slides - network systems lab @ sfu
... System Calls How can we access OS services? System calls A programming interface to OS services Typically written in high-level language (C or C++) Mostly accessed by programs via a high-level Application Program Interface (API), rather than direct system call ...
... System Calls How can we access OS services? System calls A programming interface to OS services Typically written in high-level language (C or C++) Mostly accessed by programs via a high-level Application Program Interface (API), rather than direct system call ...
Slide 1
... Programming Language, 2nd Edition, Prentice Hall – Is considered “THE” book on C : coauthor belongs to the creators of the C programming language – The book is not an introductory programming manual; it assumes some familiarity with basic programming concepts ...
... Programming Language, 2nd Edition, Prentice Hall – Is considered “THE” book on C : coauthor belongs to the creators of the C programming language – The book is not an introductory programming manual; it assumes some familiarity with basic programming concepts ...
Chapter 1 Introduction to Computers, Programs, and Java
... 5. A bit is a binary digit 0 or 1. A byte is a sequence of 8 bits. 6. Memory is like a work area for programs. Before a program is executed, it is brought into the memory. RAM stands for random-access memory. It is called RAM because a memory cell can be accessed directly. 7. Memory size is measured ...
... 5. A bit is a binary digit 0 or 1. A byte is a sequence of 8 bits. 6. Memory is like a work area for programs. Before a program is executed, it is brought into the memory. RAM stands for random-access memory. It is called RAM because a memory cell can be accessed directly. 7. Memory size is measured ...
smu_MCA_SYSTEM PROGRAMMING(MC0073)
... 2. symbols, data 3. symbols, instruction and addresses 4. address, symbol Qs 13. In assembly language , each statement has two operands , the first operand is always a ---------- which can be any one of AREG, BREG, CREG and DREG. The second operands refers to a -------- using a symbolic name and an ...
... 2. symbols, data 3. symbols, instruction and addresses 4. address, symbol Qs 13. In assembly language , each statement has two operands , the first operand is always a ---------- which can be any one of AREG, BREG, CREG and DREG. The second operands refers to a -------- using a symbolic name and an ...
Operating- System Structures
... the system rather than touching all sections of the operating system. Information is kept only where it is needed and is accessible only within a defined and restricted area, so any bugs affecting that data must be limited to a specific module or layer. ...
... the system rather than touching all sections of the operating system. Information is kept only where it is needed and is accessible only within a defined and restricted area, so any bugs affecting that data must be limited to a specific module or layer. ...
Chapter 2: OS Structures
... OS kernel and returns status of the system call and any return values • The caller need know nothing about how the system call is implemented – Just needs to obey API and understand what OS will do as a result call – Most details of OS interface hidden from programmer by API • Managed by run-time su ...
... OS kernel and returns status of the system call and any return values • The caller need know nothing about how the system call is implemented – Just needs to obey API and understand what OS will do as a result call – Most details of OS interface hidden from programmer by API • Managed by run-time su ...
Lecture_1 - bridges to computing
... For Macintosh computers, Mac OS X, Linux, BSD, and some Windows variants are commonly used. Cellphones and other portable devices usually have their own custom build Operating Systems (Apple) but other portable OS are coming online (Android). ...
... For Macintosh computers, Mac OS X, Linux, BSD, and some Windows variants are commonly used. Cellphones and other portable devices usually have their own custom build Operating Systems (Apple) but other portable OS are coming online (Android). ...
Chapter Two User Operating System interface
... (the final system call). As we can see1 even simple programs may make heavy use of the operating system. Frequently, systems execute thousands of system calls per second. Most programmers never see this level of detail however. Typically application developers design programs according to an applic ...
... (the final system call). As we can see1 even simple programs may make heavy use of the operating system. Frequently, systems execute thousands of system calls per second. Most programmers never see this level of detail however. Typically application developers design programs according to an applic ...
dasan.sejong.ac.kr
... Internals and Design Principles Operating systems are those programs that interface the machine with the applications programs. The main function of these systems is to dynamically allocate the shared system resources to the executing programs. As such, research in this area is clearly concerned wit ...
... Internals and Design Principles Operating systems are those programs that interface the machine with the applications programs. The main function of these systems is to dynamically allocate the shared system resources to the executing programs. As such, research in this area is clearly concerned wit ...
ppt
... The Java compiler translates the program into bytecode, a sort of intermediate language. When the Java program is run, the Java Virtual Machine compiles/translates the bytecode into machine code, and then the program runs. The machine code produced is different depending on the computer. The bytecod ...
... The Java compiler translates the program into bytecode, a sort of intermediate language. When the Java program is run, the Java Virtual Machine compiles/translates the bytecode into machine code, and then the program runs. The machine code produced is different depending on the computer. The bytecod ...
installing debian
... • Is the main tool to add and remove software. • You have to do this as “root”. • Set the distribution to be the “testing”. • Set the apt method for getting package files. • You can also add non-official sources: • http://www.braincells.com/debian sid/ for pine for example ...
... • Is the main tool to add and remove software. • You have to do this as “root”. • Set the distribution to be the “testing”. • Set the apt method for getting package files. • You can also add non-official sources: • http://www.braincells.com/debian sid/ for pine for example ...
Operating Systems
... processor requires is not in main memory kada so appudu page fault occur avutundi. ante when the page required by the processor is not present in the main memory then a page fault occurs The following thing is the definition given by some site check this out An interrupt that occurs when a program r ...
