Live and Trustworthy Forensic Analysis of Commodity Production
... by a compromised OS, and therefore it can be used to enforce stronger protection [5–9]. Advanced techniques, like the one used by Shadow Walker to hide malicious code, are defeated using out-of-the-box memory content scanners. Unfortunately, all the VMM-based solutions proposed in literature are bas ...
... by a compromised OS, and therefore it can be used to enforce stronger protection [5–9]. Advanced techniques, like the one used by Shadow Walker to hide malicious code, are defeated using out-of-the-box memory content scanners. Unfortunately, all the VMM-based solutions proposed in literature are bas ...
Before You Begin: Assign Information Classification
... Most operating systems have an HCL. HCLs can be found on the manufacturer's website. HCL includes list of hardware that is known to work with the operating system. ...
... Most operating systems have an HCL. HCLs can be found on the manufacturer's website. HCL includes list of hardware that is known to work with the operating system. ...
Operating systems
... control card from the terminal, and output is normally printed immediately to the screen. d. Real time. Often used in a dedicated application. The system reads information from sensors and must respond within a fixed amount of time to ensure correct performance. e. Distributed. Distributes computati ...
... control card from the terminal, and output is normally printed immediately to the screen. d. Real time. Often used in a dedicated application. The system reads information from sensors and must respond within a fixed amount of time to ensure correct performance. e. Distributed. Distributes computati ...
Reboots are for Hardware: Challenges and Solutions to
... some classes that do not yet have state-transfer functions or factories, so are currently not updatable. We included these, because the addition of state-transfer functions and factories is relatively simple (the changes are confined to the class itself), and because we believe that showing the limi ...
... some classes that do not yet have state-transfer functions or factories, so are currently not updatable. We included these, because the addition of state-transfer functions and factories is relatively simple (the changes are confined to the class itself), and because we believe that showing the limi ...
Operating System Concepts
... the entire multithreaded process. Another limitation to a many-to-one thread mapping is that a process's threads cannot simultaneously execute on multiple processors. Scheduler activations attempt to address these limitations to userlevel threads. A scheduler activation is a kernel thread that can n ...
... the entire multithreaded process. Another limitation to a many-to-one thread mapping is that a process's threads cannot simultaneously execute on multiple processors. Scheduler activations attempt to address these limitations to userlevel threads. A scheduler activation is a kernel thread that can n ...
슬라이드 1 - Dankook
... Xen is intended to scale to approximately 100 virtual machines running industry standard applications and services. ...
... Xen is intended to scale to approximately 100 virtual machines running industry standard applications and services. ...
* Abstract
... addition to any such mechanism that may be provided by the hosted operating system. These features have been carefully implemented to avoid the inefficiencies that have plagued virtual machine monitors in the past [20]. For example, Cellular Disco tracks operating system memory usage and paging disk ...
... addition to any such mechanism that may be provided by the hosted operating system. These features have been carefully implemented to avoid the inefficiencies that have plagued virtual machine monitors in the past [20]. For example, Cellular Disco tracks operating system memory usage and paging disk ...
Cellular Disco: resource management using
... addition to any such mechanism that may be provided by the hosted operating system. These features have been carefully implemented to avoid the inefficiencies that have plagued virtual machine monitors in the past [20]. For example, Cellular Disco tracks operating system memory usage and paging disk ...
... addition to any such mechanism that may be provided by the hosted operating system. These features have been carefully implemented to avoid the inefficiencies that have plagued virtual machine monitors in the past [20]. For example, Cellular Disco tracks operating system memory usage and paging disk ...
Linux+ Guide to Linux Certification Chapter Nine System Initialization
... • Boot loaders are typically loaded by the system BIOS from the MBR or the first sector of the active partition of a hard disk • The boot loader is responsible for loading the Linux kernel • The LILO boot loader uses the /etc/lilo.conf configuration file, whereas the GRUB boot loader uses the /boot/ ...
... • Boot loaders are typically loaded by the system BIOS from the MBR or the first sector of the active partition of a hard disk • The boot loader is responsible for loading the Linux kernel • The LILO boot loader uses the /etc/lilo.conf configuration file, whereas the GRUB boot loader uses the /boot/ ...
DEGREE PROGRAM IN ELECTRICAL ENGINEERING LINUX
... implement a network layer without an operating system. Hence, Linux implements network layer functionality very well, research scenarios are much easier to implement, because there is no need to concentrate on an unrelevant low level functionality. It is possible to control all layers of the OSI mod ...
... implement a network layer without an operating system. Hence, Linux implements network layer functionality very well, research scenarios are much easier to implement, because there is no need to concentrate on an unrelevant low level functionality. It is possible to control all layers of the OSI mod ...
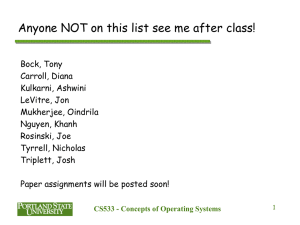
ppt
... On multiprocessor systems, with several CPUs, it would make sense for a process to have several CPU contexts (threads of control) Multiple threads of control could run in the same address space on a single CPU system too! o ...
