santhanam_ratlocc2011
... • Note that if Prx(Q(x) = 1) = 1 – o(1) (as is typical for properties on which probabilistic method is successful) and if G is a quick PRG against Q, then for each N, Range(GN) is an efficiently computable poly(N)-sized list of objects at least one of which satisfies Q ...
... • Note that if Prx(Q(x) = 1) = 1 – o(1) (as is typical for properties on which probabilistic method is successful) and if G is a quick PRG against Q, then for each N, Range(GN) is an efficiently computable poly(N)-sized list of objects at least one of which satisfies Q ...
Mathematical Social Sciences
... Moberg (2012). Note that a similar method was proposed for solving the taxation problem already in the nineteenth century by a Dutch economist Arnold Jacob Cohen-Stuart (Cohen-Stuart, 1889). Moreover, the variant of this method (using the square-root function) was also considered in Bummel (2010, p. ...
... Moberg (2012). Note that a similar method was proposed for solving the taxation problem already in the nineteenth century by a Dutch economist Arnold Jacob Cohen-Stuart (Cohen-Stuart, 1889). Moreover, the variant of this method (using the square-root function) was also considered in Bummel (2010, p. ...
EXTRA CREDIT PROJECTS The following extra credit projects are
... axiom of choice is outside the scope of this class, we’ll finish with a version that only requires notions that we have previously discussed. Note that this version does not make explicit mention of functions, but it does rely on the fact that the axiom of choice is always true whenever every set in ...
... axiom of choice is outside the scope of this class, we’ll finish with a version that only requires notions that we have previously discussed. Note that this version does not make explicit mention of functions, but it does rely on the fact that the axiom of choice is always true whenever every set in ...
P - Department of Computer Science
... returns True if run on some element that is in S and False if run on an element that is not in S. – A characteristic function can be used to determine whether or not a given element is in S. ...
... returns True if run on some element that is in S and False if run on an element that is not in S. – A characteristic function can be used to determine whether or not a given element is in S. ...
Class Notes
... In this example, the axioms (called premises or hypotheses) are written above the line and the theorem (called the conclusion) is written below the line. The whole argument is called a deduction. This particular argument is an example of a rule of inference which is now usually called Universal Inst ...
... In this example, the axioms (called premises or hypotheses) are written above the line and the theorem (called the conclusion) is written below the line. The whole argument is called a deduction. This particular argument is an example of a rule of inference which is now usually called Universal Inst ...
Computational foundations of basic recursive function theory
... The theory of computability, or basic recursive function theory as it is often called, is usually motivated and developed using Church’s thesis. Here we show that there is an alternative computability theory in which some of the basic results on unsolvability become more absolute, results on complet ...
... The theory of computability, or basic recursive function theory as it is often called, is usually motivated and developed using Church’s thesis. Here we show that there is an alternative computability theory in which some of the basic results on unsolvability become more absolute, results on complet ...
Unary negation: ϕ1 ¬ϕ1 T F F T
... Logic textbooks don’t usually discuss connectives of higher adicity, although the following one is sometimes mentioned (e.g., by Alonzo Church, 1956). He called it “conditional disjunction”, although most of the rest of us call it “if–then–else”: ...
... Logic textbooks don’t usually discuss connectives of higher adicity, although the following one is sometimes mentioned (e.g., by Alonzo Church, 1956). He called it “conditional disjunction”, although most of the rest of us call it “if–then–else”: ...
UNIVERSITY OF LONDON BA EXAMINATION PHILOSOPHY
... (i) Prove that there is an injection from a set A to its power set PA. (ii) Prove that there is no bijection from a set A to its power set PA. (iii) Let C ⊆ D. What is the characteristic function of C in D? For any set A, let H be the function with domain PA such that for any B ∈ PA, H(B) = the char ...
... (i) Prove that there is an injection from a set A to its power set PA. (ii) Prove that there is no bijection from a set A to its power set PA. (iii) Let C ⊆ D. What is the characteristic function of C in D? For any set A, let H be the function with domain PA such that for any B ∈ PA, H(B) = the char ...
