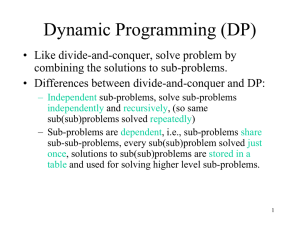
Dynamic Programming
... DP is better by a constant factor due to no recursive involvement as in Memoized algorithm. • If some subproblems may not need to be solved, Memoized algorithm may be more efficient, since it only solve these subproblems which are definitely required. ...
... DP is better by a constant factor due to no recursive involvement as in Memoized algorithm. • If some subproblems may not need to be solved, Memoized algorithm may be more efficient, since it only solve these subproblems which are definitely required. ...
Artificial Intelligence, Logic and Formalizing Common Sense
... to this audience—why they shouldn’t avoid it. It gives a sense of the wider significance of the program that John presented in the 1989 paper, and it might help you to be persuasive when you talk to philosophers. I can use all the help I can get in convincing them to take work in AI seriously. McCar ...
... to this audience—why they shouldn’t avoid it. It gives a sense of the wider significance of the program that John presented in the 1989 paper, and it might help you to be persuasive when you talk to philosophers. I can use all the help I can get in convincing them to take work in AI seriously. McCar ...
Simplification, Optimization and Implication
... a weakly projecting solver never uses more variables than is required ...
... a weakly projecting solver never uses more variables than is required ...
LINEAR PROGRAMMING MODELS
... Optimal Solution corresponds to CPF solution C. Some observations on the solution algorithm: Simplex method focuses solely on CPF solutions. Simplex method is an iteration algorithm. Whenever possible, the initialization of the simplex method chooses the origin as the initial CPF solution. G ...
... Optimal Solution corresponds to CPF solution C. Some observations on the solution algorithm: Simplex method focuses solely on CPF solutions. Simplex method is an iteration algorithm. Whenever possible, the initialization of the simplex method chooses the origin as the initial CPF solution. G ...
The TSP phase transition - Computer Science and Engineering
... to extrapolate to larger n. The asymptotic value of the control parameter, at the phase transition reported in [ 131 is 0.7124 i 0.0002. This is significantly smaller than the value of a used here. If LYis set to 0.7124, a critical value like, for example, the mean or median tour length can be model ...
... to extrapolate to larger n. The asymptotic value of the control parameter, at the phase transition reported in [ 131 is 0.7124 i 0.0002. This is significantly smaller than the value of a used here. If LYis set to 0.7124, a critical value like, for example, the mean or median tour length can be model ...
The Multiple Knapsack Problem Approached by a Binary Differential
... The Genetic Algorithms (GA) are one of the best known and most used algorithms from the Evolutionary Computation field and was proposed by John Holland in 1975 [7]. The inspiration behind GA is based on Darwin’s theory of evolution of species. In nature, individuals from different populations compet ...
... The Genetic Algorithms (GA) are one of the best known and most used algorithms from the Evolutionary Computation field and was proposed by John Holland in 1975 [7]. The inspiration behind GA is based on Darwin’s theory of evolution of species. In nature, individuals from different populations compet ...
Computational Experiments for the Problem of
... Note that different Hamiltonian path problems are extensively studied (see e.g. [1] – [3]). have natural applications in the design of experiments. In particular, the problem of Hamiltonian path with fixed number of color repetitions for c-arc-colored digraphs can be used for scenarios creation for se ...
... Note that different Hamiltonian path problems are extensively studied (see e.g. [1] – [3]). have natural applications in the design of experiments. In particular, the problem of Hamiltonian path with fixed number of color repetitions for c-arc-colored digraphs can be used for scenarios creation for se ...
LP and Approximation
... geometrical shape - we call it a polyhedron. If we can determine all the corner points of the ...
... geometrical shape - we call it a polyhedron. If we can determine all the corner points of the ...
The Robustness-Performance Tradeoff in Markov Decision Processes
... We call c(1) x the first objective, and c(2) x the second objective. We assume that the Linear Program (LP) is feasible and bounded for both objectives. Although there are uncountably many possible λ, Problem (1) can be solved by a simplex-like algorithm. Here, “solve” means that for each λ, we find ...
... We call c(1) x the first objective, and c(2) x the second objective. We assume that the Linear Program (LP) is feasible and bounded for both objectives. Although there are uncountably many possible λ, Problem (1) can be solved by a simplex-like algorithm. Here, “solve” means that for each λ, we find ...