... On multiprocessor systems, with several CPUs, it would make sense for a process to have several CPU contexts (threads of control) Multiple threads of control could run in the same address space on a single CPU system too! o ...
A Virtual Machine Introspection Based Architecture for Intrusion
... creasing the risk of having an incorrect view of system state, and reducing the number of unmonitored avenues of attack. On the other hand, increasing the visibility of the target system to the IDS frequently comes at the cost of weaker isolation between the IDS and attacker. This increases the risk ...
... creasing the risk of having an incorrect view of system state, and reducing the number of unmonitored avenues of attack. On the other hand, increasing the visibility of the target system to the IDS frequently comes at the cost of weaker isolation between the IDS and attacker. This increases the risk ...
SPARC Enterprise T5140 and T5240 Servers Product Notes
... This distribution may include materials developed by third parties. Parts of the product may be derived from Berkeley BSD systems, licensed from the University of California. UNIX is a registered trademark in the U.S. and in other countries, exclusively licensed through X/Open Company, Ltd. Sun, Sun ...
... This distribution may include materials developed by third parties. Parts of the product may be derived from Berkeley BSD systems, licensed from the University of California. UNIX is a registered trademark in the U.S. and in other countries, exclusively licensed through X/Open Company, Ltd. Sun, Sun ...
Threads (continued)
... • Processes are heavyweight in Windows and Linux • Difficult to develop concurrent applications when address space is unique per process ...
... • Processes are heavyweight in Windows and Linux • Difficult to develop concurrent applications when address space is unique per process ...
Copyright © 1997 IEEE. Reprinted from Proceedings of the Third
... Shared memory. Shared memory allows multiple processes to reference the same physical data through (potentially) different virtual addresses. Space requirements can be reduced by sharing code between processes. Using shared memory for communication avoids the data-copying of traditional message-pass ...
... Shared memory. Shared memory allows multiple processes to reference the same physical data through (potentially) different virtual addresses. Space requirements can be reduced by sharing code between processes. Using shared memory for communication avoids the data-copying of traditional message-pass ...
Cooperating Processes
... • Blocking send: The sender is blocked until the requested message is delivered. • Nonblocking send: The sending process sends the message and resumes operation. • Blocking receive: The receiver blocks until the requested message is delivered/arrived. • Nonblocking receive: The receiver retrieves ei ...
... • Blocking send: The sender is blocked until the requested message is delivered. • Nonblocking send: The sending process sends the message and resumes operation. • Blocking receive: The receiver blocks until the requested message is delivered/arrived. • Nonblocking receive: The receiver retrieves ei ...
I/O Paravirtualization at the Device File Boundary
... is an event, the process is notified with a signal. To correctly access an I/O device, an application may need to know the exact make, model or functional capabilities of the device. For example, the X Server needs to know the GPU make in order to load the correct libraries. As such, the kernel coll ...
... is an event, the process is notified with a signal. To correctly access an I/O device, an application may need to know the exact make, model or functional capabilities of the device. For example, the X Server needs to know the GPU make in order to load the correct libraries. As such, the kernel coll ...
Chapter 4: Threads
... The register set, stacks, and private storage area are known as the context of the threads! ...
... The register set, stacks, and private storage area are known as the context of the threads! ...
ppt
... Both M:M and Two-level models require communication to maintain the appropriate number of kernel threads allocated to the application ...
... Both M:M and Two-level models require communication to maintain the appropriate number of kernel threads allocated to the application ...
Chapter 1: Introduction
... require communication to maintain the appropriate number of kernel threads allocated to the application Scheduler activations provide upcalls a communication mechanism from the kernel to the thread library This communication allows an application to maintain the correct number kernel threads ...
... require communication to maintain the appropriate number of kernel threads allocated to the application Scheduler activations provide upcalls a communication mechanism from the kernel to the thread library This communication allows an application to maintain the correct number kernel threads ...
Figure 5.01
... Increased responsiveness to user: A program continues running with other threads even if part of it is blocked or performing a lengthy operation in one thread. Resource Sharing Threads share memory and resources of their process. Economy Less time consuming to create and manage threads t ...
... Increased responsiveness to user: A program continues running with other threads even if part of it is blocked or performing a lengthy operation in one thread. Resource Sharing Threads share memory and resources of their process. Economy Less time consuming to create and manage threads t ...
Proceedings of the First Symposium on Networked Systems Design and Implementation
... other words, rather than have a single privileged application controlling a particular aspect of the OS, the PlanetLab OS potentially supports many such management services. One implication of this interface being sharable is that it must be well-defined, explicitly exposing the state of the underly ...
... other words, rather than have a single privileged application controlling a particular aspect of the OS, the PlanetLab OS potentially supports many such management services. One implication of this interface being sharable is that it must be well-defined, explicitly exposing the state of the underly ...