Introduction to "Mathematical Foundations for Software Engineering"
... Computability is the study of the limits of these machines 2012: J Paul Gibson ...
... Computability is the study of the limits of these machines 2012: J Paul Gibson ...
docx
... If U={1, 2, 3, 4, 5, 6} and using the same ordering as above, provide bit-representations for the following: ...
... If U={1, 2, 3, 4, 5, 6} and using the same ordering as above, provide bit-representations for the following: ...
Upper-Bounding Proof Length with the Busy
... Statements of this form are known as a Π1 statements, and this class includes famous problems such as the Goldbach conjecture (“all even numbers are sums of two primes”). It is commonly taught that checking examples never suffices to establish the truth of a hypothesis, no matter how many examples o ...
... Statements of this form are known as a Π1 statements, and this class includes famous problems such as the Goldbach conjecture (“all even numbers are sums of two primes”). It is commonly taught that checking examples never suffices to establish the truth of a hypothesis, no matter how many examples o ...
A Question About Increasing Functions
... Now u < v, so u − v < 0. The quantity in the square brackets on the right side of (3) is positive because it is the sum of two squares which can’t both be zero. Thus, the product on the right side of (3) is negative, and from this it follows that u3 < v 3 . Our appeal to the definition shows that th ...
... Now u < v, so u − v < 0. The quantity in the square brackets on the right side of (3) is positive because it is the sum of two squares which can’t both be zero. Thus, the product on the right side of (3) is negative, and from this it follows that u3 < v 3 . Our appeal to the definition shows that th ...
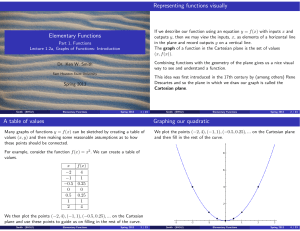
1.2 Functions Graphs (slides 4-to-1)
... x-value hits the curve at exactly one point. This should be true for all the elements in the domain of the function. A variety of applications in science require that we understand where a function is rising or falling and that we be able to find the local minimums and locals maximums of a function. ...
... x-value hits the curve at exactly one point. This should be true for all the elements in the domain of the function. A variety of applications in science require that we understand where a function is rising or falling and that we be able to find the local minimums and locals maximums of a function. ...
Arindama Singh`s "Cantor`s Little Theorem"
... is taken up to equivalence, two formulas in F1 are equal iff they are equivalent as first order formulas. Similarly, F0 denotes the set of all formulas having no free variables, i.e., all statements, up to equivalence. We also require the mechanism of Gödel numbering. This scheme assigns a unique n ...
... is taken up to equivalence, two formulas in F1 are equal iff they are equivalent as first order formulas. Similarly, F0 denotes the set of all formulas having no free variables, i.e., all statements, up to equivalence. We also require the mechanism of Gödel numbering. This scheme assigns a unique n ...
3463: Mathematical Logic
... (1.7) Lemma If M is a Turing machine with initial state q0 , and x is an input string, then there is a unique longest sequence σ0 , σ1 , . . . such that σ0 = q0 x, the initial configuration on input x, and for j = 1, 2, . . . if σj is defined then σj−1 ⊢M σj . This longest sequence is bounded if and ...
... (1.7) Lemma If M is a Turing machine with initial state q0 , and x is an input string, then there is a unique longest sequence σ0 , σ1 , . . . such that σ0 = q0 x, the initial configuration on input x, and for j = 1, 2, . . . if σj is defined then σj−1 ⊢M σj . This longest sequence is bounded if and ...
PDF
... is the class of Boolean algebras. Downey and Jockusch [23] showed that every low Boolean algebra is isomorphic to a computable one, and this result was extended to low2 Boolean algebras by Thurber [112] and then to low4 Boolean algebras by Knight and Stob [68]. Thus if the degree spectrum of a Boole ...
... is the class of Boolean algebras. Downey and Jockusch [23] showed that every low Boolean algebra is isomorphic to a computable one, and this result was extended to low2 Boolean algebras by Thurber [112] and then to low4 Boolean algebras by Knight and Stob [68]. Thus if the degree spectrum of a Boole ...