... processor requires is not in main memory kada so appudu page fault occur avutundi. ante when the page required by the processor is not present in the main memory then a page fault occurs The following thing is the definition given by some site check this out An interrupt that occurs when a program r ...
Lecture 2 Slides
... This is a word we make up to identify part of the program (in this case, the program itself) Identifiers must be a single word ...
... This is a word we make up to identify part of the program (in this case, the program itself) Identifiers must be a single word ...
PPT
... computers for specific application Operators collects program, runs it on the computer, collects output and returns it to the user Programmers write programs, submits it to the operator, waits for output, looks for errors, ...
... computers for specific application Operators collects program, runs it on the computer, collects output and returns it to the user Programmers write programs, submits it to the operator, waits for output, looks for errors, ...
Goals of Today’s Class Writing Portable Programs
... – Still, good to make programs as portable as possible – This requires extra care in writing and testing code ...
... – Still, good to make programs as portable as possible – This requires extra care in writing and testing code ...
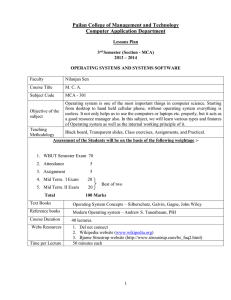
Operating Systems
... Ability to understand the synchronous and asynchronous communication mechanisms in their respective OS. ...
... Ability to understand the synchronous and asynchronous communication mechanisms in their respective OS. ...
OPERATING SYSTEM FUNCTIONS
... directory hierarchy, the root directory. Such absolute path names consist of the list of directories that must be traversed from the root directory to get to the file, with slashes separating the components. In Fig. 1-6, the path for file CS101 is /Faculty/Prof.Brown/Courses/CS101. The leading slash ...
... directory hierarchy, the root directory. Such absolute path names consist of the list of directories that must be traversed from the root directory to get to the file, with slashes separating the components. In Fig. 1-6, the path for file CS101 is /Faculty/Prof.Brown/Courses/CS101. The leading slash ...
Operating System
... – Each process is allocated a “slice” of time in the CPU. – When the time runs out, the process is interrupted, and another process is loaded into the CPU. • The act of giving each process a small slice of time to run is called time slicing. ...
... – Each process is allocated a “slice” of time in the CPU. – When the time runs out, the process is interrupted, and another process is loaded into the CPU. • The act of giving each process a small slice of time to run is called time slicing. ...
General overview of the System
... The Unix file system is characterized by : 1. A hierarchical structure – as a tree with a root 2. Consistent treatment of file data – unformatted stream of bytes 3. The ability to create and delete files 4. Dynamic growth of files 5. The protection of file data – access permissions for three classes ...
... The Unix file system is characterized by : 1. A hierarchical structure – as a tree with a root 2. Consistent treatment of file data – unformatted stream of bytes 3. The ability to create and delete files 4. Dynamic growth of files 5. The protection of file data – access permissions for three classes ...
accounting for managers - Pailan College of Management and
... Course to be covered 7.1 Basic concepts of security Different kinds of threats Security principle Types of authentication Formal models of protection worms and viruses ...
... Course to be covered 7.1 Basic concepts of security Different kinds of threats Security principle Types of authentication Formal models of protection worms and viruses ...
Library (computing)
In computer science, a library is a collection of non-volatile resources used by computer programs, often to develop software. These may include configuration data, documentation, help data, message templates, pre-written code and subroutines, classes, values or type specifications. In IBM's OS/360 and its successors they are referred to as partitioned data sets.In computer science, a library is a collection of implementations of behavior, written in terms of a language, that has a well-defined interface by which the behavior is invoked. This means that as long as a higher level program uses a library to make system calls, it does not need to be re-written to implement those system calls over and over again. In addition, the behavior is provided for reuse by multiple independent programs. A program invokes the library-provided behavior via a mechanism of the language. For example, in a simple imperative language such as C, the behavior in a library is invoked by using C's normal function-call. What distinguishes the call as being to a library, versus being to another function in the same program, is the way that the code is organized in the system. Library code is organized in such a way that it can be used by multiple programs that have no connection to each other, while code that is part of a program is organized to only be used within that one program. This distinction can gain a hierarchical notion when a program grows large, such as a multi-million-line program. In that case, there may be internal libraries that are reused by independent sub-portions of the large program. The distinguishing feature is that a library is organized for the purposes of being reused by independent programs or sub-programs, and the user only needs to know the interface, and not the internal details of the library.The value of a library is the reuse of the behavior. When a program invokes a library, it gains the behavior implemented inside that library without having to implement that behavior itself. Libraries encourage the sharing of code in a modular fashion, and ease the distribution of the code. The behavior implemented by a library can be connected to the invoking program at different program lifecycle phases. If the code of the library is accessed during the build of the invoking program, then the library is called a static library. An alternative is to build the executable of the invoking program and distribute that, independently from the library implementation. The library behavior is connected after the executable has been invoked to be executed, either as part of the process of starting the execution, or in the middle of execution. In this case the library is called a dynamic library. A dynamic library can be loaded and linked as part of preparing a program for execution, by the linker. Alternatively, in the middle of execution, an application may explicitly request that a module be loaded.Most compiled languages have a standard library although programmers can also create their own custom libraries. Most modern software systems provide libraries that implement the majority of system services. Such libraries have commoditized the services which a modern application requires. As such, most code used by modern applications is provided in these system libraries.