Computer Backup Demo
... the Operating System, the “Documents & Settings” directory, and those programs that refuse to install anywhere else). Move the “My Documents” directory, “TEMP”, and “Temporary Internet Files” elsewhere. Use Ghost to backup C: to another partition (e.g. D: - which may be on the same physical hard dri ...
... the Operating System, the “Documents & Settings” directory, and those programs that refuse to install anywhere else). Move the “My Documents” directory, “TEMP”, and “Temporary Internet Files” elsewhere. Use Ghost to backup C: to another partition (e.g. D: - which may be on the same physical hard dri ...
File Systems - The University of Alabama in Huntsville
... serial access is enforced to make sure data is consistent. That is, one operation is performed in its entirety before the next one begins. • However, a read from user 1, followed by a write from user 2, followed by a read from user 1 means that user 1 is reading two different versions of the file. U ...
... serial access is enforced to make sure data is consistent. That is, one operation is performed in its entirety before the next one begins. • However, a read from user 1, followed by a write from user 2, followed by a read from user 1 means that user 1 is reading two different versions of the file. U ...
Lec9 Networking
... DNS server converts the name to an IP address, allowing the client to send a packet to the Web server as requested The information in DNS can be thought of as an inverted hierarchical tree, where the top of the tree is called root and is represented by a period Users typically don’t refer to roots, ...
... DNS server converts the name to an IP address, allowing the client to send a packet to the Web server as requested The information in DNS can be thought of as an inverted hierarchical tree, where the top of the tree is called root and is represented by a period Users typically don’t refer to roots, ...
Gfarm Grid File System Osamu Tatebe University of Tsukuba
... Virtual file system that federates local storage of commodity PCs (cluster nodes or Grid nodes) Enables transparent access using Global namespace to dispersed file data in a Grid Supports fault tolerance and avoids access concentration by automatic replica selection It can be mounted by all cluster ...
... Virtual file system that federates local storage of commodity PCs (cluster nodes or Grid nodes) Enables transparent access using Global namespace to dispersed file data in a Grid Supports fault tolerance and avoids access concentration by automatic replica selection It can be mounted by all cluster ...
Introduction to MS Access - San Francisco State University
... – Don’t use the default ID field for primary key. Use a meaningful entity key field. ...
... – Don’t use the default ID field for primary key. Use a meaningful entity key field. ...
File - CSUS
... Word document and a WordPerfect document. The first two point out a difference in the actual data, the second pair a difference in “formatting”. Many times a file’s content can be known by the file extension, that is the trailing letters of the filename after the “.” For example a file named opera.e ...
... Word document and a WordPerfect document. The first two point out a difference in the actual data, the second pair a difference in “formatting”. Many times a file’s content can be known by the file extension, that is the trailing letters of the filename after the “.” For example a file named opera.e ...
The broken file shredder
... The file system may relocate a file block when it is updated, to reduce file fragmentation. Journaling file systems may create additional temporary copies of data (Ext3fs: journal=data). Copy-on-write file systems (like Solaris ZFS) never overwrite a disk block that is “in use”. None of thes ...
... The file system may relocate a file block when it is updated, to reduce file fragmentation. Journaling file systems may create additional temporary copies of data (Ext3fs: journal=data). Copy-on-write file systems (like Solaris ZFS) never overwrite a disk block that is “in use”. None of thes ...
Split Up For Class XII
... NOT; Truth Tables; Closure Property, Commutative Law, Associative Law, Identity law, Inverse law, Principle of Duality, Idem potent Law, Distributive Law, Absorption Law, Involution law, DeMorgan’s Law and their applications; Obtaining Sum of Product (SOP) and Product of Sum (POS) form from the Trut ...
... NOT; Truth Tables; Closure Property, Commutative Law, Associative Law, Identity law, Inverse law, Principle of Duality, Idem potent Law, Distributive Law, Absorption Law, Involution law, DeMorgan’s Law and their applications; Obtaining Sum of Product (SOP) and Product of Sum (POS) form from the Trut ...
ppt
... Get the torrent file (has tracker and metadata for the file) Contact the tracker Tracker tells the peer which peers to contact for the different chunks Use TCP to get the chunks, use checksum to see if error-free and merge ...
... Get the torrent file (has tracker and metadata for the file) Contact the tracker Tracker tells the peer which peers to contact for the different chunks Use TCP to get the chunks, use checksum to see if error-free and merge ...
Mid-term Presentation
... Important to know how our data is being stored. Need to know how your data can be stored efficiently in the cloud i.e. choosing the right kind of storage. ...
... Important to know how our data is being stored. Need to know how your data can be stored efficiently in the cloud i.e. choosing the right kind of storage. ...
File Systems
... disk to memory – return to user as requested. – For sequential reading, this means that buffering can (ideally) keep ahead of the user process, reducing the number of delays to wait for input. ...
... disk to memory – return to user as requested. – For sequential reading, this means that buffering can (ideally) keep ahead of the user process, reducing the number of delays to wait for input. ...
File-Management
... File Operations • File is an abstract data type • Create- find space in file system, make entry in the file system • Write- make system call to specify name and information content of the file to b written in the file. • Read- system call specifying the name and the location in the memory where tha ...
