T - Intel
... A Label-switching Packet Forwarding Architecture for Multi-hop Wireless LANs IBM TJ Watson Research Center ...
... A Label-switching Packet Forwarding Architecture for Multi-hop Wireless LANs IBM TJ Watson Research Center ...
PPT - Winlab
... Any intermediate node in a multi-hop wireless network can operate as a router wide-applicability for a packet forwarding architecture ...
... Any intermediate node in a multi-hop wireless network can operate as a router wide-applicability for a packet forwarding architecture ...
Chapter 02 - Communicating Over The Network
... However, Network layer considers: the maximum size of PDU that each medium can transport Maximum Transmission Unit (MTU). Part of the control communication between the Data Link layer and the Network layer is the establishment of a maximum size for the packet. The Data Link layer passes the MTU upwa ...
... However, Network layer considers: the maximum size of PDU that each medium can transport Maximum Transmission Unit (MTU). Part of the control communication between the Data Link layer and the Network layer is the establishment of a maximum size for the packet. The Data Link layer passes the MTU upwa ...
18. Distributed Denial of Service (DDoS) ENEE 757 | CMSC 818V Today’s Lecture
... Defense #3: Network Capabiliaes • We’ve seen: CapabiliCes for file access control – User holds unforgeable Ccket for each file it needs to read/write ...
... Defense #3: Network Capabiliaes • We’ve seen: CapabiliCes for file access control – User holds unforgeable Ccket for each file it needs to read/write ...
Network Layer: Internet Protocol
... an IPv4 header without options. The header is divided into 16-bit sections. All the sections are added and the sum is complemented after wrapping the leftmost digit. The result is inserted in the checksum field. Note that the calculation of wrapped sum and checksum can also be done as follows in hex ...
... an IPv4 header without options. The header is divided into 16-bit sections. All the sections are added and the sum is complemented after wrapping the leftmost digit. The result is inserted in the checksum field. Note that the calculation of wrapped sum and checksum can also be done as follows in hex ...
Chapter 7 Packet-Switching Networks Chapter 7 Packet
... connection; All NEs have to be involved in reestablishment of connections in case of network fault In connectionless network operation, NEs do not deal with each explicit connection and hence are much simpler in design ...
... connection; All NEs have to be involved in reestablishment of connections in case of network fault In connectionless network operation, NEs do not deal with each explicit connection and hence are much simpler in design ...
Voice over IP
... RTP does not address resource reservation and does not guarantee quality-of-service for real-time services. ...
... RTP does not address resource reservation and does not guarantee quality-of-service for real-time services. ...
DatagramPacket packet
... For other applications, loss of packets is not acceptable (e.g. file transfers). ...
... For other applications, loss of packets is not acceptable (e.g. file transfers). ...
18 DPI
... information resources and supports reliable and secure communication. Because of reasons defined above now DPI systems are actual issue in the global telecommunication market. Researchers are working to development new methods to improve the performance of deep packet inspection applications. Theref ...
... information resources and supports reliable and secure communication. Because of reasons defined above now DPI systems are actual issue in the global telecommunication market. Researchers are working to development new methods to improve the performance of deep packet inspection applications. Theref ...
Introduction
... Inter-Process Communication Network Architecture Performance Metrics Implementation Issues ...
... Inter-Process Communication Network Architecture Performance Metrics Implementation Issues ...
Computer Networks: LANs, WANs The Internet
... History of Computers Computer – a machine that manipulates data according to a set of ...
... History of Computers Computer – a machine that manipulates data according to a set of ...
Darwin: Customizable Resource Management for Value
... » Forward error correction: many related code words map to the same data word » Detect errors and retry transmission ...
... » Forward error correction: many related code words map to the same data word » Detect errors and retry transmission ...
ppt - Carnegie Mellon School of Computer Science
... » Forward error correction: many related code words map to the same data word » Detect errors and retry transmission ...
... » Forward error correction: many related code words map to the same data word » Detect errors and retry transmission ...
Wireless Networks
... • Allocates a fixed bandwidth between a point-to-point connection involving the master and a single slave • The master maintains the SCO link by using reserved slots at regular intervals • The master can support up to three simultaneous SCO links, while a slave can support two or three SCO links ...
... • Allocates a fixed bandwidth between a point-to-point connection involving the master and a single slave • The master maintains the SCO link by using reserved slots at regular intervals • The master can support up to three simultaneous SCO links, while a slave can support two or three SCO links ...
TCP - WordPress.com
... – Increase window size so that sender is transmitting packets as fast as the network can carry them – Eliminates network idle time – Increases throughput (as compared to the simple positive acknowledgment protocol) ...
... – Increase window size so that sender is transmitting packets as fast as the network can carry them – Eliminates network idle time – Increases throughput (as compared to the simple positive acknowledgment protocol) ...
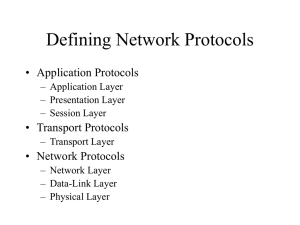
Defining Network Protocols
... ARP entries have a finite (timed) lifetime ARP entries are created by routers for non ethernet protocols (token ring, PPP) • tracing an ethernet address – Host system – Router – Switch ...
... ARP entries have a finite (timed) lifetime ARP entries are created by routers for non ethernet protocols (token ring, PPP) • tracing an ethernet address – Host system – Router – Switch ...
Overview - La Revue MODULAD
... – No insertion of own packets, just listen! – Obtain information from the captured data ...
... – No insertion of own packets, just listen! – Obtain information from the captured data ...