Section2.2notes
... Using the decipherment formula x 9( y 21) MOD 26 , we can decipher the message using the following repetitive steps: A y 0 x 9(0 21) MOD 26 9(21) MOD 26 189 MOD 26 7 H R y 17 x 9(17 21) MOD 26 9(38) MOD 26 342 MOD 26 4 E M y 12 x 9(12 21) MOD 26 9( ...
... Using the decipherment formula x 9( y 21) MOD 26 , we can decipher the message using the following repetitive steps: A y 0 x 9(0 21) MOD 26 9(21) MOD 26 189 MOD 26 7 H R y 17 x 9(17 21) MOD 26 9(38) MOD 26 342 MOD 26 4 E M y 12 x 9(12 21) MOD 26 9( ...
CR Yang, NTNU MT
... The response of a system subjected to any type of nonperiodic force is commonly found using the following methods: (1) Convolution integral; (2) Laplace transform; (3) Numerical methods ...
... The response of a system subjected to any type of nonperiodic force is commonly found using the following methods: (1) Convolution integral; (2) Laplace transform; (3) Numerical methods ...
perimeter of the elliptical arc a geometric method
... Where ‘e’ is the Eccentricity of the Ellipse, the current known solution to the integral is through numerical Integration. A method to estimate a closed form solution to this integral using the geometric method is detailed below. Approximating the Incomplete Elliptical Integral of Second Kind ...
... Where ‘e’ is the Eccentricity of the Ellipse, the current known solution to the integral is through numerical Integration. A method to estimate a closed form solution to this integral using the geometric method is detailed below. Approximating the Incomplete Elliptical Integral of Second Kind ...
2-7 The Mathematics Models and an Actual Proof Experiment
... 2 IP traceback 2.1 Functions of IP traceback IP traceback methods are designed to track down the sources of attacks mainly within a single autonomous system (AS). In most cases, however, DDoS attack packets pass across several ASs to reach a victim. Therefore, in addition to performing traceback wi ...
... 2 IP traceback 2.1 Functions of IP traceback IP traceback methods are designed to track down the sources of attacks mainly within a single autonomous system (AS). In most cases, however, DDoS attack packets pass across several ASs to reach a victim. Therefore, in addition to performing traceback wi ...
Large–Scale Tikhonov Regularization for Total Least
... a linear model is error free, and all errors are confined to the right hand side b. However, in engineering applications this assumption is often unrealistic. Many problems in data estimation are obtained by linear systems where both, the matrix A and the right-hand side b, are contaminated by noise ...
... a linear model is error free, and all errors are confined to the right hand side b. However, in engineering applications this assumption is often unrealistic. Many problems in data estimation are obtained by linear systems where both, the matrix A and the right-hand side b, are contaminated by noise ...
2 - Madison Central School District
... Decimal (a fraction whose denominator is a power of ten and whose numerator is expressed by figures placed to the right of a decimal point) Digit (a numeral between 0 and 9) Divisor (the number by which another number is divided) Equation (a statement that the values of two mathematical expressions ...
... Decimal (a fraction whose denominator is a power of ten and whose numerator is expressed by figures placed to the right of a decimal point) Digit (a numeral between 0 and 9) Divisor (the number by which another number is divided) Equation (a statement that the values of two mathematical expressions ...
Pdf - Text of NPTEL IIT Video Lectures
... Now, by the Picard’s theorem, we have y equal to y naught plus integral x naught to x f x y z d x which is equal to 0.5 plus integral 0 to x z d x f x by z is equal to z here. And z is equal to z naught plus integral x naught to x g x y z d x z naught is equal to 0.1 minus integral 0 to x 2 x z plu ...
... Now, by the Picard’s theorem, we have y equal to y naught plus integral x naught to x f x y z d x which is equal to 0.5 plus integral 0 to x z d x f x by z is equal to z here. And z is equal to z naught plus integral x naught to x g x y z d x z naught is equal to 0.1 minus integral 0 to x 2 x z plu ...
A Comparative Analysis of Different Categorical Data Clustering
... algorithms like Divisive algorithm, LIMBO [11] , single link, Fuzzy C-Means, Fuzzy C-Medoids [12] [13] [14] etc are emerged over earlier periods. Conversely it is known that there is no single clustering method is capable of providing accurate and appropriate cluster results [14]. Since by applying ...
... algorithms like Divisive algorithm, LIMBO [11] , single link, Fuzzy C-Means, Fuzzy C-Medoids [12] [13] [14] etc are emerged over earlier periods. Conversely it is known that there is no single clustering method is capable of providing accurate and appropriate cluster results [14]. Since by applying ...
Multi-Digit Whole Number and Decimal Fraction Operations • Grade 5
... Decimal (a fraction whose denominator is a power of ten and whose numerator is expressed by figures placed to the right of a decimal point) Digit (a numeral between 0 and 9) Divisor (the number by which another number is divided) Equation (a statement that the values of two mathematical expressions ...