Slide 1
... • The checking algorithm A would then verify that the tour really does visit all of the cities and really does have total length K. without seeking all possible K solutions through each of the vertices. Polynomial. • The TSP, therefore, also belongs to NP. • How could a problem fail to belong to NP? ...
... • The checking algorithm A would then verify that the tour really does visit all of the cities and really does have total length K. without seeking all possible K solutions through each of the vertices. Polynomial. • The TSP, therefore, also belongs to NP. • How could a problem fail to belong to NP? ...
CHAPTER 8 One-to-One Functions and One-to
... words. As a rule of thumb, you should end your proof by summarizing what you have proved, with the last clause being the conclusion of the proof. This is sometimes implied, but usually you should put it in explicitly. We now prove that f(x) = 3 is not onto. Note that whether this is true or not depe ...
... words. As a rule of thumb, you should end your proof by summarizing what you have proved, with the last clause being the conclusion of the proof. This is sometimes implied, but usually you should put it in explicitly. We now prove that f(x) = 3 is not onto. Note that whether this is true or not depe ...
Midterm Exam 2 Solutions, Comments, and Feedback
... Thus, (1) holds for n = k + 1, and since a1 , . . . , ak+1 were arbitrary real numbers, we have obtained statement P (k + 1). Hence, the proof of the induction step is complete. Conclusion: By the principle of induction, P (n) is true for all n ∈ N. 5. Let A, B, C be sets, f : A → B, and g : B → C b ...
... Thus, (1) holds for n = k + 1, and since a1 , . . . , ak+1 were arbitrary real numbers, we have obtained statement P (k + 1). Hence, the proof of the induction step is complete. Conclusion: By the principle of induction, P (n) is true for all n ∈ N. 5. Let A, B, C be sets, f : A → B, and g : B → C b ...
compactness slides
... The language of sentential logic, that is, the set of all wffs, corresponds to C ∗ , the intersection of all inductive sets w.r.t. B and F. By the unique readability theorem C ∗ is freely generated from the set of sentence symbols by the functions in F. This guarantees the uniqueness of the extensi ...
... The language of sentential logic, that is, the set of all wffs, corresponds to C ∗ , the intersection of all inductive sets w.r.t. B and F. By the unique readability theorem C ∗ is freely generated from the set of sentence symbols by the functions in F. This guarantees the uniqueness of the extensi ...
here - Core Math Seminars
... exponents and logarithms, and the solution of logarithmic and exponential equations. Graphing utilities will be used to investigate and verify the graphs and solutions. ...
... exponents and logarithms, and the solution of logarithmic and exponential equations. Graphing utilities will be used to investigate and verify the graphs and solutions. ...
1-1
... • Property – A property possesed by all and only those set elements is given. • Acceptor – A finite state acceptor is used for languages (sets of strings) for which only a finite number of things need to be remembered. • Recursive methods – a finite basis set is given along with rules for forming th ...
... • Property – A property possesed by all and only those set elements is given. • Acceptor – A finite state acceptor is used for languages (sets of strings) for which only a finite number of things need to be remembered. • Recursive methods – a finite basis set is given along with rules for forming th ...
Recursion
... a denotes the first Fibonacci number b is the second Fibonacci number n is the nth Fibonacci number: ...
... a denotes the first Fibonacci number b is the second Fibonacci number n is the nth Fibonacci number: ...
Reasoning About Recursively Defined Data
... Next, if z is not an atom, it must have projections. (4) Vz[-~atom(z) D ~x(K(z) = x)]. Vz[~atom(z) D 3 x ( L ( z ) = x)]. Finally, once an element z lies in A, all iterations of projection functions from z (as long as they are defined) must lie in A. (5) Vz[atom(z) A 3 x ( K ( z ) = x) ~ atom(K(z)) ...
... Next, if z is not an atom, it must have projections. (4) Vz[-~atom(z) D ~x(K(z) = x)]. Vz[~atom(z) D 3 x ( L ( z ) = x)]. Finally, once an element z lies in A, all iterations of projection functions from z (as long as they are defined) must lie in A. (5) Vz[atom(z) A 3 x ( K ( z ) = x) ~ atom(K(z)) ...