How to Avoid Spam Filters
... You don’t have to be a spammer to get reported for spamming. Sometimes an email gets reported as spam, even if it’s not. Sometimes it’s a simple mistake, like when an inexperienced user clicks the spam button to unsubscribe from an email. But mistake or not, getting reported for abuse is serious. If ...
... You don’t have to be a spammer to get reported for spamming. Sometimes an email gets reported as spam, even if it’s not. Sometimes it’s a simple mistake, like when an inexperienced user clicks the spam button to unsubscribe from an email. But mistake or not, getting reported for abuse is serious. If ...
IOSR Journal of Business and Management (IOSR-JBM) e-ISSN: 2278-487X, p-ISSN: 2319-7668. www.iosrjournals.org
... (Krishnamurthy, 2000). Despite the many benefits to senders of direct e-marketing campaigns, the impacts are pernicious on consumers, e-mail providers, and organizations. Many users are angry and frustrated because they must sift through the hills of unsolicited commercial e-mail (UCE) in their inbo ...
... (Krishnamurthy, 2000). Despite the many benefits to senders of direct e-marketing campaigns, the impacts are pernicious on consumers, e-mail providers, and organizations. Many users are angry and frustrated because they must sift through the hills of unsolicited commercial e-mail (UCE) in their inbo ...
Spam
... came out of the war. The use of veterans as performers was also used to appeal to all of the former troops who may have had poor experiences with the product during their service. By the 1960’s the canned food market became very saturated with competitors. Marketing campaigns such as The Hormel Girl ...
... came out of the war. The use of veterans as performers was also used to appeal to all of the former troops who may have had poor experiences with the product during their service. By the 1960’s the canned food market became very saturated with competitors. Marketing campaigns such as The Hormel Girl ...
Research Paper - Pace University
... that time. At this time people quickly picked up on this and began using the term “spam” more widely to describe junk email. However, in this case the net users fought back by flooding mailboxes, emails, fax machines, every possible account that was connected to the spamming with their own messages. ...
... that time. At this time people quickly picked up on this and began using the term “spam” more widely to describe junk email. However, in this case the net users fought back by flooding mailboxes, emails, fax machines, every possible account that was connected to the spamming with their own messages. ...
All about “Spam”
... and other spam sources21. The idea is to avoid accepting email from systems that are being actively exploited by spammers. The Internet is composed of co-operating but independent networks, so there is no right for anyone to have their email accepted and so mail servers owners can apply any acceptan ...
... and other spam sources21. The idea is to avoid accepting email from systems that are being actively exploited by spammers. The Internet is composed of co-operating but independent networks, so there is no right for anyone to have their email accepted and so mail servers owners can apply any acceptan ...
Top Ten Things About Spam Firewalls
... precaution, it is a necessity for all organizations that rely on email as an effective business communications tool. Despite this, the price for many popular spam solutions remains at a premium that many organizations cannot afford. Many vendors determine pricing based on the number of users in an o ...
... precaution, it is a necessity for all organizations that rely on email as an effective business communications tool. Despite this, the price for many popular spam solutions remains at a premium that many organizations cannot afford. Many vendors determine pricing based on the number of users in an o ...
AZ of Cybercrime terms and definitions
... Spamming: the abuse of electronic messaging systems to indiscriminately send unsolicited bulk messages. While the most widely recognized form of spam is e-mail spam, the term is applied to similar abuses in other media: instant messaging spam, Usenet newsgroup spam, Web search engine spam, spam in b ...
... Spamming: the abuse of electronic messaging systems to indiscriminately send unsolicited bulk messages. While the most widely recognized form of spam is e-mail spam, the term is applied to similar abuses in other media: instant messaging spam, Usenet newsgroup spam, Web search engine spam, spam in b ...
LearnEnglish Professionals
... Yahoo address you get that little 'do you Yahoo?' message at the end basically advertising what Yahoo does, while still providing you with the service the message you've received. P: But it's not limited to internet email providers, is it? M: Not at all. Hotmail is perhaps the most famous exa ...
... Yahoo address you get that little 'do you Yahoo?' message at the end basically advertising what Yahoo does, while still providing you with the service the message you've received. P: But it's not limited to internet email providers, is it? M: Not at all. Hotmail is perhaps the most famous exa ...
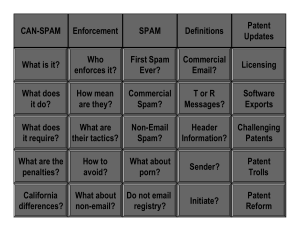
CAN SPAM Presentation
... •The target does not know until it gets served, which is too late. •The FTC will then fight tooth and nail with their endless resources. It's not pleasant. ...
... •The target does not know until it gets served, which is too late. •The FTC will then fight tooth and nail with their endless resources. It's not pleasant. ...
E-mail marketing and picture blocking
... buyers. Anyone can get hold e-mails and add them to a subscription list, but this ease of use increases the spam. Most countries have strict Spam Laws that makes it illegal to send unsolicited e-mails to anyone that the company do not already have a business relation with. According to MessageLabs, ...