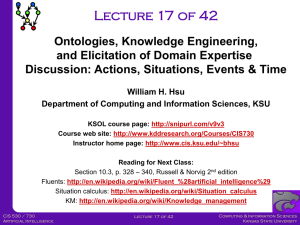
Knowledge Engineering - KDD
... The knowledge engineer schedules numerous meetings with the expert to uncover basic concepts, primitive relations, and definitions needed to talk about and understand this problem and its solutions. The following is a sample dialogue between the knowledge engineer and the expert: KE: Suppose you wer ...
... The knowledge engineer schedules numerous meetings with the expert to uncover basic concepts, primitive relations, and definitions needed to talk about and understand this problem and its solutions. The following is a sample dialogue between the knowledge engineer and the expert: KE: Suppose you wer ...
A Genetic Algorithm Approach to Solve for Multiple Solutions of
... the IK problem is to use numerical methods [3], [4]. In numerical methods, the algorithm converges on the solution that is closest to the initial starting point of the algorithm. Since most of these methods are divergence based, they are vulnerable to local optimums. To solve IK for a redundant robo ...
... the IK problem is to use numerical methods [3], [4]. In numerical methods, the algorithm converges on the solution that is closest to the initial starting point of the algorithm. Since most of these methods are divergence based, they are vulnerable to local optimums. To solve IK for a redundant robo ...
Fuzzy logic and neural networks
... In this paper we elucidate the basic principle of neural computing - the neuronal morphology of the brain, and an artificial neural computing systems (1-31. In the conventional neural computing systems, the main mathematical tools employed are based upon algebraic and differential calculus. In the d ...
... In this paper we elucidate the basic principle of neural computing - the neuronal morphology of the brain, and an artificial neural computing systems (1-31. In the conventional neural computing systems, the main mathematical tools employed are based upon algebraic and differential calculus. In the d ...
Utility maximization and trade
... output for each good? Solution: Since demand must equal supply and demand is just the solution for the utility maximization problem, output must be [x = 7.0, y = 3.0] . Exports and imports are both zero. Example 21 Assume that the international terms of trade are equal to 1.5. Which good will the co ...
... output for each good? Solution: Since demand must equal supply and demand is just the solution for the utility maximization problem, output must be [x = 7.0, y = 3.0] . Exports and imports are both zero. Example 21 Assume that the international terms of trade are equal to 1.5. Which good will the co ...
Solution 1 - JEJAK 1000 PENA
... Arrange the digits 1 through 9 in increasing order, and exclude 0 because a positive integer cannot begin with 0. To get a monotonous number, we can either include or exclude each of the remaining 9 digits, and there are ways to do this. However, we cannot exclude every digit at once, so we subtract ...
... Arrange the digits 1 through 9 in increasing order, and exclude 0 because a positive integer cannot begin with 0. To get a monotonous number, we can either include or exclude each of the remaining 9 digits, and there are ways to do this. However, we cannot exclude every digit at once, so we subtract ...
Optimization of (s, S) Inventory Systems with Random Lead Times
... A review of the literature on service level constraints reveals that the two most relevant works are Schneider and Ringuest (1990) and Tijms and Groenevelt (1984). Schneider and Ringuest consider a periodic review system operating under a -service level measure, where (1 ? ) is the fraction of ...
... A review of the literature on service level constraints reveals that the two most relevant works are Schneider and Ringuest (1990) and Tijms and Groenevelt (1984). Schneider and Ringuest consider a periodic review system operating under a -service level measure, where (1 ? ) is the fraction of ...
Using Hopfield Networks to Solve Assignment Problem and N
... The continuous Hopfield neural network (CHNN) [1] can be used to solve an optimization problem in such a way that the cost function and constraints are first mapped to an energy function (if possible) and then a solution is obtained as the network stabilizes. Ever since Hopfield and Tank applied thi ...
... The continuous Hopfield neural network (CHNN) [1] can be used to solve an optimization problem in such a way that the cost function and constraints are first mapped to an energy function (if possible) and then a solution is obtained as the network stabilizes. Ever since Hopfield and Tank applied thi ...
Conservation decision-making in large state spaces
... Although SDP gives the optimal solution to conservation management questions in a stochastic world, its applicability has always been limited by the so-called curse of dimensionality. The curse of dimensionality is the problem that adding new state variables inevitably results in much larger (often ...
... Although SDP gives the optimal solution to conservation management questions in a stochastic world, its applicability has always been limited by the so-called curse of dimensionality. The curse of dimensionality is the problem that adding new state variables inevitably results in much larger (often ...
The Utilization of A..
... Consists of three functional components Information source: provider a stream of event records Analysis engine: finds signs of intrusions Response component: generates reactions based on the outcome of the analysis engine ...
... Consists of three functional components Information source: provider a stream of event records Analysis engine: finds signs of intrusions Response component: generates reactions based on the outcome of the analysis engine ...