... File Operations • File is an abstract data type • Create- find space in file system, make entry in the file system • Write- make system call to specify name and information content of the file to b written in the file. • Read- system call specifying the name and the location in the memory where tha ...
Xerox PARCTAB
... CeOpenDatabaseEx() to open an existing database – can ask to be notified if someone else modifies when in use. • CeWriteRecordProps() to create or update a record. • Each call to CeReadRecordProps() returns the next record in the specified sort order (at open) • CeSeekDatabase() to seek to a specifi ...
... CeOpenDatabaseEx() to open an existing database – can ask to be notified if someone else modifies when in use. • CeWriteRecordProps() to create or update a record. • Each call to CeReadRecordProps() returns the next record in the specified sort order (at open) • CeSeekDatabase() to seek to a specifi ...
582 Lab Activities - University of Maryland, College Park
... Network Time Protocol (Space-to-Ground I/F) Triana mission flight software architecture. ...
... Network Time Protocol (Space-to-Ground I/F) Triana mission flight software architecture. ...
(DOCX, Unknown)
... Files are stored in one or more clusters, these clusters are unlikely to be next to each other because of the way files are allocated space on the HDD. Because they are scattered they form a ‘chain’ with all their separate clusters. The FAT system keeps at track of these chains. The FAT is a data ta ...
... Files are stored in one or more clusters, these clusters are unlikely to be next to each other because of the way files are allocated space on the HDD. Because they are scattered they form a ‘chain’ with all their separate clusters. The FAT system keeps at track of these chains. The FAT is a data ta ...
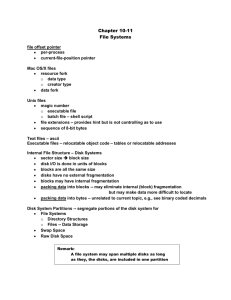
Chapter 10-11 File Systems
... Internal File Structure – Disk Systems sector size block size disk I/O is done in units of blocks blocks are all the same size disks have no external fragmentation blocks may have internal fragmentation packing data into blocks -- may eliminate internal (block) fragmentation but may make data more ...
... Internal File Structure – Disk Systems sector size block size disk I/O is done in units of blocks blocks are all the same size disks have no external fragmentation blocks may have internal fragmentation packing data into blocks -- may eliminate internal (block) fragmentation but may make data more ...
Schedule File Transformation Tools
... take effective decisions. This text file has section details spanned across multiple pages with headers repeating in each page. This text file also has some additional details in between sections that are not necessarily used. This project “GSU Schedule File Transformation Tools” focuses on creating ...
... take effective decisions. This text file has section details spanned across multiple pages with headers repeating in each page. This text file also has some additional details in between sections that are not necessarily used. This project “GSU Schedule File Transformation Tools” focuses on creating ...
File Transfer Protocol
... programs or other information from one computer to another. • This simple tool will let you do many things: download software, upload your own web pages, transfer information between your home and work machines. ...
... programs or other information from one computer to another. • This simple tool will let you do many things: download software, upload your own web pages, transfer information between your home and work machines. ...
Data Structures in C
... • In addition to these modes a file may be opened either as a binary or text file. • Text files may only contain ASCII data. • Binary files contain images of the data. • Files are opened as text by adding a “t” to the open mode. • Files are opened as binary by adding a “b” to the open mode. ...
... • In addition to these modes a file may be opened either as a binary or text file. • Text files may only contain ASCII data. • Binary files contain images of the data. • Files are opened as text by adding a “t” to the open mode. • Files are opened as binary by adding a “b” to the open mode. ...
Files and Directories
... – Inefficient for tiny files (a 1 byte file requires both an inode and a data block) – Inefficient encoding when file is mostly contiguous on disk (no equivalent to superpages) – Need to reserve 10-20% of free space to prevent ...
... – Inefficient for tiny files (a 1 byte file requires both an inode and a data block) – Inefficient encoding when file is mostly contiguous on disk (no equivalent to superpages) – Need to reserve 10-20% of free space to prevent ...
DBMS File Structure
... sequential file organization mechanism, records are placed in the file in the some sequential order based on the unique key field or search key. Practically, it is not possible to store all the records sequentially in physical form. Hash File Organization: This mechanism uses a Hash function computa ...
... sequential file organization mechanism, records are placed in the file in the some sequential order based on the unique key field or search key. Practically, it is not possible to store all the records sequentially in physical form. Hash File Organization: This mechanism uses a Hash function computa ...
Chapter 9 Physical Database Design Methodology
... • Select software based on user’s requirement • Select hardware based on software requirement ...
... • Select software based on user’s requirement • Select hardware based on software requirement ...
An Improved Approach to Generating Configuration Files from a
... Standard development environment Host interface written once Code sharing with web routines All work done centrally PL/SQL well integrated to Database ...
... Standard development environment Host interface written once Code sharing with web routines All work done centrally PL/SQL well integrated to Database ...
OSPP: File Systems
... – Inefficient for tiny files (a 1 byte file requires both an inode and a data block) – Inefficient encoding when file is mostly contiguous on disk (no equivalent to superpages) – Need to reserve 10-20% of free space to prevent ...
... – Inefficient for tiny files (a 1 byte file requires both an inode and a data block) – Inefficient encoding when file is mostly contiguous on disk (no equivalent to superpages) – Need to reserve 10-20% of free space to prevent ...