PDF - 4up
... that stores other objects, referred to as data or elements. So some people refer a data structure as a container object or a collection object. To define a data structure is essentially to declare a class. The class for a data structure should use data fields to store data and provide methods to sup ...
... that stores other objects, referred to as data or elements. So some people refer a data structure as a container object or a collection object. To define a data structure is essentially to declare a class. The class for a data structure should use data fields to store data and provide methods to sup ...
A polynomial time algorithm for Rayleigh ratio on
... algorithm alternative to the spectral method that delivers solutions to the problems that are often of better quality and with more efficient run times. The theoretical underpinnings for the spectral method were motivated by Perron-Frobenius theorem (1907, 1912). The spectral method has been used in r ...
... algorithm alternative to the spectral method that delivers solutions to the problems that are often of better quality and with more efficient run times. The theoretical underpinnings for the spectral method were motivated by Perron-Frobenius theorem (1907, 1912). The spectral method has been used in r ...
Unsupervised Feature Selection for the k
... Given an n × d matrix A, let Uk ∈ Rn×k (resp. Vk ∈ Rd×k ) be the matrix of the top k left (resp. right) singular vectors of A, and let Σk ∈ Rk×k be a diagonal matrix containing the top k singular values of A. If we let ρ be the rank of A, then Aρ−k is equal to A − Ak , with Ak = Uk Σk VkT . ∥A∥F and ...
... Given an n × d matrix A, let Uk ∈ Rn×k (resp. Vk ∈ Rd×k ) be the matrix of the top k left (resp. right) singular vectors of A, and let Σk ∈ Rk×k be a diagonal matrix containing the top k singular values of A. If we let ρ be the rank of A, then Aρ−k is equal to A − Ak , with Ak = Uk Σk VkT . ∥A∥F and ...
Cooperation between Trust and Routing Mechanisms for Relay
... problems of all networks occur if the communication paths are disconnected for a short time. The hybrid MANET-DTN is an evolution of the Mobile Ad Hoc Networks (MANET) and Delay/Disruption Tolerant Network (DTN) and it gives the possibilities of data transport between the disconnected islands of the ...
... problems of all networks occur if the communication paths are disconnected for a short time. The hybrid MANET-DTN is an evolution of the Mobile Ad Hoc Networks (MANET) and Delay/Disruption Tolerant Network (DTN) and it gives the possibilities of data transport between the disconnected islands of the ...
Lightpath Establishment in Wavelength
... larger systems, heuristic methods must be used. In [3], the routing problem is formulated as an ILP in which the objective is to minimize the number of wavelengths required to establish a fixed set of lightpaths. The search space of the problem is reduced by restricting the set of links through whic ...
... larger systems, heuristic methods must be used. In [3], the routing problem is formulated as an ILP in which the objective is to minimize the number of wavelengths required to establish a fixed set of lightpaths. The search space of the problem is reduced by restricting the set of links through whic ...
Counting Inversions, Offline Orthogonal Range Counting, and Related Problems Timothy M. Chan
... simple, the end result remains surprising. In fact, more O(n) [JMS04]. powerful instantiations of this basic idea yield a handful Given this precise understanding, it now makes of improved algorithms and data structures. sense to look at the preprocessing time more carefully. Unfortunately, it is no ...
... simple, the end result remains surprising. In fact, more O(n) [JMS04]. powerful instantiations of this basic idea yield a handful Given this precise understanding, it now makes of improved algorithms and data structures. sense to look at the preprocessing time more carefully. Unfortunately, it is no ...
Powerpoint Slides
... PLR knows Ruv and Suv for all links PLR computes total bandwidth Ruv+Suv available to route the new backup path on each link(u,v) All links for which Ruv+Suv < bnew are pruned For each remaining link(u,v), the additional bandwidth required is given by max(0, bnew-Suv) PLR computes the route that req ...
... PLR knows Ruv and Suv for all links PLR computes total bandwidth Ruv+Suv available to route the new backup path on each link(u,v) All links for which Ruv+Suv < bnew are pruned For each remaining link(u,v), the additional bandwidth required is given by max(0, bnew-Suv) PLR computes the route that req ...
Star-crossed cube: an alternative to star graph
... Definition 3 The diameter of a graph G denoted as D G is defined to be max. {d G (u,v): u,v ∈ V} , where d G is the distance between 2 nodes. Definition 4 A graph is said to be regular if all of its vertices have the same degree. Definition 5 A graph G(V, E)is vertex symmetric if for every pair of v ...
... Definition 3 The diameter of a graph G denoted as D G is defined to be max. {d G (u,v): u,v ∈ V} , where d G is the distance between 2 nodes. Definition 4 A graph is said to be regular if all of its vertices have the same degree. Definition 5 A graph G(V, E)is vertex symmetric if for every pair of v ...
Set 2
... For each (distinct) pair of points in the set, compute a, b, and c to define the line ax + by = c. For each other point, plug its x and y coordinates into the expression ax + by – c. If, for all the other points (x,y), ax + by – c has the same sign (all positive or all negative), then this pair ...
... For each (distinct) pair of points in the set, compute a, b, and c to define the line ax + by = c. For each other point, plug its x and y coordinates into the expression ax + by – c. If, for all the other points (x,y), ax + by – c has the same sign (all positive or all negative), then this pair ...
Evolving Neural Networks using Ant Colony Optimization with
... Each input parameter is associated with a single unit from the input layer. The target parameter is used to calculate the network error, i.e., the difference between the actual and the target outputs. When the network error becomes sufficiently small it means that the network has generalized and the ...
... Each input parameter is associated with a single unit from the input layer. The target parameter is used to calculate the network error, i.e., the difference between the actual and the target outputs. When the network error becomes sufficiently small it means that the network has generalized and the ...
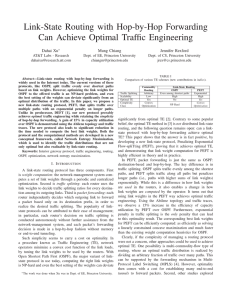
Link-State Routing with Hop-by-Hop Forwarding Can Achieve Optimal Traffic Engineering Dahai Xu
... but these solutions do not enable routers to independently compute the flow-splitting ratios from link weights. Instead, a central management system must compute and configure the traffic-splitting ratios, and update them when the topology changes, sacrificing the main benefit of running a distribut ...
... but these solutions do not enable routers to independently compute the flow-splitting ratios from link weights. Instead, a central management system must compute and configure the traffic-splitting ratios, and update them when the topology changes, sacrificing the main benefit of running a distribut ...
USC3002 Picturing the World Through Mathematics
... connected subset which is not a proper subset of any path connected subset of X . Question 1. How are path components related to ? Lemma If X is an open subset of path component is open. ...
... connected subset which is not a proper subset of any path connected subset of X . Question 1. How are path components related to ? Lemma If X is an open subset of path component is open. ...
A+B
... Big-Omega and Big-Theta Nation • Definition 2: Let f and g be functions from the set of integers or the set of real numbers to the set of real numbers. • We say that f(x) is Ω(g(x)) if there are positive constants C and k such that |f(x)|≥ C|g(x)| Whenever x > k. ( this is read as “f(x) is big-Omeg ...
... Big-Omega and Big-Theta Nation • Definition 2: Let f and g be functions from the set of integers or the set of real numbers to the set of real numbers. • We say that f(x) is Ω(g(x)) if there are positive constants C and k such that |f(x)|≥ C|g(x)| Whenever x > k. ( this is read as “f(x) is big-Omeg ...