the information has not been altered in transit Authentication – how to ensure the identity of the sender and receiver Authorization – how to ensure a user has the authority to access / update information Non-repudiation – how do you legally prove ...
Lecture8_Dare
... Authentication Server is a server that wishes to know the identity of its client may contact the client host's Authentication Server, and ask it for information about the user owning a particular connection This request involves a second TCP connection – so it can help prevent ISN and source routing ...
... Authentication Server is a server that wishes to know the identity of its client may contact the client host's Authentication Server, and ask it for information about the user owning a particular connection This request involves a second TCP connection – so it can help prevent ISN and source routing ...
Mutual Attestation of IoT Devices via strongSwan VPN
... Live Demo: Mutual Attestation of Secure Video Phones Before a pair of Raspberry Pi 2 based video phones set up a secure IPsec-protected multimedia connection, the IoT devices mutually determine the trustworthiness of their peer by attesting all system libraries and executables installed on the remot ...
... Live Demo: Mutual Attestation of Secure Video Phones Before a pair of Raspberry Pi 2 based video phones set up a secure IPsec-protected multimedia connection, the IoT devices mutually determine the trustworthiness of their peer by attesting all system libraries and executables installed on the remot ...
Network Security For Distributed Simulation Systems
... Derived from both the data and the signer, who has the public key Does not guarantee the signer is the owner of the public key This can be guaranteed by the use of Digital Certificates Identity Certificates (eg X.509) - public key and sufficient data to identify the key holder Accreditation - I ...
... Derived from both the data and the signer, who has the public key Does not guarantee the signer is the owner of the public key This can be guaranteed by the use of Digital Certificates Identity Certificates (eg X.509) - public key and sufficient data to identify the key holder Accreditation - I ...
neutralizing credential theft and abuse
... These methods are not effective when dealing with targeted attacks, such as those used for credential phishing. By using cloaking techniques, the site can avoid being recognized as a phishing site. If the site is not categorized as bad, traditional security products, such as mail filtering solutions ...
... These methods are not effective when dealing with targeted attacks, such as those used for credential phishing. By using cloaking techniques, the site can avoid being recognized as a phishing site. If the site is not categorized as bad, traditional security products, such as mail filtering solutions ...
Download attachment
... The Bank has successfully obtained the necessary legislative approvals for this unique product from both the Central Bank of Bahrain and the Bank’s Shari’a Supervisory Board, and is working for its launch shortly. While being a new addition to the Bank's range of innovative products and services, th ...
... The Bank has successfully obtained the necessary legislative approvals for this unique product from both the Central Bank of Bahrain and the Bank’s Shari’a Supervisory Board, and is working for its launch shortly. While being a new addition to the Bank's range of innovative products and services, th ...
Computer Security
... – Carry out manual user authentication – As users are added or changed, more maintenance is required for each script – Usernames and passwords held in one central script Many times in clear text ...
... – Carry out manual user authentication – As users are added or changed, more maintenance is required for each script – Usernames and passwords held in one central script Many times in clear text ...
Web Server Administration
... represents a potential target for attack Hackers can gather data and modify systems SSL can secure data transmission Keep each server to a single purpose such as Web server or e-mail Keep applications and services to a minimum ...
... represents a potential target for attack Hackers can gather data and modify systems SSL can secure data transmission Keep each server to a single purpose such as Web server or e-mail Keep applications and services to a minimum ...
Presentation4 - University Of Worcester
... uniquely designed so it will not run on a server without a server certificate ...
... uniquely designed so it will not run on a server without a server certificate ...
Powerpoint Slides
... Authorities (contd.) A CA is a trusted party whose public key is known, e.g., VeriSign, Inc. The recipient uses the public key of the CA, to decrypt the sender's public key in the certificate. The most vulnerable part of this method is the CA’s private key, which is used to digitally sign the cer ...
... Authorities (contd.) A CA is a trusted party whose public key is known, e.g., VeriSign, Inc. The recipient uses the public key of the CA, to decrypt the sender's public key in the certificate. The most vulnerable part of this method is the CA’s private key, which is used to digitally sign the cer ...
Access Control, Operations Security, and Computer Forensics
... authentication server in UNIX systems • User password administered in a central database rather than in individual routers • TACACS enabled network device prompts for user name and static password • TACACS enabled network device queries TACACA server to verify password • Does not support prompting f ...
... authentication server in UNIX systems • User password administered in a central database rather than in individual routers • TACACS enabled network device prompts for user name and static password • TACACS enabled network device queries TACACA server to verify password • Does not support prompting f ...
Presentation6 - University Of Worcester
... e.g. for an organisation the “trusted” links might be to customers and business partners uses the public Internet as its transmission system requires authentication to gain access ...
... e.g. for an organisation the “trusted” links might be to customers and business partners uses the public Internet as its transmission system requires authentication to gain access ...
Chapter 6
... • The commerce server, along with the Web server, responds to requests from Web browsers through the HTTP protocol and CGI scripts. • Security solutions for commerce servers: – Access control and authentication – Operating system controls – Firewall ...
... • The commerce server, along with the Web server, responds to requests from Web browsers through the HTTP protocol and CGI scripts. • Security solutions for commerce servers: – Access control and authentication – Operating system controls – Firewall ...
Chapter 4
... These threat originate from individuals who have authorized access to the network or have an account on a server. It can be from a disgruntled former or current employee or contractor. ...
... These threat originate from individuals who have authorized access to the network or have an account on a server. It can be from a disgruntled former or current employee or contractor. ...
Access Control, Operations Security, and Computer Forensics
... Commonly used by remote access servers and xDSL, ISDN, and cable modems ...
... Commonly used by remote access servers and xDSL, ISDN, and cable modems ...
IPSec (IP Security)
... Phase1-SA is used to setup IPSec SAs usually (at least)two unidirectional IPSec SAs Phase2 repeated to change keys, Phase1-SA remains ...
... Phase1-SA is used to setup IPSec SAs usually (at least)two unidirectional IPSec SAs Phase2 repeated to change keys, Phase1-SA remains ...
IPSEC Presentation
... What is IPsec? (cont) • Created November 1998 • Created by the Internet Engineering Task Force (IETF) • Deployable on all platforms – Windows – Unix – Etc.. ...
... What is IPsec? (cont) • Created November 1998 • Created by the Internet Engineering Task Force (IETF) • Deployable on all platforms – Windows – Unix – Etc.. ...
Secure Mobility - Grand Rapids ISSA
... Cache cleanup / wipers are best effort, leave recoverable data and do not work at all if session is not properly terminated Encrypted containers - new and better approach; if the data remains, it is not readable Split-Tunneling - this is browser based connection only, not a full LAN-like conne ...
... Cache cleanup / wipers are best effort, leave recoverable data and do not work at all if session is not properly terminated Encrypted containers - new and better approach; if the data remains, it is not readable Split-Tunneling - this is browser based connection only, not a full LAN-like conne ...