... buyers. Anyone can get hold e-mails and add them to a subscription list, but this ease of use increases the spam. Most countries have strict Spam Laws that makes it illegal to send unsolicited e-mails to anyone that the company do not already have a business relation with. According to MessageLabs, ...
Message Characteristics
... past; – Subject lines should begin with”ADV” and “ADV:ADLT” for adult content – A toll-free telephone number or a valid return address is required so that recipients can opt out ...
... past; – Subject lines should begin with”ADV” and “ADV:ADLT” for adult content – A toll-free telephone number or a valid return address is required so that recipients can opt out ...
Team project: Stopping Spam
... the mailer to pay postage. In many cases email is cheap to send, and may be expensive to receive (depending on service provider pricing and connection speed). The process of sending unsolicited email to large, untargeted lists, or through mailing list discussion groups or Usenet newsgroups, is known ...
... the mailer to pay postage. In many cases email is cheap to send, and may be expensive to receive (depending on service provider pricing and connection speed). The process of sending unsolicited email to large, untargeted lists, or through mailing list discussion groups or Usenet newsgroups, is known ...
Introduction - Computer Science and Engineering
... • Mobile spam is a growing problem for users • The efficient and accurate control of spam’s on mobile handsets is an important problem. ...
... • Mobile spam is a growing problem for users • The efficient and accurate control of spam’s on mobile handsets is an important problem. ...
Chapter Five Advertising and Solicitation
... Client surveys Advertising Web sites Chat groups/threaded discussions ...
... Client surveys Advertising Web sites Chat groups/threaded discussions ...
Madleňák Radovan BASIC ASPECTS OF SPAM
... e-mail users. Though the purpose of such attacks is not to alter the service of the attacked machines, its effect on ISPs or enterprises is similar to a denial of service (DoS) attack, wherein legitimate use of the ISP’s services is denied by massive illegitimate traffic [4]. Some spammers gather li ...
... e-mail users. Though the purpose of such attacks is not to alter the service of the attacked machines, its effect on ISPs or enterprises is similar to a denial of service (DoS) attack, wherein legitimate use of the ISP’s services is denied by massive illegitimate traffic [4]. Some spammers gather li ...
Fighting Spam - Northern Michigan University
... • It’s just mass electronic marketing • They give you a web site, you click over and buy the product. • Email might even be targeted. ...
... • It’s just mass electronic marketing • They give you a web site, you click over and buy the product. • Email might even be targeted. ...
View Comment
... Human Capacity Building should be reconsidered in the context of this Report. It would be more constructive to address general sectorial issues that are more applicable to national environments in a separate report, if this is required. There are extensive policy discussions of a number of these are ...
... Human Capacity Building should be reconsidered in the context of this Report. It would be more constructive to address general sectorial issues that are more applicable to national environments in a separate report, if this is required. There are extensive policy discussions of a number of these are ...
Database Techniques for fight SPAM
... Merge Phase – Start with each leaf in its own cluster and merge going up the tree. ...
... Merge Phase – Start with each leaf in its own cluster and merge going up the tree. ...
Chapter 9: Intellectual Property
... Hormel also expresses concern that even comic association with an unclean 'grotesque' boar will call into question the purity and high quality of its meat product. But the district court found no evidence that Spa'am was unhygienic. At worst, he might be described as 'untidy.' Moreover, by now Horme ...
... Hormel also expresses concern that even comic association with an unclean 'grotesque' boar will call into question the purity and high quality of its meat product. But the district court found no evidence that Spa'am was unhygienic. At worst, he might be described as 'untidy.' Moreover, by now Horme ...
international telecommunication union
... The fact that our data now crosses borders and that on-the-run spammers can relocate to safe havens — where privacy laws vary widely — is also a concern. That’s why stopping SPAM and the protection of data has emerged as a top concern of Internet and handset users across the world today. The persona ...
... The fact that our data now crosses borders and that on-the-run spammers can relocate to safe havens — where privacy laws vary widely — is also a concern. That’s why stopping SPAM and the protection of data has emerged as a top concern of Internet and handset users across the world today. The persona ...
Spamming

Electronic spamming is the use of electronic messaging systems to send unsolicited messages (spam), especially advertising, as well as sending messages repeatedly on the same site. While the most widely recognized form of spam is email spam, the term is applied to similar abuses in other media: instant messaging spam, Usenet newsgroup spam, Web search engine spam, spam in blogs, wiki spam, online classified ads spam, mobile phone messaging spam, Internet forum spam, junk fax transmissions, social spam, television advertising and file sharing spam. It is named after Spam, a luncheon meat, by way of a Monty Python sketch in which Spam is included in every dish. The food is stereotypically disliked/unwanted, so the word came to be transferred by analogy.Spamming remains economically viable because advertisers have no operating costs beyond the management of their mailing lists, and it is difficult to hold senders accountable for their mass mailings. Because the barrier to entry is so low, spammers are numerous, and the volume of unsolicited mail has become very high. In the year 2011, the estimated figure for spam messages is around seven trillion. The costs, such as lost productivity and fraud, are borne by the public and by Internet service providers, which have been forced to add extra capacity to cope with the deluge. Spamming has been the subject of legislation in many jurisdictions.A person who creates electronic spam is called a spammer.