... Decimal (a fraction whose denominator is a power of ten and whose numerator is expressed by figures placed to the right of a decimal point) Digit (a numeral between 0 and 9) Divisor (the number by which another number is divided) Equation (a statement that the values of two mathematical expressions ...
Regularization Tools
... a great source of inspiration. The package was also inspired by a paper by Natterer [68] where a “numerical analyst’s toolkit for ill-posed problems” is suggested. The Fortran programs by Drake [20], te Riele [76], and Wahba and her co-workers [6] also deserve to be mentioned here. The package has b ...
... a great source of inspiration. The package was also inspired by a paper by Natterer [68] where a “numerical analyst’s toolkit for ill-posed problems” is suggested. The Fortran programs by Drake [20], te Riele [76], and Wahba and her co-workers [6] also deserve to be mentioned here. The package has b ...
Exact Solution of Time History Response for Dynamic
... modal damping matrix are moved to the right-hand-side as a pseudo-load term proportional to the cross-coupling damping matrix times the generalized velocity vector after modal transformation, leaving on the left-hand-side pseudo-uncoupled equations with modal damping ratios. An approximate solution ...
... modal damping matrix are moved to the right-hand-side as a pseudo-load term proportional to the cross-coupling damping matrix times the generalized velocity vector after modal transformation, leaving on the left-hand-side pseudo-uncoupled equations with modal damping ratios. An approximate solution ...
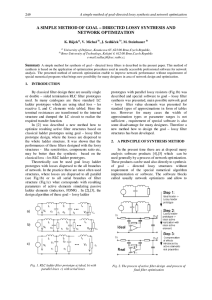
a simple method of goal – directed lossy synthesis and network
... difference of transfer function from ideal required transfer response, how declare a typical example of transfer function of Tschebyshev goal – lossy prototype of 5th filter order from Fig.5. From comparison of transfer responses is evidently seen influence of parasitic pole for RLC lossy structure ...
... difference of transfer function from ideal required transfer response, how declare a typical example of transfer function of Tschebyshev goal – lossy prototype of 5th filter order from Fig.5. From comparison of transfer responses is evidently seen influence of parasitic pole for RLC lossy structure ...
a comparative evaluation of matlab, octave, freemat - here
... On multi-core processors or on multi-core compute nodes with shared memory among all computational cores, software such as the numerical computational packages considered here automatically use all available cores, since the underlying libraries such as BLAS, LAPACK, etc. use them; studies by these ...
... On multi-core processors or on multi-core compute nodes with shared memory among all computational cores, software such as the numerical computational packages considered here automatically use all available cores, since the underlying libraries such as BLAS, LAPACK, etc. use them; studies by these ...
A GENERAL THEOREM ON ERROR ESTIMATES WITH
... has mesh size h. How large is the difference between a locally optimal control and its numerical approximation, if the state equation is handled by a finite element method and the controls are discretized appropriately? In the last decade, the associated error analysis of optimal control problems fo ...
... has mesh size h. How large is the difference between a locally optimal control and its numerical approximation, if the state equation is handled by a finite element method and the controls are discretized appropriately? In the last decade, the associated error analysis of optimal control problems fo ...
Preconditioning of Markov Chain Monte Carlo Simulations Using
... (2.1)-(2.3) on the fine-grid. Generally, the MCMC method requires thousands of iterations before it converges to the steady state. To quantify the uncertainty of the permeability field accurately, one also needs to generate a large number of different samples. However, the acceptance rate of the dir ...
... (2.1)-(2.3) on the fine-grid. Generally, the MCMC method requires thousands of iterations before it converges to the steady state. To quantify the uncertainty of the permeability field accurately, one also needs to generate a large number of different samples. However, the acceptance rate of the dir ...
Isotopic depletion
... by adopting a numerical method that has the capability to deal with stiff systems of equations. The Kaps-Renthrop algorithm and integration factor method are numerical methods with such capability. by eliminating the depletion equations with high values of Λk . These equations can be lumped at the o ...
... by adopting a numerical method that has the capability to deal with stiff systems of equations. The Kaps-Renthrop algorithm and integration factor method are numerical methods with such capability. by eliminating the depletion equations with high values of Λk . These equations can be lumped at the o ...
¿Cuál debería ser el nivel de sencillez ideal para un análisis no
... Approximation) but allows refining it for advanced analyses and assessments (higher-order Levels-of-Approximation). The use of numerical tools consistent with the design procedures used for simpler analyses becomes thus encouraged for designers. A question arises then on how should a suitable nonlin ...
... Approximation) but allows refining it for advanced analyses and assessments (higher-order Levels-of-Approximation). The use of numerical tools consistent with the design procedures used for simpler analyses becomes thus encouraged for designers. A question arises then on how should a suitable nonlin ...